Cette page explique comment utiliser les clés de chiffrement gérées par le client (CMEK, Customer-Managed Encryption Keys) créées manuellement pour Spanner.
Pour en savoir plus sur les CMEK, consultez la présentation des clés de chiffrement gérées par le client (CMEK).
Créer une base de données compatible avec les CMEK
Créez une clé dans Cloud Key Management Service (Cloud KMS). Vous pouvez utiliser les types de clés suivants, qui présentent différents niveaux de protection dans Spanner :
La clé doit se trouver au même emplacement que votre instance Spanner. Par exemple, si la configuration de votre instance Spanner se trouve dans
us-west1, l'emplacement de votre trousseau de clés Cloud KMS doit également êtreus-west1.Toutes les configurations d'instances multirégionales Spanner ne disposent pas d'un emplacement de trousseau de clés Cloud KMS correspondant. Pour les bases de données Spanner dans des configurations d'instance personnalisées, birégionales ou multirégionales, vous pouvez utiliser plusieurs clés Cloud KMS régionales (monorégionales) pour protéger votre base de données. Exemple :
- Si votre base de données Spanner se trouve dans la configuration d'instance multirégionale
nam14, vous pouvez créer des clés Cloud KMS dansus-east4,northamerica-northeast1etus-east1. - Si votre base de données se trouve dans une configuration d'instance personnalisée qui utilise
nam3comme configuration d'instance de base avec un réplica en lecture seule supplémentaire dansus-central2, vous pouvez créer des clés Cloud KMS dansus-east4,us-east1,us-central1etus-central2.
Facultatif : Pour afficher la liste des emplacements des répliques dans la configuration de votre instance Spanner, utilisez la commande
gcloud spanner instances get-locations:gcloud spanner instances get-locations <var>INSTANCE_ID</var>Pour en savoir plus, consultez les ressources suivantes :
- Si votre base de données Spanner se trouve dans la configuration d'instance multirégionale
Accordez à Spanner l'accès à la clé.
Dans Cloud Shell, créez et affichez l'agent de service, ou affichez-le si le compte existe déjà :
gcloud beta services identity create --service=spanner.googleapis.com \ --project=PROJECT_IDSi vous êtes invité à installer le composant Commandes bêta de gcloud, saisissez
Y. Une fois l'installation terminée, la commande est automatiquement redémarrée.La commande
gcloud services identitycrée ou obtient l'agent de service que Spanner peut utiliser pour accéder à la clé Cloud KMS en votre nom.L'ID de compte de service se présente sous la forme d'une adresse e-mail :
Service identity created: service-xxx@gcp-sa-spanner.iam.gserviceaccount.comAccordez le rôle Chiffreur/Déchiffreur de CryptoKey Cloud KMS(
cloudkms.cryptoKeyEncrypterDecrypter) au compte de service pour chaque région (--location) dans la configuration de votre instance Spanner. Pour ce faire, exécutez la commandegcloud kms keys add-iam-policybinding:gcloud kms keys add-iam-policy-binding KMS_KEY \ --location KMS_KEY_LOCATION \ --keyring KMS_KEY_RING \ --project=PROJECT_ID \ --member serviceAccount:service-xxx@gcp-sa-spanner.iam.gserviceaccount.com \ --role roles/cloudkms.cryptoKeyEncrypterDecrypterVoici un exemple de résultat :
Updated IAM policy for key [KMS_KEY]Si vous utilisez plusieurs clés Cloud KMS pour protéger votre base de données, exécutez la commande
gcloud kms keys add-iam-policybindingpour toutes vos clés.Ce rôle garantit que le compte de service est autorisé à chiffrer et à déchiffrer les données avec la clé Cloud KMS. Pour en savoir plus, consultez Autorisations et rôles Cloud KMS.
Créez la base de données et spécifiez votre clé Cloud KMS.
Console
Utilisez la console pour créer des bases de données dans des configurations d'instances régionales.
