本主题介绍如何将加密密钥作为新密钥版本导入到 Cloud HSM 或 Cloud Key Management Service。
如需详细了解如何导入密钥(包括限制和局限),请参阅密钥导入。
您可以在 5 至 10 分钟内完成本主题中的步骤,但不包括准备工作步骤。手动封装密钥会增加任务的复杂性。
准备工作
建议您创建一个新项目来测试此功能,以便在测试后轻松清理并确保您拥有足够的 Identity and Access Management (IAM) 权限来导入密钥。
在导入密钥之前,您需要准备项目、本地系统和密钥本身。
准备项目
- Sign in to your Google Cloud account. If you're new to Google Cloud, create an account to evaluate how our products perform in real-world scenarios. New customers also get $300 in free credits to run, test, and deploy workloads.
-
In the Google Cloud console, on the project selector page, select or create a Google Cloud project.
Roles required to select or create a project
- Select a project: Selecting a project doesn't require a specific IAM role—you can select any project that you've been granted a role on.
-
Create a project: To create a project, you need the Project Creator
(
roles/resourcemanager.projectCreator), which contains theresourcemanager.projects.createpermission. Learn how to grant roles.
-
Verify that billing is enabled for your Google Cloud project.
-
Enable the required API.
Roles required to enable APIs
To enable APIs, you need the Service Usage Admin IAM role (
roles/serviceusage.serviceUsageAdmin), which contains theserviceusage.services.enablepermission. Learn how to grant roles. -
Install the Google Cloud CLI.
-
如果您使用的是外部身份提供方 (IdP),则必须先使用联合身份登录 gcloud CLI。
-
如需初始化 gcloud CLI,请运行以下命令:
gcloud init -
In the Google Cloud console, on the project selector page, select or create a Google Cloud project.
Roles required to select or create a project
- Select a project: Selecting a project doesn't require a specific IAM role—you can select any project that you've been granted a role on.
-
Create a project: To create a project, you need the Project Creator
(
roles/resourcemanager.projectCreator), which contains theresourcemanager.projects.createpermission. Learn how to grant roles.
-
Verify that billing is enabled for your Google Cloud project.
-
Enable the required API.
Roles required to enable APIs
To enable APIs, you need the Service Usage Admin IAM role (
roles/serviceusage.serviceUsageAdmin), which contains theserviceusage.services.enablepermission. Learn how to grant roles. -
Install the Google Cloud CLI.
