Cloud Billing 匯集了多項工具,可協助您追蹤及瞭解 Google Cloud 支出、支付帳單費用,並發揮最佳成本效益。
本文涵蓋下列主題:
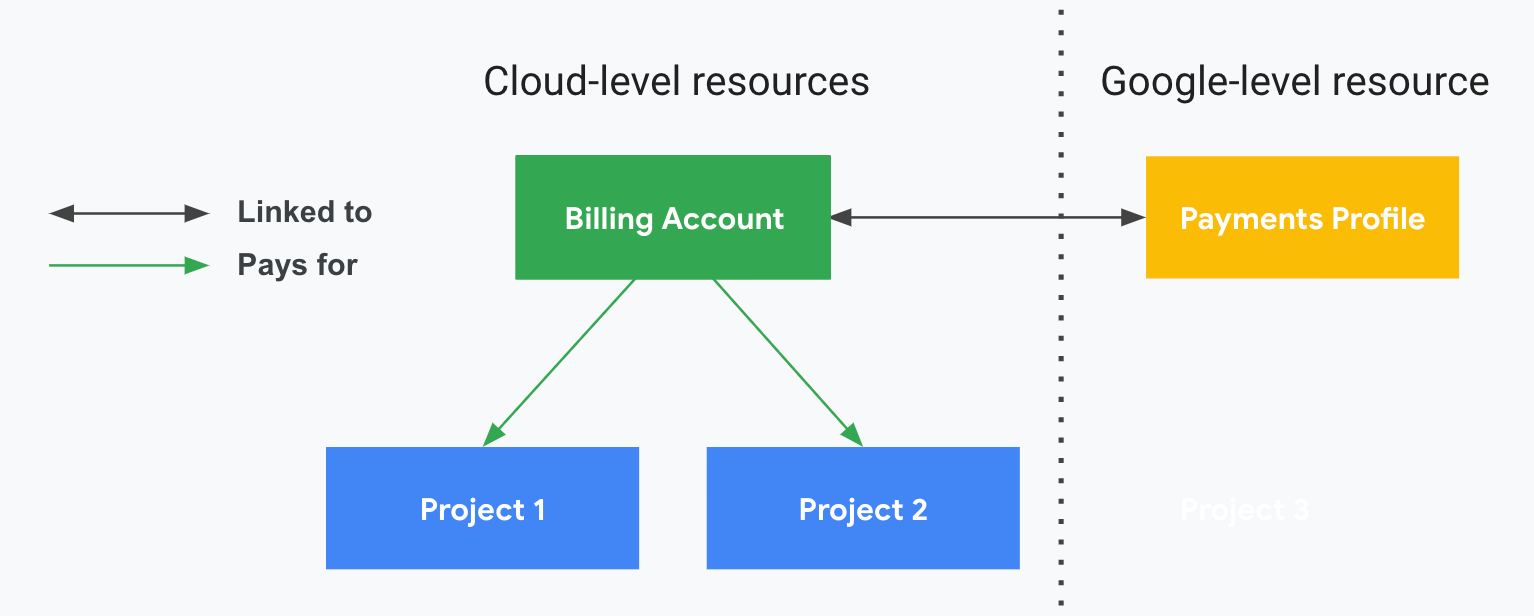
Cloud Billing 帳戶簡介,以及 Cloud Billing 帳戶與 Google 付款資料之間的關係。Cloud Billing 帳戶會支付 Google Cloud 和 Google 地圖平台資源與服務的使用費用。
Google Cloud資源管理總覽。 Google Cloud 資源的整理方式取決於貴機構的結構,並會影響您在 Cloud Billing 報表中分析費用的方式。
Cloud Billing 工具簡介
Cloud Billing 中的工具可協助您監控用量費用、預測支出,並找出節省費用的機會。
開始使用
透過互動式導覽瞭解 Cloud Billing。如果您是Google Cloud新手,本教學課程將介紹基本資訊,逐步說明如何使用 Google Cloud 控制台來掌握及管理費用。
查看帳單報表和費用趨勢。帳單報表可協助您解答「哪項服務 (例如 Compute Engine 或 Cloud Storage) 的成本最高?」等問題。 Google Cloud
監控費用
將帳單資料匯出至 BigQuery。將用量和費用資料匯出至 BigQuery 資料集,並使用該資料集進行詳細分析。您也可以在 Looker Studio 等工具中,以視覺化方式呈現匯出的資料。
建議您盡早啟用 BigQuery 匯出功能,這樣資料就能反映 Google Cloud 一開始的使用情形。
建立預算並設定支出快訊。您可以透過預算追蹤實際支出與預估支出之間的差異。 Google Cloud 接著設定快訊,隨時掌握支出情形。
查看專案的異常狀況。異常狀況是指與過往支出模式相比,使用費用出現尖峰或偏差,與預期支出不同。「異常狀況」資訊主頁會顯示連結帳單帳戶中,與專案相關的所有費用異常狀況。
