Esta página descreve como usar chaves de encriptação geridas pelo cliente (CMEK) criadas manualmente para o Spanner.
Para saber mais sobre a CMEK, consulte a vista geral das chaves de encriptação geridas pelo cliente (CMEK).
Crie uma base de dados com CMEK ativada
Crie uma chave no Cloud Key Management Service (Cloud KMS). Pode usar os seguintes tipos de chaves que têm diferentes níveis de proteção no Spanner:
A chave tem de estar na mesma localização que a instância do Spanner. Por exemplo, se a configuração da instância do Spanner estiver em
us-west1, a localização do conjunto de chaves do Cloud KMS também tem de serus-west1.Nem todas as configurações de instâncias multirregionais do Spanner têm uma localização do conjunto de chaves do Cloud KMS correspondente. Para as bases de dados do Spanner em configurações de instâncias personalizadas, de dupla região ou multirregião, pode usar várias chaves do Cloud KMS regionais (de região única) para proteger a sua base de dados. Por exemplo:
- Se a sua base de dados do Spanner estiver na configuração de instância multirregião
nam14, pode criar chaves do Cloud KMS emus-east4,northamerica-northeast1eus-east1. - Se a sua base de dados estiver numa configuração de instância personalizada que use
nam3como configuração de instância base com uma réplica só de leitura adicional emus-central2, pode criar chaves do Cloud KMS emus-east4,us-east1,us-central1eus-central2.
Opcional: para ver uma lista das localizações das réplicas na configuração da instância do Spanner, use o comando
gcloud spanner instances get-locations:gcloud spanner instances get-locations <var>INSTANCE_ID</var>Para obter mais informações, consulte os seguintes recursos:
- Se a sua base de dados do Spanner estiver na configuração de instância multirregião
Conceda acesso do Spanner à chave.
No Cloud Shell, crie e apresente o agente de serviço ou apresente-o se a conta já existir:
gcloud beta services identity create --service=spanner.googleapis.com \ --project=PROJECT_IDSe lhe for pedido que instale o componente gcloud Beta Commands, escreva
Y. Após a instalação, o comando é reiniciado automaticamente.O comando
gcloud services identitycria ou obtém o agente de serviço que o Spanner pode usar para aceder à chave do Cloud KMS em seu nome.O ID da conta de serviço está formatado como um endereço de email:
Service identity created: service-xxx@gcp-sa-spanner.iam.gserviceaccount.comConceda a função encriptar/desencriptar do CryptoKey do Cloud KMS(
cloudkms.cryptoKeyEncrypterDecrypter) à conta de serviço para cada região (--location) na configuração da instância do Spanner. Para o fazer, execute o comandogcloud kms keys add-iam-policybinding:gcloud kms keys add-iam-policy-binding KMS_KEY \ --location KMS_KEY_LOCATION \ --keyring KMS_KEY_RING \ --project=PROJECT_ID \ --member serviceAccount:service-xxx@gcp-sa-spanner.iam.gserviceaccount.com \ --role roles/cloudkms.cryptoKeyEncrypterDecrypterSegue-se um exemplo de saída:
Updated IAM policy for key [KMS_KEY]Se estiver a usar várias chaves do Cloud KMS para proteger a sua base de dados, execute o comando
gcloud kms keys add-iam-policybindingpara todas as chaves.Esta função garante que a conta de serviço tem autorização para encriptar e desencriptar com a chave do Cloud KMS. Para mais informações, consulte o artigo Autorizações e funções do Cloud KMS.
Crie a base de dados e especifique a sua chave do Cloud KMS.
Consola
Use a consola para criar bases de dados em configurações de instâncias regionais.
Na Google Cloud consola, aceda à página Instâncias.
Clique na instância onde quer criar uma base de dados.
Clique em Criar base de dados e preencha os campos obrigatórios.
Clique em Mostrar opções de encriptação.
Selecione Chave do Cloud KMS.
Selecione uma chave na lista pendente.
A lista de chaves está limitada ao Google Cloud projeto atual. Para usar uma chave de um Google Cloud projeto diferente, crie a base de dados com a CLI gcloud em vez daGoogle Cloud consola.
