Questa pagina ti aiuta a diagnosticare i problemi di installazione o esecuzione dell'agente di monitoraggio.
Elenco di controllo
Se hai difficoltà a installare o utilizzare l'agente Monitoring, Ecco alcuni aspetti da verificare:
Se i comandi di installazione di Linux generano errori, assicurati di anteporre
sudoai comandi di installazione.Verifica che il servizio dell'agente sia in esecuzione sull'istanza VM:
Per una VM Windows, utilizza il seguente comando PowerShell:
Get-Service -Name StackdriverMonitoringCerca un servizio denominato Stackdriver Monitoring. Se l'agente non è in esecuzione, potrebbe essere necessario riavviarlo.
Per una VM Linux, utilizza il seguente comando:
sudo service stackdriver-agent statusSe l'agente non è in esecuzione, potrebbe essere necessario riavviarlo utilizzando il seguente comando:
sudo service stackdriver-agent restartSe il riavvio non va a buon fine e l'output del log mostra "Disattivato tramite metadati", è probabile che tu stia eseguendo un'immagine da Google Cloud Marketplace, dove l'agente di monitoraggio è disattivato per impostazione predefinita. Questo valore è controllato dalla chiave dei metadati dell'istanza
google-monitoring-enable(con il valore0). Per riattivare l'agente, rimuovi la chiave o imposta il valore su1(consulta Impostare i metadati dell'istanza).Se l'agente non è disattivato tramite i metadati, reinstallalo. Per informazioni su questa procedura, consulta Reinstallazione dell'agente Monitoring.
Controlla se l'agente ha scritto messaggi di errore nei log.
Su Windows, l'agente di monitoraggio scrive i messaggi nel log eventi di Windows.
Su Linux, l'agente di monitoraggio è un pacchetto
collectde registra i messaggi in/var/log/syslogo/var/log/messages. I messaggi di log sono preceduti dacollectdostackdriver-agent:Se visualizzi errori HTTP 429, potresti aver superato le quote dell'API di monitoraggio. Puoi visualizzare la quota disponibile selezionando API e servizi > Dashboard nella consoleGoogle Cloud . Scegli l'API Monitoring.
Se riscontri problemi con il proxy, verifica di aver configurato correttamente il proxy HTTP. Le istruzioni fanno parte della sezione Installazione su Linux e Windows.
Se riscontri problemi di accesso o autorizzazione all'API o messaggi di errore come "Impossibile determinare l'endpoint collectd", consulta la sezione Verifica del progetto e delle credenziali che segue.
Se nei log vengono visualizzati gli errori "Combinazione di plug-in/tipo collectd non supportata" o "ID collectd non supportato", è possibile che tu stia inviando metriche dell'agente non supportate. Questo può accadere nei seguenti scenari:
Hai modificato una delle configurazioni dell'agente per le applicazioni di terze parti. Per annullare le modifiche, puoi reinstallare la configurazione per il plug-in specifico seguendo le istruzioni riportate nella pagina della documentazione pertinente. Se vuoi utilizzare l'agente per inviare la metrica a Monitoraggio, valuta la possibilità di convertirla in metriche definite dall'utente.
Uno dei plug-in delle applicazioni di terze parti sta inviando nuove metriche sconosciute a Monitoraggio. Per informazioni dettagliate su come inviare una richiesta per la revisione e la classificazione di queste metriche, consulta la pagina di assistenza.
Se l'agente sembra funzionare normalmente, ma non ricevi dati o i tuoi criteri di avviso non funzionano come pensi, devi verificare che l'agente invii i dati al progetto corretto. Consulta la sezione seguente, Verifica del progetto e delle credenziali.
Verifica del progetto e delle credenziali
Se l'agente di monitoraggio segnala errori di accesso o autorizzazione oppure se l'agente sembra funzionare normalmente, ma non sono presenti dati o i criteri di avviso non funzionano come previsto, verifica che le credenziali dell'istanza VM siano corrette, inclusa la specifica del progetto corretto:
Se utilizzi un'istanza VM Compute Engine con credenziali standard (non private-key), è improbabile che i dati vengano inviati al progetto sbagliato, ma le tue credenziali potrebbero comunque essere insufficienti. Per informazioni sulle credenziali, consulta Autorizzare l'agente Monitoring. Per verificare le credenziali, consulta la pagina Verificare le credenziali di Compute Engine.