-
如果您使用的是外部身份提供方 (IdP),则必须先使用联合身份登录 gcloud CLI。
-
如需初始化 gcloud CLI,请运行以下命令:
gcloud init -
执行导入的用户需要以下 IAM 权限才能创建密钥环、密钥和导入作业。如果用户不是项目所有者,您可以为该用户分配以下两个预定义角色:
roles/editorroles/cloudkms.importer
如需详细了解 Cloud KMS 的可用 IAM 角色和权限,请参阅权限和角色。
- 如果您想要允许 Google Cloud CLI 自动封装密钥再将密钥传输到 Google Cloud,则必须在本地系统上安装 Pyca 加密库。Pyca 库供导入作业使用,该导入作业用于在将密钥发送到 Google Cloud之前在本地封装和保护密钥。
- 如果您想手动封装密钥,则必须配置 OpenSSL 以便手动封装密钥。
保护级别指示密钥是保存在软件中、HSM 还是外部密钥管理系统中。无法将密钥材料从这些存储环境之一移到另一个存储环境。密钥的所有版本都具有相同的保护级别。
用途指示密钥的版本是用于对称加密、非对称加密还是非对称签名。密钥的用途会限制可用于创建该密钥的版本的可能算法。密钥的所有版本都具有相同的用途。
在 Google Cloud 控制台中,前往密钥管理页面。
点击创建密钥环。
在密钥环名称字段中,输入密钥环的名称。
在位置类型下,选择位置类型和位置。
点击创建。此时会打开创建密钥页面。
在密钥名称字段中,输入密钥的名称。
对于保护级别,选择软件或 HSM,然后点击继续。
对于密钥材料,选择导入的密钥,然后点击继续。 这样做可以防止创建初始密钥版本。
为密钥设置用途和算法,然后点击继续。
可选:如果您希望此密钥仅包含导入的密钥版本,请选择将密钥版本限制为仅供导入。这可防止您在 Cloud KMS 中意外创建新密钥版本。
可选:对于导入的密钥,自动轮替在默认情况下处于停用状态。 如需启用自动轮替,请从密钥轮替周期字段中选择一个值。
如果启用自动轮替,则新密钥版本将在 Cloud KMS 中生成,并且导入的密钥版本将不再是轮替之后的默认密钥版本。
点击创建。
创建目标密钥环。如果您打算导入到 Cloud HSM 密钥,请选择支持 Cloud HSM 的位置。
gcloud kms keyrings create KEY_RING \ --location LOCATION
您可以详细了解如何创建密钥环。
创建目标密钥。
- 指定密钥的用途。
- 使用
--skip-initial-version-creation标志阻止创建初始版本。 - 可选:使用
--import-only标志防止在 Cloud KMS 中创建新版本。 - 可选:不指定轮替政策。如果启用自动轮替,则新密钥版本将在 Cloud KMS 中生成,并且导入的密钥版本将不再是轮替之后的默认密钥版本。如果指定了
--import-only标志,则不能指定轮替政策。
gcloud kms keys create KEY_NAME \ --location LOCATION \ --keyring KEY_RING \ --purpose PURPOSE \ --skip-initial-version-creation \ --import-only
您可以详细了解如何创建 Cloud KMS 密钥或 Cloud HSM 密钥。
创建新的密钥环:
curl "https://cloudkms.googleapis.com/v1/projects/PROJECT_ID/locations/LOCATION/keyRings?keyRingId=KEY_RING" \ --request "POST" \ --header "authorization: Bearer TOKEN" \ --header "content-type: application/json" \ --header "x-goog-user-project: PROJECT_ID" \ --data "{}"如需了解详情,请参阅
KeyRing.createAPI 文档。创建仅限导入的空密钥:
curl "https://cloudkms.googleapis.com/v1/projects/PROJECT_ID/locations/LOCATION/keyRings/KEY_RING/cryptoKeys?cryptoKeyId=KEY_NAME&skipInitialVersionCreation=true&importOnly=true" \ --request "POST" \ --header "authorization: Bearer TOKEN" \ --header "content-type: application/json" \ --header "x-goog-user-project: PROJECT_ID" \ --data "{"purpose":"PURPOSE", "versionTemplate":{"protectionLevel":"PROTECTION_LEVEL","algorithm":"ALGORITHM"}}"如需了解详情,请参阅