Dans la console Google Cloud , accédez à la page Instances.
Cliquez sur l'instance dans laquelle vous souhaitez créer une base de données.
Cliquez sur Créer une base de données et remplissez les champs obligatoires.
Cliquez sur Afficher les options de chiffrement.
Sélectionnez Clé Cloud KMS.
Sélectionnez une clé dans la liste déroulante.
La liste des clés est limitée au projet Google Cloud actuel. Pour utiliser une clé provenant d'un autre projet Google Cloud , créez la base de données à l'aide de gcloud CLI au lieu de la consoleGoogle Cloud .
Une fois la base de données créée, vous pouvez vérifier qu'elle est compatible avec CMEK en consultant la page Vue d'ensemble de la base de données.
gcloud
Pour créer une base de données compatible CMEK dans une configuration d'instance régionale, personnalisée ou multirégionale, exécutez la commande gcloud spanner databases create :
gcloud spanner databases create DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_ID \
--ddl="CREATE TABLE Users (Id INT64 NOT NULL, FirstName STRING(100) NOT NULL, LastName STRING(100) NOT NULL,) PRIMARY KEY (Id)" \
--kms-project=KMS_PROJECT_ID \
--kms-location=KMS_KEY_LOCATION \
--kms-keyring=KMS_KEYRING \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]Pour vérifier qu'une base de données est compatible avec CMEK, exécutez la commande gcloud spanner databases describe :
gcloud spanner databases describe DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDLes bases de données compatibles avec les CMEK incluent un champ encryptionConfig, comme illustré dans l'exemple de résultat suivant :
encryptionConfig:
kmsKeyNames:projects/my-kms-project/locations/eur5/keyRings/my-kms-key-ring/cryptoKeys/my-kms-key
name: projects/my-spanner-project/instances/my-instance/databases/my-db
state: READY
Bibliothèques clientes
C#
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance régionale :