Depois de criar a base de dados, pode verificar se a mesma tem a CMEK ativada na página Vista geral da base de dados.
gcloud
Para criar uma base de dados com CMEK numa configuração de instância regional, personalizada ou multirregional, execute o comando gcloud spanner databases create:
gcloud spanner databases create DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_ID \
--ddl="CREATE TABLE Users (Id INT64 NOT NULL, FirstName STRING(100) NOT NULL, LastName STRING(100) NOT NULL,) PRIMARY KEY (Id)" \
--kms-project=KMS_PROJECT_ID \
--kms-location=KMS_KEY_LOCATION \
--kms-keyring=KMS_KEYRING \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]Para verificar se uma base de dados tem a CMEK ativada, execute o comando
gcloud spanner databases describe:
gcloud spanner databases describe DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDAs bases de dados ativadas com a CMEK incluem um campo para encryptionConfig, conforme mostrado no exemplo de saída seguinte:
encryptionConfig:
kmsKeyNames:projects/my-kms-project/locations/eur5/keyRings/my-kms-key-ring/cryptoKeys/my-kms-key
name: projects/my-spanner-project/instances/my-instance/databases/my-db
state: READY
Bibliotecas cliente
C#
Para criar uma base de dados com CMEK numa configuração de instância regional:
Para criar uma base de dados com a CMEK ativada numa configuração de instância de várias regiões:
C++
Para criar uma base de dados com CMEK numa configuração de instância regional:
Para criar uma base de dados com a CMEK ativada numa configuração de instância de várias regiões:
Ir
Para criar uma base de dados com CMEK numa configuração de instância regional:
Para criar uma base de dados com a CMEK ativada numa configuração de instância de várias regiões:
Java
Para criar uma base de dados com CMEK numa configuração de instância regional:
Para criar uma base de dados com a CMEK ativada numa configuração de instância de várias regiões:
Node.js
Para criar uma base de dados com CMEK numa configuração de instância regional:
Para criar uma base de dados com a CMEK ativada numa configuração de instância de várias regiões:
PHP
Para criar uma base de dados com CMEK numa configuração de instância regional:
Para criar uma base de dados com a CMEK ativada numa configuração de instância de várias regiões:
Python
Para criar uma base de dados com CMEK numa configuração de instância regional:
Para criar uma base de dados com a CMEK ativada numa configuração de instância de várias regiões:
Ruby
Para criar uma base de dados com CMEK numa configuração de instância regional:
Para criar uma base de dados com a CMEK ativada numa configuração de instância de várias regiões:
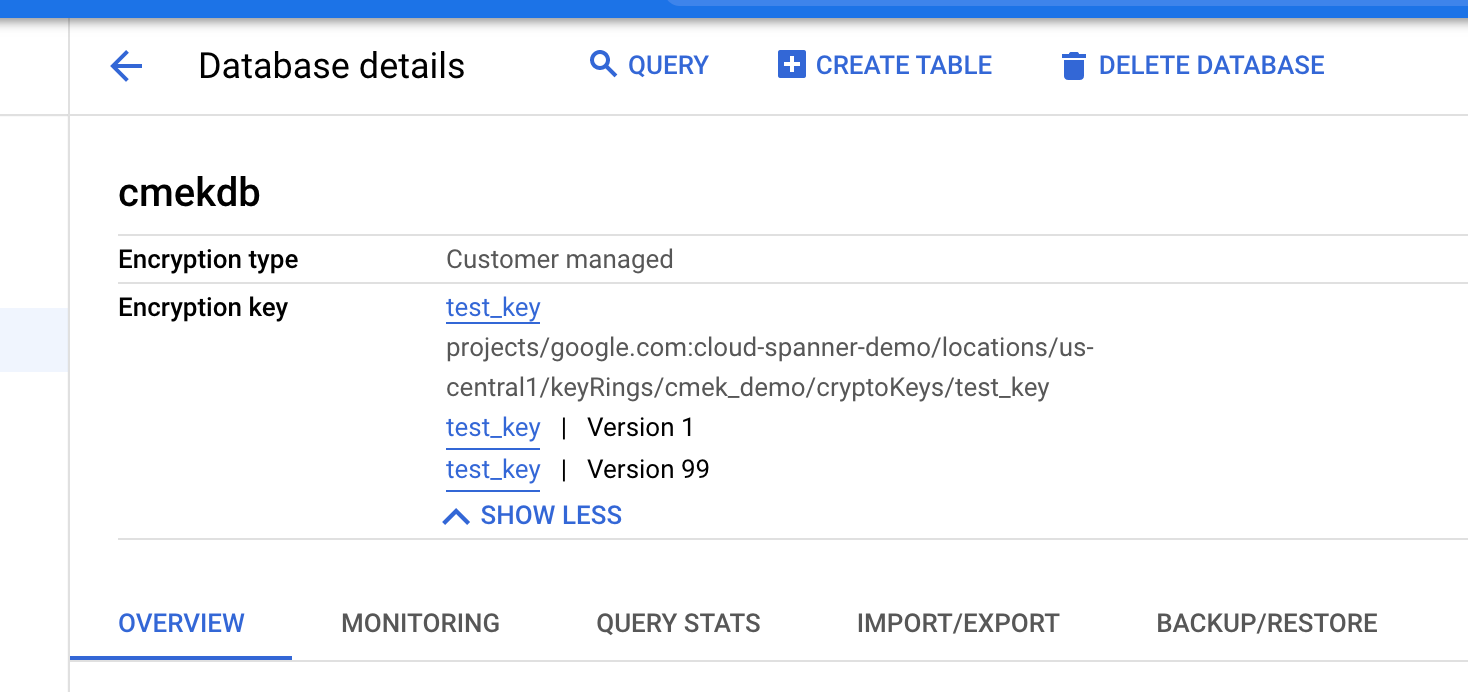
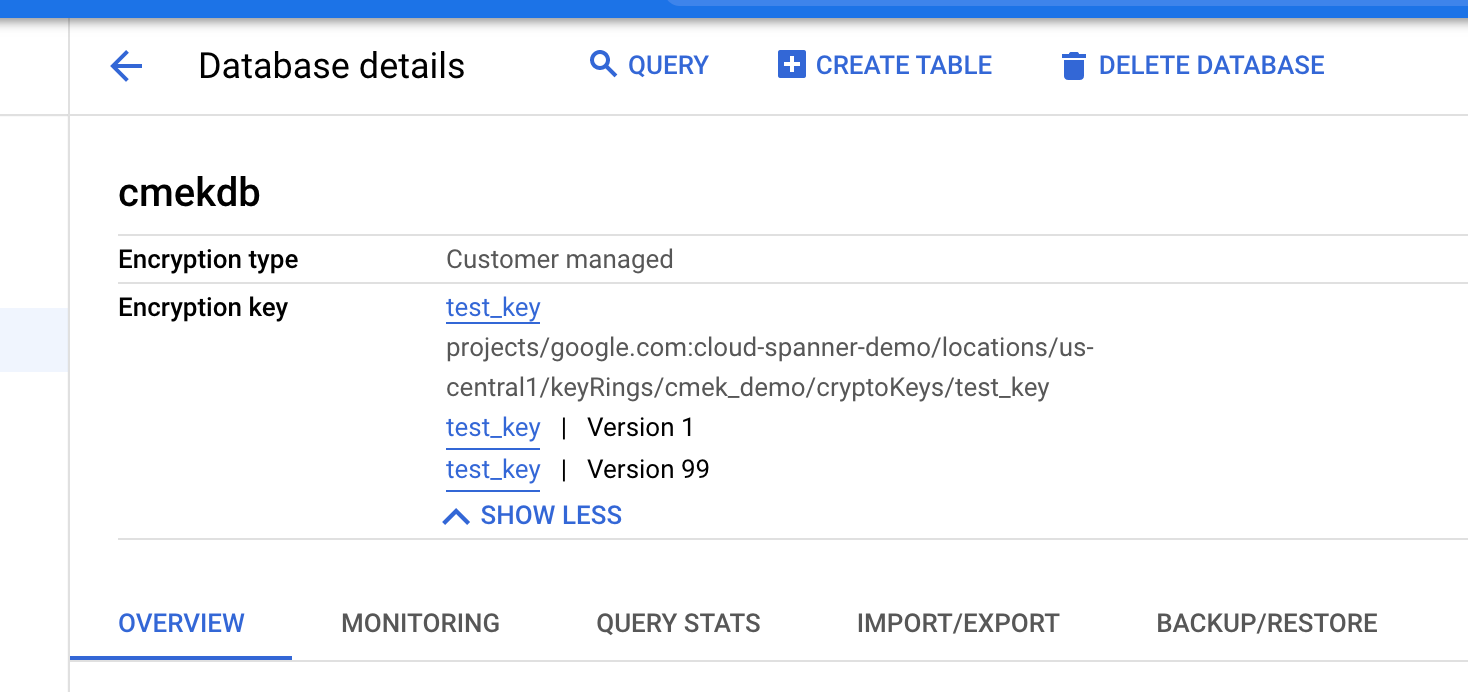
Veja as versões das chaves em utilização
O campo encryption_info
da base de dados mostra informações sobre as versões principais.