Se utilizzi un'istanza VM Amazon EC2 o se utilizzi le credenziali con chiave privata nell'istanza Compute Engine, le credenziali potrebbero non essere valide o potrebbero provenire dal progetto sbagliato. Per gli account AWS, il progetto utilizzato dall'agente deve essere il progetto Google Cloud a cui stai inviando le metriche. Per informazioni sulle credenziali, consulta Autorizzare l'agente Monitoring. Per verificare le tue credenziali, consulta Verificare le credenziali con chiave privata.
Verifica delle credenziali di Compute Engine
Utilizza la pagina Istanze VM di Compute Engine della Google Cloud console per verificare che l'istanza VM Compute Engine disponga delle credenziali adeguate per l'agente di monitoraggio. In genere, le credenziali vengono aggiunte nell'account di servizio predefinito di tutte le nuove istanze VM di Compute Engine, ma è possibile sovrascrivere i valori predefiniti durante la creazione di un'istanza.
Nella Google Cloud console, vai alla pagina Istanze VM:
Se utilizzi la barra di ricerca per trovare questa pagina, seleziona il risultato con il sottotitolo Compute Engine.
- Se necessario, modifica il progetto Google Cloud attuale in modo che corrisponda a quello associato all'istanza VM di Compute Engine. Ad esempio, se ti viene chiesto di attivare la fatturazione, significa che il progetto corrente non contiene istanze VM Compute Engine.
- Nella pagina Istanze VM, fai clic sul nome dell'istanza VM. Viene visualizzata la pagina dei dettagli dell'istanza VM.
- Nella pagina Dettagli istanza VM, cerca la sezione Ambiti di accesso alle API Cloud:
- Se vedi "Consenti l'accesso completo a tutte le API Cloud", significa che disponi delle credenziali adeguate.
- Se accanto a API Stackdriver Monitoring è visualizzato un nome precedente dell'API Cloud Monitoring e disponi dell'autorizzazione Scrittura solo o Completa, significa che disponi delle credenziali adeguate.
- In caso contrario, l'account di servizio predefinito dell'istanza non dispone delle credenziali necessarie per l'agente. Per utilizzare l'agente nell'istanza, devi aggiungere le credenziali dell'account di servizio con chiave privata. Per le istruzioni, consulta Aggiungere le credenziali.
Se disponi delle credenziali predefinite corrette, vai alla sezione Installazione su Linux e Windows.
Verifica delle credenziali della chiave privata
Per verificare che le credenziali con chiave privata valide siano installate nell'istanza VM, innanzitutto verifica che il file delle credenziali esista nella posizione prevista e poi verifica che le informazioni nel file delle credenziali siano valide. Le credenziali precedentemente valide possono essere revocate utilizzando la sezione IAM e amministrazione > Account di servizio della Google Cloud console. Se non sono presenti credenziali valide, consulta Aggiunta di credenziali per sostituire quelle esistenti o aggiungerne di nuove.
Le credenziali sono presenti?
Per verificare se le credenziali dell'account di servizio con chiave privata sono presenti nell'istanza, esegui i seguenti comandi Linux sull'istanza:
sudo cat $GOOGLE_APPLICATION_CREDENTIALS
sudo cat /etc/google/auth/application_default_credentials.json
Se uno dei comandi mostra un file come quello mostrato di seguito, la tua istanza potrebbe avere credenziali della chiave privata valide. Se entrambi i comandi mostrano un file, viene utilizzato il file indicato da GOOGLE_APPLICATION_CREDENTIALS.
{
"type": "service_account",
"project_id": "{your-project-id}",
"private_key_id": "{your-private-key-id}",
"private_key": "{your-private-key}",
"client_email": "{your-project-number}-{your-key}@developer.gserviceaccount.com",
"client_id": "{your-client-id}",
"auth_uri": "https://accounts.google.com/o/oauth2/auth",
"token_uri": "https://accounts.google.com/o/oauth2/token",
"auth_provider_x509_cert_url": "{x509-cert-url}",
"client_x509_cert_url": "{client-x509-cert-url}"
}
Se non sono presenti file di credenziali, consulta Aggiunta delle credenziali.
Le credenziali sono valide?
