This deployment guide shows you how to deploy and connect to a Compute Engine virtual machine (VM) that is ready for the installation of SAP Adaptive Server Enterprise (ASE) on a Linux operating system.
The instructions in this guide use Cloud Deployment Manager to deploy and configure the VM, the Linux operating system, and the required disk volumes for SAP ASE.
For details on planning your deployment, see the SAP ASE planning guide.
Prerequisites
If you require your SAP workload to run in compliance with data residency, access control, support personnel, or regulatory requirements, then you must create the required Assured Workloads folder. For more information, see Compliance and sovereign controls for SAP on Google Cloud.
If you do not already have a Google Cloud project with billing enabled, then you must create one before you can deploy a VM for your SAP ASE installation.
To create a project:
- Sign in to your Google Cloud account. If you're new to Google Cloud, create an account to evaluate how our products perform in real-world scenarios. New customers also get $300 in free credits to run, test, and deploy workloads.
-
In the Google Cloud console, on the project selector page, select or create a Google Cloud project.
Roles required to select or create a project
- Select a project: Selecting a project doesn't require a specific IAM role—you can select any project that you've been granted a role on.
-
Create a project: To create a project, you need the Project Creator
(
roles/resourcemanager.projectCreator), which contains theresourcemanager.projects.createpermission. Learn how to grant roles.
-
Verify that billing is enabled for your Google Cloud project.
-
In the Google Cloud console, on the project selector page, select or create a Google Cloud project.
Roles required to select or create a project
- Select a project: Selecting a project doesn't require a specific IAM role—you can select any project that you've been granted a role on.
-
Create a project: To create a project, you need the Project Creator
(
roles/resourcemanager.projectCreator), which contains theresourcemanager.projects.createpermission. Learn how to grant roles.
-
Verify that billing is enabled for your Google Cloud project.
Configuring the gcloud command environment
These instructions use
Cloud Shell to enter gcloud commands that deploy or configure
your Google Cloud resources. Cloud Shell is accessed through the
Google Cloud console in your browser.
Cloud Shell runs on a VM that Google Cloud provisions each time
you start Cloud Shell. The first time you use Cloud Shell,
Google Cloud also creates a persistent $HOME directory for you,
which is restored each time you open Cloud Shell.
The provisioned VM includes the latest
Google Cloud CLI.
Therefore, the gcloud
commands that you use in Cloud Shell are the same as
those you would use in a locally installed instance of the gcloud CLI.
If you have the gcloud CLI installed, you can issue the gcloud
commands that are used in these instructions from your local machine. However,
with a locally installed gcloud CLI you must always make sure that you
are using the latest version of the gcloud CLI.
Whether you use Cloud Shell or gcloud CLI, you
can set and change the properties of your gcloud command environment and save
them as a configuration. Configurations are collections of key-value pairs
that influence the behavior of the gcloud commands.
Some basic actions you can take with a configuration in Cloud Shell include:
Initialize a configuration:
gcloud init
Check the settings of your current gcloud configuration:
gcloud config list
Switch to the required Google Cloud project. Replace
PROJECT_IDwith your Google Cloud project ID.gcloud config set project PROJECT_ID
Set a default region. Replace
REGIONwith a Google Cloud region.gcloud config set compute/region REGION
Set a default zone. Replace
ZONEwith a Google Cloud zone.gcloud config set compute/zone ZONE
Create a new configuration. Replace
NAMEwith the name for the configuration.gcloud config configurations create NAME
For more information about working with configurations, see Managing gcloud CLI configurations.
Creating a network
For security purposes, create a new network. You can control who has access by adding firewall rules or by using another access control method.
If your project has a default VPC network, then don't use it. Instead, create your own VPC network so that the only firewall rules in effect are those that you create explicitly.
During deployment, Compute Engine instances typically require access to the internet to download Google Cloud's Agent for SAP. If you are using one of the SAP-certified Linux images that are available from Google Cloud, then the compute instance also requires access to the internet in order to register the license and to access OS vendor repositories. A configuration with a NAT gateway and with VM network tags supports this access, even if the target compute instances don't have external IPs.