Quando a versão da chave de uma base de dados é alterada, a alteração não é propagada imediatamente
para encryption_info. Pode haver um atraso antes de a alteração ser refletida neste campo.
Consola
Na Google Cloud consola, aceda à página Instâncias.
Clique na instância que contém a base de dados que quer ver.
Clique na base de dados.
As informações de encriptação são apresentadas na página Detalhes da base de dados.
gcloud
Pode obter o encryption_info de uma base de dados executando o comando
gcloud spanner databases describe
ou gcloud spanner databases list. Por exemplo:
gcloud spanner databases describe DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDSegue-se um exemplo de saída:
name: projects/my-project/instances/test-instance/databases/example-db
encryptionInfo:
- encryptionType: CUSTOMER_MANAGED_ENCRYPTION
kmsKeyVersion: projects/my-kms-project/locations/my-kms-key1-location/keyRings/my-kms-key-ring1/cryptoKeys/my-kms-key1/cryptoKeyVersions/1
- encryptionType: CUSTOMER_MANAGED_ENCRYPTION
kmsKeyVersion: projects/my-kms-project/locations/my-kms-key2-location/keyRings/my-kms-key-ring2/cryptoKeys/my-kms-key2/cryptoKeyVersions/1
Desative a chave
Desative as versões das chaves que estão a ser usadas seguindo estas instruções para cada versão da chave.
Aguarde que a alteração entre em vigor. A desativação de uma chave pode demorar até três horas a propagar-se.
Para confirmar que a base de dados já não está acessível, execute uma consulta na base de dados com as CMEK desativadas:
gcloud spanner databases execute-sql DATABASE \ --project=SPANNER_PROJECT_ID \ --instance=INSTANCE_ID \ --sql='SELECT * FROM Users'É apresentada a seguinte mensagem de erro:
KMS key required by the Spanner resource is not accessible.
Ative a chave
Ative as versões das chaves que estão a ser usadas pela base de dados seguindo estas instruções para cada versão da chave.
Aguarde que a alteração entre em vigor. A propagação da ativação de uma chave pode demorar até três horas.
Para confirmar que a base de dados já não está acessível, execute uma consulta na base de dados com CMEK:
gcloud spanner databases execute-sql DATABASE \ --project=SPANNER_PROJECT_ID \ --instance=INSTANCE_ID \ --sql='SELECT * FROM Users'Se a alteração tiver sido aplicada, o comando é executado com êxito.