Nel file delle credenziali, il campo project_id è il tuo progetto,
client_email identifica l'account di servizio nel progetto
e private_key_id identifica
la chiave privata nell'account di servizio. Google Cloud Confrontale con quelle riportate nella sezione IAM e amministrazione > Account di servizio della consoleGoogle Cloud .
Il file delle credenziali non è valido se una delle seguenti condizioni è vera:
- Stai controllando un'istanza VM di Compute Engine, ma il progettoGoogle Cloud nel file delle credenziali non è il progetto che contiene l'istanza.
- Stai controllando un'istanza Amazon EC2, ma il Google Cloud progetto nel file delle credenziali non è il Google Cloud progetto a cui stai inviando le metriche dal tuo account AWS.
- Il service account elencato non esiste. Potrebbe essere stato eliminato.
- Per l'account di servizio elencato non sono stati attivati i ruoli corretti. Deve avere almeno
roles/monitoring.metricWriter(Monitoring Metric Writer) per la raccolta delle metriche eroles/logging.logWriter(Logs Writer) per la scrittura dei log. - La chiave privata non esiste. Potrebbe essere stato revocato.
Se l'account di servizio è corretto, ma la chiave privata è stata revocata, puoi creare una nuova chiave privata e copiarla nell'istanza. In caso contrario, devi creare un nuovo account di servizio come descritto nella sezione seguente, Aggiunta delle credenziali.
Generazione di nuove credenziali
Se le credenziali non sono valide, svolgi i seguenti passaggi:
- Per ogni progetto collegato contenente istanze che devono essere autorizzate con una chiave privata, ovvero ogni progetto contenente istanze Compute Engine create senza includere l'ambito di accesso
https://www.googleapis.com/auth/monitoring.write, crea un account di servizio e genera una chiave privata, se non esistono già. Procedi come indicato di seguito:-
Nella Google Cloud console, vai alla pagina settings Impostazioni:
Se utilizzi la barra di ricerca per trovare questa pagina, seleziona il risultato con il sottotitolo Monitoring.
- Seleziona la scheda Ambito metrica.
- Identifica il progetto contenente le risorse Compute Engine in discussione e vai alla Google Cloud console.
- Vai alla pagina Account di servizio IAM della
console Google Cloud , seleziona il tuo Google Cloud progetto, crea un nuovo
account di servizio e poi genera una nuova chiave privata per quell'account di servizio.
Per eseguire questi passaggi, svolgi una delle seguenti operazioni:
Vai alla pagina Account di servizio IAM, seleziona il tuo Google Cloud progetto e poi segui i passaggi descritti in Creare un account di servizio:
Fai clic sul seguente pulsante e seleziona il tuo Google Cloud progetto:
Creare l'account di servizio e scaricare la chiave
Il pulsante precedente automatizza la procedura di creazione e download di una chiave sul sistema locale per l'account di servizio specifico dell'agente. Se necessario, la procedura crea anche l'account di servizio richiesto e garantisce che disponga delle autorizzazioni corrette. Gli account di servizio specifici dell'agente hanno un nome simile a
stackdriver-1234@PROJECT_ID.iam.gserviceaccount.com. Riceverai una notifica al termine di queste azioni con una finestra di dialogo simile alla seguente: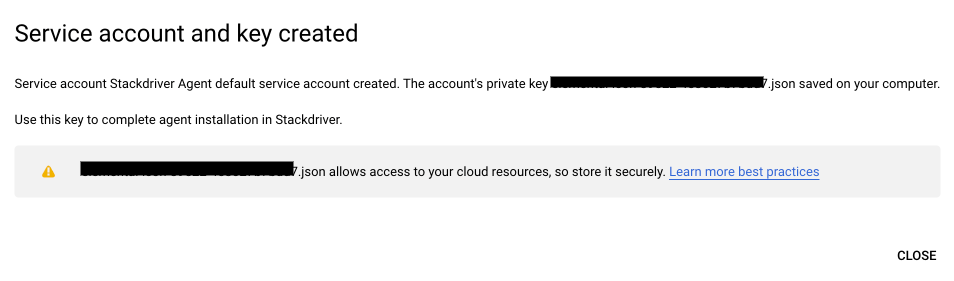
-
Sostituisci la chiave privata nelle istanze corrispondenti all'account di servizio in questione.