提高成本效益及控管成本
前往 FinOps 中心查看建議和使用率深入分析。 透過 FinOps 中心,您可以監控及傳達目前的節省金額、探索建議的最佳化成本機會,以及規劃最佳化目標。
申請承諾使用折扣 (CUD)。如果可預測工作負載的資源需求,您可以購買 Google Cloud 承諾,只要承諾在指定期間內達到一定的資源用量,即可享有折扣價。
如果貴機構已註冊承諾使用折扣,請參閱這篇文章,瞭解如何分析承諾使用折扣的效益。
使用程式輔助通知自動控管費用。當您收到預算或異常快訊時,可使用程式輔助通知自動執行成本控制回應,例如將快訊轉寄至其他媒介,或調整配額來控管資源用量。
Cloud Billing 帳戶和 Google 付款資料簡介
您可以在 Google Cloud 設定 Cloud Billing 帳戶,並指定特定 Google Cloud 資源和 Google Maps Platform API 的費用由誰支付。Cloud Billing 帳戶的存取權控管是依照 IAM 角色所建立。Cloud 帳單帳戶會連結到 Google 付款資料。Google 付款資料包含用於收費的付款方式。
| Cloud 帳單帳戶 | Google 付款資料 |
|---|---|
Cloud 帳單帳戶:
|
Google 付款資料:
|
Cloud Billing 帳戶類型
Cloud Billing 帳戶分為兩種:
自助式 (或線上) 帳戶
- 自助式帳戶的計費狀態為免費試用帳戶或付費帳戶。
- 付款方式為信用卡、簽帳金融卡或透過 ACH 直接扣款,視您所在國家或地區的金融服務供應情況而定。
- 如果帳戶的計費狀態為「已付費帳戶」,系統會自動向連結至 Cloud Billing 帳戶的付款方式收取費用。
- 可在線上申請自助式帳戶。
- 系統為自助式帳戶產生的文件包括對帳單、付款收據和稅務月結單,您可以在 Google Cloud 控制台中存取這些文件。