CryptoKey.createAPI 文档。前往 Google Cloud 控制台中的密钥管理页面。
点击目标密钥环的名称。
将保护级别设置为软件或 HSM。使用与您设置给目标密钥相同的保护级别。
点击创建导入作业。
在名称字段中,输入导入作业的名称。
从导入方法下拉列表,将导入方法设置为 3072 位 RSA或 4096 位 RSA。
点击创建。
- 使用与目标密钥相同的密钥环和位置。
- 将保护级别设置为
software或hsm。 - 将导入方法设置为
rsa-oaep-3072-sha1-aes-256、rsa-oaep-4096-sha1-aes-256、rsa-oaep-3072-sha256-aes-256、rsa-oaep-4096-sha256-aes-256、rsa-oaep-3072-sha256或rsa-oaep-4096-sha256。 前往 Google Cloud 控制台中的密钥管理页面。
点击包含导入作业的密钥环的名称。
点击页面顶部的导入作业标签页。
状态将会显示在导入作业名称旁的状态下。
- 仅向密钥管理员授予
importjobs.create权限。 - 向要将使用该作业导入密钥的操作员授予特定导入作业的
importjobs.useToImport权限。 - 创建导入作业时,请为使用它导入的密钥版本指定保护级别和算法。
用途为
ENCRYPT_DECRYPT的密钥使用google-symmetric-encryption算法,长度为 32。用途为
ASYMMETRIC_DECRYPT或ASYMMETRIC_SIGN的密钥支持各种算法和长度。创建密钥后不能更改密钥的用途,但可以使用与初始密钥版本不同的长度创建后续密钥版本。
在Google Cloud 控制台中打开密钥管理页面。
点击包含导入作业的密钥环的名称。系统会显示目标密钥以及密钥环上的任何其他密钥。
点击目标密钥的名称,然后点击导入密钥版本。
从选择导入作业下拉列表中选择您的导入作业。
在上传封装密钥选择器中,选择已封装的密钥。
如果要导入非对称密钥,请从算法下拉列表中选择算法。导入密钥版本页面应如下所示:
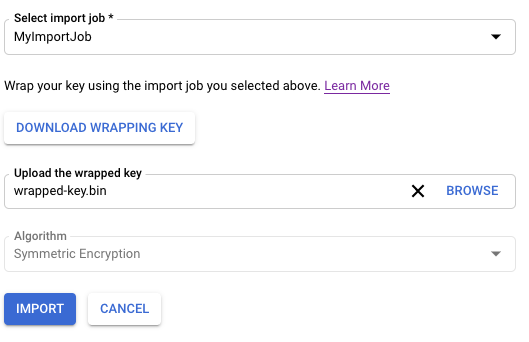
点击导入。
IMPORT_JOB_ID:相应导入作业的完整资源名称。
ALGORITHM:要导入的密钥的
algorithm,其类型为CryptoKeyVersionAlgorithm。WRAPPED_KEY:采用 base64 格式的手动封装密钥。
在Google Cloud 控制台中打开密钥管理页面。
点击包含导入作业的密钥环的名称。
点击页面顶部的导入作业标签页。
状态将会显示在导入作业名称旁的状态下。
- 只有以前导入的
CryptoKeyVersions才能重新导入。 - 如果以前已成功导入版本,则重新导入的密钥材料必须与原始密钥材料完全一致。
- 在此功能发布之前销毁的
CryptoKeyVersions无法重新导入。如果版本符合重新导入的条件,则CryptoKeyVersion的reimport_eligible字段为true,否则为false。 前往 Google Cloud 控制台中的密钥管理页面。
点击您要重新导入的密钥版本的密钥所在的密钥环的名称。
点击您要重新导入的密钥版本的密钥。
点击您要重新导入的密钥版本旁边的三个点。
选择重新导入密钥版本
从选择导入作业下拉列表中选择您的导入作业。
在上传封装密钥选择器中,选择已封装的密钥。该密钥必须与原始密钥材料匹配。
点击重新导入。
使用原始密钥材料重新导入密钥版本。
gcloud kms keys versions import \ --location LOCATION \ --keyring KEY_RING \ --key KEY_NAME \ --version KEY_VERSION \ --algorithm ALGORITHM \ --import-job IMPORT_JOB \ --target-key-file PATH_TO_KEY \
在
cryptoKeyVersions.import方法的请求正文中,将cryptoKeyVersion字段设置为要导入的版本的密钥版本名称。它必须是加密密钥的子级。在请求正文中,将
algorithm字段设置为要导入的密钥的算法。此值必须与原始密钥版本的算法匹配。algorithm字段的类型为CryptoKeyVersionAlgorithm。在请求正文中,将
wrappedKeyMaterial字段设置为您已封装的密钥材料。调用
cryptoKeyVersions.import方法。cryptoKeyVersions.import响应的类型为CryptoKeyVersion。成功导入密钥后,其状态为ENABLED,您可以在 Cloud KMS 中使用该密钥。- 验证导入的密钥。确认导入的密钥材料与原始密钥完全相同后,您可以使用该密钥进行签名或保护数据。
- 密钥导入失败问题排查。
准备本地系统
选择以下选项之一以准备本地系统:对于大多数用户,推荐使用自动封装密钥功能。
准备密钥