- Su Linux, sostituisci la chiave privata situata in
/etc/google/auth/application_default_credentials.json. - Su Windows, sostituisci la chiave privata che si trova in
C:\ProgramData\Google\Auth\application_default_credentials.json. Per ulteriori informazioni, consulta Copiare la chiave privata nell'istanza.
- Su Linux, sostituisci la chiave privata situata in
Riavvia l'agente
- Su Linux, esegui
sudo service stackdriver-agent restart - Su Windows, vai alla console di gestione dei servizi e riavvia il servizio
Cloud Monitoring.
- Su Linux, esegui
Se hai più progetti che richiedono nuove chiavi private, ripeti questa procedura per ciascuno di essi.
Per verificare che la chiave privata sia corretta, consulta Le credenziali sono presenti?. In particolare:
- Leggi il file JSON della chiave privata nell'istanza, ad esempio (su Linux):
sudo cat /etc/google/auth/application_default_credentials.json - Assicurati che il valore del campo
project_idcorrisponda a quello del progetto monitorato per cui hai appena generato le credenziali.
Verifica dei dati dell'agente
Per verificare che l'agente invii correttamente le metriche, utilizza il metodo timeSeries.list dell'API di monitoraggio per cercare i dati delle serie temporali recenti dell'istanza VM. Puoi chiamare il metodo utilizzando Explorer API nella pagina della documentazione del metodo. Se non vedi alcun dato, è possibile che l'agente stia inviando i dati al progetto sbagliato. Per verificarlo, consulta Verificare il progetto e le credenziali.
Ecco le istruzioni dettagliate per l'utilizzo del metodo
timeSeries.list:
Determina l'ID istanza dell'istanza VM in cui hai installato l'agente:
Istanze Compute Engine: vai alla pagina dei dettagli di Compute Engine per la tua istanza. Nella parte inferiore della pagina, fai clic su Equivalente REST. L'ID è un numero di 19 cifre.
Istanze Amazon EC2: l'ID di ogni istanza viene visualizzato nell'elenco delle istanze. L'ID è simile a
i-1a2b3c4d.
Vai alla pagina della documentazione relativa al metodo
timeSeries.list.Compila il modulo di Explorer API:
Imposta name sul progetto contenente l'istanza VM, preceduta da
projects/. Ad esempio:projects/[YOUR_PROJECT_ID].Imposta filter sulla riga seguente per scegliere una metrica dell'agente dalla tua istanza VM. Copia e incollalo in Esplora API, quindi modifica l'ID istanza VM:
metric.type = "agent.googleapis.com/memory/bytes_used" AND resource.label.instance_id = "[YOUR-VM-INSTANCE-ID]"Imposta l'intervallo di tempo di ricerca. Ti consigliamo di lasciare un intervallo di circa cinque minuti:
Imposta interval.endTime sull'ora GMT corrente, che puoi trovare su time.is/GMT. L'ora deve essere formattata come nell'esempio seguente. Non racchiudere la data e l'ora tra virgolette:
2016-10-31T14:10:00ZImposta interval.startTime su circa cinque minuti prima dell'ora di fine, utilizzando lo stesso formato.
Lascia vuoti tutti gli altri campi.
Fai clic su Execute (Esegui).
Dovresti visualizzare un output simile al seguente:
{
"timeSeries": [
{
"metric": {
"labels": {
"state": "buffered"
},
"type": "agent.googleapis.com/memory/bytes_used"
},
"resource": {
"type": "[INSTANCE-TYPE]",
"labels": {
"instance_id": "[YOUR-VM-INSTANCE-ID]",
"zone": "[YOUR-INSTANCE-ZONE]",
"project_id": "[YOUR-PROJECT-ID]"
}
},
"metricKind": "GAUGE",
"valueType": "DOUBLE",
"points": [
{
"interval": {
"startTime": "[START_TIME]",
"endTime": "[END_TIME]"
},
"value": {
"doubleValue": 27451392
}
},
...
Se la chiamata API restituisce dati delle serie temporali dall'istanza VM, come mostrato sopra, l'agente funziona correttamente e hai finito.