To set up networking:
Console
- In the Google Cloud console, go to the VPC networks page.
- Click Create VPC network.
- Enter a Name for the network.
The name must adhere to the naming convention. VPC networks use the Compute Engine naming convention.
- For Subnet creation mode, choose Custom.
- In the New subnet section, specify the following configuration parameters for a
subnet:
- Enter a Name for the subnet.
- For Region, select the Compute Engine region where you want to create the subnet.
- For IP stack type, select IPv4 (single-stack) and then enter an IP
address range in the
CIDR format,
such as
10.1.0.0/24.This is the primary IPv4 range for the subnet. If you plan to add more than one subnet, then assign non-overlapping CIDR IP ranges for each subnetwork in the network. Note that each subnetwork and its internal IP ranges are mapped to a single region.
- Click Done.
- To add more subnets, click Add subnet and repeat the preceding steps. You can add more subnets to the network after you have created the network.
- Click Create.
gcloud
- Go to Cloud Shell.
- To create a new network in the custom subnetworks mode, run:
gcloud compute networks create NETWORK_NAME --subnet-mode custom
Replace
NETWORK_NAMEwith the name of the new network. The name must adhere to the naming convention. VPC networks use the Compute Engine naming convention.Specify
--subnet-mode customto avoid using the default auto mode, which automatically creates a subnet in each Compute Engine region. For more information, see Subnet creation mode. - Create a subnetwork, and specify the region and IP range:
gcloud compute networks subnets create SUBNETWORK_NAME \ --network NETWORK_NAME --region REGION --range RANGEReplace the following:
SUBNETWORK_NAME: the name of the new subnetworkNETWORK_NAME: the name of the network you created in the previous stepREGION: the region where you want the subnetwork If you are using SAP ASE with SAP NetWeaver, use a region that is supported for SAP NetWeaver.RANGE: the IP address range, specified in CIDR format, such as10.1.0.0/24If you plan to add more than one subnetwork, assign non-overlapping CIDR IP ranges for each subnetwork in the network. Note that each subnetwork and its internal IP ranges are mapped to a single region.
- Optionally, repeat the previous step and add additional subnetworks.
Setting up a NAT gateway
If you need to create one or more VMs without public IP addresses, then you need to use network address translation (NAT) to enable the VMs to access the internet. Use Cloud NAT, a Google Cloud distributed, software-defined managed service that lets VMs send outbound packets to the internet and receive any corresponding established inbound response packets. Alternatively, you can set up a separate VM as a NAT gateway.
To create a Cloud NAT instance for your project, see Using Cloud NAT.
After you configure Cloud NAT for your project, your VM instances can securely access the internet without a public IP address.
Adding firewall rules
By default, an implied firewall rule blocks incoming connections from outside your Virtual Private Cloud (VPC) network. To allow incoming connections, set up a firewall rule for your VM. After an incoming connection is established with a VM, traffic is permitted in both directions over that connection.
You can also create a firewall rule to allow external access to specified ports,
or to restrict access between VMs on the same network. If the default
VPC network type is used, some additional default rules also
apply, such as the default-allow-internal rule, which allows connectivity
between VMs on the same network on all ports.
Depending on the IT policy that is applicable to your environment, you might need to isolate or otherwise restrict connectivity to your database host, which you can do by creating firewall rules.
Depending on your scenario, you can create firewall rules to allow access for:
- ASE network listener for client connections. The default ASE port number is
5000. - The ports required by SAP ASE Cockpit. For a list of ports that ASE Cockpit uses, see the SAP ASE Cockpit documentation in the SAP Help Portal.
- The default SAP ports that are listed in TCP/IP of All SAP Products.
- Connections from your computer or your corporate network environment to your Compute Engine VM instance. If you are unsure of what IP address to use, talk to your company's network administrator.
- Communication between VMs in the SAP HANA subnetwork, including communication between nodes in an SAP HANA scale-out system or communication between the database server and application servers in a 3-tier architecture. You can enable communication between VMs by creating a firewall rule to allow traffic that originates from within the subnetwork.
- SSH connections to your VM instance, including SSH-in-browser.
