Raccogliere i dati DNS di Microsoft Windows
Questo documento:
- Descrive l'architettura di deployment e i passaggi di installazione, oltre a qualsiasi configurazione richiesta che produca log supportati dal parser di Google Security Operations per gli eventi DNS di Microsoft Windows. Per una panoramica dell'importazione dati in Google Security Operations, consulta Importazione dei dati in Google Security Operations.
- Include informazioni su come il parser mappa i campi nel log originale ai campi del modello di dati unificato di Google Security Operations.
In base all'architettura di deployment, configura l'agente Bindplane o l'agente NXLog per importare i log DNS di Windows in Google Security Operations. Ti consigliamo di utilizzare Bindplane Agent per inoltrare i log DNS di Windows a Google Security Operations.
Le informazioni in questo documento si applicano al parser con l'etichetta di importazione WINDOWS_DNS. L'etichetta di importazione identifica il parser che normalizza i dati di log non elaborati in formato UDM strutturato.
Prima di iniziare
Prima di configurare Bindplane Agent o NXLog Agent, completa le seguenti attività:
- Configura il server DNS Microsoft Windows. Per ulteriori informazioni, consulta Installare e configurare DNS Server su Windows Server.
- Attiva la registrazione diagnostica DNS sul server DNS Windows. Per ulteriori informazioni, consulta Log e diagnostica DNS.
- Configura tutti i sistemi con il fuso orario UTC.
- Esaminare i dispositivi e le versioni supportati
- Esaminare i tipi di log supportati
Esamina i dispositivi e le versioni supportati
Il parser di Google Security Operations supporta i log delle seguenti versioni di Microsoft Windows Server. Microsoft Windows Server viene rilasciato con le seguenti versioni: Foundation, Essentials, Standard e Datacenter. Lo schema degli eventi dei log generati da ogni versione non è diverso.
- Microsoft Windows Server 2019
- Microsoft Windows Server 2016
Microsoft Windows Server 2012 R2
Il parser di Google Security Operations supporta i log raccolti da NXLog Enterprise Edition.
Esamina i tipi di log supportati
Il parser di Google Security Operations supporta i seguenti tipi di log generati dai server DNS di Microsoft Windows. Per ulteriori informazioni su questi tipi di log, consulta la documentazione su logging e diagnostica DNS. Il parser supporta i log generati con testo in lingua inglese e non è supportato con i log generati in lingue diverse dall'inglese.
- Log di controllo: per una descrizione di questo tipo di log, vedi Eventi di controllo.
- Log di Analytics: per una descrizione di questo tipo di log, consulta Eventi di Analytics.
- Configura i server DNS Microsoft Windows. Per ulteriori informazioni, consulta Installare e attivare i log di diagnostica DNS.
Configurare l'agente Bindplane
Ti consigliamo di utilizzare Bindplane Agent per inoltrare i log DNS di Windows a Google SecOps.
- Installa l'agente Bindplane su ogni server DNS Windows. Per ulteriori informazioni sull'installazione di Bindplane Agent, consulta le istruzioni di installazione di Bindplane Agent.
Crea un file di configurazione Bindplane Agent con i seguenti contenuti:
receivers: windowseventlog/dns_log: channel: Microsoft-Windows-DNSServer/Audit raw: true processors: batch: exporters: chronicle/dns_log: endpoint: https://malachiteingestion-pa.googleapis.com creds: '{ "type": "service_account", "project_id": "malachite-projectname", "private_key_id": `PRIVATE_KEY_ID`, "private_key": `PRIVATE_KEY`, "client_email":"`SERVICE_ACCOUNT_NAME`@malachite-`PROJECT_ID`.`SERVICE_ACCOUNT_DOMAIN`", "client_id": `CLIENT_ID`, "auth_uri": "https://accounts.google.com/o/oauth2/auth", "token_uri": "https://oauth2.googleapis.com/token", "auth_provider_x509_cert_url":"https://www.googleapis.com/oauth2/v1/certs", "client_x509_cert_url": "https://www.googleapis.com/robot/v1/metadata/x509/`SERVICSERVICE_ACCOUNT_NAME`%40malachite-`PROJECT_ID`.`SERVICE_ACCOUNT_DOMAIN`", "universe_domain": "googleapis.com" }' log_type: 'WINDOWS_DNS' override_log_type: false raw_log_field: body customer_id: `CUSTOMER_ID` service: pipelines: logs/dns: receivers: - windowseventlog/dns_log processors: [batch] exporters: [chronicle/dns_log]Sostituisci
PRIVATE_KEY_ID,PRIVATE_KEYSERVICSERVICE_ACCOUNT_NAME,PROJECT_ID,CLIENT_ID,SERVICE_ACCOUNT_DOMAINeCUSTOMER_IDcon i rispettivi valori del file JSON dell'account di servizio che puoi scaricare dalla Google Cloud piattaforma. Per ulteriori informazioni sulle chiavi degli account di servizio, consulta la documentazione su come creare ed eliminare le chiavi degli account di servizio.Per avviare il servizio dell'agente Bindplane (in precedenza observerIQ), seleziona Servizi > Avanzate > il servizio Bindplane > Avvia.
Configurare l'agente NXLog e il forwarder di Google Security Operations
Il seguente diagramma mostra un'architettura in cui sono installati agenti NXLog per raccogliere e inviare eventi DNS di Microsoft Windows a Google SecOps. Confronta queste informazioni con il tuo ambiente per assicurarti che questi componenti siano installati. Il tuo deployment potrebbe essere diverso da questa rappresentazione.
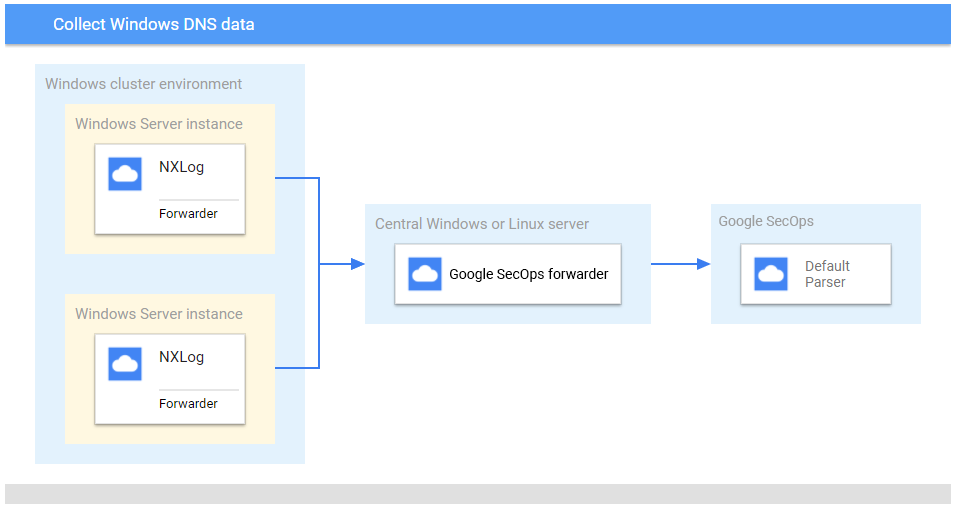
Se utilizzi NXLog Agent anziché Bindplane Agent, completa i seguenti prerequisiti: - Installa NXLog sui server Microsoft Windows in cluster per raccogliere e inoltrare i log al server Microsoft Windows o Linux centrale. - Installa il forwarder Google SecOps sul server Microsoft Windows o Linux centrale.
- Installa NXLog su ogni server DNS Microsoft Windows. Segui la documentazione di NXLog.
Crea un file di configurazione per ogni istanza NXLog. Utilizza il modulo di input im_etw per estrarre i log di analisi DNS e il modulo di input im_msvistalog per gli audit log.
- Per ulteriori informazioni sul modulo di input im_etw, consulta Event Tracing for Microsoft Windows (im_etw), incluse informazioni su configurazione di NXLog per il DNS di Microsoft Windows.
- Per ulteriori informazioni sul modulo di input im_msvistalog, consulta Log eventi per Microsoft Windows 2008/Vista e versioni successive (im_msvistalog).
Ecco un esempio di configurazione di NXLog. Sostituisci i valori
<hostname>e<port>con le informazioni sul server Linux o Microsoft Windows centrale. Per convertire e analizzare facoltativamente i log in JSON anziché in XML, modifica la rigaExec to_xml();inExec to_json();. Per ulteriori informazioni, consulta la documentazione di NXLog relativa al modulo om_tcp.define ROOT C:\Program Files\nxlog define WINDNS_OUTPUT_DESTINATION_ADDRESS <hostname> define WINDNS_OUTPUT_DESTINATION_PORT <port> Moduledir %ROOT%\modules CacheDir %ROOT%\data Pidfile %ROOT%\data\nxlog.pid SpoolDir %ROOT%\data LogFile %ROOT%\data\nxlog.log <Extension syslog> Module xm_syslog </Extension> # To collect XML logs, use the below NXLog module <Extension xml> Module xm_xml </Extension> # To collect JSON logs, use the below NXLog module <Extension json> Module xm_json </Extension> <Input eventlog> Module im_etw Provider Microsoft-Windows-DNSServer </Input> <Input auditeventlog> Module im_msvistalog <QueryXML> <QueryList> <Query Id="0" Path="Microsoft-Windows-DNSServer/Audit"> <Select Path="Microsoft-Windows-DNSServer/Audit">*</Select> </Query> </QueryList> </QueryXML> </Input> <Output out_chronicle_windns> Module om_tcp Host %WINDNS_OUTPUT_DESTINATION_ADDRESS% Port %WINDNS_OUTPUT_DESTINATION_PORT% Exec $EventTime = integer($EventTime) / 1000; Exec $EventReceivedTime = integer($EventReceivedTime) / 1000; Exec to_xml(); # To collect JSON, use to_json() </Output> <Route analytical_windns_to_chronicle> Path eventlog => out_chronicle_windns </Route> <Route audit_windns_to_chronicle> Path auditeventlog => out_chronicle_windns </Route>Installa il forwarder di Google Security Operations sul server Microsoft Windows o Linux centrale. Per informazioni sull'installazione e sulla configurazione del forwarder, consulta Installazione e configurazione del forwarder su Linux o Installazione e configurazione del forwarder su Microsoft Windows.
Configura il forwarder di Google Security Operations per inviare i log a Google Security Operations. Ecco un esempio di configurazione dell'agente di inoltro.
- syslog: common: enabled: true data_type: WINDOWS_DNS batch_n_seconds: 10 batch_n_bytes: 1048576 tcp_address: 0.0.0.0:10518 connection_timeout_sec: 60
Formati dei log DNS di Windows supportati
L'analizzatore DNS di Windows supporta i log nei formati JSON, XML, SYSLOG + KV e SYSLOG.