可開立月結單的 (或離線) 帳戶
- 可開立月結單帳戶的可計費狀態為「付費帳戶」。
- 付款方式為支票或電匯。
- 月結單會以實體郵件或電子郵件的形式寄送。
- 您也可以在 Google Cloud 控制台中存取月結單和付款收據。
- 您必須符合月結帳單資格。 進一步瞭解月結帳單的申請條件。
Google 付款資料類型
建立 Google 付款資料時,系統會要求您指定資料類型。請務必提供正確的資訊,以便我們進行稅務及身分驗證。建立付款資料後,這項設定就無法變更。設定 Google 付款資料時,請務必針對所規劃的使用資料方式,選擇最適合的類型。
Google 付款資料分為兩種:
個人
- 您使用帳戶支付個人費用。
- 如果您將付款資料註冊為「個人」,則只有您才能管理資料。您無法新增或移除使用者,也不能變更資料的相關權限。
Business
- 您透過帳戶支付企業、機構、合作夥伴或教育機構費用。
- 您可以透過 Google 付款中心支付各種 Google 產品/服務的相關費用,例如 Play 中的應用程式和遊戲內容、Google Ads、 Google Cloud和 Fi 電信服務等。
- 「公司」資料可讓您將其他使用者新增到您管理的 Google 付款資料,以便讓多人存取或管理付款資料。
- 所有新增到「公司」資料的使用者皆可查看該資料的相關付款資訊。
收費週期
Cloud Billing 帳戶的收費週期會決定您支付 Google Cloud 服務和 Google 地圖平台 API 使用費的方式和時間。
如果是自助式 Cloud Billing 帳戶,系統會自動透過下列其中一種方式向您收取 Google Cloud 費用:
- 按月收費:每個月定期收取費用。
- 帳單信用額度:帳戶的應繳費用累計達特定金額時才會收費。
如果是自助式 Cloud Billing 帳戶,系統會在您建立帳戶時自動指派收費週期。您無法選擇或變更收費週期。