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance multirégionale :
C++
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance régionale :
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance multirégionale :
Go
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance régionale :
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance multirégionale :
Java
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance régionale :
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance multirégionale :
Node.js
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance régionale :
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance multirégionale :
PHP
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance régionale :
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance multirégionale :
Python
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance régionale :
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance multirégionale :
Ruby
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance régionale :
Pour créer une base de données compatible avec les CMEK dans une configuration d'instance multirégionale :
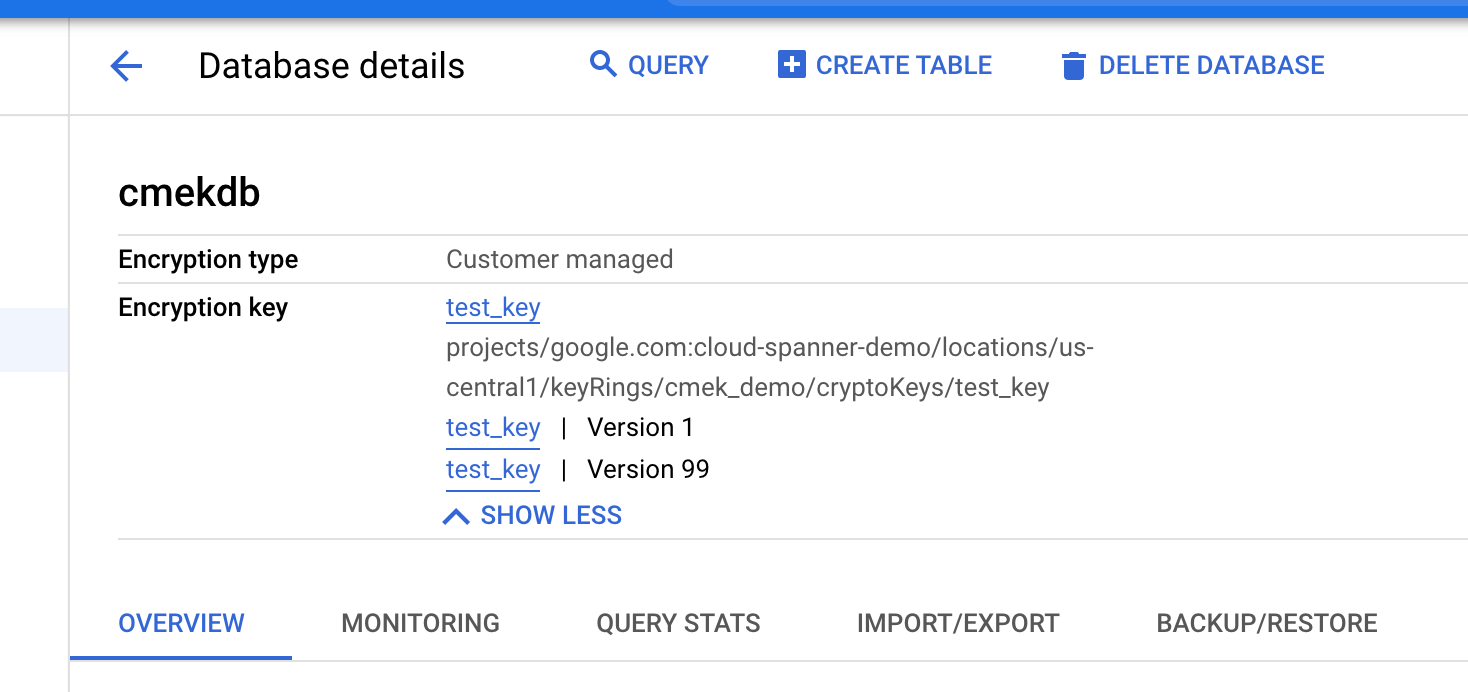
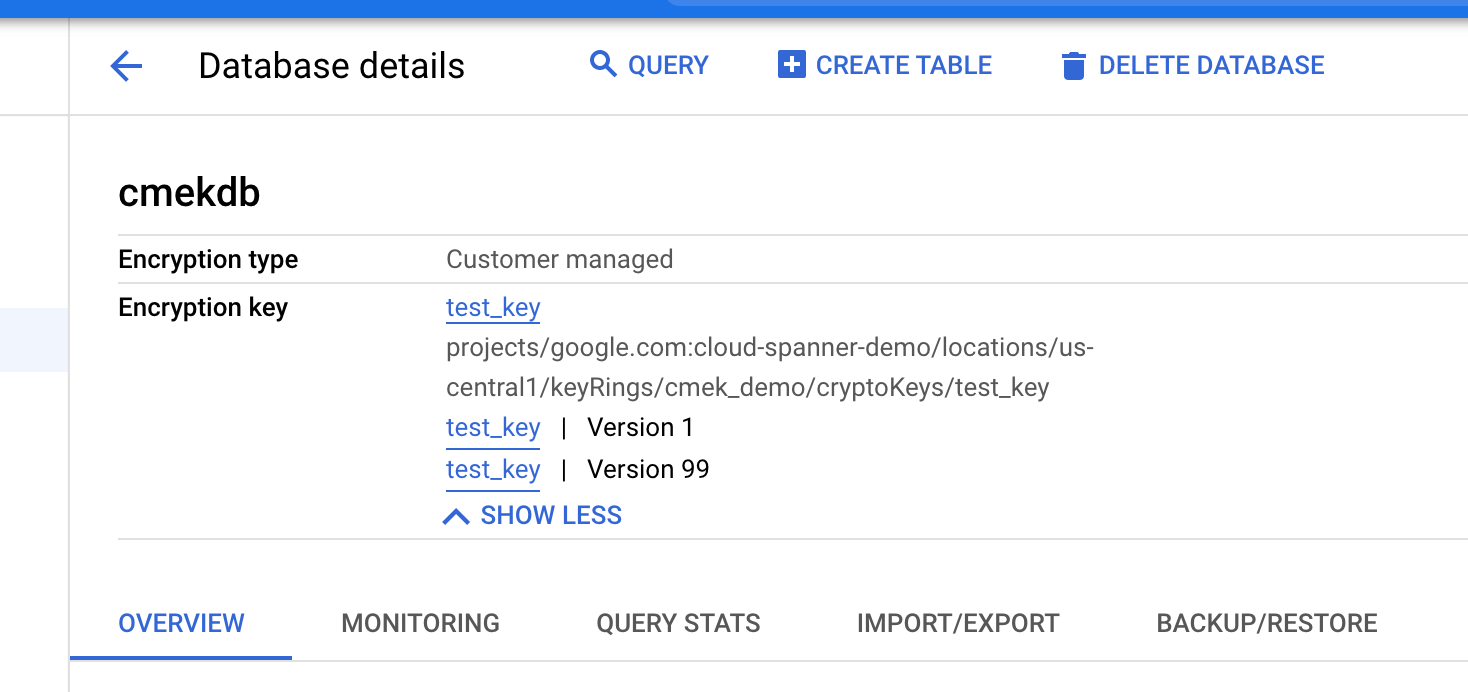
Afficher les versions de clé utilisées
Le champ encryption_info de la base de données affiche des informations sur les versions de clé.
Lorsque la version de clé d'une base de données change, la modification n'est pas immédiatement propagée à encryption_info. Il peut s'écouler un certain temps avant que la modification ne soit reflétée dans ce champ.
Console
Dans la console Google Cloud , accédez à la page Instances.
Cliquez sur l'instance contenant la base de données que vous souhaitez afficher.
Cliquez sur la base de données.
Les informations sur le chiffrement s'affichent sur la page Détails de la base de données.
gcloud