Log di esempio DNS di Windows supportati
JSON:
{ "EventTime": 1640073312000, "Hostname": "WIN-TEST", "Keywords": "4611686018427912192", "EventType": "INFO", "SeverityValue": 2, "Severity": "INFO", "EventID": 514, "SourceName": "Microsoft-Windows-DNSServer", "ProviderGuid": "{EB79061A-A566-4698-9119-3ED2807060E7}", "Version": 0, "TaskValue": 5, "OpcodeValue": 0, "RecordNumber": 1, "ExecutionProcessID": 2244, "ExecutionThreadID": 1448, "Channel": "Microsoft-Windows-DNSServer/Audit", "Domain": "DNSTEST", "AccountName": "Administrator", "UserID": "S-1-2-3", "AccountType": "User", "Message": "The zone dnstest.local was updated. The SecondaryServers setting has been set to deny zone transfers. [virtualization instance: .].", "Category": "ZONE_OP", "Opcode": "Info", "Zone": "dnstest.local", "PropertyKey": "SecondaryServers", "NewValue": "deny zone transfers", "VirtualizationID": ".", "EventReceivedTime": 1640073312001, "SourceModuleName": "auditeventlog", "SourceModuleType": "im_msvistalog" }XML:
<Event> <SourceName>Microsoft-Windows-DNSServer</SourceName> <ProviderGuid>{EB79061A-A566-4698-9119-3ED2807060E7} </ProviderGuid> <EventID>256</EventID> <Version>0</Version> <ChannelID>16</ChannelID> <OpcodeValue>0</OpcodeValue> <TaskValue>1</TaskValue> <Keywords>9223372036854775809</Keywords> <EventTime>1640073312000</EventTime> <ExecutionProcessID>2476</ExecutionProcessID> <ExecutionThreadID>3972</ExecutionThreadID> <EventType>INFO</EventType> <SeverityValue>2</SeverityValue> <Severity>INFO</Severity> <Hostname>WIN-TEST</Hostname> <Domain>NT AUTHORITY</Domain> <AccountName>SYSTEM</AccountName> <UserID>S-1-2-3</UserID> <AccountType>User</AccountType> <Flags>256</Flags> <TCP>0</TCP> <InterfaceIP>198.51.100.5</InterfaceIP> <Source>198.51.100.0</Source> <RD>1</RD> <QNAME>www.google.com.</QNAME> <QTYPE>1</QTYPE> <XID>55835</XID> <Port>50843</Port> <BufferSize>43</BufferSize> <PacketData>0xDA1B0100000100000000000006766F727465780464617461096D6963726F736F667403636F6D0000010001</PacketData> <AdditionalInfo>.</AdditionalInfo> <EventReceivedTime>1640073312001</EventReceivedTime> <SourceModuleName>eventlog</SourceModuleName> <SourceModuleType>im_etw</SourceModuleType> </Event>SYSLOG + KV:
UDP question info at 00000027580C8220 Socket = 556 Remote addr 198.51.100.1, port 60766 Time Query=559415, Queued=0, Expire=0 Buf length = 0x0fa0 (4000) Msg length = 0x0044 (68) Message: XID 0x49d7 Flags 0x0100 QR 0 (QUESTION) OPCODE 0 (QUERY) AA 0 TC 0 RD 1 RA 0 Z 0 CD 0 AD 0 RCODE 0 (NOERROR) QCOUNT 1 ACOUNT 0 NSCOUNT 0 ARCOUNT 0 QUESTION SECTION: Offset = 0x000c, RR count = 0 Name \"(5)_ldap(4)_tcp(4)INMS(6)_sites(14)ForestDnsZones(8)genmills(3)com(0)\" QTYPE SRV (33) QCLASS 1 ANSWER SECTION: empty AUTHORITY SECTION: empty ADDITIONAL SECTION: emptySYSLOG
29.11.2023 14:13:11 1B14 PACKET 00000274481BF1B0 UDP Snd 198.51.100.0 14fc Q [0001 D NOERROR] A (23)win-dns(10)westeurope(8)test(5)azure(3)com(0)
Riferimento alla mappatura dei campi: campi dei log del dispositivo ai campi UDM
Questa sezione descrive in che modo il parser mappa i campi dei log del dispositivo originale ai campi Unified Data Model (UDM).
Campi comuni
| Campo NXLog | Campo UDM | Commento |
|---|---|---|
SourceName |
metadata.vendor_name = "Microsoft"metadata.product_name = "Windows DNS Server" |
|
EventID |
security_result.rule_name |
Stored as "EventID: %{EventID}". In events with Error and Warning level,
the field is_alert is set to true. |
Severity |
security_result.severity |
The values are mapped to the UDM field enum as follows: 0 (None) - UNKNOWN_SEVERITY1 (Critical) - INFORMATIONAL2 (Error) - ERROR3 (Warning) - ERROR4 (Informational) - INFORMATIONAL5 (Verbose) - INFORMATIONAL |
EventTime |
metadata.event_timestamp |
|
ExecutionProcessID |
principal.process.pid / target.process.pid |
Value stored in target.process.pid for the following Event IDs 256, 259, 261, 263, 266, 268, 270, 272, 273, 275, 278, 279, 280.Value stored in principal.process.pid for all other Event IDs. |
Channel |
metadata.product_event_type |
|
Hostname |
principal.hostname / target.hostname |
Value stored in target.hostname for the following Event IDs: 256, 259, 261, 263, 266, 268, 270, 272, 273, 275, 278, 279, 280.Value stored in principal.hostname from all other Event IDs. |
UserID |
principal.user.windows_sid / target.user.windows_sid |
Stored in target.user.windows_sid for the following Event IDs: 256, 259, 261, 263, 266, 268, 270, 272,273, 275, 278, 279, 280.Stored in principal.user.windows_sid for all other Event IDs |
Log di analisi
| Campo del log originale | Campo UDM | Commento |
|---|---|---|
AA |
network.dns.authoritative |
|
Destination |
target.ip / principal.ip |
Populated in either principal and target. |
InterfaceIP |
target.ip / principal.ip |
Stores DNS Server's IP address in target.ip for following Event IDs, 256, 259, 261, 263, 266, 268, 270, 272, 273, 275, 278, 279, 280.Stored in principal.ip for all other Event IDs (DNS response). |
PacketData |
network.dns.answers.binary_data |
|
Port |
target.port / principal.port |
|
QNAME |
network.dns.questions.name, target.hostname |
Do not store QNAME in target.hostname for following Event IDs: 256, 259, 261, 263, 266, 268, 270, 272, 273, 275, 278, 279, and 280 |
QTYPE |
network.dns.questions.type |
|
RCODE |
network.dns.response_code |
|
RD |
network.dns.recursion_desired |
|
Reason |
security_result.summary |
|
Source |
principal.ip / target.ip |
Source IPv4/IPv6 address of the machine that initiated the DNS request. Stored in target.ip for Event ID 274. Stored in target.ip for Event ID 265 and 269. InterfaceIP contains the secondary server's IP address (principal) and Source (target) is the primary server's IP address. |
TCP |
network.ip_protocol |
|
XID |
network.dns.id |
Audit log
| Campo del log originale | Campo UDM | Nota |
|---|---|---|
Name |
target.resource.name |
Value is collected from events with Event ID 512. |
Policy |
target.resource.name |
Value is collected from events with Event ID 577, 578, 579, 580, 581, and 582, which are mapped to the SETTING_* event types. |
QNAME |
network.dns.questions.name, target.hostname |
|
QTYPE |
network.dns.questions.type |
|
RecursionScope |
target.resource.name |
Value is collected from events with Event IDs mapped to SETTING_* event types. |
Scope |
target.resource.name |
Value is collected from events with Event IDs mapped to SETTING_* event types. |
Setting |
target.resource.name |
Value is collected from events with Event IDs mapped to SETTING_* event types. |
Source |
principal.ip |
|
Zone |
target.resource.name |
Value is collected from events with Event IDs mapped to SETTING_* event types. |
ZoneScope |
target.resource.name |
Value is collected from events with Event IDs mapped to SETTING_* event types. |
Log im_file di SourceModuleType
| Campo del log originale | Campo UDM | Nota |
|---|---|---|
EventReceivedTime |
metadata.collected_timestamp |
|
Expire |
about.labels (deprecated) |
|
Expire |
additional.fields |
|
InternalPacketIdentifier |
about.labels (deprecated) |
|
InternalPacketIdentifier |
additional.fields |
|
|
about.labels (deprecated) |
Grok: Extracted the internal_packet_identifier field from the raw log and then mapped the internal_packet_identifier field to the about.labels UDM field. |
|
additional.fields |
Grok: Extracted the internal_packet_identifier field from the raw log and then mapped the internal_packet_identifier field to the additional.fields UDM field. |
packet_identifier |
about.labels (deprecated) |
|
packet_identifier |
additional.fields |
|
LogInfo |
metadata.description |
|
PortNum |
principal.port |
|
Queued |
about.labels (deprecated) |
|
Queued |
additional.fields |
|
Socket |
principal.labels (deprecated) |
|
Socket |
additional.fields |
|
TimeQuery |
about.labels (deprecated) |
|
TimeQuery |
additional.fields |
|
BufLen |
about.labels (deprecated) |
|
BufLen |
additional.fields |
|
Opcode |
network.dns.opcode |
If the Opcode log field value is equal to Q, then the network.dns.opcode UDM field is set to 0.Else, if the Opcode log field value is equal to I, then the network.dns.opcode UDM field is set to 1.Else, if the Opcode log field value is equal to S, then the network.dns.opcode UDM field is set to 2.Else, if the Opcode log field value is equal to N, then the network.dns.opcode UDM field is set to 4.Else, if the Opcode log field value is equal to U, then the network.dns.opcode UDM field is set to 5. |
opcode |
network.dns.opcode |
Grok: Extracted the opcode field from the raw log.If the opcode field value is equal to Q, then the network.dns.opcode UDM field is set to 0.Else, if the opcode field value is equal to I, then the network.dns.opcode UDM field is set to 1.Else, if the opcode field value is equal to S, then the network.dns.opcode UDM field is set to 2.Else, if the opcode field value is equal to N, then the network.dns.opcode UDM field is set to 4.Else, if the opcode field value is equal to U, then the network.dns.opcode UDM field is set to 5. |
Protocol |
network.ip_protocol |
If the Protocol log field value is equal to 1 or ICMP, then the network.ip_protocol UDM field is set to ICMP.Else, if the Protocol log field value is equal to 2 or IGMP, then the network.ip_protocol UDM field is set to IGMP.Else, if the Protocol log field value is equal to 6 or TCP, then the network.ip_protocol UDM field is set to TCP.Else, if the Protocol log field value is equal to 17 or UDP, then the network.ip_protocol UDM field is set to UDP.Else, if the Protocol log field value is equal to 41 or IP6IN4, then the network.ip_protocol UDM field is set to IP6IN4.Else, if the Protocol log field value is equal to 47 or GRE, then the network.ip_protocol UDM field is set to GRE.Else, if the Protocol log field value is equal to 50 or ESP, then the network.ip_protocol UDM field is set to ESP.Else, if the Protocol log field value is equal to 88 or EIGRP, then the network.ip_protocol UDM field is set to EIGRP.Else, if the Protocol log field value is equal to 97 or ETHERIP, then the network.ip_protocol UDM field is set to ETHERIP.Else, if the Protocol log field value is equal to 103 or PIM, then the network.ip_protocol UDM field is set to PIM.Else, if the Protocol log field value is equal to 112 or VRRP, then the network.ip_protocol UDM field is set to VRRP. |
|
network.ip_protocol |
Grok: Extracted the ip_protocol field from the raw log.If the ip_protocol field value is equal to 1 or ICMP, then the network.ip_protocol UDM field is set to ICMP.Else, if the ip_protocol field value is equal to 2 or IGMP, then the network.ip_protocol UDM field is set to IGMP.Else, if the ip_protocol field value is equal to 6 or TCP, then the network.ip_protocol UDM field is set to TCP.Else, if the ip_protocol field value is equal to 17 or UDP, then the network.ip_protocol UDM field is set to UDP.Else, if the ip_protocol field value is equal to 41 or IP6IN4, then the network.ip_protocol UDM field is set to IP6IN4.Else, if the ip_protocol field value is equal to 47 or GRE, then the network.ip_protocol UDM field is set to GRE.Else, if the ip_protocol field value is equal to 50 or ESP, then the network.ip_protocol UDM field is set to ESP.Else, if the ip_protocol field value is equal to 88 or EIGRP, then the network.ip_protocol UDM field is set to EIGRP.Else, if the ip_protocol field value is equal to 97 or ETHERIP, then the network.ip_protocol UDM field is set to ETHERIP.Else, if the ip_protocol field value is equal to 103 or PIM, then the network.ip_protocol UDM field is set to PIM.Else, if the ip_protocol field value is equal to 112 or VRRP, then the network.ip_protocol UDM field is set to VRRP. |
|
network.dns.response_code |
Grok: Extracted the dns_response_code field from the raw log.If the dns_response_code field value is equal to NOERROR, then the network.dns.response_code UDM field is set to 0.Else, if the dns_response_code field value is equal to FORMERR, then the network.dns.response_code UDM field is set to 1.Else, if the dns_response_code field value is equal to SERVFAIL, then the network.dns.response_code UDM field is set to 2.Else, if the dns_response_code field value is equal to NXDOMAIN, then the network.dns.response_code UDM field is set to 3.Else, if the dns_response_code field value is equal to NOTIMP, then the network.dns.response_code UDM field is set to 4.Else, if the dns_response_code field value is equal to REFUSED, then the network.dns.response_code UDM field is set to 5.Else, if the dns_response_code field value is equal to YXDOMAIN, then the network.dns.response_code UDM field is set to 6.Else, if the dns_response_code field value is equal to YXRRSET, then the network.dns.response_code UDM field is set to 7.Else, if the dns_response_code field value is equal to NXRRSET, then the network.dns.response_code UDM field is set to 8.Else, if the dns_response_code field value is equal to NOTAUTH, then the network.dns.response_code UDM field is set to 9.Else, if the dns_response_code field value is equal to NOTZONE, then the network.dns.response_code UDM field is set to 10.Else, if the dns_response_code field value is equal to DSOTYPENI, then the network.dns.response_code UDM field is set to 11.Else, if the dns_response_code field value is equal to BADVERS, then the network.dns.response_code UDM field is set to 16.Else, if the dns_response_code field value is equal to BADSIG, then the network.dns.response_code UDM field is set to 16.Else, if the dns_response_code field value is equal to BADKEY, then the network.dns.response_code UDM field is set to 17.Else, if the dns_response_code field value is equal to BADTIME, then the network.dns.response_code UDM field is set to 18.Else, if the dns_response_code field value is equal to BADMODE, then the network.dns.response_code UDM field is set to 19.Else, if the dns_response_code field value is equal to BADNAME, then the network.dns.response_code UDM field is set to 20.Else, if the dns_response_code field value is equal to BADALG, then the network.dns.response_code UDM field is set to 21.Else, if the dns_response_code field value is equal to BADTRUNC, then the network.dns.response_code UDM field is set to 22.Else, if the dns_response_code field value is equal to BADCOOKIE, then the network.dns.response_code UDM field is set to 23. |