對於可開立月結單的 Cloud Billing 帳戶,您通常每月會收到一張月結單,但分開開立月結單的情況除外。您必須支付月結單的時間 (即付款條件),取決於您與 Google 簽訂的協議。
帳單聯絡人
Cloud 帳單帳戶包含一或多個聯絡人,這些聯絡人是在連結至 Cloud 帳單帳戶的 Google 付款資料中定義。當付款方式出現特定帳單資訊 (例如需要更新信用卡時),系統會通知這些已經設定好的聯絡人。如要存取及管理這份聯絡人清單,請使用 Google 付款中心或 Google Cloud 主控台。
子帳戶
子帳戶適用於經銷商。如果您是經銷商,可以使用子帳戶代表客戶的費用,以進行退款作業。
有了 Cloud Billing 子帳戶,您就能將各項專案的費用集中顯示於月結單中的獨立區段。帳單子帳戶是 Cloud Billing 帳戶,由經銷商的上層 Cloud Billing 帳戶擁有。所有帳單子帳戶的使用費用,都會由經銷商的上層 Cloud Billing 帳戶支付。請注意,上層 Cloud Billing 帳戶必須採用月結制。
在大部分情況下,子帳戶的功能與 Cloud Billing 帳戶相同:可以與專案相連結、可以設定相關的 Cloud Billing 資料匯出選項,也能定義帳戶的 IAM 角色。在月結單上,子帳戶關聯專案所產生的任何費用都會經過分類並個別加總。如果適用分開結帳,則會產生多張月結單。另外,在資源管理方面,您可以在子帳戶中設定完全獨立的存取權控制政策,藉此區隔及管理客戶。
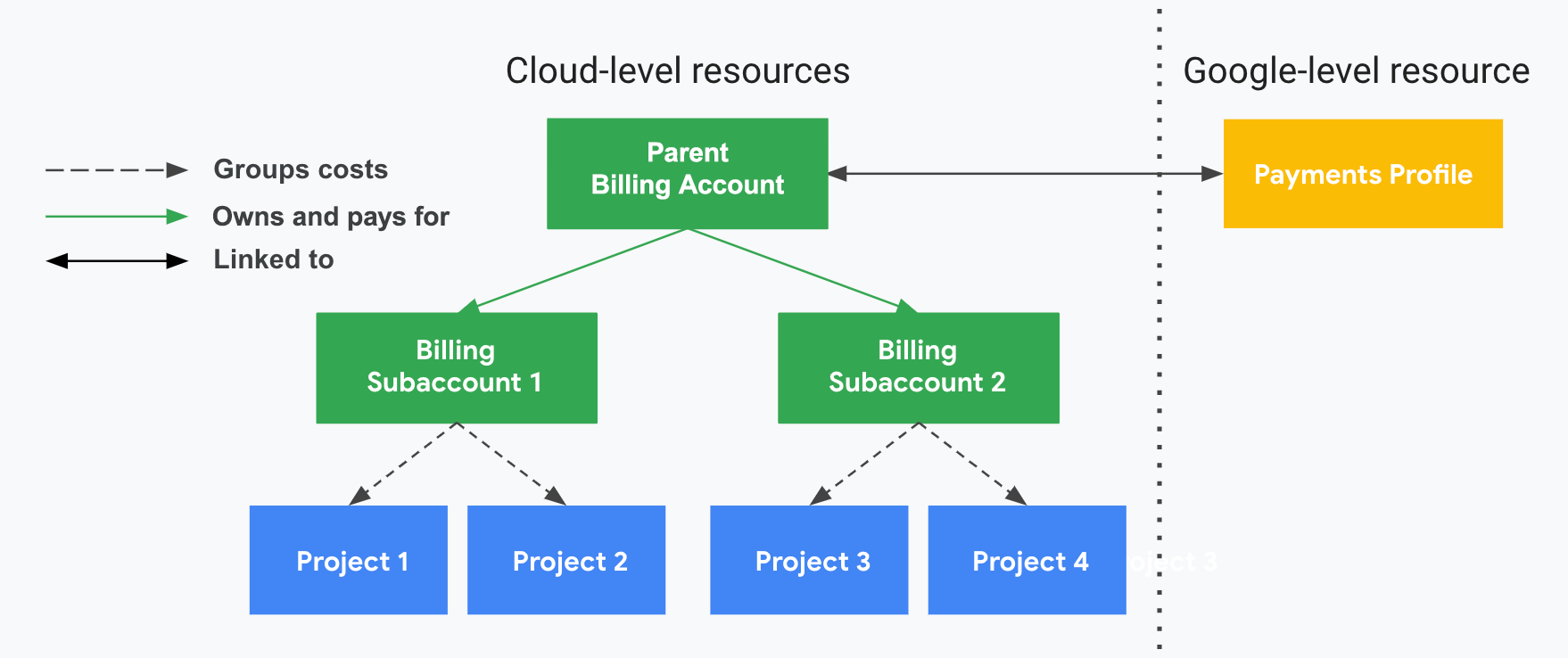
您可以使用 Cloud Billing 帳戶 API 建立及管理子帳戶。使用 API 連結現有系統,以及藉由程式設計的方式管理新客戶或退款群組的帳戶。
帳單資源管理簡介
您可以透過各種方式設定 Google Cloud 帳單,以滿足不同的需求。本節將介紹機構和帳單的核心概念,並說明如何有效使用這些功能。
