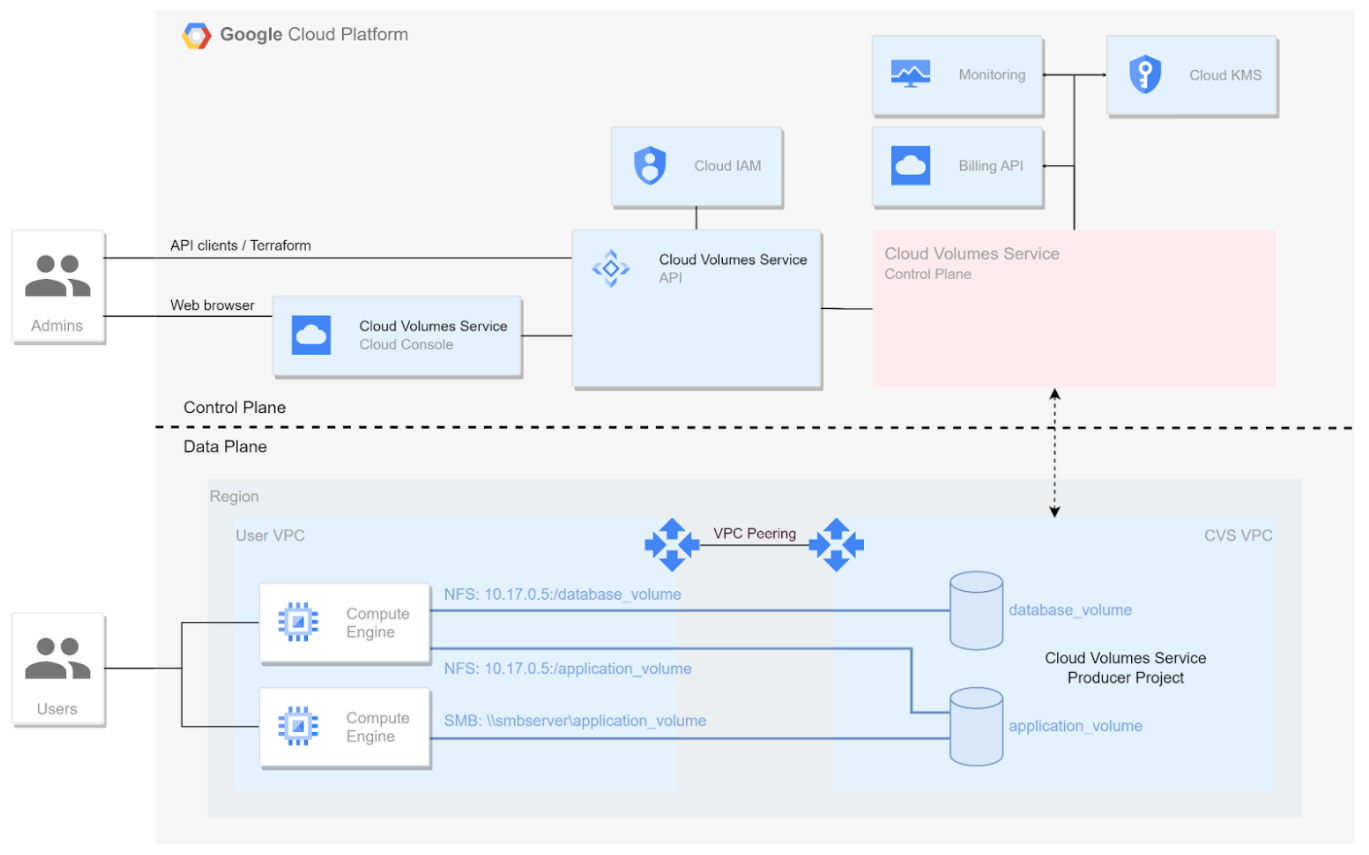
Cloud Volumes Service for Google Cloud uses the Google Cloud Private Services Access framework.
In this framework, you can connect to the Cloud Volumes Service from your VPC networks by using private (RFC 1918) addresses and non-private (non-RFC 1918) addresses. This framework uses Service Networking and VPC peering constructs similar to other Google Cloud services like Cloud SQL.
This design provides enhanced security and complete isolation between tenants, and the setup requires no manual intervention.
Cloud Volumes Service is deployed for your projects as one or more producer tenant projects with their own tenant VPC networks. You peer your VPC network with the tenant VPC network to provide access to the volumes.
The following diagram shows the high-level flow of elements in the service's control plane (top) and data plane (bottom). This diagram is a general representation of the integration between NetApp Cloud Volumes Service and Google Cloud, not necessarily the physical architecture of a specific implementation.
Learn about how to set up private services access for Cloud Volumes Service.
In the control plane view, you can see and manage only volumes, snapshots, AD connections, and other project components that were created in a particular project.
In the data plane view, you can access every volume that is connected to the VPC network to which Cloud Volumes Service is connected.
The following diagram shows multiple deployment scenarios in one picture.

This diagram shows a project with three VPC networks connected to Cloud Volumes Service and multiple Compute Engine VMs (GCE1-7) sharing volumes.
- VPC1 allows GCE1 to access volumes A and B.
- VPC2 allows GCE2 and GCE4 to access volume C.
- The third VPC network is a shared VPC, shared with two service projects. It allows GCE3, GCE4, GCE5, and GCE6 to access volumes D and E.
- GCE7 cannot access any volume.