|
network.dns.authoritative |
Grok: Extracted the authoritative field from the raw log.If the authoritative field value is equal to A, then the network.dns.authoritative UDM field is set to true. |
|
network.dns.truncated |
Grok: Extracted the truncated field from the raw log.If the truncated field value is equal to T, then the network.dns.truncated UDM field is set to true. |
|
network.dns.recursion_desired |
Grok: Extracted the recursion_desired field from the raw log.If the recursion_desired field value is equal to D, then the network.dns.recursion_desired UDM field is set to true. |
|
network.dns.recursion_available |
Grok: Extracted the recursion_available field from the raw log.If the recursion_available field value is equal to R, then the network.dns.recursion_available UDM field is set to true. |
QueryType |
network.dns.response |
If the QueryType log field value is equal to R, then the network.dns.response UDM field is set to true.Else, the network.dns.response UDM field is set to false. |
req_or_resp |
network.dns.response |
Grok: Extracted the req_or_resp field from the raw log. If the req_or_resp field value is equal to R, then the network.dns.response UDM field is set to true.Else, the network.dns.response UDM field is set to false. |
QuestionName |
network.dns.questions.name, target.hostname |
|
domain |
network.dns.questions.name, target.hostname |
Grok: Extracted the domain field from the raw log and then mapped the domain field to the network.dns.questions.name and target.hostname UDM field. |
QuestionType |
network.dns.questions.type |
If the QuestionType field value is equal to A, then the network.dns.question.type UDM field is set to 1.Else, if the QuestionType field value is equal to NS, then the network.dns.question.type UDM field is set to 2.Else, if the QuestionType field value is equal to MD, then the network.dns.question.type UDM field is set to 3.Else, if the QuestionType field value is equal to MF, then the network.dns.question.type UDM field is set to 4.Else, if the QuestionType field value is equal to CNAME, then the network.dns.question.type UDM field is set to 5.Else, if the QuestionType field value is equal to SOA, then the network.dns.question.type UDM field is set to 6.Else, if the QuestionType field value is equal to MB, then the network.dns.question.type UDM field is set to 7.Else, if the QuestionType field value is equal to MG, then the network.dns.question.type UDM field is set to 8.Else, if the QuestionType field value is equal to MR, then the network.dns.question.type UDM field is set to 9.Else, if the QuestionType field value is equal to NULL, then the network.dns.question.type UDM field is set to 10.Else, if the QuestionType field value is equal to WKS, then the network.dns.question.type UDM field is set to 11.Else, if the QuestionType field value is equal to PTR, then the network.dns.question.type UDM field is set to 12.Else, if the QuestionType field value is equal to HINFO, then the network.dns.question.type UDM field is set to 13.Else, if the QuestionType field value is equal to MINFO, then the network.dns.question.type UDM field is set to 14.Else, if the QuestionType field value is equal to MX, then the network.dns.question.type UDM field is set to 15.Else, if the QuestionType field value is equal to TXT, then the network.dns.question.type UDM field is set to 16.Else, if the QuestionType field value is equal to RP, then the network.dns.question.type UDM field is set to 17.Else, if the QuestionType field value is equal to AFSDB, then the network.dns.question.type UDM field is set to 18.Else, if the QuestionType field value is equal to X25, then the network.dns.question.type UDM field is set to 19.Else, if the QuestionType field value is equal to ISDN, then the network.dns.question.type UDM field is set to 20.Else, if the QuestionType field value is equal to RT, then the network.dns.question.type UDM field is set to 21.Else, if the QuestionType field value is equal to NSAP, then the network.dns.question.type UDM field is set to 22.Else, if the QuestionType field value is equal to NSAP-PT, then the network.dns.question.type UDM field is set to 23.Else, if the QuestionType field value is equal to SIG, then the network.dns.question.type UDM field is set to 24.Else, if the QuestionType field value is equal to KEY, then the network.dns.question.type UDM field is set to 25.Else, if the QuestionType field value is equal to PX, then the network.dns.question.type UDM field is set to 26.Else, if the QuestionType field value is equal to GPOS, then the network.dns.question.type UDM field is set to 27.Else, if the QuestionType field value is equal to AAAA, then the network.dns.question.type UDM field is set to 28.Else, if the QuestionType field value is equal to LOC, then the network.dns.question.type UDM field is set to 29.Else, if the QuestionType field value is equal to NXT, then the network.dns.question.type UDM field is set to 30.Else, if the QuestionType field value is equal to EID, then the network.dns.question.type UDM field is set to 31.Else, if the QuestionType field value is equal to NIMLOC, then the network.dns.question.type UDM field is set to 32.Else, if the QuestionType field value is equal to SRV, then the network.dns.question.type UDM field is set to 33.Else, if the QuestionType field value is equal to ATMA, then the network.dns.question.type UDM field is set to 34.Else, if the QuestionType field value is equal to NAPTR, then the network.dns.question.type UDM field is set to 35.Else, if the QuestionType field value is equal to KX, then the network.dns.question.type UDM field is set to 36.Else, if the QuestionType field value is equal to CERT, then the network.dns.question.type UDM field is set to 37.Else, if the QuestionType field value is equal to A6, then the network.dns.question.type UDM field is set to 38.Else, if the QuestionType field value is equal to DNAME, then the network.dns.question.type UDM field is set to 39.Else, if the QuestionType field value is equal to SINK, then the network.dns.question.type UDM field is set to 40.Else, if the QuestionType field value is equal to OPT, then the network.dns.question.type UDM field is set to 41.Else, if the QuestionType field value is equal to APL, then the network.dns.question.type UDM field is set to 42.Else, if the QuestionType field value is equal to DS, then the network.dns.question.type UDM field is set to 43.Else, if the QuestionType field value is equal to SSHFP, then the network.dns.question.type UDM field is set to 44.Else, if the QuestionType field value is equal to IPSECKE, then the network.dns.question.type UDM field is set to 45.Else, if the QuestionType field value is equal to RRSIG, then the network.dns.question.type UDM field is set to 46.Else, if the QuestionType field value is equal to NSEC, then the network.dns.question.type UDM field is set to 47.Else, if the QuestionType field value is equal to DNSKEY, then the network.dns.question.type UDM field is set to 48.Else, if the QuestionType field value is equal to DHCID, then the network.dns.question.type UDM field is set to 49.Else, if the QuestionType field value is equal to NSEC3, then the network.dns.question.type UDM field is set to 50.Else, if the QuestionType field value is equal to NSEC3PA, then the network.dns.question.type UDM field is set to 51.Else, if the QuestionType field value is equal to TLSA, then the network.dns.question.type UDM field is set to 52.Else, if the QuestionType field value is equal to SMIMEA, then the network.dns.question.type UDM field is set to 53.Else, if the QuestionType field value is equal to UNASSIG, then the network.dns.question.type UDM field is set to 54.Else, if the QuestionType field value is equal to HIP, then the network.dns.question.type UDM field is set to 55.Else, if the QuestionType field value is equal to NINFO, then the network.dns.question.type UDM field is set to 56.Else, if the QuestionType field value is equal to RKEY, then the network.dns.question.type UDM field is set to 57.Else, if the QuestionType field value is equal to TALINK, then the network.dns.question.type UDM field is set to 58.Else, if the QuestionType field value is equal to CDS, then the network.dns.question.type UDM field is set to 59.Else, if the QuestionType field value is equal to CDNSKEY, then the network.dns.question.type UDM field is set to 60.Else, if the QuestionType field value is equal to OPENPGP, then the network.dns.question.type UDM field is set to 61.Else, if the QuestionType field value is equal to CSYNC, then the network.dns.question.type UDM field is set to 62.Else, if the QuestionType field value is equal to ZONEMD, then the network.dns.question.type UDM field is set to 63.Else, if the QuestionType field value is equal to SVCB, then the network.dns.question.type UDM field is set to 64.Else, if the QuestionType field value is equal to HTTPS, then the network.dns.question.type UDM field is set to 65.Else, if the QuestionType field value is equal to SPF, then the network.dns.question.type UDM field is set to 99.Else, if the QuestionType field value is equal to UINFO, then the network.dns.question.type UDM field is set to 100.Else, if the QuestionType field value is equal to UID, then the network.dns.question.type UDM field is set to 101.Else, if the QuestionType field value is equal to GID, then the network.dns.question.type UDM field is set to 102.Else, if the QuestionType field value is equal to UNSPEC, then the network.dns.question.type UDM field is set to 103.Else, if the QuestionType field value is equal to NID, then the network.dns.question.type UDM field is set to 104.Else, if the QuestionType field value is equal to L32, then the network.dns.question.type UDM field is set to 105.Else, if the QuestionType field value is equal to L64, then the network.dns.question.type UDM field is set to 106.Else, if the QuestionType field value is equal to LP, then the network.dns.question.type UDM field is set to 107.Else, if the QuestionType field value is equal to EUI48, then the network.dns.question.type UDM field is set to 108.Else, if the QuestionType field value is equal to EUI64, then the network.dns.question.type UDM field is set to 109.Else, if the QuestionType field value is equal to TKEY, then the network.dns.question.type UDM field is set to 249.Else, if the QuestionType field value is equal to TSIG, then the network.dns.question.type UDM field is set to 250.Else, if the QuestionType field value is equal to IXFR, then the network.dns.question.type UDM field is set to 251.Else, if the QuestionType field value is equal to AXFR, then the network.dns.question.type UDM field is set to 252.Else, if the QuestionType field value is equal to MAILB, then the network.dns.question.type UDM field is set to 253.Else, if the QuestionType field value is equal to MAILA, then the network.dns.question.type UDM field is set to 254.Else, if the QuestionType field value is equal to ALL, then the network.dns.question.type UDM field is set to 255.Else, if the QuestionType field value is equal to URI, then the network.dns.question.type UDM field is set to 256.Else, if the QuestionType field value is equal to CAA, then the network.dns.question.type UDM field is set to 257.Else, if the QuestionType field value is equal to AVC, then the network.dns.question.type UDM field is set to 258.Else, if the QuestionType field value is equal to DOA, then the network.dns.question.type UDM field is set to 259.Else, if the QuestionType field value is equal to AMTRELA, then the network.dns.question.type UDM field is set to 260.Else, if the QuestionType field value is equal to TA, then the network.dns.question.type UDM field is set to 32768.Else, if the QuestionType field value is equal to DLV, then the network.dns.question.type UDM field is set to 32769. |
|
network.dns.questions.type |