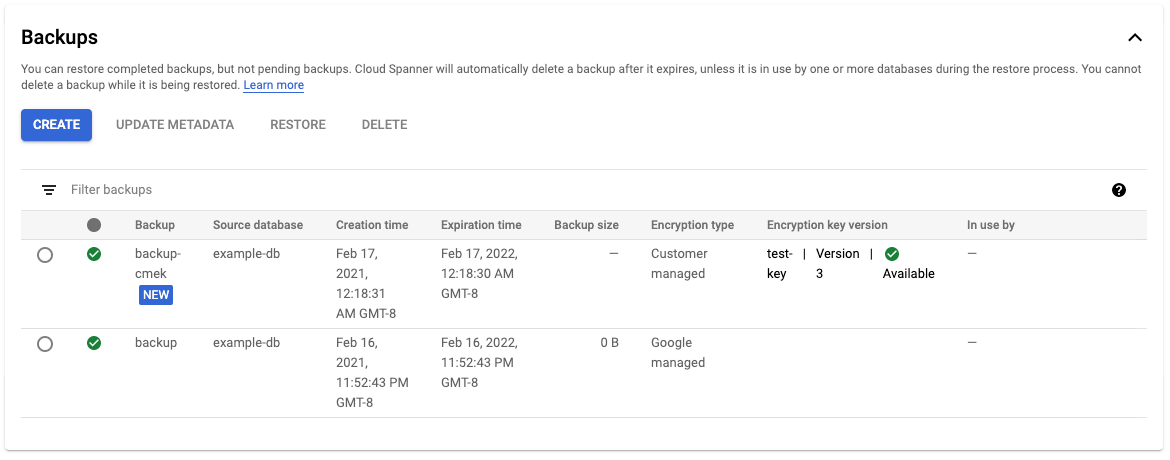
Faça uma cópia de segurança de uma base de dados
Pode usar as cópias de segurança do Spanner para criar cópias de segurança das suas bases de dados. Por predefinição, as cópias de segurança do Spanner criadas a partir de uma base de dados usam a mesma configuração de encriptação que a própria base de dados. Opcionalmente, pode especificar uma configuração de encriptação diferente para uma cópia de segurança.
Consola
Use a consola para criar cópias de segurança em configurações de instâncias regionais.
Na Google Cloud consola, aceda à página Instâncias.
Clique no nome da instância que contém a base de dados da qual quer fazer uma cópia de segurança.
Clique na base de dados.
No painel de navegação, clique em Cópia de segurança/restauro.
No separador Cópias de segurança, clique em Criar cópia de segurança.
Introduza um nome de cópia de segurança e selecione uma data de validade.
Opcional: clique em Mostrar opções de encriptação.
a. Se quiser usar uma configuração de encriptação diferente para a sua cópia de segurança, clique no controlo de deslize junto a Usar encriptação existente.
a. Selecione Chave do Cloud KMS.
a. Selecione uma chave na lista pendente.
A lista de chaves está limitada ao Google Cloud projeto atual. Para usar uma chave de um Google Cloud projeto diferente, crie a base de dados usando a CLI gcloud em vez da Google Cloud consola.
Clique em Criar.
A tabela Cópias de segurança apresenta informações de encriptação para cada cópia de segurança.
gcloud
Para criar uma cópia de segurança com CMEK numa configuração de instância regional, personalizada ou multirregional, execute o comando gcloud spanner backups create:
gcloud spanner backups create BACKUP \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_ID \
--database=DATABASE \
--retention-period=RETENTION_PERIOD \
--encryption-type=customer_managed_encryption \
--kms-project=KMS_PROJECT_ID \
--kms-location=KMS_KEY_LOCATION \
--kms-keyring=KMS_KEY_RING \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]
--asyncPara verificar se a cópia de segurança criada está encriptada com CMEK:
gcloud spanner backups describe BACKUP \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDBibliotecas cliente
C#
Para criar uma cópia de segurança com CMEK numa configuração de instância regional:
Para criar uma cópia de segurança com a CMEK numa configuração de instância de várias regiões:
C++
Para criar uma cópia de segurança com CMEK numa configuração de instância regional:
Para criar uma cópia de segurança com a CMEK numa configuração de instância de várias regiões:
Ir
Para criar uma cópia de segurança com CMEK numa configuração de instância regional:
Para criar uma cópia de segurança com a CMEK numa configuração de instância de várias regiões:
Java
Para criar uma cópia de segurança com CMEK numa configuração de instância regional:
Para criar uma cópia de segurança com a CMEK numa configuração de instância de várias regiões:
Node.js
Para criar uma cópia de segurança com CMEK numa configuração de instância regional:
Para criar uma cópia de segurança com a CMEK numa configuração de instância de várias regiões:
PHP
Para criar uma cópia de segurança com CMEK numa configuração de instância regional:
Para criar uma cópia de segurança com a CMEK numa configuração de instância de várias regiões:
Python
Para criar uma cópia de segurança com CMEK numa configuração de instância regional:
Para criar uma cópia de segurança com a CMEK numa configuração de instância de várias regiões:
Ruby
Para criar uma cópia de segurança com CMEK numa configuração de instância regional:
Para criar uma cópia de segurança com a CMEK numa configuração de instância de várias regiões:
Copie uma cópia de segurança
Pode copiar uma cópia de segurança da sua base de dados do Spanner de uma instância para outra instância num projeto ou numa região diferente. Por predefinição, uma cópia de segurança copiada usa a mesma configuração de encriptação, gerida pela Google ou pelo cliente, que a encriptação da cópia de segurança de origem. Pode substituir este comportamento especificando uma configuração de encriptação diferente quando copiar a cópia de segurança. Se quiser que a cópia de segurança seja encriptada com CMEK quando copiar entre regiões, especifique as chaves do Cloud KMS correspondentes às regiões de destino.