验证密钥的算法和长度是否受支持。密钥的允许算法取决于密钥是用于对称加密、非对称加密还是非对称签名,以及密钥是存储在软件还是 HSM 中。您可以在导入请求中指定密钥的算法。
您还必须单独验证密钥的编码方式,并在必要时进行调整。
在创建或导入密钥版本后,无法更改以下内容:
如果您没有要导入的密钥,但想要验证导入密钥的过程,则可以在本地系统上使用以下命令创建对称密钥:
openssl rand 32 > ${HOME}/test.bin
仅将此密钥用于测试。以这种方式创建的密钥可能不适合生产用途。
如果您需要手动封装密钥,请先完成此步骤,然后再按照本主题的步骤继续操作。
创建目标密钥和密钥环
Cloud KMS 密钥是一个包含零个或多个密钥版本的容器对象。每个密钥版本都包含一个加密密钥。
将密钥导入 Cloud KMS 或 Cloud HSM 时,导入的密钥将成为现有 Cloud KMS 或 Cloud HSM 密钥上的新密钥版本。在本主题的其余部分中,此密钥称为目标密钥。在导入密钥材料之前,目标密钥必须已存在。
导入密钥版本不会影响该密钥的现有版本。但是,建议您在测试密钥导入时创建空密钥。空密钥没有版本,处于无效状态,且无法使用。
您可以视需要指定新建的密钥只能包含导入的版本,这可以防止在 Cloud KMS 中意外生成新版本。
密钥环中存在密钥;在本主题中,此密钥环称为目标密钥环。目标密钥环的位置决定了导入后密钥材料的可用位置。无法在某些位置创建或导入 Cloud HSM 密钥。创建密钥后,无法将其移至其他密钥环或位置。
按照以下步骤使用 Google Cloud CLI 或 Google Cloud 控制台在新密钥环上创建空密钥。
控制台
gcloud
如需在命令行上使用 Cloud KMS,请先安装或升级到最新版本的 Google Cloud CLI。
Go
要运行此代码,请先设置 Go 开发环境并安装 Cloud KMS Go SDK。
Java
要运行此代码,请先设置 Java 开发环境并安装 Cloud KMS Java SDK。
Node.js
要运行此代码,请先设置 Node.js 开发环境并安装 Cloud KMS Node.js SDK。
Python
要运行此代码,请先设置 Python 开发环境并安装 Cloud KMS Python SDK。
API
这些示例使用 curl 作为 HTTP 客户端来演示如何使用 API。如需详细了解访问权限控制,请参阅访问 Cloud KMS API。
密钥环和密钥现在已存在,但密钥不包含密钥材料,没有版本,且处于无效状态。接下来创建导入作业。
创建导入作业
导入作业定义其导入的密钥的特性,包括导入密钥后无法更改的属性。
保护级别定义了此导入作业导入的密钥是位于软件、HSM 还是外部密钥管理系统中。最终导入密钥后,无法更改保护级别。
导入方法定义用于创建封装密钥的算法,用于在从本地系统传输到目标 Google Cloud 项目的过程中保护导入的密钥。您可以选择 3072 位或 4096 位 RSA 密钥。除非您有特定要求,否则建议使用 3072 位封装密钥。
您可以使用 gcloud CLI、Google Cloud 控制台或 Cloud Key Management Service API 创建导入作业。
控制台
gcloud
如需在命令行上使用 Cloud KMS,请先安装或升级到最新版本的 Google Cloud CLI。
使用如下所示的命令创建导入作业。
gcloud kms import-jobs create IMPORT_JOB \ --location LOCATION \ --keyring KEY_RING \ --import-method IMPORT_METHOD \ --protection-level PROTECTION_LEVEL
Go
要运行此代码,请先设置 Go 开发环境并安装 Cloud KMS Go SDK。
Java
要运行此代码,请先设置 Java 开发环境并安装 Cloud KMS Java SDK。
Node.js
要运行此代码,请先设置 Node.js 开发环境并安装 Cloud KMS Node.js SDK。
Python
要运行此代码,请先设置 Python 开发环境并安装 Cloud KMS Python SDK。
API
这些示例使用 curl 作为 HTTP 客户端来演示如何使用 API。如需详细了解访问权限控制,请参阅访问 Cloud KMS API。
如需创建导入作业,请使用 ImportJobs.create 方法:
curl "https://cloudkms.googleapis.com/v1/projects/PROJECT_ID/locations/LOCATION/keyRings/KEY_RING/importJobs?import_job_id=IMPORT_JOB_ID" \
--request "POST" \
--header "authorization: Bearer TOKEN" \
--header "content-type: application/json" \
--data '{"import_method": "IMPORT_METHOD", "protection_level": "PROTECTION_LEVEL"}'