Grok: Extracted the dns_record_type field from the raw log.If the dns_record_type field value is equal to A, then the network.dns.question.type UDM field is set to 1.Else, if the dns_record_type field value is equal to NS, then the network.dns.question.type UDM field is set to 2.Else, if the dns_record_type field value is equal to MD, then the network.dns.question.type UDM field is set to 3.Else, if the dns_record_type field value is equal to MF, then the network.dns.question.type UDM field is set to 4.Else, if the dns_record_type field value is equal to CNAME, then the network.dns.question.type UDM field is set to 5.Else, if the dns_record_type field value is equal to SOA, then the network.dns.question.type UDM field is set to 6.Else, if the dns_record_type field value is equal to MB, then the network.dns.question.type UDM field is set to 7.Else, if the dns_record_type field value is equal to MG, then the network.dns.question.type UDM field is set to 8.Else, if the dns_record_type field value is equal to MR, then the network.dns.question.type UDM field is set to 9.Else, if the dns_record_type field value is equal to NULL, then the network.dns.question.type UDM field is set to 10.Else, if the dns_record_type field value is equal to WKS, then the network.dns.question.type UDM field is set to 11.Else, if the dns_record_type field value is equal to PTR, then the network.dns.question.type UDM field is set to 12.Else, if the dns_record_type field value is equal to HINFO, then the network.dns.question.type UDM field is set to 13.Else, if the dns_record_type field value is equal to MINFO, then the network.dns.question.type UDM field is set to 14.Else, if the dns_record_type field value is equal to MX, then the network.dns.question.type UDM field is set to 15.Else, if the dns_record_type field value is equal to TXT, then the network.dns.question.type UDM field is set to 16.Else, if the dns_record_type field value is equal to RP, then the network.dns.question.type UDM field is set to 17.Else, if the dns_record_type field value is equal to AFSDB, then the network.dns.question.type UDM field is set to 18.Else, if the dns_record_type field value is equal to X25, then the network.dns.question.type UDM field is set to 19.Else, if the dns_record_type field value is equal to ISDN, then the network.dns.question.type UDM field is set to 20.Else, if the dns_record_type field value is equal to RT, then the network.dns.question.type UDM field is set to 21.Else, if the dns_record_type field value is equal to NSAP, then the network.dns.question.type UDM field is set to 22.Else, if the dns_record_type field value is equal to NSAP-PT, then the network.dns.question.type UDM field is set to 23.Else, if the dns_record_type field value is equal to SIG, then the network.dns.question.type UDM field is set to 24.Else, if the dns_record_type field value is equal to KEY, then the network.dns.question.type UDM field is set to 25.Else, if the dns_record_type field value is equal to PX, then the network.dns.question.type UDM field is set to 26.Else, if the dns_record_type field value is equal to GPOS, then the network.dns.question.type UDM field is set to 27.Else, if the dns_record_type field value is equal to AAAA, then the network.dns.question.type UDM field is set to 28.Else, if the dns_record_type field value is equal to LOC, then the network.dns.question.type UDM field is set to 29.Else, if the dns_record_type field value is equal to NXT, then the network.dns.question.type UDM field is set to 30.Else, if the dns_record_type field value is equal to EID, then the network.dns.question.type UDM field is set to 31.Else, if the dns_record_type field value is equal to NIMLOC, then the network.dns.question.type UDM field is set to 32.Else, if the dns_record_type field value is equal to SRV, then the network.dns.question.type UDM field is set to 33.Else, if the dns_record_type field value is equal to ATMA, then the network.dns.question.type UDM field is set to 34.Else, if the dns_record_type field value is equal to NAPTR, then the network.dns.question.type UDM field is set to 35.Else, if the dns_record_type field value is equal to KX, then the network.dns.question.type UDM field is set to 36.Else, if the dns_record_type field value is equal to CERT, then the network.dns.question.type UDM field is set to 37.Else, if the dns_record_type field value is equal to A6, then the network.dns.question.type UDM field is set to 38.Else, if the dns_record_type field value is equal to DNAME, then the network.dns.question.type UDM field is set to 39.Else, if the dns_record_type field value is equal to SINK, then the network.dns.question.type UDM field is set to 40.Else, if the dns_record_type field value is equal to OPT, then the network.dns.question.type UDM field is set to 41.Else, if the dns_record_type field value is equal to APL, then the network.dns.question.type UDM field is set to 42.Else, if the dns_record_type field value is equal to DS, then the network.dns.question.type UDM field is set to 43.Else, if the dns_record_type field value is equal to SSHFP, then the network.dns.question.type UDM field is set to 44.Else, if the dns_record_type field value is equal to IPSECKE, then the network.dns.question.type UDM field is set to 45.Else, if the dns_record_type field value is equal to RRSIG, then the network.dns.question.type UDM field is set to 46.Else, if the dns_record_type field value is equal to NSEC, then the network.dns.question.type UDM field is set to 47.Else, if the dns_record_type field value is equal to DNSKEY, then the network.dns.question.type UDM field is set to 48.Else, if the dns_record_type field value is equal to DHCID, then the network.dns.question.type UDM field is set to 49.Else, if the dns_record_type field value is equal to NSEC3, then the network.dns.question.type UDM field is set to 50.Else, if the dns_record_type field value is equal to NSEC3PA, then the network.dns.question.type UDM field is set to 51.Else, if the dns_record_type field value is equal to TLSA, then the network.dns.question.type UDM field is set to 52.Else, if the dns_record_type field value is equal to SMIMEA, then the network.dns.question.type UDM field is set to 53.Else, if the dns_record_type field value is equal to UNASSIG, then the network.dns.question.type UDM field is set to 54.Else, if the dns_record_type field value is equal to HIP, then the network.dns.question.type UDM field is set to 55.Else, if the dns_record_type field value is equal to NINFO, then the network.dns.question.type UDM field is set to 56.Else, if the dns_record_type field value is equal to RKEY, then the network.dns.question.type UDM field is set to 57.Else, if the dns_record_type field value is equal to TALINK, then the network.dns.question.type UDM field is set to 58.Else, if the dns_record_type field value is equal to CDS, then the network.dns.question.type UDM field is set to 59.Else, if the dns_record_type field value is equal to CDNSKEY, then the network.dns.question.type UDM field is set to 60.Else, if the dns_record_type field value is equal to OPENPGP, then the network.dns.question.type UDM field is set to 61.Else, if the dns_record_type field value is equal to CSYNC, then the network.dns.question.type UDM field is set to 62.Else, if the dns_record_type field value is equal to ZONEMD, then the network.dns.question.type UDM field is set to 63.Else, if the dns_record_type field value is equal to SVCB, then the network.dns.question.type UDM field is set to 64.Else, if the dns_record_type field value is equal to HTTPS, then the network.dns.question.type UDM field is set to 65.Else, if the dns_record_type field value is equal to SPF, then the network.dns.question.type UDM field is set to 99.Else, if the dns_record_type field value is equal to UINFO, then the network.dns.question.type UDM field is set to 100.Else, if the dns_record_type field value is equal to UID, then the network.dns.question.type UDM field is set to 101.Else, if the dns_record_type field value is equal to GID, then the network.dns.question.type UDM field is set to 102.Else, if the dns_record_type field value is equal to UNSPEC, then the network.dns.question.type UDM field is set to 103.Else, if the dns_record_type field value is equal to NID, then the network.dns.question.type UDM field is set to 104.Else, if the dns_record_type field value is equal to L32, then the network.dns.question.type UDM field is set to 105.Else, if the dns_record_type field value is equal to L64, then the network.dns.question.type UDM field is set to 106.Else, if the dns_record_type field value is equal to LP, then the network.dns.question.type UDM field is set to 107.Else, if the dns_record_type field value is equal to EUI48, then the network.dns.question.type UDM field is set to 108.Else, if the dns_record_type field value is equal to EUI64, then the network.dns.question.type UDM field is set to 109.Else, if the dns_record_type field value is equal to TKEY, then the network.dns.question.type UDM field is set to 249.Else, if the dns_record_type field value is equal to TSIG, then the network.dns.question.type UDM field is set to 250.Else, if the dns_record_type field value is equal to IXFR, then the network.dns.question.type UDM field is set to 251.Else, if the dns_record_type field value is equal to AXFR, then the network.dns.question.type UDM field is set to 252.Else, if the dns_record_type field value is equal to MAILB, then the network.dns.question.type UDM field is set to 253.Else, if the dns_record_type field value is equal to MAILA, then the network.dns.question.type UDM field is set to 254.Else, if the dns_record_type field value is equal to ALL, then the network.dns.question.type UDM field is set to 255.Else, if the dns_record_type field value is equal to URI, then the network.dns.question.type UDM field is set to 256.Else, if the dns_record_type field value is equal to CAA, then the network.dns.question.type UDM field is set to 257.Else, if the dns_record_type field value is equal to AVC, then the network.dns.question.type UDM field is set to 258.Else, if the dns_record_type field value is equal to DOA, then the network.dns.question.type UDM field is set to 259.Else, if the dns_record_type field value is equal to AMTRELA, then the network.dns.question.type UDM field is set to 260.Else, if the dns_record_type field value is equal to TA, then the network.dns.question.type UDM field is set to 32768.Else, if the dns_record_type field value is equal to DLV, then the network.dns.question.type UDM field is set to 32769. |
dns_record_name |
network.dns.questions.type |
If the dns_record_name field value is equal to A, then the network.dns.question.type UDM field is set to 1.Else, if the dns_record_name field value is equal to NS, then the network.dns.question.type UDM field is set to 2.Else, if the dns_record_name field value is equal to MD, then the network.dns.question.type UDM field is set to 3.Else, if the dns_record_name field value is equal to MF, then the network.dns.question.type UDM field is set to 4.Else, if the dns_record_name field value is equal to CNAME, then the network.dns.question.type UDM field is set to 5.Else, if the dns_record_name field value is equal to SOA, then the network.dns.question.type UDM field is set to 6.Else, if the dns_record_name field value is equal to MB, then the network.dns.question.type UDM field is set to 7.Else, if the dns_record_name field value is equal to MG, then the network.dns.question.type UDM field is set to 8.Else, if the dns_record_name field value is equal to MR, then the network.dns.question.type UDM field is set to 9.Else, if the dns_record_name field value is equal to NULL, then the network.dns.question.type UDM field is set to 10.Else, if the dns_record_name field value is equal to WKS, then the network.dns.question.type UDM field is set to 11.Else, if the dns_record_name field value is equal to PTR, then the network.dns.question.type UDM field is set to 12.Else, if the dns_record_name field value is equal to HINFO, then the network.dns.question.type UDM field is set to 13.Else, if the dns_record_name field value is equal to MINFO, then the network.dns.question.type UDM field is set to 14.Else, if the dns_record_name field value is equal to MX, then the network.dns.question.type UDM field is set to 15.Else, if the dns_record_name field value is equal to TXT, then the network.dns.question.type UDM field is set to 16.Else, if the dns_record_name field value is equal to RP, then the network.dns.question.type UDM field is set to 17.Else, if the dns_record_name field value is equal to AFSDB, then the network.dns.question.type UDM field is set to 18.Else, if the dns_record_name field value is equal to X25, then the network.dns.question.type UDM field is set to 19.Else, if the dns_record_name field value is equal to ISDN, then the network.dns.question.type UDM field is set to 20.Else, if the dns_record_name field value is equal to RT, then the network.dns.question.type UDM field is set to 21.Else, if the dns_record_name field value is equal to NSAP, then the network.dns.question.type UDM field is set to 22.Else, if the dns_record_name field value is equal to NSAP-PT, then the network.dns.question.type UDM field is set to 23.Else, if the dns_record_name field value is equal to SIG, then the network.dns.question.type UDM field is set to 24.Else, if the dns_record_name field value is equal to KEY, then the network.dns.question.type UDM field is set to 25.Else, if the dns_record_name field value is equal to PX, then the network.dns.question.type UDM field is set to 26.Else, if the dns_record_name field value is equal to GPOS, then the network.dns.question.type UDM field is set to 27.Else, if the dns_record_name field value is equal to AAAA, then the