Se non vengono visualizzati dati delle serie temporali, controlla quanto segue:
Se la chiamata API genera un messaggio di errore, non indica un problema con l'agente. Verifica che i campi di Explorer API siano compilati correttamente:
Gli errori "Argomento non valido" indicano probabilmente un problema con l'ortografia e il formato dell'ID progetto, del filtro o dei due timestamp.
I requisiti per gli argomenti timestamp dipendono dal tipo di metrica specificato. Un tipo di metrica registra dati
GAUGE,DELTAoCUMULATIVE. Per maggiori informazioni, consultaMetricKind.Per le metriche
DELTAeCUMULATIVE, sono obbligatorie sia l'ora di inizio sia quella di fine, che deve essere successiva all'ora di inizio. Questi tipi di metriche registrano le variazioni misurate nel tempo, pertanto le ore di inizio e di fine devono definire un intervallo diverso da zero.Gli errori "Non autorizzato" possono indicare che hai scritto male l'ID progetto.
Gli errori "Non trovato" possono indicare che hai omesso il prefisso obbligatorio
projects/nel campo "nome".
Risolvi i problemi e riprova a eseguire la chiamata all'API.
Se la chiamata all'API va a buon fine, ma viene visualizzata solo una risposta vuota,
{ }, controlla che il filtro e l'intervallo di tempo siano corretti. Errori di formattazione i timestamp possono comportare la mancata restituzione di dati. Se tutto sembra corretto, ma non ricevi dati, significa che l'agente non invia dati sulle metriche o almeno non al progetto che ti aspetti. Potrebbe indicare un problema con le credenziali. Consulta la sezione Verificare le credenziali della chiave privata.
Reinstallazione dell'agente Monitoring
L'installazione della versione più recente dell'agente può risolvere molti problemi:
Se hai la certezza che il problema non riguarda le credenziali, puoi saltare вперед a Installazione su Linux e Windows.
Per un'installazione completa dell'agente e di eventuali credenziali necessarie, consulta Installare l'agente Monitoring.
Determinare su quali VM Linux è installato l'agente
Esegui una delle seguenti query per vedere su quali VM Linux è in esecuzione l'agente:
Tieni presente che per ogni query devi inserire il nome del progetto e modificare gli intervalli di tempo.
Riavvio automatico dell'agente
Puoi configurare uno script per verificare se l'agente è in esecuzione e poi riavviarlo nel caso in cui abbia avuto un arresto anomalo.
Ad esempio, su Linux, puoi creare la seguente voce crontab per controllare lo stato dell'agente ogni 5 minuti:
*/5 * * * * /bin/pidof stackdriver-collectd >/dev/null 2>&1 || /usr/sbin/service stackdriver-agent restart >/dev/null 2>&1
Problemi noti
Le sezioni seguenti descrivono i problemi noti dell'agente di monitoraggio.
Problema di accesso ai dati di elaborazione (Windows)
Nel Registro eventi di Windows potresti visualizzare un messaggio di errore dell'agente simile al seguente:
Read access denied for processes: Registry (84), smss.exe (264), csrss.exe (376), wininit.exe (448), csrss.exe (456), services.exe (580), NisSrv.exe (3008), MsMpEng.exe (3624), csrss.exe (7044)
Questo messaggio indica che l'agente non ha accesso a questi dati sul tuo sistema. Per non visualizzare più questo messaggio, puoi fornire all'utente SYSTEM autorizzazioni sufficienti per leggere i dati di processo per i processi e i servizi elencati nei messaggi di errore. Se non hai bisogno di questi dati, puoi ignorare tranquillamente questi messaggi informativi.
Problemi relativi alla cache dei metadati (Linux)
Potresti visualizzare un messaggio di errore nel file di log di sistema di Linux (/var/log/syslog su Debian / Ubuntu o /var/log/messages su Red Hat / CentOS / SLES) simile al seguente:
collectd[25571]: uc_update: Value too old: name = myhost/processes-all/ps_vm;
value time = 1511345468.180; last cache update = 1511345468.180;
write_gcm: wg_update_stats failed.
write_gcm: uc_update returned an error.
Questi messaggi sono avvisi innocui e non indicano una perdita di dati. Questi messaggi vengono generati dall'attuale implementazione del plug-in dei processi quando si verifica una mancata corrispondenza del timestamp.