Vous pouvez obtenir le encryption_info d'une base de données en exécutant la commande gcloud spanner databases describe ou gcloud spanner databases list. Exemple :
gcloud spanner databases describe DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDVoici un exemple de résultat :
name: projects/my-project/instances/test-instance/databases/example-db
encryptionInfo:
- encryptionType: CUSTOMER_MANAGED_ENCRYPTION
kmsKeyVersion: projects/my-kms-project/locations/my-kms-key1-location/keyRings/my-kms-key-ring1/cryptoKeys/my-kms-key1/cryptoKeyVersions/1
- encryptionType: CUSTOMER_MANAGED_ENCRYPTION
kmsKeyVersion: projects/my-kms-project/locations/my-kms-key2-location/keyRings/my-kms-key-ring2/cryptoKeys/my-kms-key2/cryptoKeyVersions/1
Désactiver la clé
Désactivez les versions de clé en cours d'utilisation en suivant ces instructions pour chaque version de clé.
Attendez que la modification prenne effet. La désactivation d'une clé peut prendre jusqu'à trois heures.
Pour vérifier que la base de données n'est plus accessible, exécutez une requête dans la base de données CMEK désactivée :
gcloud spanner databases execute-sql DATABASE \ --project=SPANNER_PROJECT_ID \ --instance=INSTANCE_ID \ --sql='SELECT * FROM Users'Le message d'erreur suivant s'affiche :
KMS key required by the Spanner resource is not accessible.
Activer la clé
Activez les versions de clé utilisées par la base de données en suivant ces instructions pour chaque version de clé.
Attendez que la modification prenne effet. L'activation d'une clé peut prendre jusqu'à trois heures.
Pour vérifier que la base de données n'est plus accessible, exécutez une requête dans la base de données compatible avec CMEK :
gcloud spanner databases execute-sql DATABASE \ --project=SPANNER_PROJECT_ID \ --instance=INSTANCE_ID \ --sql='SELECT * FROM Users'Si la modification a été appliquée, la commande s'exécute correctement.
