Shielded VMs
Hardened virtual machines on Google Cloud
Shielded VM offers verifiable integrity of Compute Engine VM instances, so you can be confident your instances haven't been compromised by boot- or kernel-level malware.
Features
Protect your VMs against advanced threats
In just a few clicks, you can enable Shielded VMs to help protect against threats such as malicious project insiders, malicious guest firmware, and kernel- or user-mode vulnerabilities.
Ensure that your workloads are trusted and verifiable
Shielded VMs help protect your virtual machines against rootkits and boot- and kernel-level malware with secure and measured boot capabilities. Using a vTPM, Shielded VMs provide a virtual root-of-trust to verify VM identity and ensure they’re part of your specified project and region.
Help protect secrets against exfiltration and replay
Using Shielded VMs, secrets generated or protected by a vTPM are sealed to a VM and only revealed once integrity is verified.
Verifiable integrity with secure and measured boot
Secure boot helps prevent malicious code from being loaded early in the boot sequence. Measured boot ensures the integrity of the bootloader and kernel and boot drivers to guard against malicious modifications to the VM.
vTPM exfiltration resistance
Validate your guest VM pre-boot and boot integrity using vTPM technology, which is compatible with Trusted Computing Group TPM 2.0 specifications and is FIPS 140-2 L1 verified. A vTPM generates and securely stores encryption keys or sensitive data on guest operating systems.
Trusted UEFI firmware
Trusted firmware is based on Unified Extensible Firmware Interface (UEFI) 2.3.1, which replaces legacy BIOS sub-systems and enables UEFI Secure Boot capability.
Tamper-evident attestations
Gain insight into the integrity state of Shielded VMs with tamper-evident attestation claims available in Cloud Logging and Cloud Monitoring. These integrity measurements help identify changes from the "healthy" baseline of your VM and current runtime state.
Live migration and patching
Keep your virtual machine instances running even when a host system event occurs, such as a software or hardware update.
Define IAM policies and permissions
Set policies and permissions that constrain all new Compute Engine instances to use Shielded VM disk images and have vTPM and integrity monitoring options enabled.
Shield existing VM images
Transform your existing VMs into Shielded VMs that run on Google Cloud, bringing verifiable integrity and exfiltration resistance to your existing images.
How It Works
Shielded VMs are virtual machines hardened by a set of security controls that help defend against rootkits and bootkits. Shielded VMs leverage advanced platform security capabilities such as secure and measured boot, a virtual trusted platform module (vTPM), UEFI firmware, and integrity monitoring.
Shielded VMs are virtual machines hardened by a set of security controls that help defend against rootkits and bootkits. Shielded VMs leverage advanced platform security capabilities such as secure and measured boot, a virtual trusted platform module (vTPM), UEFI firmware, and integrity monitoring.
Common Uses
Secure your VMs
Hardened security for VMs
Hardened security for VMs
Getting started
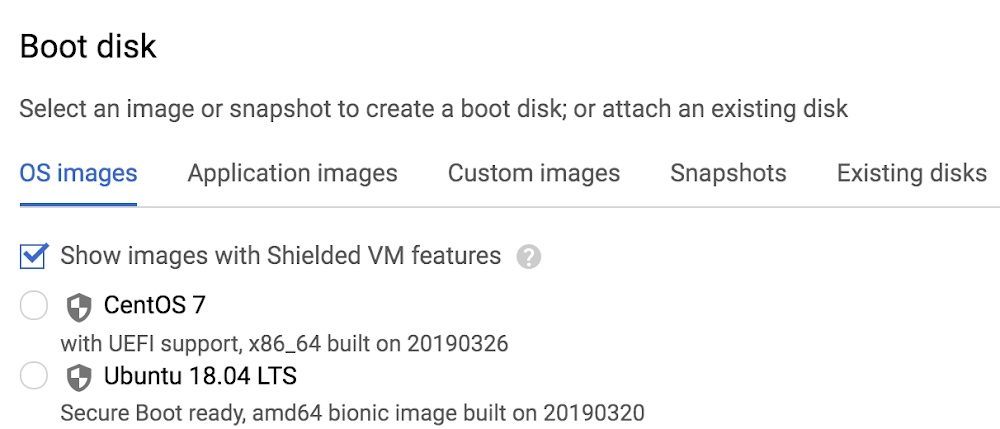
It’s easy to get started with Shielded VM. In the Google Cloud console, when you're creating a new VM instance or instance template, simply check the "Show images with Shielded VM features" checkbox.
Next, you can adjust your Shielded VM configuration options under the Security tab. Here you can gain more granular control over Shielded VM functionality, including the option to enable or disable Secure Boot, vTPM, and integrity monitoring. By default, vTPM and integrity monitoring are enabled; Secure Boot requires explicit opt-in.
If you're looking for additional centralized and programmatic control over your organization's VM instances, we've also made a new organization policy available for Shielded VM.
Tutorials, quickstarts, & labs
Hardened security for VMs
Hardened security for VMs
Getting started
It’s easy to get started with Shielded VM. In the Google Cloud console, when you're creating a new VM instance or instance template, simply check the "Show images with Shielded VM features" checkbox.
Next, you can adjust your Shielded VM configuration options under the Security tab. Here you can gain more granular control over Shielded VM functionality, including the option to enable or disable Secure Boot, vTPM, and integrity monitoring. By default, vTPM and integrity monitoring are enabled; Secure Boot requires explicit opt-in.
If you're looking for additional centralized and programmatic control over your organization's VM instances, we've also made a new organization policy available for Shielded VM.
Pricing
| Shielded VMs pricing | There is no separate charge for using Shielded VMs. | |
|---|---|---|
| Service | Description | Pricing |
Shielded VMs | Enable Shielded VM options in the Google Cloud console. | Free |
Shielded VMs pricing
There is no separate charge for using Shielded VMs.
Shielded VMs
Enable Shielded VM options in the Google Cloud console.
Free