Problema di eliminazione del punto dati con valore infinito (Linux)
Potresti visualizzare un messaggio di errore nel file di log di sistema di Linux (/var/log/syslog su Debian / Ubuntu o /var/log/messages su Red Hat / CentOS / SLES) simile al seguente:
write_gcm: can not take infinite value
Questo messaggio indica che un singolo punto dati con formato non corretto viene ignorato. In genere, non sono dannosi e possono essere ignorati.
Problema di limitazione della chiave dei metadati (Linux)
Potresti visualizzare un messaggio di errore nel file di log di sistema di Linux (/var/log/syslog su Debian / Ubuntu o /var/log/messages su Red Hat / CentOS / SLES) simile al seguente:
collectd[7440]:match_throttle_metadata_keys: uc_meta_data_add returned an error
collectd[7440]:match_throttle_metadata_keys: mtg_update_stats failed
Questo messaggio indica che l'aggiornamento dello stato del throttling della memoria non è riuscito una volta. In genere è innocuo, ma potrebbe indicare che l'agente sta esaurendo la memoria, soprattutto se si verifica di frequente.
Problema di quota dell'API Cloud Monitoring (Linux)
Potresti visualizzare un messaggio di errore nel file di log di sistema di Linux (/var/log/syslog su Debian / Ubuntu o /var/log/messages su Red Hat / CentOS / SLES) simile al seguente:
collectd[25198]: write_gcm: Unsuccessful HTTP request 429
Questo messaggio indica che è stato raggiunto il limite di quota dell'API Cloud Monitoring. Segui la guida sulle quote per informazioni su come gestire il limite di quota.
Utilizzo elevato della memoria a causa di un valore COLLECTD_INTERVAL basso (Linux)
Potresti notare un utilizzo elevato della memoria dell'agente quando il valore COLLECTD_INTERVAL è impostato su un valore più breve rispetto al valore predefinito 60 seconds, ad esempio 10
seconds. Si tratta di una limitazione nota dell'agente perché invia le richieste in modo seriale da un singolo thread. Per attenuare questo problema, valuta la possibilità di ridurreCOLLECTD_INTERVAL solo per un sottoinsieme di metriche richieste e lascia il resto delle metriche con l'intervallo predefinito.
Problema di overflow del buffer dei token (Linux)
Nel file di log di sistema di Linux (/var/log/syslog su Debian / Ubuntu o /var/log/messages su Red Hat / CentOS / SLES) potresti visualizzare un messaggio di errore simile al seguente:
write_gcm: Error or buffer overflow when building auth_header
write_gcm: wg_oauth2_get_auth_header failed.
write_gcm: wg_transmit_unique_segment failed.
write_gcm: wg_transmit_unique_segments failed. Flushing.
Questi messaggi indicano che è necessario eseguire l'upgrade dell'agente di monitoraggio alla versione 6.1.2 o successive.
Il repository ha modificato il valore "Origine" (Linux)
Quando esegui l'upgrade dell'agente, lo installi o esegui apt-get update su Debian/Ubuntu Linux, potresti visualizzare un messaggio di errore simile al seguente:
E: Repository 'https://packages.cloud.google.com/apt google-cloud-monitoring-buster-all InRelease' changed its 'Origin' value from 'google-cloud-monitoring-buster' to 'namespaces/cloud-ops-agents-artifacts/repositories/google-cloud-monitoring-buster-all'
E: Repository 'https://packages.cloud.google.com/apt google-cloud-monitoring-buster-all InRelease' changed its 'Label' value from 'google-cloud-monitoring-buster' to 'namespaces/cloud-ops-agents-artifacts/repositories/google-cloud-monitoring-buster-all'
Questo messaggio indica che la cache del repository dei pacchetti potrebbe essere diversa dalla fonte. Per risolvere il problema, esegui il seguente comando:
apt-get --allow-releaseinfo-change update
Quindi, esegui di nuovo l'upgrade o l'installazione.
Agente rimosso segnalato dalla Google Cloud console come installato
Dopo aver disinstallato l'agente, la Google Cloud console potrebbe richiedere fino a un'ora per segnalare questa modifica.
L'agente di monitoraggio non viene visualizzato nell'elenco Disinstalla un programma di Windows
Per disinstallare l'agente di monitoraggio se non è presente nell'elenco Disinstalla un programma del Pannello di controllo di Windows, esegui uninstall.exe dalla directory in cui l'hai installato.