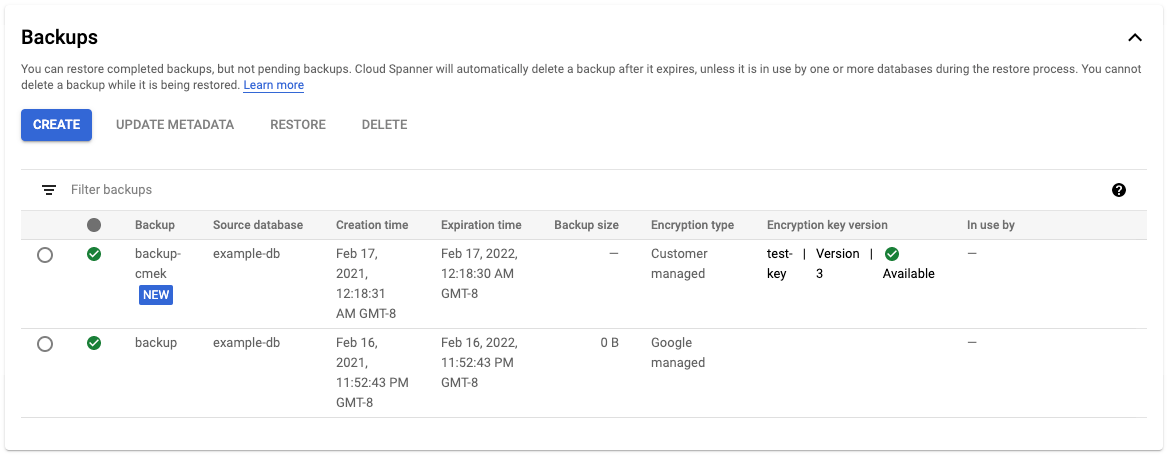
Sauvegarder une base de données
Vous pouvez utiliser les sauvegardes Spanner pour créer des sauvegardes de vos bases de données. Par défaut, les sauvegardes Spanner créées à partir d'une base de données utilisent la même configuration de chiffrement que la base de données elle-même. Vous pouvez éventuellement spécifier une autre configuration de chiffrement pour une sauvegarde.
Console
Utilisez la console pour créer des sauvegardes dans les configurations d'instances régionales.
Dans la console Google Cloud , accédez à la page Instances.
Cliquez sur le nom de l'instance contenant la base de données que vous souhaitez sauvegarder.
Cliquez sur la base de données.
Dans le volet de navigation, cliquez sur Sauvegarder/Restaurer.
Dans l'onglet Sauvegardes, cliquez sur Créer une sauvegarde.
Saisissez un nom de sauvegarde et sélectionnez une date d'expiration.
Facultatif : Cliquez sur Afficher les options de chiffrement.
a. Si vous souhaitez utiliser une autre configuration de chiffrement pour votre sauvegarde, cliquez sur le bouton bascule à côté de Utiliser le chiffrement existant.
a. Sélectionnez Clé Cloud KMS.
a. Sélectionnez une clé dans la liste déroulante.
La liste des clés est limitée au projet Google Cloud actuel. Pour utiliser une clé provenant d'un autre projet Google Cloud , créez la base de données à l'aide de gcloud CLI au lieu de la console Google Cloud .
Cliquez sur Créer.
Le tableau Sauvegardes affiche des informations sur le chiffrement pour chaque sauvegarde.