- Connection to your VM by using a third-party tool in Linux. Create a rule to allow access for the tool through your firewall.
To create a firewall rule:
Console
In the Google Cloud console, go to the VPC network Firewall page.
At the top of the page, click Create firewall rule.
- In the Network field, select the network where your VM is located.
- In the Targets field, specify the resources on Google Cloud that this rule applies to. For example, specify All instances in the network. Or to to limit the rule to specific instances on Google Cloud, enter tags in Specified target tags.
- In the Source filter field, select one of the following:
- IP ranges to allow incoming traffic from specific IP addresses. Specify the range of IP addresses in the Source IP ranges field.
- Subnets to allow incoming traffic from a particular subnetwork. Specify the subnetwork name in the following Subnets field. You can use this option to allow access between the VMs in a 3-tier or scaleout configuration.
- In the Protocols and ports section, select Specified protocols and
ports and enter
tcp:PORT_NUMBER.
Click Create to create your firewall rule.
gcloud
Create a firewall rule by using the following command:
$ gcloud compute firewall-rules create FIREWALL_NAME
--direction=INGRESS --priority=1000 \
--network=NETWORK_NAME --action=ALLOW --rules=PROTOCOL:PORT \
--source-ranges IP_RANGE --target-tags=NETWORK_TAGSDeploying a Linux VM for SAP ASE with Deployment Manager
The following instructions use Deployment Manager to deploy a VM instance with Linux and all of the persistent disks that SAP ASE requires. You define the values for the installation in a Deployment Manager configuration file template.
Deployment Manager treats all of the resources that are created for the SAP ASE system as a single entity called a deployment. You can view all of the deployments for your Google Cloud project on the Deployments page in the Google Cloud console.
The following instructions use Cloud Shell, but if you prefer, you can use the Google Cloud CLI in your local terminal instead.
Open the Cloud Shell.
Download the
template.yamlconfiguration file template to your working directory by entering the following command in the Cloud Shell:wget https://storage.googleapis.com/cloudsapdeploy/deploymentmanager/latest/dm-templates/sap_ase/template.yaml
Optionally, rename the
template.yamlfile to identify the configuration it defines.Open the
template.yamlfile in the Cloud Shell code editor.To open the Cloud Shell code editor, click the pencil icon in the upper right corner of the Cloud Shell terminal window.
In the
template.yamlfile, update the following property values by replacing the brackets and their contents with the values for your installation.Property Data type Description typeString Specifies the location, type, and version of the Deployment Manager template to use during deployment.
The YAML file includes two
typespecifications, one of which is commented out. Thetypespecification that is active by default specifies the template version aslatest. Thetypespecification that is commented out specifies a specific template version with a timestamp.If you need all of your deployments to use the same template version, use the
typespecification that includes the timestamp.instanceNameString The name of the VM instance on which SAP ASE will be installed. The name must be 13 characters or less and be specified in lowercase letters, numbers, or hyphens. instanceTypeString The type of Compute Engine virtual machine on which SAP ASE will be installed. If you are running SAP ASE with SAP NetWeaver on the same VM, select a machine type that includes enough CPUs and memory to support both systems. See the SAP NetWeaver planning guide. zoneString The zone in which you are deploying your SAP ASE. It must be in the same region that you selected for your subnetwork. subnetworkString The name of the subnetwork that you created in a previous step. If you are deploying to a shared VPC, specify this value as SHARED_VPC_PROJECT/SUBNETWORK. For example,myproject/network1.linuxImageString The name of the Linux operating- system image or image family that you are using with SAP ASE. To specify an image family, add the prefix family/to the family name. For example,family/rhel-7orfamily/sles-12-sp2-sap. To use a specific image, enter only the image name. For the list of available image families, see the Images page in the Cloud console.linuxImageProjectString The Google Cloud project