Questa pagina si applica ad Apigee, ma non ad Apigee hybrid.
Visualizza la documentazione di
Apigee Edge.
![]()
Questo documento descrive l'utilizzo di Private Service Connect (PSC) per configurare il routing dai client ad Apigee, chiamato anche traffico "inbound".
Panoramica
Puoi utilizzare PSC per connettere il VPC Apigee al VPC di cui hai eseguito il peering con Apigee o a qualsiasi altro VPC che controlli. Questo pattern architetturale elimina la necessità di creare gruppi di istanze gestite per inoltrare le richieste dal bilanciatore del carico globale ad Apigee. Con il metodo di routing PSC, le richieste proxy API passano attraverso un bilanciatore del carico HTTP(S) esterno globale che installi in un VPC a un singolo punto di collegamento nel VPC Apigee, chiamato collegamento del servizio. Questa configurazione ti consente di inviare richieste proxy API Apigee da qualsiasi macchina abilitata alla rete. Vedi la Figura 1.
Tieni presente le seguenti funzionalità PSC supportate in direzione nord:
- Puoi utilizzare PSC con qualsiasi istanza Apigee esistente.
- Puoi collegare più gruppi di endpoint di rete (NEG) PSC al bilanciatore del carico HTTP(S) esterno globale basato su Envoy di Google Cloud.
- PSC è supportato con i controlli di servizio VPC.
Puoi impostare una policy di gestione del traffico per il rilevamento di outlier nel servizio di backend per gestire automaticamente gli scenari di failover. Vai ai seguenti argomenti per ulteriori informazioni:
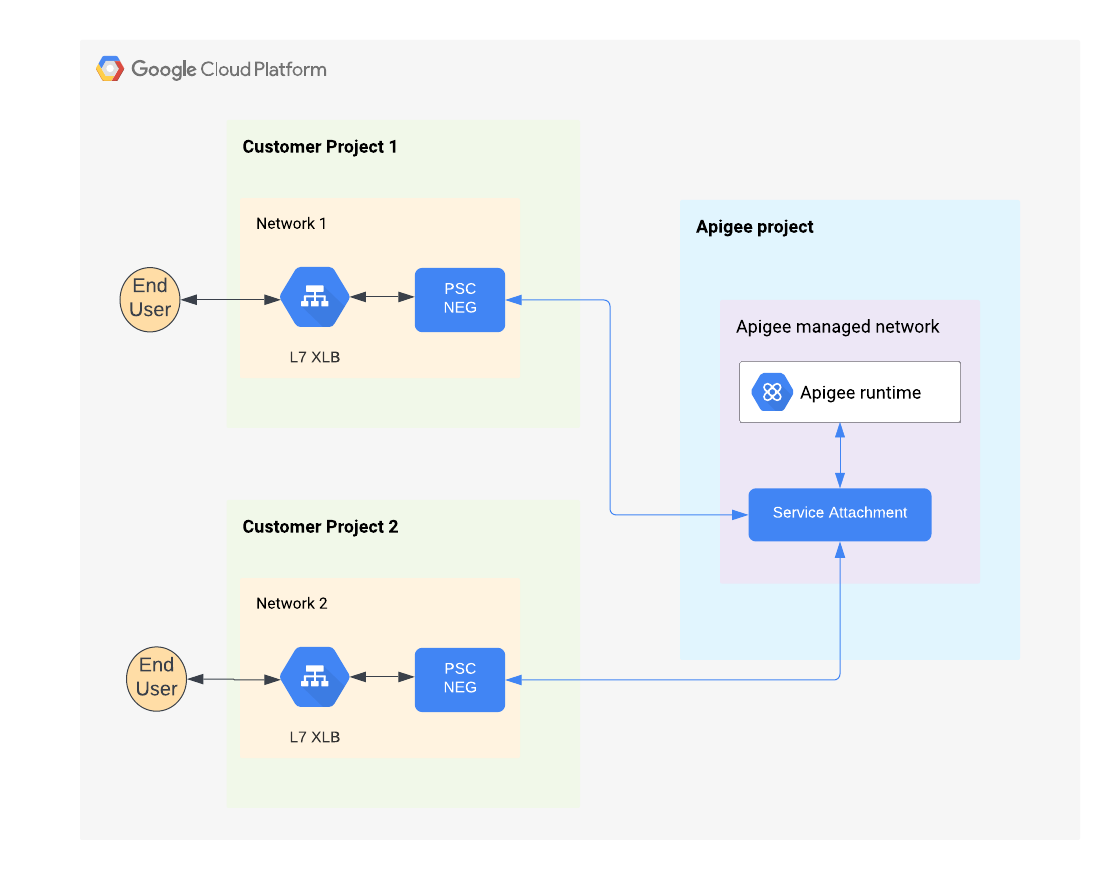
Figura 1: connessioni private ai servizi
Limitazioni
L'utilizzo di PSC con Apigee presenta attualmente le seguenti limitazioni:
Aggiornamento dell'elenco di accettazione dei consumatori per un'istanza Apigee
Il 10 ottobre 2024, il limite di connessioni NEG PSC consentite per progetto a un'istanza Apigee è stato aumentato da 20 a 100. Per tutte le istanze Apigee create prima di questa data, devi eseguire i passaggi descritti in questa sezione per aggiornare l'elenco di accettazione dei consumer e sfruttare il nuovo limite. Devi eseguire l'upgrade di ogni istanza di Apigee una sola volta per ricevere il nuovo limite di connessioni. Vedi anche Limiti di Private Service Connect (PSC).
Se hai bisogno di più di 1000 connessioni NEG PSC in totale in tutti i progetti Cloud collegati a un'istanza Apigee, contatta l'assistenza Google Cloud.