gcloud
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance régionale, personnalisée ou multirégionale, exécutez la commande gcloud spanner backups create :
gcloud spanner backups create BACKUP \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_ID \
--database=DATABASE \
--retention-period=RETENTION_PERIOD \
--encryption-type=customer_managed_encryption \
--kms-project=KMS_PROJECT_ID \
--kms-location=KMS_KEY_LOCATION \
--kms-keyring=KMS_KEY_RING \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]
--asyncPour vérifier que la sauvegarde créée est chiffrée avec CMEK :
gcloud spanner backups describe BACKUP \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDBibliothèques clientes
C#
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance régionale :
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance multirégionale :
C++
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance régionale :
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance multirégionale :
Go
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance régionale :
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance multirégionale :
Java
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance régionale :
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance multirégionale :
Node.js
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance régionale :
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance multirégionale :
PHP
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance régionale :
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance multirégionale :
Python
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance régionale :
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance multirégionale :
Ruby
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance régionale :
Pour créer une sauvegarde compatible avec CMEK dans une configuration d'instance multirégionale :
Copier une sauvegarde
Vous pouvez copier une sauvegarde de votre base de données Spanner d'une instance vers une autre instance dans une autre région ou un autre projet. Par défaut, une sauvegarde copiée utilise la même configuration de chiffrement (gérée par Google ou par le client) que la sauvegarde source. Vous pouvez ignorer ce comportement en spécifiant une autre configuration de chiffrement lors de la copie de la sauvegarde. Si vous souhaitez que la sauvegarde copiée soit chiffrée avec CMEK lors de la copie entre régions, spécifiez les clés Cloud KMS correspondant aux régions de destination.
Console
Utilisez la console pour copier une sauvegarde dans une configuration d'instance régionale.
Dans la console Google Cloud , accédez à la page Instances.
Cliquez sur le nom de l'instance contenant la base de données que vous souhaitez sauvegarder.
Cliquez sur la base de données.
Dans le volet de navigation, cliquez sur Sauvegarder/Restaurer.
Dans le tableau Sauvegardes, sélectionnez Actions pour votre sauvegarde, puis cliquez sur Copier.
Remplissez le formulaire en choisissant une instance de destination, en fournissant un nom et en sélectionnant une date d'expiration pour la copie de sauvegarde.
Facultatif : Si vous souhaitez utiliser une configuration de chiffrement différente pour votre sauvegarde, cliquez sur Afficher les options de chiffrement.
a. Sélectionnez Clé Cloud KMS.
a. Sélectionnez une clé dans la liste déroulante.
La liste des clés est limitée au projet Google Cloud actuel. Pour utiliser une clé provenant d'un autre projet Google Cloud , créez la base de données à l'aide de gcloud CLI au lieu de la console Google Cloud .
Cliquez sur Copier.
gcloud
Pour copier une sauvegarde avec une nouvelle configuration de chiffrement vers une autre instance du même projet, exécutez la commande gcloud spanner backups copy suivante :
gcloud spanner backups copy --async \
--source-instance=INSTANCE_ID \
--source-backup=SOURCE_BACKUP_NAME \
--destination-instance=DESTINATION_INSTANCE_ID \
--destination-backup=DESTINATION_BACKUP_NAME \
--expiration-date=EXPIRATION_DATE \
--encryption-type=CUSTOMER_MANAGED_ENCRYPTION \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]Pour copier une sauvegarde avec une nouvelle configuration de chiffrement vers une autre instance dans un autre projet, exécutez la commande gcloud spanner backups copy suivante :
gcloud spanner backups copy --async \
--source-backup=SOURCE_BACKUP_NAME \
--destination-backup=DESTINATION_BACKUP_NAME \
--encryption-type=CUSTOMER_MANAGED_ENCRYPTION \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]Pour vérifier que la sauvegarde copiée est chiffrée avec CMEK :
gcloud spanner backups describe BACKUP \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDBibliothèques clientes
C#
Pour copier une sauvegarde CMEK dans une configuration d'instance multirégionale :
C++
Pour copier une sauvegarde CMEK dans une configuration d'instance multirégionale :
Go
Pour copier une sauvegarde CMEK dans une configuration d'instance multirégionale :
Java
Pour copier une sauvegarde CMEK dans une configuration d'instance multirégionale :
Node.js
Pour copier une sauvegarde CMEK dans une configuration d'instance multirégionale :
PHP
Pour copier une sauvegarde CMEK dans une configuration d'instance multirégionale :
Python
Pour copier une sauvegarde CMEK dans une configuration d'instance multirégionale :
Ruby
Pour copier une sauvegarde CMEK dans une configuration d'instance multirégionale :
Restaurer à partir d'une sauvegarde
Vous pouvez restaurer une sauvegarde d'une base de données Spanner dans une nouvelle base de données. Par défaut, les bases de données restaurées à partir d'une sauvegarde utilisent la même configuration de chiffrement que la sauvegarde elle-même, mais vous pouvez ignorer ce comportement en spécifiant une configuration de chiffrement différente pour la base de données restaurée. Si la sauvegarde est protégée par CMEK, la version de clé utilisée pour la créer doit être disponible pour pouvoir la déchiffrer.