network.dns.question.type UDM field is set to 28.Else, if the dns_record_name field value is equal to LOC, then the network.dns.question.type UDM field is set to 29.Else, if the dns_record_name field value is equal to NXT, then the network.dns.question.type UDM field is set to 30.Else, if the dns_record_name field value is equal to EID, then the network.dns.question.type UDM field is set to 31.Else, if the dns_record_name field value is equal to NIMLOC, then the network.dns.question.type UDM field is set to 32.Else, if the dns_record_name field value is equal to SRV, then the network.dns.question.type UDM field is set to 33.Else, if the dns_record_name field value is equal to ATMA, then the network.dns.question.type UDM field is set to 34.Else, if the dns_record_name field value is equal to NAPTR, then the network.dns.question.type UDM field is set to 35.Else, if the dns_record_name field value is equal to KX, then the network.dns.question.type UDM field is set to 36.Else, if the dns_record_name field value is equal to CERT, then the network.dns.question.type UDM field is set to 37.Else, if the dns_record_name field value is equal to A6, then the network.dns.question.type UDM field is set to 38.Else, if the dns_record_name field value is equal to DNAME, then the network.dns.question.type UDM field is set to 39.Else, if the dns_record_name field value is equal to SINK, then the network.dns.question.type UDM field is set to 40.Else, if the dns_record_name field value is equal to OPT, then the network.dns.question.type UDM field is set to 41.Else, if the dns_record_name field value is equal to APL, then the network.dns.question.type UDM field is set to 42.Else, if the dns_record_name field value is equal to DS, then the network.dns.question.type UDM field is set to 43.Else, if the dns_record_name field value is equal to SSHFP, then the network.dns.question.type UDM field is set to 44.Else, if the dns_record_name field value is equal to IPSECKE, then the network.dns.question.type UDM field is set to 45.Else, if the dns_record_name field value is equal to RRSIG, then the network.dns.question.type UDM field is set to 46.Else, if the dns_record_name field value is equal to NSEC, then the network.dns.question.type UDM field is set to 47.Else, if the dns_record_name field value is equal to DNSKEY, then the network.dns.question.type UDM field is set to 48.Else, if the dns_record_name field value is equal to DHCID, then the network.dns.question.type UDM field is set to 49.Else, if the dns_record_name field value is equal to NSEC3, then the network.dns.question.type UDM field is set to 50.Else, if the dns_record_name field value is equal to NSEC3PA, then the network.dns.question.type UDM field is set to 51.Else, if the dns_record_name field value is equal to TLSA, then the network.dns.question.type UDM field is set to 52.Else, if the dns_record_name field value is equal to SMIMEA, then the network.dns.question.type UDM field is set to 53.Else, if the dns_record_name field value is equal to UNASSIG, then the network.dns.question.type UDM field is set to 54.Else, if the dns_record_name field value is equal to HIP, then the network.dns.question.type UDM field is set to 55.Else, if the dns_record_name field value is equal to NINFO, then the network.dns.question.type UDM field is set to 56.Else, if the dns_record_name field value is equal to RKEY, then the network.dns.question.type UDM field is set to 57.Else, if the dns_record_name field value is equal to TALINK, then the network.dns.question.type UDM field is set to 58.Else, if the dns_record_name field value is equal to CDS, then the network.dns.question.type UDM field is set to 59.Else, if the dns_record_name field value is equal to CDNSKEY, then the network.dns.question.type UDM field is set to 60.Else, if the dns_record_name field value is equal to OPENPGP, then the network.dns.question.type UDM field is set to 61.Else, if the dns_record_name field value is equal to CSYNC, then the network.dns.question.type UDM field is set to 62.Else, if the dns_record_name field value is equal to ZONEMD, then the network.dns.question.type UDM field is set to 63.Else, if the dns_record_name field value is equal to SVCB, then the network.dns.question.type UDM field is set to 64.Else, if the dns_record_name field value is equal to HTTPS, then the network.dns.question.type UDM field is set to 65.Else, if the dns_record_name field value is equal to SPF, then the network.dns.question.type UDM field is set to 99.Else, if the dns_record_name field value is equal to UINFO, then the network.dns.question.type UDM field is set to 100.Else, if the dns_record_name field value is equal to UID, then the network.dns.question.type UDM field is set to 101.Else, if the dns_record_name field value is equal to GID, then the network.dns.question.type UDM field is set to 102.Else, if the dns_record_name field value is equal to UNSPEC, then the network.dns.question.type UDM field is set to 103.Else, if the dns_record_name field value is equal to NID, then the network.dns.question.type UDM field is set to 104.Else, if the dns_record_name field value is equal to L32, then the network.dns.question.type UDM field is set to 105.Else, if the dns_record_name field value is equal to L64, then the network.dns.question.type UDM field is set to 106.Else, if the dns_record_name field value is equal to LP, then the network.dns.question.type UDM field is set to 107.Else, if the dns_record_name field value is equal to EUI48, then the network.dns.question.type UDM field is set to 108.Else, if the dns_record_name field value is equal to EUI64, then the network.dns.question.type UDM field is set to 109.Else, if the dns_record_name field value is equal to TKEY, then the network.dns.question.type UDM field is set to 249.Else, if the dns_record_name field value is equal to TSIG, then the network.dns.question.type UDM field is set to 250.Else, if the dns_record_name field value is equal to IXFR, then the network.dns.question.type UDM field is set to 251.Else, if the dns_record_name field value is equal to AXFR, then the network.dns.question.type UDM field is set to 252.Else, if the dns_record_name field value is equal to MAILB, then the network.dns.question.type UDM field is set to 253.Else, if the dns_record_name field value is equal to MAILA, then the network.dns.question.type UDM field is set to 254.Else, if the dns_record_name field value is equal to ALL, then the network.dns.question.type UDM field is set to 255.Else, if the dns_record_name field value is equal to URI, then the network.dns.question.type UDM field is set to 256.Else, if the dns_record_name field value is equal to CAA, then the network.dns.question.type UDM field is set to 257.Else, if the dns_record_name field value is equal to AVC, then the network.dns.question.type UDM field is set to 258.Else, if the dns_record_name field value is equal to DOA, then the network.dns.question.type UDM field is set to 259.Else, if the dns_record_name field value is equal to AMTRELA, then the network.dns.question.type UDM field is set to 260.Else, if the dns_record_name field value is equal to TA, then the network.dns.question.type UDM field is set to 32768.Else, if the dns_record_name field value is equal to DLV, then the network.dns.question.type UDM field is set to 32769. |
RemoteIP |
principal.ip |
If the value of the RemoteIP field matches the regular expression ip, then the principal.ip UDM field is mapped to RemoteIP.Else, principal.hostname UDM field is mapped to RemoteIP |
|
principal.ip |
Grok: Extracted the client field from the raw log.If the value of the client field matches the regular expression ip, then the principal.ip UDM field is mapped to client.Else, principal.hostname UDM field is mapped to client. |
|
principal.hostname |
Grok: Extracted the syslog_host field from the raw log.If the value of the client field matches the regular expression ip, then the principal.hostname UDM field is mapped to the syslog_host. |
SendReceiveIndicator |
network.direction |
If the SendReceiveIndicator log field value is equal to Snd, then the network.direction UDM field is set to OUTBOUND.Else, if the SendReceiveIndicator log field value is equal to Rcv, then the network.direction UDM field is set to INBOUND. |
send_receive_indicator |
network.direction |
Grok: Extracted the send_receive_indicator field from the raw log.If the send_receive_indicator field value is equal to Snd, then the network.direction UDM field is set to OUTBOUND.Else, if the send_receive_indicator field value is equal to Rcv, then the network.direction UDM field is set to INBOUND. |
Xid |
network.dns.id |
|
xid |
network.dns.id |
Grok: Extracted the xid field from the raw log and then mapped the xid field to the network.dns.id UDM field. |
|
network.dns.answers.data |
Grok: Extracted the DATA field from the raw log and then mapped the DATA field to the network.dns.answers.data UDM field. |
|
network.dns.answers.type |
Grok: Extracted the TYPE field from the raw log and then mapped the TYPE field to the network.dns.answers.type UDM field. |
|
network.dns.answers.name |
Grok: Extracted the Name field from the raw log and then mapped the Name field to the network.dns.answers.name UDM field. |
|
network.dns.answers.ttl |
Grok: Extracted the TTL field from the raw log and then mapped the TTL field to the network.dns.answers.ttl UDM field. |
|
network.dns.answers.class |
Grok: Extracted the CLASS field from the raw log and then mapped the CLASS field to the network.dns.answers.class UDM field. |
Log di debug legacy
#NOTYPO| Campo del log originale | Campo UDM | Nota |
|---|---|---|
BufLen |
about.labels.key/value (deprecated) |
Grok: Extracted the BufLen field from the raw log and then mapped the BufLen field to the about.labels UDM field. |
BufLen |
additional.fields |
Grok: Extracted the BufLen field from the raw log and then mapped the BufLen field to the additional.fields UDM field. |
client |
principal.ip |
Grok: Extracted the client field from the raw log. If the value of the client field matches the regular expression ip, then the principal.ip UDM field is mapped to client.Else, principal.hostname UDM field is mapped to client. |
domain |
|
Grok: Extracted the domain field from the raw log and then mapped the domain field to the network.dns.questions.name, target.hostname and target.asset.hostname UDM field. |
Expire |
about.labels.key/value (deprecated) |
Grok: Extracted the Expire field from the raw log and then mapped the Expire field to the about.labels UDM field. |
Expire |
additional.fields |
Grok: Extracted the Expire field from the raw log and then mapped the Expire field to the additional.fields UDM field. |
internal_packet_identifier |
about.labels.key/value (deprecated) |
Grok: Extracted the internal_packet_identifier field from the raw log and then mapped the internal_packet_identifier field to the about.labels UDM field. |
internal_packet_identifier |
additional.fields |
Grok: Extracted the internal_packet_identifier field from the raw log and then mapped the internal_packet_identifier field to the additional.fields UDM field. |
ip_protocol |
network.ip_protocol |
Grok: Extracted the ip_protocol field from the raw log.If the ip_protocol field value is equal to 1 or ICMP, then the network.ip_protocol UDM field is set to ICMP.Else, if the ip_protocol field value is equal to 2 or IGMP, then the network.ip_protocol UDM field is set to IGMP.Else, if the ip_protocol field value is equal to 6 or TCP, then the network.ip_protocol UDM field is set to TCP.Else, if the ip_protocol field value is equal to 17 or UDP, then the network.ip_protocol UDM field is set to UDP.Else, if the ip_protocol field value is equal to 41 or IP6IN4, then the network.ip_protocol UDM field is set to IP6IN4.Else, if the ip_protocol field value is equal to 47 or GRE, then the network.ip_protocol UDM field is set to GRE.Else, if the ip_protocol field value is equal to 50 or ESP, then the network.ip_protocol UDM field is set to ESP.Else, if the ip_protocol field value is equal to 88 or EIGRP, then the network.ip_protocol UDM field is set to EIGRP.Else, if the ip_protocol field value is equal to 97 or ETHERIP, then the network.ip_protocol UDM field is set to ETHERIP.Else, if the ip_protocol field value is equal to 103 or PIM, then the network.ip_protocol UDM field is set to PIM.Else, if the ip_protocol field value is equal to 112 or VRRP, then the network.ip_protocol UDM field is set to VRRP. |
LogInfo |
metadata.description |
Grok: Extracted the LogInfo field from the raw log and then mapped the LogInfo field to the metadata.description UDM field. |
opcode |
network.dns.opcode |
Grok: Extracted the opcode field from the raw log.If the opcode field value is equal to Q, then the network.dns.opcode UDM field is set to 0.Else, if the opcode field value is equal to I, then the network.dns.opcode UDM field is set to 1.Else, if the opcode field value is equal to S, then the network.dns.opcode UDM field is set to 2.Else, if the opcode field value is equal to N, then the network.dns.opcode UDM field is set to 4.Else, if the opcode field value is equal to U, then the network.dns.opcode UDM field is set to 5. |
PortNum |
principal.port |
Grok: Extracted the PortNum field from the raw log and then mapped the PortNum field to the principal.port UDM field. |