that contains the image you are going to use. This project might be your own project or a Google Cloud image project, such as rhel-sap-cloudorsuse-sap-cloud. For a list of Google Cloud image projects, see the Images page in the Compute Engine documentation.aseSIDString The database instance ID. asesidSizeInteger The size in GB of /sybase/DBSID, which is the root directory of the database instance. In the deployed VM, this volume is labeledASE.asediagSizeInteger The size of /sybase/DBSID/sapdiag, which holds the diagnostic tablespace for SAPTOOLS.asesaptempSizeInteger The size of /sybase/DBSID/saptmp, which holds the database temporary table space.asesapdataSizeInteger The size of /sybase/DBSID/sapdata, which holds the database data files.aselogSizeInteger The size of /sybase/DBSIDlogdir, which holds the database transaction logs.asebackupSizeInteger The size of the /sybasebackupvolume. If set to0or omitted, then no disk is created.asesapdataSSDboolean The SSD toggle for the data drive. If set to true, then the data disk is SSD.aselogSSDboolean The SSD toggle for the log drive. If set to true, then the log disk is SSD.usrsapSizeInteger Required only if you are installing SAP ASE to run with SAP NetWeaver on the same VM instance. sapmntSizeInteger Required only if you are installing SAP ASE to run with SAP NetWeaver on the same VM instance. swapSizeInteger Required only if you are installing SAP ASE to run with SAP NetWeaver on the same VM instance. The following configuration file creates a VM that is configured to run both the SAP ASE database server and SAP NetWeaver. The configuration file directs Deployment Manager to deploy an
n1-standard-16VM that is running a SLES 12 SP2 operating system. The VM includes all of the directories that are required to run SAP ASE with SAP NetWeaver.resources: - name: sap_ase type: https://storage.googleapis.com/cloudsapdeploy/deploymentmanager/latest/dm-templates/sap_ase/sap_ase.py # # By default, this configuration file uses the latest release of the deployment # scripts for SAP on Google Cloud. To fix your deployments to a specific release # of the scripts, comment out the type property above and uncomment the type property below. # # type: https://storage.googleapis.com/cloudsapdeploy/deploymentmanager/202103310846/dm-templates/sap_ase/sap_ase.py # properties: instanceName: ex-vm-ase-lin instanceType: n1-standard-16 zone: us-central1-f subnetwork: example-sub-network linuxImage: family/sles-12-sp2-sap linuxImageProject: suse-sap-cloud aseSID: AS1 asesidSize: 10 asediagSize: 15 asesaptempSize: 20 asesapdataSize: 50 aselogSize: 30 asebackupSize: 100 asesapdataSSD: Yes aselogSSD: Yes usrsapSize: 15 sapmntSize: 15 swapSize: 24Create the VM instance:
gcloud deployment-manager deployments create DEPLOYMENT_NAME --config TEMPLATE_NAME.yaml
The above command invokes the Deployment Manager, which deploys the VM according to the specifications in your
template.yamlfile. The process might take a few minutes. To check the progress of your deployment, follow the steps in the next section.
Verifying deployment
To verify deployment, you check the deployment logs in Cloud Logging and check the configuration of the VM.
Check the logs
In the Google Cloud console, open Cloud Logging to monitor installation progress and check for errors.
Filter the logs:
Logs Explorer
In the Logs Explorer page, go to the Query pane.
From the Resource drop-down menu, select Global, and then click Add.
If you don't see the Global option, then in the query editor, enter the following query:
resource.type="global" "Deployment"Click Run query.
Legacy Logs Viewer
- In the Legacy Logs Viewer page, from the basic selector menu, select Global as your logging resource.
Analyze the filtered logs:
- If
"--- Finished"is displayed, then the deployment processing is complete and you can proceed to the next step. If you see a quota error:
On the IAM & Admin Quotas page, increase any of your quotas that do not meet the SAP ASE requirements that are listed in the SAP ASE planning guide.
On the Deployment Manager Deployments page, delete the deployment to clean up the VMs and persistent disks from the failed installation.
Rerun your deployment.
- If
Check the configuration of the VM
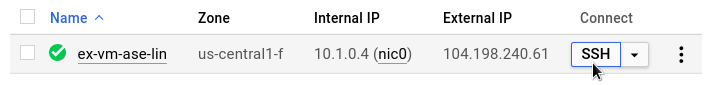
After the SAP ASE system deploys without errors, connect to your VM by using SSH. From the Compute Engine VM instances page, you can click the SSH button for your VM instance, or you can use your preferred SSH method.