如要瞭解如何整理資源,有效監控費用,請參閱 Cloud 帳單資源機構與存取權管理指南。
關於資源
在 Google Cloud環境中,資源可以指用來處理工作負載 (例如虛擬機器和資料庫) 的服務層級資源,或是倚賴這些服務的帳戶層級資源,例如專案、資料夾和機構。
資源管理
資源管理關注的重點是應該如何針對您的公司/團隊設定以及將存取權授予各種雲端資源,尤其是倚賴服務層級資源的帳戶層級資源的設定和機構。帳戶層級資源是指與設定和管理 Google Cloud 帳戶有關的資源。
資源階層
Google Cloud 資源會以階層方式整理。這樣的階層結構可讓 Google Cloud與機構經營結構保持一致,也能讓您管理相關資源群組的存取控制及權限。資源階層能為存取權管理政策 (Identity and Access Management) 和組織政策提供邏輯附加點。
IAM 和機構政策都是透過階層繼承,階層中每個節點的有效政策都是直接套用於節點的政策以及沿用自其祖系的政策。
下圖顯示資源階層的範例,並說明與管理 Google Cloud帳戶相關的核心帳戶層級資源。
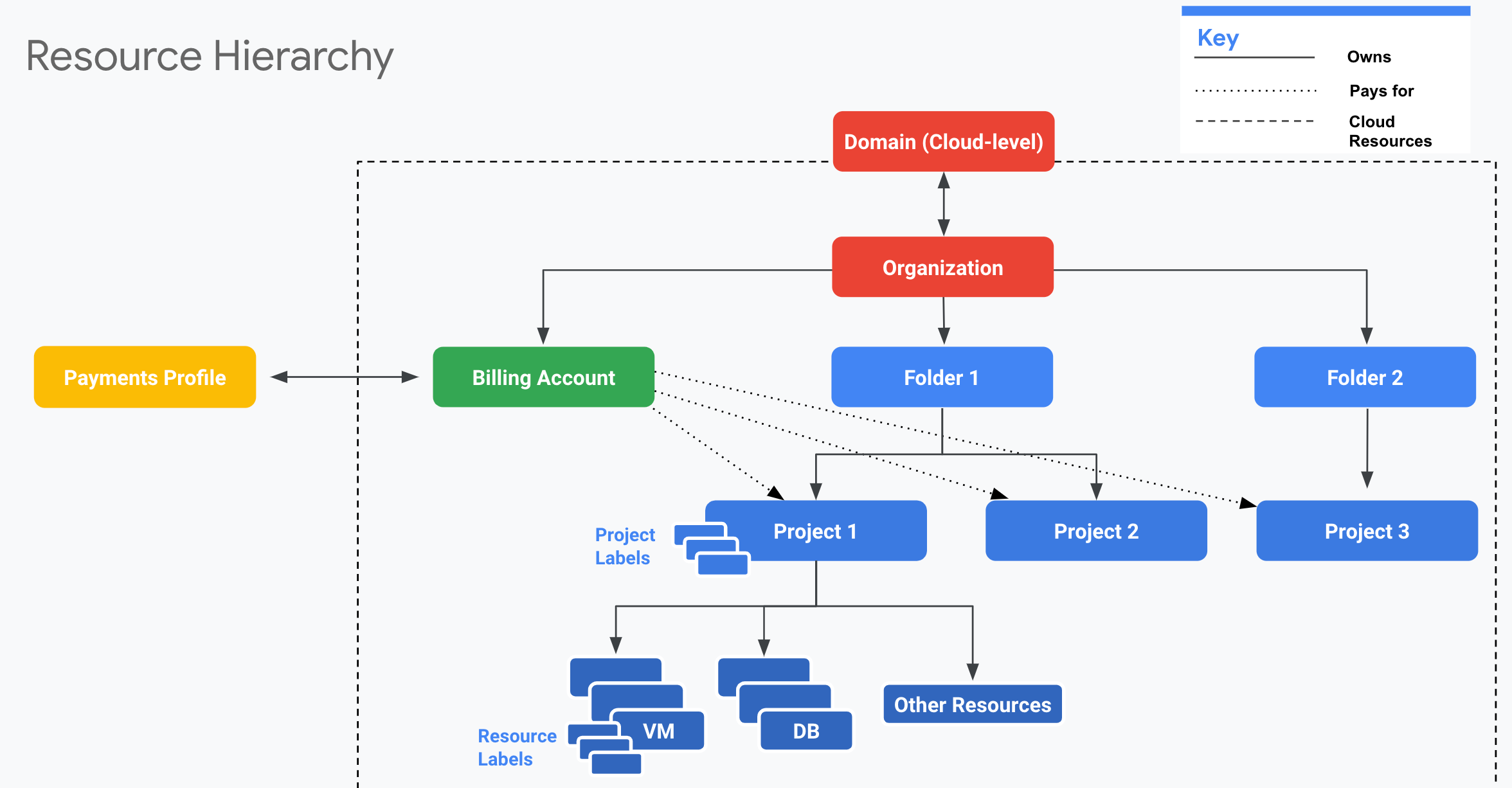
網域
- 您的公司網域等同貴機構的主要身分,也是公司用來使用 Google 服務的識別依據,上述服務包括Google Cloud。
- 透過網域,您可以管理貴機構的使用者。
- 在網域層級定義哪些使用者在使用 Google Cloud時,應與機構建立關聯。
- 網域也是制定使用者和裝置通用管理政策的地方,例如,針對機構中的任何使用者啟用兩步驟驗證及重設密碼等。
- 網域會連結到 Google Workspace 或 Cloud Identity 帳戶。
- Google Workspace 或 Cloud Identity 帳戶只會與一個機構相關聯。
- 您可使用 Google 管理控制台 (admin.google.com) 管理網域層級的功能。