Per aggiornare l'elenco di accettazione dei consumer di un'istanza Apigee per sfruttare il limite di connessione più elevato, segui questi passaggi:
console Cloud
Per conoscere la procedura dettagliata, consulta Modificare l'elenco dei progetti accettati.
API Apigee
Modifica l'elenco di accettazione dei consumatori esistente per la tua istanza Apigee. Per utilizzare l'API instances:
- Recupera il token di autenticazione per l'API Apigee:
TOKEN="$(gcloud auth print-access-token)"
- Recupera l'elenco dei progetti cloud nell'elenco di accettazione dei consumer di un'istanza:
curl https://apigee.googleapis.com/v1/organizations/PROJECT_ID/instances/INSTANCE_ID \ -H "Authorization: Bearer $TOKEN" -H Content-Type:application/json | jq .consumerAcceptList
- Crea un file JSON denominato
update_consumer_accept_list.jsoncontenente l'elenco attuale dei progetti accettati restituito dal comando precedente. Ad esempio:{ "consumerAcceptList": [ "dg-runtime-test1", "ne24b79b92c7db623p-tp", "dg-runtime-test2", "jd2fee78402218863p-tp" ] } - (Facoltativo) Modifica il file per aggiungere altri progetti.
- Aggiorna l'istanza utilizzando come input il file JSON che hai creato. Ad esempio:
curl https://apigee.googleapis.com/v1/organizations/PROJECT_ID/instances/INSTANCE_ID?updateMask="consumer_accept_list" \ -X PATCH -H "Authorization: Bearer $TOKEN" -H Content-Type:application/json -d @update_consumer_accept_list.json
Configura il routing PSC
Supportiamo l'utilizzo di PSC per il routing in uscita da client interni ed esterni. Per la procedura dettagliata, vedi Passaggio 8: configura il routing delle istruzioni di provisioning della CLI.
Espansione multiregionale con PSC
Puoi espandere un'organizzazione Apigee in più regioni e utilizzare PSC per il routing in direzione nord nelle nuove regioni. Per maggiori dettagli, vedi Espansione di Apigee in più regioni.Eliminazione di un'istanza Apigee
Per eliminare un'istanza Apigee che utilizza PSC:
- Rimuovi ed elimina il backend NEG PSC dal bilanciatore del carico esterno.
- Elimina l'istanza di runtime Apigee utilizzando l'API Apigee. Questa è un'operazione a lunga esecuzione che può richiedere fino a 20 minuti.
- Se vuoi, recupera lo stato dell'operazione a lunga esecuzione utilizzando l'API Apigee.