Queued |
about.labels.key/value (deprecated) |
Grok: Extracted the Queued field from the raw log and then mapped the Queued field to the about.labels UDM field. |
Queued |
additional.fields |
Grok: Extracted the Queued field from the raw log and then mapped the Queued field to the additional.fields UDM field. |
req_or_resp |
network.dns.response |
Grok: Extracted req_or_resp from the raw log,If the req_or_resp field value is equal to R, then the network.dns.response UDM field is set to true.Else, the network.dns.response UDM field is set to false |
send_receive_indicator |
network.direction |
Grok: Extracted the send_receive_indicator field from the raw log.If the send_receive_indicator field value is equal to Snd, then the network.direction UDM field is set to OUTBOUND.Else, if the send_receive_indicator field value is equal to Rcv, then the network.direction UDM field is set to INBOUND. |
Socket |
principal.labels.key/value (deprecated) |
Grok: Extracted the Socket field from the raw log and then mapped the Socket field to the principal.labels UDM field. |
Socket |
additional.fields |
Grok: Extracted the Socket field from the raw log and then mapped the Socket field to the additional.fields UDM field. |
TimeQuery |
about.labels.key/value (deprecated) |
Grok: Extracted the TimeQuery field from the raw log and then mapped the TimeQuery field to the about.labels UDM field. |
TimeQuery |
additional.fields |
Grok: Extracted the TimeQuery field from the raw log and then mapped the TimeQuery field to the additional.fields UDM field. |
xid |
network.dns.id |
Grok: Extracted the xid field from the raw log and then mapped the xid field to the network.dns.id UDM field. |
dns_record_type |
|
Grok: Extracted the dns_record_type field from the raw log.If the dns_record_type field value is equal to A, then the network.dns.question.type UDM field is set to 1.Else, if the dns_record_type field value is equal to NS, then the network.dns.question.type UDM field is set to 2.Else, if the dns_record_type field value is equal to MD, then the network.dns.question.type UDM field is set to 3.Else, if the dns_record_type field value is equal to MF, then the network.dns.question.type UDM field is set to 4.Else, if the dns_record_type field value is equal to CNAME, then the network.dns.question.type UDM field is set to 5.Else, if the dns_record_type field value is equal to SOA, then the network.dns.question.type UDM field is set to 6.Else, if the dns_record_type field value is equal to MB, then the network.dns.question.type UDM field is set to 7.Else, if the dns_record_type field value is equal to MG, then the network.dns.question.type UDM field is set to 8.Else, if the dns_record_type field value is equal to MR, then the network.dns.question.type UDM field is set to 9.Else, if the dns_record_type field value is equal to NULL, then the network.dns.question.type UDM field is set to 10.Else, if the dns_record_type field value is equal to WKS, then the network.dns.question.type UDM field is set to 11.Else, if the dns_record_type field value is equal to PTR, then the network.dns.question.type UDM field is set to 12.Else, if the dns_record_type field value is equal to HINFO, then the network.dns.question.type UDM field is set to 13.Else, if the dns_record_type field value is equal to MINFO, then the network.dns.question.type UDM field is set to 14.Else, if the dns_record_type field value is equal to MX, then the network.dns.question.type UDM field is set to 15.Else, if the dns_record_type field value is equal to TXT, then the network.dns.question.type UDM field is set to 16.Else, if the dns_record_type field value is equal to RP, then the network.dns.question.type UDM field is set to 17.Else, if the dns_record_type field value is equal to AFSDB, then the network.dns.question.type UDM field is set to 18.Else, if the dns_record_type field value is equal to X25, then the network.dns.question.type UDM field is set to 19.Else, if the dns_record_type field value is equal to ISDN, then the network.dns.question.type UDM field is set to 20.Else, if the dns_record_type field value is equal to RT, then the network.dns.question.type UDM field is set to 21.Else, if the dns_record_type field value is equal to NSAP, then the network.dns.question.type UDM field is set to 22.Else, if the dns_record_type field value is equal to NSAP-PT, then the network.dns.question.type UDM field is set to 23.Else, if the dns_record_type field value is equal to SIG, then the network.dns.question.type UDM field is set to 24.Else, if the dns_record_type field value is equal to KEY, then the network.dns.question.type UDM field is set to 25.Else, if the dns_record_type field value is equal to PX, then the network.dns.question.type UDM field is set to 26.Else, if the dns_record_type field value is equal to GPOS, then the network.dns.question.type UDM field is set to 27.Else, if the dns_record_type field value is equal to AAAA, then the network.dns.question.type UDM field is set to 28.Else, if the dns_record_type field value is equal to LOC, then the network.dns.question.type UDM field is set to 29.Else, if the dns_record_type field value is equal to NXT, then the network.dns.question.type UDM field is set to 30.Else, if the dns_record_type field value is equal to EID, then the network.dns.question.type UDM field is set to 31.Else, if the dns_record_type field value is equal to NIMLOC, then the network.dns.question.type UDM field is set to 32.Else, if the dns_record_type field value is equal to SRV, then the network.dns.question.type UDM field is set to 33.Else, if the dns_record_type field value is equal to ATMA, then the network.dns.question.type UDM field is set to 34.Else, if the dns_record_type field value is equal to NAPTR, then the network.dns.question.type UDM field is set to 35.Else, if the dns_record_type field value is equal to KX, then the network.dns.question.type UDM field is set to 36.Else, if the dns_record_type field value is equal to CERT, then the network.dns.question.type UDM field is set to 37.Else, if the dns_record_type field value is equal to A6, then the network.dns.question.type UDM field is set to 38.Else, if the dns_record_type field value is equal to DNAME, then the network.dns.question.type UDM field is set to 39.Else, if the dns_record_type field value is equal to SINK, then the network.dns.question.type UDM field is set to 40.Else, if the dns_record_type field value is equal to OPT, then the network.dns.question.type UDM field is set to 41.Else, if the dns_record_type field value is equal to APL, then the network.dns.question.type UDM field is set to 42.Else, if the dns_record_type field value is equal to DS, then the network.dns.question.type UDM field is set to 43.Else, if the dns_record_type field value is equal to SSHFP, then the network.dns.question.type UDM field is set to 44.Else, if the dns_record_type field value is equal to IPSECKE, then the network.dns.question.type UDM field is set to 45.Else, if the dns_record_type field value is equal to RRSIG, then the network.dns.question.type UDM field is set to 46.Else, if the dns_record_type field value is equal to NSEC, then the network.dns.question.type UDM field is set to 47.Else, if the dns_record_type field value is equal to DNSKEY, then the network.dns.question.type UDM field is set to 48.Else, if the dns_record_type field value is equal to DHCID, then the network.dns.question.type UDM field is set to 49.Else, if the dns_record_type field value is equal to NSEC3, then the network.dns.question.type UDM field is set to 50.Else, if the dns_record_type field value is equal to NSEC3PA, then the network.dns.question.type UDM field is set to 51.Else, if the dns_record_type field value is equal to TLSA, then the network.dns.question.type UDM field is set to 52.Else, if the dns_record_type field value is equal to SMIMEA, then the network.dns.question.type UDM field is set to 53.Else, if the dns_record_type field value is equal to UNASSIG, then the network.dns.question.type UDM field is set to 54.Else, if the dns_record_type field value is equal to HIP, then the network.dns.question.type UDM field is set to 55.Else, if the dns_record_type field value is equal to NINFO, then the network.dns.question.type UDM field is set to 56.Else, if the dns_record_type field value is equal to RKEY, then the network.dns.question.type UDM field is set to 57.Else, if the dns_record_type field value is equal to TALINK, then the network.dns.question.type UDM field is set to 58.Else, if the dns_record_type field value is equal to CDS, then the network.dns.question.type UDM field is set to 59.Else, if the dns_record_type field value is equal to CDNSKEY, then the network.dns.question.type UDM field is set to 60.Else, if the dns_record_type field value is equal to OPENPGP, then the network.dns.question.type UDM field is set to 61.Else, if the dns_record_type field value is equal to CSYNC, then the network.dns.question.type UDM field is set to 62.Else, if the dns_record_type field value is equal to ZONEMD, then the network.dns.question.type UDM field is set to 63.Else, if the dns_record_type field value is equal to SVCB, then the network.dns.question.type UDM field is set to 64.Else, if the dns_record_type field value is equal to HTTPS, then the network.dns.question.type UDM field is set to 65.Else, if the dns_record_type field value is equal to SPF, then the network.dns.question.type UDM field is set to 99.Else, if the dns_record_type field value is equal to UINFO, then the network.dns.question.type UDM field is set to 100.Else, if the dns_record_type field value is equal to UID, then the network.dns.question.type UDM field is set to 101.Else, if the dns_record_type field value is equal to GID, then the network.dns.question.type UDM field is set to 102.Else, if the dns_record_type field value is equal to UNSPEC, then the network.dns.question.type UDM field is set to 103.Else, if the dns_record_type field value is equal to NID, then the network.dns.question.type UDM field is set to 104.Else, if the dns_record_type field value is equal to L32, then the network.dns.question.type UDM field is set to 105.Else, if the dns_record_type field value is equal to L64, then the network.dns.question.type UDM field is set to 106.Else, if the dns_record_type field value is equal to LP, then the network.dns.question.type UDM field is set to 107.Else, if the dns_record_type field value is equal to EUI48, then the network.dns.question.type UDM field is set to 108.Else, if the dns_record_type field value is equal to EUI64, then the network.dns.question.type UDM field is set to 109.Else, if the dns_record_type field value is equal to TKEY, then the network.dns.question.type UDM field is set to 249.Else, if the dns_record_type field value is equal to TSIG, then the network.dns.question.type UDM field is set to 250.Else, if the dns_record_type field value is equal to IXFR, then the network.dns.question.type UDM field is set to 251.Else, if the dns_record_type field value is equal to AXFR, then the network.dns.question.type UDM field is set to 252.Else, if the dns_record_type field value is equal to MAILB, then the network.dns.question.type UDM field is set to 253.Else, if the dns_record_type field value is equal to MAILA, then the network.dns.question.type UDM field is set to 254.Else, if the dns_record_type field value is equal to ALL, then the network.dns.question.type UDM field is set to 255.Else, if the dns_record_type field value is equal to URI, then the network.dns.question.type UDM field is set to 256.Else, if the dns_record_type field value is equal to CAA, then the network.dns.question.type UDM field is set to 257.Else, if the dns_record_type field value is equal to AVC, then the network.dns.question.type UDM field is set to 258.Else, if the dns_record_type field value is equal to DOA, then the network.dns.question.type UDM field is set to 259.Else, if the dns_record_type field value is equal to AMTRELA, then the network.dns.question.type UDM field is set to 260.Else, if the dns_record_type field value is equal to TA, then the network.dns.question.type UDM field is set to 32768.Else, if the dns_record_type field value is equal to DLV, then the network.dns.question.type UDM field is set to 32769. |
CLASS |
network.dns.additional.class |
PREREQUISITE SECTION CLASS |
DATA |
network.dns.additional.data |
PREREQUISITE SECTION DATA |
Name |
network.dns.additional.name |
PREREQUISITE SECTION Name |
TTL |
network.dns.additional.ttl |
PREREQUISITE SECTION TTL |
TYPE |
network.dns.additional.type |
PREREQUISITE SECTION TYPE |
Flags |
additional.fields.key/value.string_value |
Grok: Extracted the Flags field from the raw log and then mapped the Flags field to the additional.fields.key/value.string_value UDM field. |
CLASS |
network.dns.additional.class |
UPDATE SECTION CLASS |
DATA |
network.dns.additional.data |
UPDATE SECTION DATA |
Name |
network.dns.additional.name |
UPDATE SECTION Name |
TTL |
network.dns.additional.ttl |
UPDATE SECTION TTL |
TYPE |
network.dns.additional.type |
UPDATE SECTION TYPE |
ZCLASS |
network.dns.additional.class |
ZONE SECTION ZCLASS |
Name |
network.dns.additional.name |
ZONE SECTION Name |
ZTYPE |
network.dns.additional.type |