替换以下内容:
检查导入作业的状态
导入作业的初始状态为 PENDING_GENERATION。当状态为 ACTIVE 时,您可以使用它导入密钥。
导入作业将在三天后过期。如果导入作业已过期,则必须创建新导入作业。
您可以使用 Google Cloud CLI、Google Cloud 控制台或 Cloud Key Management Service API 来检查导入作业的状态。
控制台
gcloud
如需在命令行上使用 Cloud KMS,请先安装或升级到最新版本的 Google Cloud CLI。
当导入作业处于有效状态时,您可以使用它来导入密钥。这可能需要几分钟的时间。使用此命令验证导入作业是否处于有效状态。使用创建导入作业的位置和密钥环。
gcloud kms import-jobs describe IMPORT_JOB \ --location LOCATION \ --keyring KEY_RING \ --format="value(state)"
输出类似于以下内容:
state: ACTIVE
Go
要运行此代码,请先设置 Go 开发环境并安装 Cloud KMS Go SDK。
Java
要运行此代码,请先设置 Java 开发环境并安装 Cloud KMS Java SDK。
Node.js
要运行此代码,请先设置 Node.js 开发环境并安装 Cloud KMS Node.js SDK。
Python
要运行此代码,请先设置 Python 开发环境并安装 Cloud KMS Python SDK。
API
这些示例使用 curl 作为 HTTP 客户端来演示如何使用 API。如需详细了解访问权限控制,请参阅访问 Cloud KMS API。
如需检查导入作业的状态,请使用 ImportJobs.get 方法:
curl "https://cloudkms.googleapis.com/v1/projects/PROJECT_ID/locations/LOCATION/keyRings/KEY_RING/importJobs/IMPORT_JOB_ID" \
--request "GET" \
--header "authorization: Bearer TOKEN"
导入作业处于活动状态时,您可以发出导入密钥的请求。
防止修改导入作业
导入作业将确定所导入密钥的许多特性,包括密钥的算法以及所导入密钥是 HSM 密钥还是软件密钥。您可以配置 IAM 权限,以阻止用户创建导入作业,同时允许用户使用导入作业导入密钥。
在导入作业到期之前,具有指定导入作业的 importjobs.useToImport 权限但没有 importjobs.create 权限的用户可以导入密钥,但无法修改导入作业的特性。
导入密钥
检查导入作业的状态后,您可以发出导入请求。
您可以使用不同的标志来发出导入请求,具体取决于您是希望 Google Cloud CLI 自动封装密钥,还是您已手动封装密钥。
无论您是手动还是自动封装密钥,都必须将算法设置为与要导入的实际密钥的长度匹配的受支持算法,并指定密钥的用途。
自动封装和导入密钥
如果您想使用自动封装功能,则必须使用 Google Cloud CLI。使用如下所示的命令。将 --target-key-file 设置为要封装并导入的未封装密钥的位置。切勿设置 --wrapped-key-file。
您可以选择将 --public-key-file 标志设置为已下载公钥的位置。导入大量密钥时,这会阻止在每次导入期间下载公钥。例如,您可以编写一个脚本来下载公钥,然后在导入每个密钥时提供其位置。
gcloud kms keys versions import \
--import-job IMPORT_JOB \
--location LOCATION \
--keyring KEY_RING \
--key KEY_NAME \
--algorithm ALGORITHM \
--target-key-file PATH_TO_UNWRAPPED_KEY
密钥由与导入作业关联的封装密钥封装,将被传输到 Google Cloud,并作为目标密钥上的新密钥版本导入。
导入手动封装的密钥
按照本部分中的说明导入已手动封装的密钥。将 --wrapped-key-file 设置为手动封装的密钥所在的位置。切勿设置 --target-key-file。
您可以选择将 --public-key-file 标志设置为已下载公钥的位置。导入大量密钥时,这会阻止在每次导入期间下载公钥。例如,您可以编写一个脚本来下载公钥,然后在导入每个密钥时提供其位置。
控制台
gcloud
如需在命令行上使用 Cloud KMS,请先安装或升级到最新版本的 Google Cloud CLI。
使用如下所示的命令。
gcloud kms keys versions import \ --import-job IMPORT_JOB \ --location LOCATION \ --keyring KEY_RING \ --key KEY_NAME \ --algorithm ALGORITHM \ --wrapped-key-file PATH_TO_WRAPPED_KEY