Consola
Use a consola para copiar uma cópia de segurança numa configuração de instância regional.
Na Google Cloud consola, aceda à página Instâncias.
Clique no nome da instância que contém a base de dados da qual quer fazer uma cópia de segurança.
Clique na base de dados.
No painel de navegação, clique em Cópia de segurança/restauro.
Na tabela Cópias de segurança, selecione Ações para a sua cópia de segurança e clique em Copiar.
Preencha o formulário escolhendo uma instância de destino, indicando um nome e selecionando uma data de validade para a cópia de segurança.
Opcional: se quiser usar uma configuração de encriptação diferente para a sua cópia de segurança, clique em Mostrar opções de encriptação.
a. Selecione Chave do Cloud KMS.
a. Selecione uma chave na lista pendente.
A lista de chaves está limitada ao Google Cloud projeto atual. Para usar uma chave de um Google Cloud projeto diferente, crie a base de dados usando a CLI gcloud em vez da Google Cloud consola.
Clique em Copiar.
gcloud
Para copiar uma cópia de segurança, com uma nova configuração de encriptação, para uma instância diferente no mesmo projeto, execute o seguinte comando gcloud spanner backups copy:
gcloud spanner backups copy --async \
--source-instance=INSTANCE_ID \
--source-backup=SOURCE_BACKUP_NAME \
--destination-instance=DESTINATION_INSTANCE_ID \
--destination-backup=DESTINATION_BACKUP_NAME \
--expiration-date=EXPIRATION_DATE \
--encryption-type=CUSTOMER_MANAGED_ENCRYPTION \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]Para copiar uma cópia de segurança, com uma nova configuração de encriptação, para uma instância diferente
num projeto diferente, execute o seguinte comando gcloud spanner backups copy:
gcloud spanner backups copy --async \
--source-backup=SOURCE_BACKUP_NAME \
--destination-backup=DESTINATION_BACKUP_NAME \
--encryption-type=CUSTOMER_MANAGED_ENCRYPTION \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]Para verificar se a cópia de segurança copiada está encriptada com CMEK:
gcloud spanner backups describe BACKUP \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDBibliotecas cliente
C#
Para copiar uma cópia de segurança com CMEK numa configuração de instância de várias regiões:
C++
Para copiar uma cópia de segurança com CMEK numa configuração de instância de várias regiões:
Ir
Para copiar uma cópia de segurança com CMEK numa configuração de instância de várias regiões:
Java
Para copiar uma cópia de segurança com CMEK numa configuração de instância de várias regiões:
Node.js
Para copiar uma cópia de segurança com CMEK numa configuração de instância de várias regiões:
PHP
Para copiar uma cópia de segurança com CMEK numa configuração de instância de várias regiões:
Python
Para copiar uma cópia de segurança com CMEK numa configuração de instância de várias regiões:
Ruby
Para copiar uma cópia de segurança com CMEK numa configuração de instância de várias regiões:
Restauro a partir de cópia de segurança
Pode restaurar uma cópia de segurança de uma base de dados do Spanner numa nova base de dados. Por predefinição, as bases de dados que são restauradas a partir de uma cópia de segurança usam a mesma configuração de encriptação que a própria cópia de segurança, mas pode substituir este comportamento especificando uma configuração de encriptação diferente para a base de dados restaurada. Se a cópia de segurança estiver protegida por CMEK, a versão da chave usada para criar a cópia de segurança tem de estar disponível para que possa ser desencriptada.