ZONE SECTION ZTYPE |
QR |
additional.fields.key/value.string_value |
|
OPCODE |
additional.fields.key/value.string_value |
|
AA |
additional.fields.key/value.string_value |
|
TC |
additional.fields.key/value.string_value |
|
RD |
additional.fields.key/value.string_value |
|
RA |
additional.fields.key/value.string_value |
|
Z |
additional.fields.key/value.string_value |
|
CD |
additional.fields.key/value.string_value |
|
AD |
additional.fields.key/value.string_value |
|
RCODE |
additional.fields.key/value.string_value |
|
ZCOUNT |
additional.fields.key/value.string_value |
|
PRECOUNT |
additional.fields.key/value.string_value |
|
ARCOUNT |
additional.fields.key/value.string_value |
|
UPCOUNT |
additional.fields.key/value.string_value |
|
QCOUNT |
additional.fields.key/value.string_value |
|
ACOUNT | additional.fields.key/value.string_value |
|
NSCOUNT |
additional.fields.key/value.string_value |
|
host_name |
intermediary.hostname |
Grok: Extracted the host_name field from the raw log and then mapped the host_name field to the intermediary.hostname UDM field. |
os_type |
intermediary.asset.platform_software.platform |
Grok: Extracted the os_type field from the raw log.If the os_type extracted field value matches the regular expression pattern (?i)windows, then the intermediary.asset.platform_software.platform UDM field is set to WINDOWS.Else, if the os_type extracted field value matches the regular expression pattern (?i)linux, then the intermediary.asset.platform_software.platform UDM field is set to LINUX.Else, if the os_type extracted field is not empty, then the os_type extracted field is mapped with the intermediary.asset.attribute.labels UDM field. |
Altri log
| Campo del log originale | Campo UDM | Nota |
|---|---|---|
|
network.dns.questions.name, target.hostname |
Grok: Extracted the record_name field from the raw log and then mapped the record_name field to the network.dns.questions.name and target.hostname UDM field. |
|
network.dns.questions.type |
Grok: Extracted the record_type field from the raw log.If the record_type field value is equal to A, then the network.dns.question.type UDM field is set to 1.Else, if the record_type field value is equal to NS, then the network.dns.question.type UDM field is set to 2.Else, if the record_type field value is equal to MD, then the network.dns.question.type UDM field is set to 3.Else, if the record_type field value is equal to MF, then the network.dns.question.type UDM field is set to 4.Else, if the record_type field value is equal to CNAME, then the network.dns.question.type UDM field is set to 5.Else, if the record_type field value is equal to SOA, then the network.dns.question.type UDM field is set to 6.Else, if the record_type field value is equal to MB, then the network.dns.question.type UDM field is set to 7.Else, if the record_type field value is equal to MG, then the network.dns.question.type UDM field is set to 8.Else, if the record_type field value is equal to MR, then the network.dns.question.type UDM field is set to 9.Else, if the record_type field value is equal to NULL, then the network.dns.question.type UDM field is set to 10.Else, if the record_type field value is equal to WKS, then the network.dns.question.type UDM field is set to 11.Else, if the record_type field value is equal to PTR, then the network.dns.question.type UDM field is set to 12.Else, if the record_type field value is equal to HINFO, then the network.dns.question.type UDM field is set to 13.Else, if the record_type field value is equal to MINFO, then the network.dns.question.type UDM field is set to 14.Else, if the record_type field value is equal to MX, then the network.dns.question.type UDM field is set to 15.Else, if the record_type field value is equal to TXT, then the network.dns.question.type UDM field is set to 16.Else, if the record_type field value is equal to RP, then the network.dns.question.type UDM field is set to 17.Else, if the record_type field value is equal to AFSDB, then the network.dns.question.type UDM field is set to 18.Else, if the record_type field value is equal to X25, then the network.dns.question.type UDM field is set to 19.Else, if the record_type field value is equal to ISDN, then the network.dns.question.type UDM field is set to 20.Else, if the record_type field value is equal to RT, then the network.dns.question.type UDM field is set to 21.Else, if the record_type field value is equal to NSAP, then the network.dns.question.type UDM field is set to 22.Else, if the record_type field value is equal to NSAP-PT, then the network.dns.question.type UDM field is set to 23.Else, if the record_type field value is equal to SIG, then the network.dns.question.type UDM field is set to 24.Else, if the record_type field value is equal to KEY, then the network.dns.question.type UDM field is set to 25.Else, if the record_type field value is equal to PX, then the network.dns.question.type UDM field is set to 26.Else, if the record_type field value is equal to GPOS, then the network.dns.question.type UDM field is set to 27.Else, if the record_type field value is equal to AAAA, then the network.dns.question.type UDM field is set to 28.Else, if the record_type field value is equal to LOC, then the network.dns.question.type UDM field is set to 29.Else, if the record_type field value is equal to NXT, then the network.dns.question.type UDM field is set to 30.Else, if the record_type field value is equal to EID, then the network.dns.question.type UDM field is set to 31.Else, if the record_type field value is equal to NIMLOC, then the network.dns.question.type UDM field is set to 32.Else, if the record_type field value is equal to SRV, then the network.dns.question.type UDM field is set to 33.Else, if the record_type field value is equal to ATMA, then the network.dns.question.type UDM field is set to 34.Else, if the record_type field value is equal to NAPTR, then the network.dns.question.type UDM field is set to 35.Else, if the record_type field value is equal to KX, then the network.dns.question.type UDM field is set to 36.Else, if the record_type field value is equal to CERT, then the network.dns.question.type UDM field is set to 37.Else, if the record_type field value is equal to A6, then the network.dns.question.type UDM field is set to 38.Else, if the record_type field value is equal to DNAME, then the network.dns.question.type UDM field is set to 39.Else, if the record_type field value is equal to SINK, then the network.dns.question.type UDM field is set to 40.Else, if the record_type field value is equal to OPT, then the network.dns.question.type UDM field is set to 41.Else, if the record_type field value is equal to APL, then the network.dns.question.type UDM field is set to 42.Else, if the record_type field value is equal to DS, then the network.dns.question.type UDM field is set to 43.Else, if the record_type field value is equal to SSHFP, then the network.dns.question.type UDM field is set to 44.Else, if the record_type field value is equal to IPSECKE, then the network.dns.question.type UDM field is set to 45.Else, if the record_type field value is equal to RRSIG, then the network.dns.question.type UDM field is set to 46.Else, if the record_type field value is equal to NSEC, then the network.dns.question.type UDM field is set to 47.Else, if the record_type field value is equal to DNSKEY, then the network.dns.question.type UDM field is set to 48.Else, if the record_type field value is equal to DHCID, then the network.dns.question.type UDM field is set to 49.Else, if the record_type field value is equal to NSEC3, then the network.dns.question.type UDM field is set to 50.Else, if the record_type field value is equal to NSEC3PA, then the network.dns.question.type UDM field is set to 51.Else, if the record_type field value is equal to TLSA, then the network.dns.question.type UDM field is set to 52.Else, if the record_type field value is equal to SMIMEA, then the network.dns.question.type UDM field is set to 53.Else, if the record_type field value is equal to UNASSIG, then the network.dns.question.type UDM field is set to 54.Else, if the record_type field value is equal to HIP, then the network.dns.question.type UDM field is set to 55.Else, if the record_type field value is equal to NINFO, then the network.dns.question.type UDM field is set to 56.Else, if the record_type field value is equal to RKEY, then the network.dns.question.type UDM field is set to 57.Else, if the record_type field value is equal to TALINK, then the network.dns.question.type UDM field is set to 58.Else, if the record_type field value is equal to CDS, then the network.dns.question.type UDM field is set to 59.Else, if the record_type field value is equal to CDNSKEY, then the network.dns.question.type UDM field is set to 60.Else, if the record_type field value is equal to OPENPGP, then the network.dns.question.type UDM field is set to 61.Else, if the record_type field value is equal to CSYNC, then the network.dns.question.type UDM field is set to 62.Else, if the record_type field value is equal to ZONEMD, then the network.dns.question.type UDM field is set to 63.Else, if the record_type field value is equal to SVCB, then the network.dns.question.type UDM field is set to 64.Else, if the record_type field value is equal to HTTPS, then the network.dns.question.type UDM field is set to 65.Else, if the record_type field value is equal to SPF, then the network.dns.question.type UDM field is set to 99.Else, if the record_type field value is equal to UINFO, then the network.dns.question.type UDM field is set to 100.Else, if the record_type field value is equal to UID, then the network.dns.question.type UDM field is set to 101.Else, if the record_type field value is equal to GID, then the network.dns.question.type UDM field is set to 102.Else, if the record_type field value is equal to UNSPEC, then the network.dns.question.type UDM field is set to 103.Else, if the record_type field value is equal to NID, then the network.dns.question.type UDM field is set to 104.Else, if the record_type field value is equal to L32, then the network.dns.question.type UDM field is set to 105.Else, if the record_type field value is equal to L64, then the network.dns.question.type UDM field is set to 106.Else, if the record_type field value is equal to LP, then the network.dns.question.type UDM field is set to 107.Else, if the record_type field value is equal to EUI48, then the network.dns.question.type UDM field is set to 108.Else, if the record_type field value is equal to EUI64, then the network.dns.question.type UDM field is set to 109.Else, if the record_type field value is equal to TKEY, then the network.dns.question.type UDM field is set to 249.Else, if the record_type field value is equal to TSIG, then the network.dns.question.type UDM field is set to 250.Else, if the record_type field value is equal to IXFR, then the network.dns.question.type UDM field is set to 251.Else, if the record_type field value is equal to AXFR, then the network.dns.question.type UDM field is set to 252.Else, if the record_type field value is equal to MAILB, then the network.dns.question.type UDM field is set to 253.Else, if the record_type field value is equal to MAILA, then the network.dns.question.type UDM field is set to 254.Else, if the record_type field value is equal to ALL, then the network.dns.question.type UDM field is set to 255.Else, if the record_type field value is equal to URI, then the network.dns.question.type UDM field is set to 256.Else, if the record_type field value is equal to CAA, then the network.dns.question.type UDM field is set to 257.Else, if the record_type field value is equal to AVC, then the network.dns.question.type UDM field is set to 258.Else, if the record_type field value is equal to DOA, then the network.dns.question.type UDM field is set to 259.Else, if the record_type field value is equal to AMTRELA, then the network.dns.question.type UDM field is set to 260.Else, if the record_type field value is equal to TA, then the network.dns.question.type UDM field is set to 32768.Else, if the record_type field value is equal to DLV, then the network.dns.question.type UDM field is set to 32769. |
client |
principal.ip |
Grok: Extracted the client field from the raw log. If the value of the client field matches the regular expression ip, then the principal.ip UDM field is mapped to client.Else, principal.hostname UDM field is mapped to client. |
|
principal.hostname |
Grok: Extracted the syslog_host field from the raw log.If the value of the client field matches the regular expression ip, then the principal.hostname UDM field is mapped to the syslog_host. |
|
network.dns.questions.class |
Grok: Extracted the qclass field from the raw log.If the qclass field value is equal to IN, then network.dns.questions.class is set to 1.Else, if the qclass field value is equal to CH, then network.dns.questions.class is set to 3.Else, if the qclass field value is equal to HS, then network.dns.questions.class is set to 4. |
Riferimento alla mappatura dei campi: ID evento al tipo di evento UDM
Questa sezione descrive in che modo il parser mappa gli ID evento agli event_types UDM. In generale, gli eventi vengono mappati a metadata.event_type di NETWORK_DNS, tranne per gli ID evento nella sezione seguente.