如需了解详情,请参阅 gcloud kms keys versions import --help 命令的输出。
Go
要运行此代码,请先设置 Go 开发环境并安装 Cloud KMS Go SDK。
Java
要运行此代码,请先设置 Java 开发环境并安装 Cloud KMS Java SDK。
Node.js
要运行此代码,请先设置 Node.js 开发环境并安装 Cloud KMS Node.js SDK。
Python
要运行此代码,请先设置 Python 开发环境并安装 Cloud KMS Python SDK。
API
这些示例使用 curl 作为 HTTP 客户端来演示如何使用 API。如需详细了解访问权限控制,请参阅访问 Cloud KMS API。
使用 cryptoKeyVersions.import 方法导入密钥。
curl "https://cloudkms.googleapis.com/v1/projects/PROJECT_ID/locations/LOCATION/keyRings/KEY_RING/cryptoKeys/KEY_NAME/cryptoKeyVersions:import" \
--request "POST" \
--header "authorization: Bearer TOKEN" \
--header "content-type: application/json" \
--data '{"importJob": "IMPORT_JOB_ID", "algorithm": "ALGORITHM", "wrappedKey": "WRAPPED_KEY"}'
替换以下内容:
密钥导入请求已启动。您可以监控其状态。
检查导入的密钥版本的状态
导入密钥版本的初始状态为 PENDING_IMPORT。当状态为 ENABLED 时,表示密钥版本已成功导入。如果导入失败,则状态为 IMPORT_FAILED。
您可以使用 Google Cloud CLI、Google Cloud 控制台或 Cloud Key Management Service API 来检查导入请求的状态。
控制台
gcloud
如需在命令行上使用 Cloud KMS,请先安装或升级到最新版本的 Google Cloud CLI。
使用 versions list 命令检查状态。使用您在本主题前面创建的同一个位置、目标密钥环和目标密钥。
gcloud kms keys versions list \ --keyring KEY_RING \ --location LOCATION \ --key KEY_NAME
Go
要运行此代码,请先设置 Go 开发环境并安装 Cloud KMS Go SDK。
Java
要运行此代码,请先设置 Java 开发环境并安装 Cloud KMS Java SDK。
Node.js
要运行此代码,请先设置 Node.js 开发环境并安装 Cloud KMS Node.js SDK。
Python
要运行此代码,请先设置 Python 开发环境并安装 Cloud KMS Python SDK。
API
这些示例使用 curl 作为 HTTP 客户端来演示如何使用 API。如需详细了解访问权限控制,请参阅访问 Cloud KMS API。
调用 ImportJob.get 方法并检查 state 字段。如果 state 为 PENDING_GENERATION,表示导入作业仍在创建中。请定期重新检查状态,直到状态为 ACTIVE。
导入初始密钥版本后,密钥的状态会变为有效。对于对称密钥,您必须先将导入的密钥版本设置为主版本,然后才能使用该密钥。
对称密钥:设置主要版本
导入对称密钥时,必须执行此步骤,非对称密钥则无需执行此步骤。非对称密钥没有主要版本。您必须使用 Google Cloud CLI 来设置主要版本。
gcloud kms keys set-primary-version KEY_NAME\
--location=LOCATION\
--keyring=KEY_RING\
--version=KEY_VERSION
重新导入先前销毁的密钥
Cloud Key Management Service 支持密钥重新导入,该服务通过提供原始密钥材料,可将先前导入的处于 DESTROYED 或 IMPORT_FAILED 状态的密钥版本恢复到 ENABLED 状态。如果由于初始导入失败而未导入任何原始密钥材料,则系统无法提供任何密钥材料。
限制
软件和 Cloud HSM 密钥可以重新导入,但外部密钥无法重新导入。
重新导入已销毁的密钥
请按照创建导入作业中的步骤创建 ImportJob 以进行重新导入。无论是现有的 ImportJob 或新建的 ImportJob,只要保护级别与原始保护级别匹配,您都可以使用。
控制台
gcloud
如需在命令行上使用 Cloud KMS,请先安装或升级到最新版本的 Google Cloud CLI。
API
这些示例使用 curl 作为 HTTP 客户端来演示如何使用 API。如需详细了解访问权限控制,请参阅访问 Cloud KMS API。