如要進一步瞭解資源階層,請參閱 Resource Manager 說明文件。
機構
- 機構是資源階層的根節點。 Google Cloud
- 隸屬於機構的所有 Google Cloud 資源會在該機構的節點下方進行分組,可讓您定義其內所有專案、資料夾、資源和 Cloud Billing 帳戶的設定、權限以及政策。
- 機構只會與一個網域 (以 Google Workspace 或 Cloud Identity 帳戶建立) 相關聯,而且會在您在Google Cloud中設定網域時自動建立。
- 您可以透過機構集中管理 Google Cloud資源,以及使用者對於這些資源的存取權。包括:
- 主動式管理:視需要重組資源。例如,重組或啟動新部門可能需要新專案和資料夾。
- 被動式管理:針對遺失資源重新取得存取權時,機構資源可提供安全措施。例如,您的其中一個團隊成員失去存取權或離職時,就會需要這種管理。
- 您可在 Google Cloud 控制台中管理與 Google Cloud相關的各種角色和資源 (包括機構、專案、資料夾、資源和 Cloud 帳單帳戶)。
如要進一步瞭解機構,請參閱下列說明文件:
資料夾
- 資料夾是進行分組的機制,可包含專案、其他資料夾,或是以上兩者的組合。
- 您必須擁有機構節點,才能使用資料夾。
- 資料夾及專案都對應在機構節點下。
- 資料夾可用來將具有相同 IAM 政策的資源歸組。
- 資料夾內可包含多個資料夾或資源,但是每個資料夾或資源只能有一個父項。
如要進一步瞭解如何使用資料夾,請參閱建立及管理資料夾。
專案
- 所有服務層級資源均會從屬於專案,而專案也就是 Google Cloud中的基礎層級機構實體。
- 專案是使用服務層級資源 (例如 Compute Engine 虛擬機器、Pub/Sub 主題和 Cloud Storage 值區) 的必要項目。
- 您可以使用專案來代表邏輯專案、團隊、環境,或是可對應至某個企業功能/結構的其他集合。
