Learn optimization tips from IT leaders from Uber, Air Asia, Deloitte, ADT and more at our free IT Heroes Summit. Watch now.
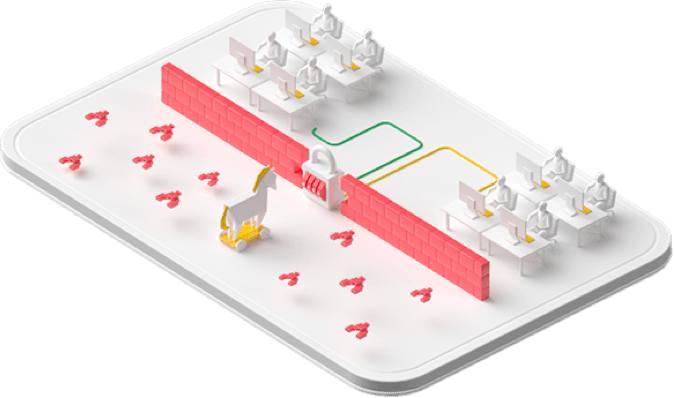
Operational and device security
We develop and deploy infrastructure software using rigorous security practices. Our operations teams detect and respond to threats to the infrastructure from both insiders and external actors, 24/7/365.
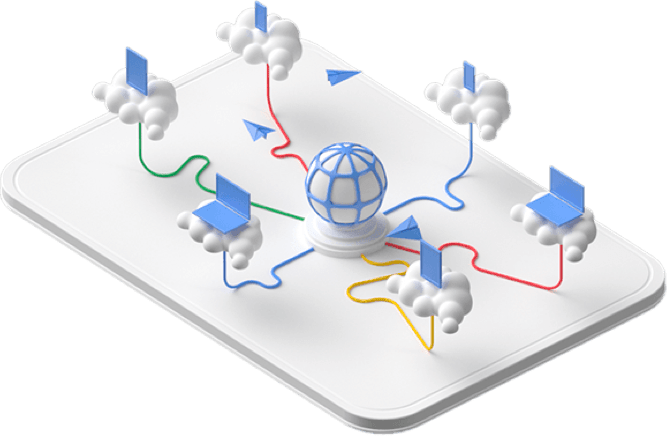
Internet communication
Communications over the internet to our public cloud services are encrypted in transit. Our network and infrastructure have multiple layers of protection to defend our customers against denial-of-service attacks.
Identity
Identities, users, and services are strongly authenticated. Access to sensitive data is protected by advanced tools like phishing-resistant security keys.

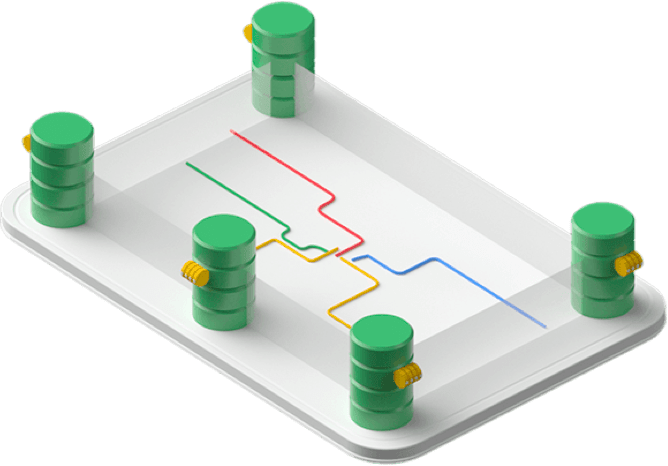
Storage services
Data stored on our infrastructure is automatically encrypted at rest and distributed for availability and reliability. This helps guard against unauthorized access and service interruptions.
Service deployment
Any application that runs on our infrastructure is deployed with security in mind. We don't assume any trust between services, and we use multiple mechanisms to establish and maintain trust. Our infrastructure was designed to be multi-tenant from the start.

Hardware infrastructure
From the physical premises to the purpose-built servers, networking equipment, and custom security chips to the low-level software stack running on every machine, our entire hardware infrastructure is Google-controlled, -secured, and -hardened.

Data centers
Google data centers feature layered security with custom-designed electronic access cards, alarms, vehicle access barriers, perimeter fencing, metal detectors, biometrics, and laser beam intrusion detection. They are monitored 24/7 by high-resolution cameras that can detect and track intruders. Only approved employees with specific roles may enter.
Our network
Google owns and operates one of the largest backbone networks in the world to connect our data centers. When your traffic is on our network, it no longer transits the public internet, making it less likely to be attacked, intercepted, or manipulated.
Take the next step
Tell us what you’re solving for. A Google Cloud expert will help you find the best solution.
Learn security best practices
See our best practicesSolve common problems
Watch security use-case videosWork with a partner
See our security partners