| ID evento | Testo evento | Tipo di evento UDM | Note |
|---|---|---|---|
275 |
XFR_NOTIFY_ACK_IN: Source=%1; InterfaceIP=%2; PacketData=%4 | GENERIC_EVENT |
|
276 |
IXFR_RESP_OUT: TCP=%1; InterfaceIP=%2; Destination=%3; QNAME=%4; XID=%5; ZoneScope=%6; Zone=%7; RCODE=%8; PacketData=%10 | GENERIC_EVENT |
|
512 |
SETTING_CREATION |
||
513 |
The zone %1 was deleted. | SETTING_DELETION |
|
514 |
The zone %1 was updated. The %2 setting has been set to %3. | SETTING_MODIFICATION |
|
515 |
A resource record of type %1, name %2, TTL %3 and RDATA %5 was created in scope %7 of zone %6. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
516 |
A resource record of type %1, name %2 and RDATA %5 was deleted from scope %7 of zone %6. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
517 |
All resource records of type %1, name %2 were deleted from scope %4 of zone %3. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
518 |
All resource records at Node name %1 were deleted from scope %3 of zone %2. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
519 |
A resource record of type %1, name %2, TTL %3 and RDATA %5 was created in scope %7 of zone %6 via dynamic update from IP Address %8. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
520 |
A resource record of type %1, name %2 and RDATA %5 was deleted from scope %7 of zone %6 via dynamic update from IP Address %8. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
521 |
A resource record of type %1, name %2, TTL %3 and RDATA %5 was scavenged from scope %7 of zone %6. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
522 |
The scope %1 was created in zone %2. | SETTING_CREATION |
|
523 |
The scope %1 was deleted in zone %2. | SETTING_DELETION |
|
525 |
The zone %1 was signed with following properties: DenialOfExistence=%2; DistributeTrustAnchor=%3; DnsKeyRecordSetTtl=%4; DSRecordGenerationAlgorithm=%5; DSRecordSetTtl=%6; EnableRfc5011KeyRollover=%7; IsKeyMasterServer=%8; KeyMasterServer=%9; NSec3HashAlgorithm=%10; NSec3Iterations=%11; NSec3OptOut=%12; NSec3RandomSaltLength=%13; NSec3UserSalt=%14; ParentHasSecureDelegation=%15; PropagationTime=%16; SecureDelegationPollingPeriod=%17; SignatureInceptionOffset=%18. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
526 |
The zone %1 was unsigned. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
527 |
The zone %1 was re-signed with following properties: DenialOfExistence=%2; DistributeTrustAnchor=%3; DnsKeyRecordSetTtl=%4; DSRecordGenerationAlgorithm=%5; DSRecordSetTtl=%6; EnableRfc5011KeyRollover=%7; IsKeyMasterServer=%8; KeyMasterServer=%9; NSec3HashAlgorithm=%10; NSec3Iterations=%11; NSec3OptOut=%12; NSec3RandomSaltLength=%13; NSec3UserSalt=%14; ParentHasSecureDelegation=%15; PropagationTime=%16; SecureDelegationPollingPeriod=%17; SignatureInceptionOffset=%18. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
528 |
Rollover was started on the type %1 with GUID %2 of zone %3. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
529 |
Rollover was completed on the type %1 with GUID %2 of zone %3. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
530 |
The type %1 with GUID %2 of zone %3 was marked for retiral. The key will be removed after the rollover completion. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
531 |
Manual rollover was triggered on the type %1 with GUID %2 of zone %3. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
533 |
The keys signing key with GUID %1 on zone %2 that was waiting for a Delegation Signer(DS) update on the parent has been forced to move to rollover completion. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
534 |
DNSSEC setting metadata was exported %1 key signing key metadata from zone %2. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
535 |
DNSSEC setting metadata was imported on zone %1. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
536 |
A record of type %1, QNAME %2 was purged from scope %3 in cache. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
537 |
The forwarder list on scope %2 has been reset to %1. | SETTING_MODIFICATION |
target.resource.name is set to "Forwarder list on scope:
%{scope_name}" |
540 |
The root hints have been modified. | SETTING_MODIFICATION |
target.resource.name populated with text "Root hints" |
541 |
The setting %1 on scope %2 has been set to %3. | SETTING_MODIFICATION |
|
542 |
The scope %1 of DNS server was created. | SETTING_CREATION |
|
543 |
The scope %1 of DNS server was deleted. | SETTING_DELETION |
|
544 |
The DNSKEY with Key Protocol %2, Base64 Data %4 and Crypto Algorithm %5 has been added at the trust point %1. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
545 |
The DS with Key Tag: %2, Digest Type: %3, Digest: %5 and Crypto Algorithm: %6 has been added at the trust point %1. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
546 |
The trust point at %1 of type %2 has been removed. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
547 |
The trust anchor for the root zone has been added. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
548 |
A request to restart the DNS server service has been received. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
549 |
The debug logs have been cleared from %1 on DNS server. | SYSTEM_AUDIT_LOG_WIPE |
|
550 |
The in-memory contents of all the zones on DNS server have been flushed to their respective files. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
551 |
All the statistical data for the DNS server has been cleared. | SYSTEM_AUDIT_LOG_WIPE |
|
552 |
A resource record scavenging cycle has been started on the DNS Server. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
553 |
%1 | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
554 |
The resource record scavenging cycle has been terminated on the DNS Server. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
555 |
The DNS server has been prepared for demotion by removing references to it from all zones stored in the Active Directory. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
556 |
The information about the root hints on the DNS server has been written back to the persistent storage. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
557 |
The addresses on which DNS server will listen has been changed to %1. | SETTING_MODIFICATION |
target.resource.name populated with text "Listen Addresses" |
558 |
An immediate RFC 5011 active refresh has been scheduled for all trust points. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
559 |
The zone %1 is paused. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
560 |
The zone %1 is resumed. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
561 |
The data for zone %1 has been reloaded from %2. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
562 |
The data for zone %1 has been refreshed from the master server %2. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
| 563 | The secondary zone %1 has been expired and new data has been requested from the master server %2. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
564 |
The zone %1 has been reloaded from the Active Directory. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
565 |
The content of the zone %1 has been written to the disk and the notification has been sent to all the notify servers. | SETTING_MODIFICATION |
|
566 |
All DNS records at the node %1 in the zone %2 will have their aging time stamp set to the current time.%3 | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
567 |
The Active Directory-integrated zone %1 has been updated. Only %2 can run scavenging. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
568 |
The key master role for zone %1 has been %2.%3 | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
569 |
A %1 singing key (%2) descriptor has been added on the zone %3 with following properties: KeyId=%4; KeyType=%5; CurrentState=%6; KeyStorageProvider=%7; StoreKeysInAD=%8; CryptoAlgorithm=%9; KeyLength=%10; DnsKeySignatureValidityPeriod=%11; DSSignatureValidityPeriod=%12; ZoneSignatureValidityPeriod=%13; InitialRolloverOffset=%14; RolloverPeriod=%15; RolloverType=%16; NextRolloverAction=%17; LastRolloverTime=%18; NextRolloverTime=%19; CurrentRolloverStatus=%20; ActiveKey=%21; StandbyKey=%22; NextKey=%23. The zone will be resigned with the %2 generated with these properties. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
570 |
A %1 singing key (%2) descriptor with GUID %3 has been updated on the zone %4. The properties of this %2 descriptor have been set to: KeyId=%5; KeyType=%6; CurrentState=%7; KeyStorageProvider=%8; StoreKeysInAD=%9; CryptoAlgorithm=%10; KeyLength=%11; DnsKeySignatureValidityPeriod=%12; DSSignatureValidityPeriod=%13; ZoneSignatureValidityPeriod=%14; InitialRolloverOffset=%15; RolloverPeriod=%16; RolloverType=%17; NextRolloverAction=%18; LastRolloverTime=%19; NextRolloverTime=%20; CurrentRolloverStatus=%21; ActiveKey=%22; StandbyKey=%23; NextKey=%24. The zone will be resigned with the %2 generated with these properties. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
571 |
A %1 singing key (%2) descriptor %4 has been removed from the zone %3. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
572 |
The state of the %1 signing key (%2) %3 has been modified on zone %4. The new active key is %5, standby key is %6 and next key is %7. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
573 |
A delegation for %1 in the scope %2 of zone %3 with the name server %4 has been added. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
574 |
The client subnet record with name %1 value %2 has been added to the client subnet map. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
575 |
The client subnet record with name %1 has been deleted from the client subnet map. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
576 |
The client subnet record with name %1 has been updated from the client subnet map. The new client subnets that it refers to are %2. | SYSTEM_AUDIT_LOG_UNCATEGORIZED |
|
577 |
A server level policy %6 for %1 has been created on server %2 with following properties: ProcessingOrder:%3; Criteria:%4; Action:%5. | SETTING_CREATION |
|
578 |
A zone level policy %8 for %1 has been created on zone %6 on server %2 with following properties: ProcessingOrder:%3; Criteria:%4; Action:%5; Scopes:%7. | SETTING_CREATION |
|
579 |
A forwarding policy %6 has been created on server %2 with following properties: ProcessingOrder:%3; Criteria:%4; Action:%5; Scope:%1. | SETTING_CREATION |
|
580 |
The server level policy %1 has been deleted from server %2. | SETTING_DELETION |
|
581 |
The zone level policy %1 has been deleted from zone %3 on server %2. | SETTING_DELETION |
|
582 |
The forwarding policy %1 has been deleted from server %2. | SETTING_DELETION |
Hai bisogno di ulteriore assistenza? Ricevi risposte dai membri della community e dai professionisti di Google SecOps.