- 專案可做為啟用服務、API 和 IAM 權限的基礎。
- 不過請注意,各項資源都只能存在於單一專案中。
如要進一步瞭解專案,請參閱下列說明文件:
資源
- Google Cloud 服務層級資源是構成所有 Google Cloud 服務的基本元件,例如 Compute Engine 虛擬機器、Pub/Sub 主題和 Cloud Storage 值區。
- 為了計算費用和控管存取權,系統會將資源存放在階層的最低層級中,而該階層也會包含專案和機構。
標籤
- 標籤可協助您分類 Google Cloud 資源 (例如 Compute Engine 執行個體)。
- 標籤是鍵/值組合
- 您可以為每一個資源加上標籤,並根據標籤篩選資源。
- 標籤是精密追蹤費用的好幫手。標籤相關資訊會轉送到帳單系統,讓您依據標籤分析您的費用。
如要進一步瞭解如何使用標籤,請參閱建立及管理標籤。
資源、Cloud Billing 帳戶和 Google 付款資料之間的關係
有兩種類型的關係控制著機構、Cloud Billing 帳戶和專案之間的互動,那就是擁有權及付款連結。
- 擁有權是指 IAM 權限繼承。
- 付款連結會定義專案費用由哪個 Cloud Billing 帳戶支付。
下圖顯示範例機構的擁有權與付款連結之間的關係。
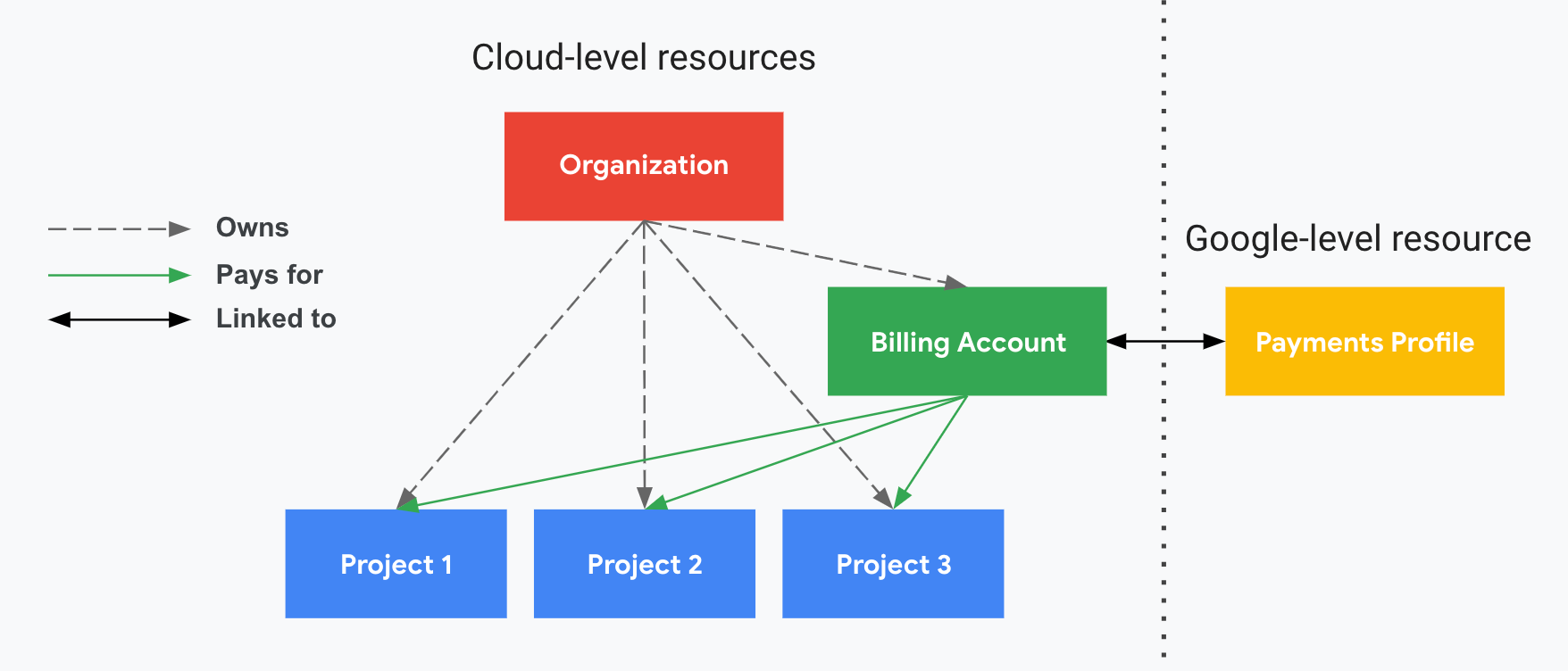
在圖中,機構有專案 1、2 和 3 的擁有權,這代表該機構是這三項專案的 IAM 權限父項。
Cloud Billing 帳戶已連結至專案 1、2 和 3,這代表該三項專案所產生的費用會透過此帳單帳戶支付。
Cloud 帳單帳戶也會連結到 Google 付款資料,其中會儲存姓名、地址和付款方式等資訊。
在這個範例中,獲得機構的 IAM 帳單角色的所有使用者,也都擁有 Cloud Billing 帳戶或專案的這些角色。
如要瞭解如何授予 IAM 帳單角色,請參閱「Cloud Billing 存取權控管總覽」。

