在 BigQuery 中使用政策標記的最佳做法
本頁面說明在 BigQuery 中使用政策標記的最佳做法。使用政策標記,在您使用資料欄層級存取權控管機制或動態資料遮蓋時,定義資料存取權。
如要瞭解如何在資料欄上設定政策標記,請參閱「在資料欄上設定政策標記」。
建構資料類別階層
建立符合業務需求的資料類別階層。
首先,請考量貴機構處理哪些類型的資料。通常機構管理的資料類別數量不多。舉例來說,機構組織可能會有以下資料類別:
- 個人識別資訊資料
- 財務資料
- 查看客戶訂單記錄
單一資料類別可透過政策代碼套用至多個資料欄。您應利用這層級的抽象化,只需使用少數政策標記即可有效管理多個資料欄。
其次,請思考是否有群組需要不同的資料類別存取權。舉例來說,某個群組需要存取業務敏感資料,例如收入和客戶記錄。另一個群組則需要存取電話號碼和地址等個人識別資料 (PII)。
請注意,您可以在樹狀結構中將政策代碼分組。有時建立包含所有其他政策標記的根政策標記會很有幫助。
下圖為分類法範例。這個階層會將所有資料類型分組為三個頂層政策代碼:「高」、「中」和「低」。
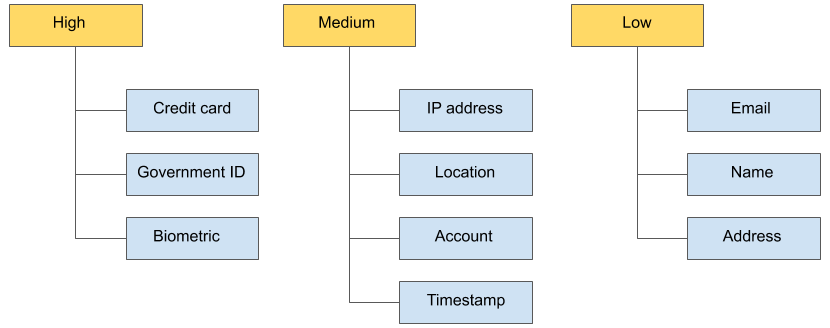
每個頂層政策標記都包含葉節政策標記。舉例來說,高政策代碼包含信用卡、政府身分證和生物特徵政策代碼。中和 低 也同樣有葉政策標記。
這種結構有幾項優點:
您可以一次授予整個政策代碼群組存取權。舉例來說,您可以授予Data Catalog 精細讀取者角色,並將其設為低層級。
您可以將政策標記從一個層級移至另一個層級。舉例來說,您可以將「Address」從「Low」等級移至「Medium」等級,進一步限制存取權,而無須重新分類所有「Address」欄。
透過這項精細的存取權,您只需控制少數幾個資料分類政策標記,即可管理多個資料欄的存取權。
如要進一步瞭解 BigQuery 中的政策標記,請參閱:

