Questa pagina descrive come utilizzare le chiavi di crittografia gestite dal cliente (CMEK) create manualmente per Spanner.
Per scoprire di più su CMEK, consulta la panoramica delle chiavi di crittografia gestite dal cliente (CMEK).
Crea un database abilitato per CMEK
Crea una chiave in Cloud Key Management Service (Cloud KMS). Puoi utilizzare i seguenti tipi di chiavi che hanno diversi livelli di protezione in Spanner:
La chiave deve trovarsi nella stessa posizione dell'istanza Spanner. Ad esempio, se la configurazione dell'istanza Spanner si trova in
us-west1, anche la posizione del portachiavi Cloud KMS deve essereus-west1.Non tutte le configurazioni di istanze multiregionali di Spanner hanno una posizione del portachiavi Cloud KMS corrispondente. Per i database Spanner nelle configurazioni di istanze personalizzate, a due regioni o multiregionali, puoi utilizzare più chiavi Cloud KMS regionali (a regione singola) per proteggere il tuo database. Ad esempio:
- Se il tuo database Spanner si trova nella configurazione
dell'istanza multiregionale
nam14, puoi creare chiavi Cloud KMS inus-east4,northamerica-northeast1eus-east1. - Se il tuo database si trova in una configurazione di istanza personalizzata che utilizza
nam3come configurazione di base con una replica di sola lettura aggiuntiva inus-central2, puoi creare chiavi Cloud KMS inus-east4,us-east1,us-central1eus-central2.
(Facoltativo) Per visualizzare un elenco delle posizioni delle repliche nella configurazione dell'istanza Spanner, utilizza il comando
gcloud spanner instances get-locations:gcloud spanner instances get-locations <var>INSTANCE_ID</var>Per maggiori informazioni, consulta le seguenti risorse:
- Se il tuo database Spanner si trova nella configurazione
dell'istanza multiregionale
Concedi a Spanner l'accesso alla chiave.
In Cloud Shell, crea e visualizza l'agente di servizio oppure visualizzalo se l'account esiste già:
gcloud beta services identity create --service=spanner.googleapis.com \ --project=PROJECT_IDSe ti viene chiesto di installare il componente gcloud Beta Commands, digita
Y. Dopo l'installazione, il comando viene riavviato automaticamente.Il comando
gcloud services identitycrea o recupera l'agente di servizio che Spanner può utilizzare per accedere alla chiave Cloud KMS per tuo conto.L'ID account di servizio ha il formato di un indirizzo email:
Service identity created: service-xxx@gcp-sa-spanner.iam.gserviceaccount.comConcedi il ruolo Autore crittografia/decrittografia CryptoKey Cloud KMS(
cloudkms.cryptoKeyEncrypterDecrypter) al account di servizio per ogni regione (--location) nella configurazione dell'istanza Spanner. Per farlo, esegui il comandogcloud kms keys add-iam-policybinding:gcloud kms keys add-iam-policy-binding KMS_KEY \ --location KMS_KEY_LOCATION \ --keyring KMS_KEY_RING \ --project=PROJECT_ID \ --member serviceAccount:service-xxx@gcp-sa-spanner.iam.gserviceaccount.com \ --role roles/cloudkms.cryptoKeyEncrypterDecrypterEcco un output di esempio:
Updated IAM policy for key [KMS_KEY]Se utilizzi più chiavi Cloud KMS per proteggere il tuo database, esegui il comando
gcloud kms keys add-iam-policybindingper tutte le chiavi.Questo ruolo garantisce che l'account di servizio disponga dell'autorizzazione per criptare e decriptare con la chiave Cloud KMS. Per ulteriori informazioni, consulta Autorizzazioni e ruoli Cloud KMS.
Crea il database e specifica la chiave Cloud KMS.
Console
Utilizza la console per creare database nelle configurazioni delle istanze regionali.
Nella console Google Cloud , vai alla pagina Istanze.
Fai clic sull'istanza in cui vuoi creare un database.
Fai clic su Crea database e compila i campi obbligatori.
Fai clic su Mostra opzioni di crittografia.
Seleziona Chiave Cloud KMS.
Seleziona una chiave dall'elenco a discesa.
L'elenco delle chiavi è limitato al progetto Google Cloud corrente. Per utilizzare una chiave di un progetto Google Cloud diverso, crea il database utilizzando gcloud CLI anziché la consoleGoogle Cloud .
Una volta creato il database, puoi verificare che sia abilitato a CMEK visualizzando la pagina Panoramica del database.
gcloud
Per creare un database abilitato per CMEK in una configurazione di istanza regionale, personalizzata o multiregionale, esegui il comando gcloud spanner databases create:
gcloud spanner databases create DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_ID \
--ddl="CREATE TABLE Users (Id INT64 NOT NULL, FirstName STRING(100) NOT NULL, LastName STRING(100) NOT NULL,) PRIMARY KEY (Id)" \
--kms-project=KMS_PROJECT_ID \
--kms-location=KMS_KEY_LOCATION \
--kms-keyring=KMS_KEYRING \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]Per verificare che un database sia abilitato per CMEK, esegui il comando
gcloud spanner databases describe:
gcloud spanner databases describe DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDI database abilitati per CMEK includono un campo per encryptionConfig, come mostrato nell'output di esempio seguente:
encryptionConfig:
kmsKeyNames:projects/my-kms-project/locations/eur5/keyRings/my-kms-key-ring/cryptoKeys/my-kms-key
name: projects/my-spanner-project/instances/my-instance/databases/my-db
state: READY
Librerie client
C#
Per creare un database abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un database abilitato per CMEK in una configurazione dell'istanza multiregionale:
C++
Per creare un database abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un database abilitato per CMEK in una configurazione dell'istanza multiregionale:
Vai
Per creare un database abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un database abilitato per CMEK in una configurazione dell'istanza multiregionale:
Java
Per creare un database abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un database abilitato per CMEK in una configurazione dell'istanza multiregionale:
Node.js
Per creare un database abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un database abilitato per CMEK in una configurazione dell'istanza multiregionale:
PHP
Per creare un database abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un database abilitato per CMEK in una configurazione dell'istanza multiregionale:
Python
Per creare un database abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un database abilitato per CMEK in una configurazione dell'istanza multiregionale:
Ruby
Per creare un database abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un database abilitato per CMEK in una configurazione dell'istanza multiregionale:
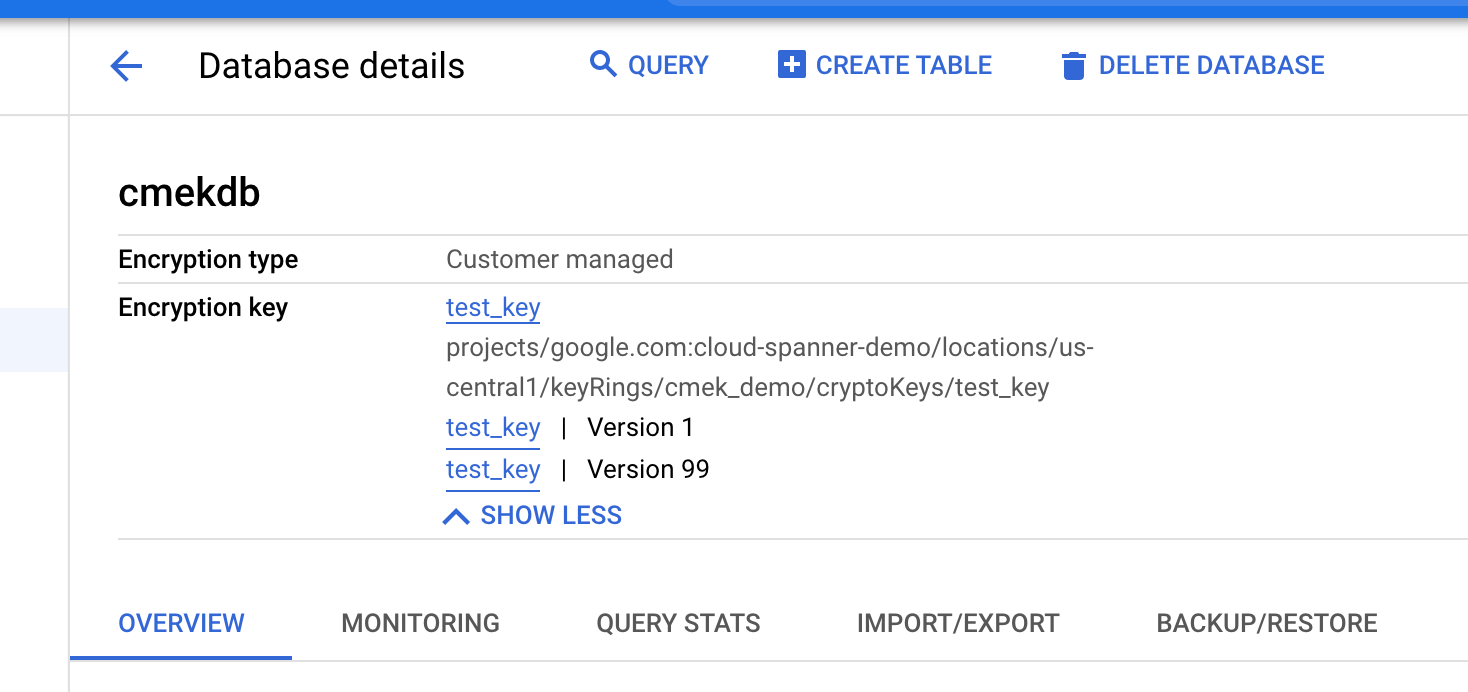
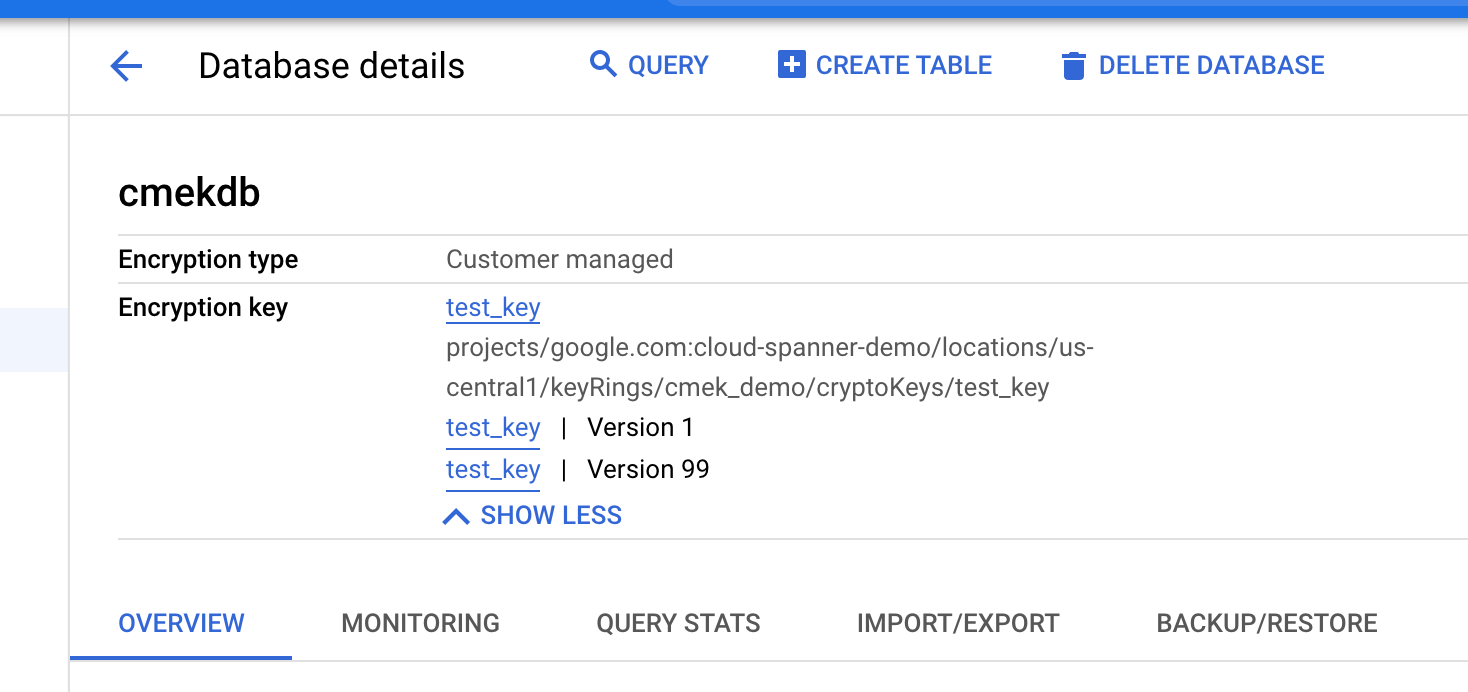
Visualizzare le versioni delle chiavi in uso
Il campo encryption_info
del database mostra informazioni sulle versioni chiave.
Quando la versione della chiave di un database cambia, la modifica non viene propagata immediatamente
a encryption_info. Potrebbe essere necessario un po' di tempo prima che la modifica venga visualizzata in
questo campo.
Console
Nella console Google Cloud , vai alla pagina Istanze.
Fai clic sull'istanza contenente il database che vuoi visualizzare.
Fai clic sul database.
Le informazioni sulla crittografia vengono visualizzate nella pagina Dettagli database.
gcloud
Puoi ottenere il encryption_info di un database eseguendo il comando
gcloud spanner databases describe
o gcloud spanner databases list. Ad esempio:
gcloud spanner databases describe DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDEcco un output di esempio:
name: projects/my-project/instances/test-instance/databases/example-db
encryptionInfo:
- encryptionType: CUSTOMER_MANAGED_ENCRYPTION
kmsKeyVersion: projects/my-kms-project/locations/my-kms-key1-location/keyRings/my-kms-key-ring1/cryptoKeys/my-kms-key1/cryptoKeyVersions/1
- encryptionType: CUSTOMER_MANAGED_ENCRYPTION
kmsKeyVersion: projects/my-kms-project/locations/my-kms-key2-location/keyRings/my-kms-key-ring2/cryptoKeys/my-kms-key2/cryptoKeyVersions/1
Disattivare la chiave
Disattiva le versioni della chiave in uso seguendo queste istruzioni per ogni versione della chiave.
Attendi che la modifica diventi effettiva. La disattivazione di una chiave può richiedere fino a tre ore per la propagazione.
Per verificare che il database non sia più accessibile, esegui una query nel database con CMEK disabilitata:
gcloud spanner databases execute-sql DATABASE \ --project=SPANNER_PROJECT_ID \ --instance=INSTANCE_ID \ --sql='SELECT * FROM Users'Viene visualizzato il seguente messaggio di errore:
KMS key required by the Spanner resource is not accessible.
Attivare la chiave
Attiva le versioni delle chiavi in uso nel database seguendo queste istruzioni per ogni versione della chiave.
Attendi che la modifica diventi effettiva. L'attivazione di una chiave può richiedere fino a tre ore per la propagazione.
Per verificare che il database non sia più accessibile, esegui una query nel database abilitato per CMEK:
gcloud spanner databases execute-sql DATABASE \ --project=SPANNER_PROJECT_ID \ --instance=INSTANCE_ID \ --sql='SELECT * FROM Users'Se la modifica è stata applicata, il comando viene eseguito correttamente.
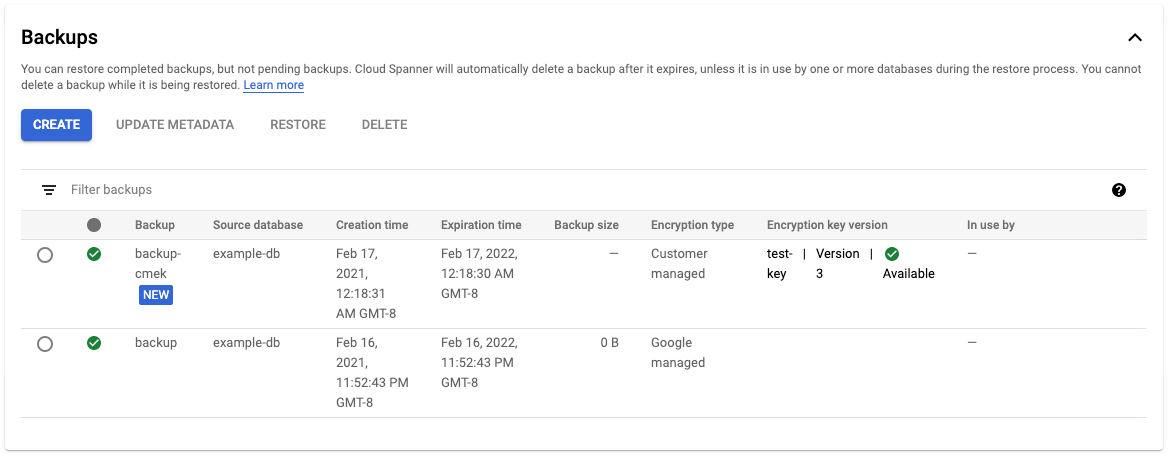
Eseguire il backup di un database
Puoi utilizzare i backup di Spanner per creare backup dei tuoi database. Per impostazione predefinita, i backup Spanner creati da un database utilizzano la stessa configurazione di crittografia del database stesso. Se preferisci, puoi specificare una configurazione di crittografia diversa per un backup.
Console
Utilizza la console per creare backup nelle configurazioni delle istanze regionali.
Nella console Google Cloud , vai alla pagina Istanze.
Fai clic sul nome dell'istanza che contiene il database di cui vuoi eseguire il backup.
Fai clic sul database.
Nel riquadro di navigazione, fai clic su Backup/Restore.
Nella scheda Backup, fai clic su Crea backup.
Inserisci un nome per il backup e seleziona una data di scadenza.
(Facoltativo) Fai clic su Mostra opzioni di crittografia.
a. Se vuoi utilizzare una configurazione di crittografia diversa per il backup, fai clic sul cursore accanto a Usa crittografia esistente.
a. Seleziona Chiave Cloud KMS.
a. Seleziona una chiave dall'elenco a discesa.
L'elenco delle chiavi è limitato al progetto Google Cloud corrente. Per utilizzare una chiave di un progetto Google Cloud diverso, crea il database utilizzando gcloud CLI anziché la console Google Cloud .
Fai clic su Crea.
La tabella Backup mostra le informazioni sulla crittografia per ogni backup.
gcloud
Per creare un backup abilitato per CMEK in una configurazione di istanza regionale, personalizzata o multiregionale,
esegui il comando gcloud spanner backups create:
gcloud spanner backups create BACKUP \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_ID \
--database=DATABASE \
--retention-period=RETENTION_PERIOD \
--encryption-type=customer_managed_encryption \
--kms-project=KMS_PROJECT_ID \
--kms-location=KMS_KEY_LOCATION \
--kms-keyring=KMS_KEY_RING \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]
--asyncPer verificare che il backup creato sia criptato con CMEK:
gcloud spanner backups describe BACKUP \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDLibrerie client
C#
Per creare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
C++
Per creare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
Vai
Per creare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
Java
Per creare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
Node.js
Per creare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
PHP
Per creare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
Python
Per creare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
Ruby
Per creare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per creare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
Copiare un backup
Puoi copiare un backup del tuo database Spanner da un'istanza a un'altra istanza in un progetto o una regione diversa. Per impostazione predefinita, un backup copiato utilizza la stessa configurazione di crittografia, gestita da Google o dal cliente, del backup di origine. Puoi ignorare questo comportamento specificando una configurazione di crittografia diversa durante la copia del backup. Se vuoi che il backup copiato venga criptato con CMEK durante la copia tra regioni, specifica le chiavi Cloud KMS corrispondenti alle regioni di destinazione.
Console
Utilizza la console per copiare un backup in una configurazione dell'istanza regionale.
Nella console Google Cloud , vai alla pagina Istanze.
Fai clic sul nome dell'istanza che contiene il database di cui vuoi eseguire il backup.
Fai clic sul database.
Nel riquadro di navigazione, fai clic su Backup/Restore.
Nella tabella Backup, seleziona Azioni per il backup e fai clic su Copia.
Compila il modulo scegliendo un'istanza di destinazione, fornendo un nome e selezionando una data di scadenza per la copia di backup.
(Facoltativo) Se vuoi utilizzare una configurazione di crittografia diversa per il backup, fai clic su Mostra opzioni di crittografia.
a. Seleziona Chiave Cloud KMS.
a. Seleziona una chiave dall'elenco a discesa.
L'elenco delle chiavi è limitato al progetto Google Cloud corrente. Per utilizzare una chiave di un progetto Google Cloud diverso, crea il database utilizzando gcloud CLI anziché la console Google Cloud .
Fai clic su Copia.
gcloud
Per copiare un backup, con una nuova configurazione di crittografia, in un'altra istanza
nello stesso progetto, esegui il seguente comando gcloud spanner backups copy:
gcloud spanner backups copy --async \
--source-instance=INSTANCE_ID \
--source-backup=SOURCE_BACKUP_NAME \
--destination-instance=DESTINATION_INSTANCE_ID \
--destination-backup=DESTINATION_BACKUP_NAME \
--expiration-date=EXPIRATION_DATE \
--encryption-type=CUSTOMER_MANAGED_ENCRYPTION \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]Per copiare un backup, con una nuova configurazione di crittografia, in un'istanza diversa
in un progetto diverso, esegui il seguente comando gcloud spanner backups copy:
gcloud spanner backups copy --async \
--source-backup=SOURCE_BACKUP_NAME \
--destination-backup=DESTINATION_BACKUP_NAME \
--encryption-type=CUSTOMER_MANAGED_ENCRYPTION \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]Per verificare che il backup copiato sia criptato con CMEK:
gcloud spanner backups describe BACKUP \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDLibrerie client
C#
Per copiare un backup abilitato per CMEK in una configurazione di istanza multiregionale:
C++
Per copiare un backup abilitato per CMEK in una configurazione di istanza multiregionale:
Vai
Per copiare un backup abilitato per CMEK in una configurazione di istanza multiregionale:
Java
Per copiare un backup abilitato per CMEK in una configurazione di istanza multiregionale:
Node.js
Per copiare un backup abilitato per CMEK in una configurazione di istanza multiregionale:
PHP
Per copiare un backup abilitato per CMEK in una configurazione di istanza multiregionale:
Python
Per copiare un backup abilitato per CMEK in una configurazione di istanza multiregionale:
Ruby
Per copiare un backup abilitato per CMEK in una configurazione di istanza multiregionale:
Ripristina da un backup
Puoi ripristinare un backup di un database Spanner in un nuovo database. Per impostazione predefinita, i database ripristinati da un backup utilizzano la stessa configurazione di crittografia del backup stesso, ma puoi sostituire questo comportamento specificando una configurazione di crittografia diversa per il database ripristinato. Se il backup è protetto da CMEK, la versione della chiave utilizzata per creare il backup deve essere disponibile per poter essere decriptata.
Console
Utilizza la console per ripristinare un backup in una configurazione dell'istanza regionale.
Nella console Google Cloud , vai alla pagina Istanze.
Fai clic sull'istanza contenente il database che vuoi ripristinare.
Fai clic sul database.
Nel riquadro di navigazione, fai clic su Backup/Restore.
Nella tabella Backup, seleziona Azioni per il backup e fai clic su Ripristina.
Seleziona l'istanza da ripristinare e assegna un nome al database ripristinato.
(Facoltativo) Se vuoi utilizzare una configurazione di crittografia diversa con il database ripristinato, fai clic sul cursore accanto a Utilizza la crittografia esistente.
a. Seleziona Chiave Cloud KMS.
a. Seleziona una chiave dall'elenco a discesa.
L'elenco delle chiavi è limitato al progetto Google Cloud corrente. Per utilizzare una chiave di un progetto Google Cloud diverso, crea il database utilizzando gcloud CLI anziché la console Google Cloud .
Fai clic su Ripristina.
gcloud
Per ripristinare un backup con una nuova configurazione di crittografia, esegui il seguente comando:gcloud spanner databases restore
gcloud spanner databases restore --async \
--project=SPANNER_PROJECT_ID \
--destination-instance=DESTINATION_INSTANCE_ID \
--destination-database=DESTINATION_DATABASE_ID \
--source-instance=SOURCE_INSTANCE_ID \
--source-backup=SOURCE_BACKUP_NAMEPer verificare che il database ripristinato sia criptato con CMEK:
gcloud spanner databases describe DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDPer ulteriori informazioni, vedi Ripristinare da un backup.
Librerie client
C#
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
C++
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
Vai
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
Java
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
Node.js
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
PHP
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
Python
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
Ruby
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza regionale:
Per ripristinare un backup abilitato per CMEK in una configurazione dell'istanza multiregionale:
Visualizza gli audit log per la chiave Cloud KMS
Assicurati che la registrazione sia abilitata per l'API Cloud KMS nel tuo progetto.
Nella console Google Cloud , vai a Esplora log.
Limita le voci di log alla tua chiave Cloud KMS aggiungendo le seguenti righe al generatore di query:
resource.type="cloudkms_cryptokey" resource.labels.location="KMS_KEY_LOCATION" resource.labels.key_ring_id="KMS_KEY_RING_ID" resource.labels.crypto_key_id="KMS_KEY_ID"Durante il normale funzionamento, le azioni di crittografia e decrittografia vengono registrate con gravità
INFO. Queste voci vengono registrate quando le zone nella tua istanza Spanner eseguono il polling della chiave Cloud KMS circa ogni cinque minuti.Se Spanner non riesce ad accedere alla chiave, le operazioni vengono registrate come
ERROR.

