Questa pagina si applica ad Apigee, ma non ad Apigee hybrid.
Visualizza la documentazione di
Apigee Edge.
![]()
Apigee facilita le comunicazioni tra le richieste dell'API client e i servizi Apigee e Cloud tramite una connessione tra due reti: il VPC (o piano di runtime) Apigee e il VPC del cliente. Queste due reti sono collegate tra loro tramite una connessione privata in un processo noto come peering VPC.
L'esempio seguente mostra come il peering VPC consente la comunicazione tra il VPC Apigee e il VPC cliente:
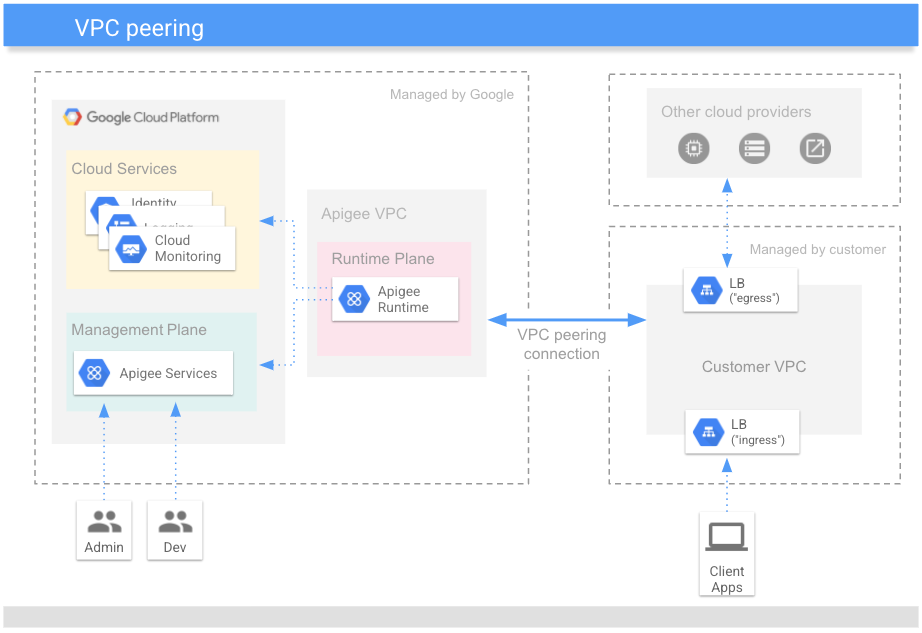
Il peering VPC consente al VPC Apigee di elaborare richieste e risposte inviate al VPC cliente:
-
Traffico in uscita: richieste proxy API inviate dai client al VPC del cliente che vengono trasmesse al piano di runtime Apigee per l'elaborazione. Anche servizi aggiuntivi come logging, gestione delle identità e metriche sono accessibili al piano di runtime.
-
Traffico in uscita: le richieste proxy API che devono accedere alle API di destinazione o ad altri servizi di backend nel VPC del cliente costituiscono la route in uscita. Questi servizi in uscita elaborano le risposte prima di restituirle al VPC del cliente per un'ulteriore elaborazione da parte del runtime Apigee prima che una risposta venga inviata al client.
Il passaggio di provisioning di Apigee, Configura il servizio di rete, esegue il peering VPC e alloca un intervallo di indirizzi IP (un intervallo CIDR) ad Apigee.
Dimensionamento della rete
Ogni istanza Apigee richiede un intervallo CIDR non sovrapposto di /22. Al piano di runtime Apigee (noto anche come data plane) vengono assegnati indirizzi IP all'interno dell'intervallo CIDR. Di conseguenza, è importante che l'intervallo sia riservato ad Apigee e non venga utilizzato da altre applicazioni nella rete VPC del cliente.
Un'istanza viene creata quando:
- Viene eseguito il provisioning di un'organizzazione Apigee, tramite la procedura guidata dell'interfaccia utente o l'interfaccia a riga di comando (CLI).
- Quando espandi Apigee a una nuova regione cloud per un'organizzazione esistente. Vedi anche Espansione di Apigee in più regioni.
Quando crei un'istanza, hai due opzioni per specificare un intervallo IP di rete:
- Alloca automaticamente l'intervallo: quando crei un'istanza Apigee, consenti ad Apigee di allocare qualsiasi intervallo disponibile e non sovrapposto dall'intervallo più grande allocato a Google. Ogni volta che viene ricreata un'istanza, l'intervallo IP viene allocato automaticamente. In questi casi, è possibile che la nuova istanza utilizzi un nuovo intervallo IP, se disponibile e non sovrapposto ad altri prodotti o servizi.
- Specifica un intervallo IP: puoi specificare l'intervallo IP che verrà utilizzato da Apigee. Questo intervallo IP deve provenire dall'intervallo non sovrapposto sottoposto a peering con Apigee. Questa opzione è utile quando vuoi allocare un intervallo IP più ampio per più prodotti Cloud, come Cloud SQL, Cloud Memorystore, Apigee e altri, e vuoi anche poter specificare intervalli IP effettivi per ciascuno di questi prodotti. Questo intervallo può essere un intervallo IP non RFC 1918, purché non sia un indirizzo IP pubblico utilizzato privatamente (PUPI). .
Dopo aver creato un'istanza, non puoi modificare l'intervallo CIDR. Per modificare l'intervallo CIDR, devi eliminare l'istanza e riconfigurarne una nuova. Fai attenzione se hai una sola istanza in un'organizzazione.
Considerazioni
Prima di allocare intervalli CIDR, consulta la sezione Considerazioni nella documentazione di Virtual Private Cloud.
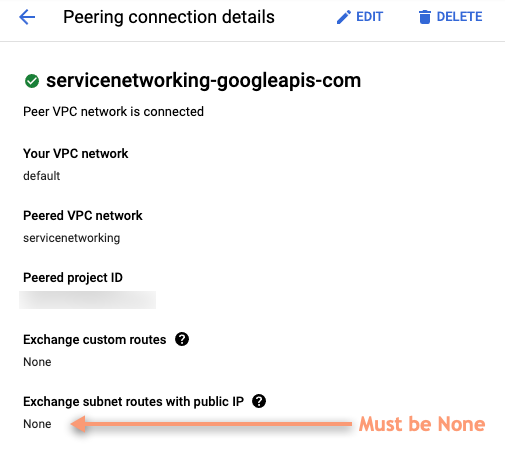
Quando crei una connessione di peering con Google, assicurati che gli IP pubblici non vengano scambiati. Per verificare:
- Nella console Google Cloud , vai alla pagina Peering di reti VPC. Vedi anche Utilizzo del peering di rete VPC.
- Seleziona la connessione di peering di rete VPC.
- Nei dettagli della connessione di peering, assicurati che l'opzione Scambia route di subnet con IP pubblico sia
impostata su Nessuno, come mostrato nello screenshot seguente.