Switch to the root user.
sudo su -
At the command prompt, enter
df -h. Ensure that you see output similar to the following, such as the//sybase/DBSID/sapdatadirectory.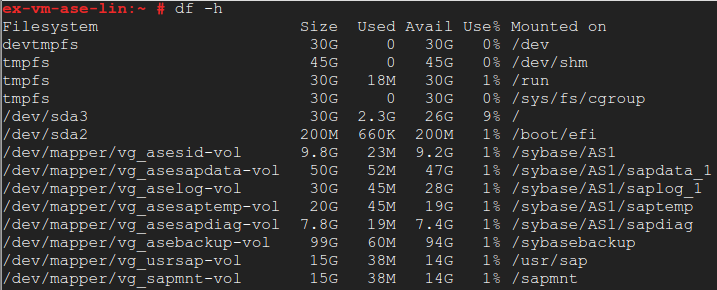
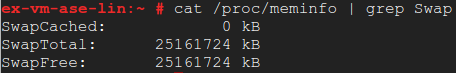
Confirm that the swap directory was created by entering the following command:
cat /proc/meminfo | grep Swap
You should see results similar to the following example:
If any of the validation steps show that the installation failed:
- Correct the error.
- On the Deployments page, delete the deployment to clean up the VMs and persistent disks from the failed installation.
- Rerun your deployment.
Installing the database
Now that your operating system is configured, you can install your SAP ASE database:
To install SAP ASE on your VM:
- Establish an SSH connection to your Linux-based VM.
- Download or copy your SAP ASE installation media from SAP to your VM.
- Prepare your SAP ASE SySAM license file or license server for use with the installation.
- Install the SAP ASE database. See the SAP ASE Installation and Upgrade Guide for Linux for guidance.
Validate your installation of Google Cloud's Agent for SAP
After you have deployed a VM and installed your SAP system, validate that Google Cloud's Agent for SAP is functioning properly.
Verify that Google Cloud's Agent for SAP is running
To verify that the agent is running, follow these steps:
Establish an SSH connection with your Compute Engine instance.
Run the following command:
systemctl status google-cloud-sap-agent
If the agent is functioning properly, then the output contains
active (running). For example:google-cloud-sap-agent.service - Google Cloud Agent for SAP Loaded: loaded (/usr/lib/systemd/system/google-cloud-sap-agent.service; enabled; vendor preset: disabled) Active: active (running) since Fri 2022-12-02 07:21:42 UTC; 4 days ago Main PID: 1337673 (google-cloud-sa) Tasks: 9 (limit: 100427) Memory: 22.4 M (max: 1.0G limit: 1.0G) CGroup: /system.slice/google-cloud-sap-agent.service └─1337673 /usr/bin/google-cloud-sap-agent
If the agent isn't running, then restart the agent.
Verify that SAP Host Agent is receiving metrics
To verify that the infrastructure metrics are collected by Google Cloud's Agent for SAP and sent correctly to the SAP Host Agent, follow these steps:
- In your SAP system, enter transaction
ST06. In the overview pane, check the availability and content of the following fields for the correct end-to-end setup of the SAP and Google monitoring infrastructure:
- Cloud Provider:
Google Cloud Platform - Enhanced Monitoring Access:
TRUE - Enhanced Monitoring Details:
ACTIVE
- Cloud Provider:
Performing post-deployment tasks
Before using your SAP ASE instance, we recommend that you perform the following post-deployment steps:
- Update your SAP ASE software with the latest patches, if available.
- Install any additional components.
- Configure and back up your new SAP ASE database.
For additional post-deployment guidance, see the Post-installation Tasks section of the SAP ASE Installation and Upgrade Guide for Linux.
Troubleshooting
This section contains information about how to correct common issues.
Troubleshooting connecting to your VM
If you are having issues connecting to your VM through SSH, then make sure that
you have created a firewall rule to open port 22 on the Google Cloud
network you are using.
For other possible issues, see Known issues for SSH from the browser.