Console
Utilisez la console pour restaurer une sauvegarde dans une configuration d'instance régionale.
Dans la console Google Cloud , accédez à la page Instances.
Cliquez sur l'instance contenant la base de données que vous souhaitez restaurer.
Cliquez sur la base de données.
Dans le volet de navigation, cliquez sur Sauvegarder/Restaurer.
Dans le tableau Sauvegardes, sélectionnez Actions pour votre sauvegarde, puis cliquez sur Restaurer.
Sélectionnez l'instance à restaurer et nommez la base de données restaurée.
Facultatif : Si vous souhaitez utiliser une configuration de chiffrement différente avec votre base de données restaurée, cliquez sur le bouton bascule à côté de Utiliser le chiffrement existant.
a. Sélectionnez Clé Cloud KMS.
a. Sélectionnez une clé dans la liste déroulante.
La liste des clés est limitée au projet Google Cloud actuel. Pour utiliser une clé provenant d'un autre projet Google Cloud , créez la base de données à l'aide de gcloud CLI au lieu de la console Google Cloud .
Cliquez sur Restaurer.
gcloud
Pour restaurer une sauvegarde avec une nouvelle configuration de chiffrement, exécutez la commande suivante :gcloud spanner databases restore
gcloud spanner databases restore --async \
--project=SPANNER_PROJECT_ID \
--destination-instance=DESTINATION_INSTANCE_ID \
--destination-database=DESTINATION_DATABASE_ID \
--source-instance=SOURCE_INSTANCE_ID \
--source-backup=SOURCE_BACKUP_NAMEPour vérifier que la base de données restaurée est chiffrée avec CMEK :
gcloud spanner databases describe DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDPour en savoir plus, consultez Restaurer à partir d'une sauvegarde.
Bibliothèques clientes
C#
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance régionale :
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance multirégionale :
C++
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance régionale :
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance multirégionale :
Go
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance régionale :
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance multirégionale :
Java
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance régionale :
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance multirégionale :
Node.js
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance régionale :
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance multirégionale :
PHP
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance régionale :
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance multirégionale :
Python
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance régionale :
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance multirégionale :
Ruby
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance régionale :
Pour restaurer une sauvegarde avec CMEK activé dans une configuration d'instance multirégionale :
Afficher les journaux d'audit de la clé Cloud KMS
Assurez-vous que la journalisation est activée pour l'API Cloud KMS dans votre projet.
Dans la console Google Cloud , accédez à l'explorateur de journaux.
Limitez les entrées de journal à votre clé Cloud KMS en ajoutant les lignes suivantes au générateur de requêtes :
resource.type="cloudkms_cryptokey" resource.labels.location="KMS_KEY_LOCATION" resource.labels.key_ring_id="KMS_KEY_RING_ID" resource.labels.crypto_key_id="KMS_KEY_ID"En fonctionnement normal, les actions de chiffrement et de déchiffrement sont consignées avec le niveau de gravité
INFO. Ces entrées sont consignées lorsque les zones de votre instance Spanner interrogent la clé Cloud KMS environ toutes les cinq minutes.Si Spanner ne parvient pas à accéder à la clé, les opérations sont consignées en tant que
ERROR.