Consola
Use a consola para restaurar uma cópia de segurança numa configuração de instância regional.
Na Google Cloud consola, aceda à página Instâncias.
Clique na instância que contém a base de dados que quer restaurar.
Clique na base de dados.
No painel de navegação, clique em Cópia de segurança/restauro.
Na tabela Cópias de segurança, selecione Ações para a sua cópia de segurança e clique em Restaurar.
Selecione a instância a restaurar e atribua um nome à base de dados restaurada.
Opcional: se quiser usar uma configuração de encriptação diferente com a base de dados restaurada, clique no controlo de deslize junto a Usar encriptação existente.
a. Selecione Chave do Cloud KMS.
a. Selecione uma chave na lista pendente.
A lista de chaves está limitada ao Google Cloud projeto atual. Para usar uma chave de um Google Cloud projeto diferente, crie a base de dados usando a CLI gcloud em vez da Google Cloud consola.
Clique em Restaurar.
gcloud
Para restaurar uma cópia de segurança com uma nova configuração de encriptação, execute o seguinte comando:
gcloud spanner databases restore
gcloud spanner databases restore --async \
--project=SPANNER_PROJECT_ID \
--destination-instance=DESTINATION_INSTANCE_ID \
--destination-database=DESTINATION_DATABASE_ID \
--source-instance=SOURCE_INSTANCE_ID \
--source-backup=SOURCE_BACKUP_NAMEPara verificar se a base de dados restaurada está encriptada com CMEK:
gcloud spanner databases describe DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDPara mais informações, consulte o artigo Restaurar a partir de uma cópia de segurança.
Bibliotecas cliente
C#
Para restaurar uma cópia de segurança com CMEK numa configuração de instância regional:
Para restaurar uma cópia de segurança com a CMEK ativada numa configuração de instância de várias regiões:
C++
Para restaurar uma cópia de segurança com CMEK numa configuração de instância regional:
Para restaurar uma cópia de segurança com a CMEK ativada numa configuração de instância de várias regiões:
Ir
Para restaurar uma cópia de segurança com CMEK numa configuração de instância regional:
Para restaurar uma cópia de segurança com a CMEK ativada numa configuração de instância de várias regiões:
Java
Para restaurar uma cópia de segurança com CMEK numa configuração de instância regional:
Para restaurar uma cópia de segurança com a CMEK ativada numa configuração de instância de várias regiões:
Node.js
Para restaurar uma cópia de segurança com CMEK numa configuração de instância regional:
Para restaurar uma cópia de segurança com a CMEK ativada numa configuração de instância de várias regiões:
PHP
Para restaurar uma cópia de segurança com CMEK numa configuração de instância regional:
Para restaurar uma cópia de segurança com a CMEK ativada numa configuração de instância de várias regiões:
Python
Para restaurar uma cópia de segurança com CMEK numa configuração de instância regional:
Para restaurar uma cópia de segurança com a CMEK ativada numa configuração de instância de várias regiões:
Ruby
Para restaurar uma cópia de segurança com CMEK numa configuração de instância regional:
Para restaurar uma cópia de segurança com a CMEK ativada numa configuração de instância de várias regiões:
Veja os registos de auditoria da chave do Cloud KMS
Certifique-se de que o registo está ativado para a API Cloud KMS no seu projeto.
Na Google Cloud consola, aceda ao Explorador de registos.
Limite as entradas do registo à sua chave do Cloud KMS adicionando as seguintes linhas ao criador de consultas:
resource.type="cloudkms_cryptokey" resource.labels.location="KMS_KEY_LOCATION" resource.labels.key_ring_id="KMS_KEY_RING_ID" resource.labels.crypto_key_id="KMS_KEY_ID"Em operações normais, as ações de encriptação e desencriptação são registadas com a gravidade
INFO. Estas entradas são registadas à medida que as zonas na sua instância do Spanner consultam a chave do Cloud KMS aproximadamente a cada cinco minutos.Se o Spanner não conseguir aceder à chave, as operações são registadas como
ERROR.

