What is threat intelligence?
Threat intelligence is information about current or potential cyberattacks that organizations use to defend themselves. It transforms raw threat data into actionable insights that security teams can use to detect, prevent, and respond to attacks. Rather than simply collecting information, threat intelligence provides context about who is attacking, their methods and motivations, and specific indicators that signal an attack is underway or imminent.
What is threat intelligence in cyber security?
Effective threat intelligence empowers cybersecurity teams to move from reactive to proactive defense. Instead of waiting for attacks to happen and then responding, you can identify vulnerabilities before attackers exploit them, recognize attack patterns as they emerge, and configure your defenses to stop threats at the perimeter. This data-driven approach reduces the time between when a threat appears and when your organization can defend against it.
Why is threat intelligence important?
Threat intelligence provides the context you need to make informed security decisions. Without it, security teams face an overwhelming volume of alerts and potential threats with limited guidance on which ones matter most. Threat intelligence helps you separate genuine threats from false positives and prioritize your response based on the actual risk to your organization.
The threat landscape evolves constantly as attackers develop new techniques and exploit newly discovered vulnerabilities. Threat intelligence keeps your defenses aligned with current attack methods rather than yesterday’s threats. When you understand the tactics, techniques, and procedures (TTPs) that threat actors use, you can detect their activities earlier in the attack chain and stop them before they cause damage.
Organizations that use threat intelligence effectively can reduce both the frequency and impact of successful attacks. By identifying which threats target your industry and understanding how attackers operate, you can focus your security investments on the controls that actually defend against the attacks you’re most likely to face.
Benefits of centralized threat intelligence
Centralized threat intelligence gives security professionals situational awareness on threat actors and malware on the rise. A centralized repository provides public vulnerability descriptions with CVSS and EPSS severity scoring, letting you assess risk consistently across your environment. You can look up public threat indicators and embed Mandiant indicator confidence scores directly into any web page with browser plugins.
For security analysts, incident responders, and SOC managers, centralized intelligence supports alert prioritization and triage. You can use current threat intelligence to prioritize and contextualize security event information, reducing alert fatigue and improving overall SOC efficiency. Centralized intelligence helps you detect hidden threats by downloading indicators and expanding your detection tools to uncover threat actors or malware activities lingering unseen in your environment.
Centralized threat intelligence accelerates responses by empowering security analyst teams with MITRE ATT&CK-based actor behavior insights. These insights help you understand potential attack progress and formulate the right response. When multiple teams access the same intelligence source, your organization can develop a consistent understanding of threats and maintain coordinated defenses.
Three types of threat intelligence
Threat intelligence operates at different levels to serve different audiences and purposes. Tactical intelligence provides the specific technical details needed to detect and block attacks. Operational intelligence guides threat hunting and helps you understand attacker behavior. Strategic intelligence informs long-term security planning and resource allocation. Each type serves a distinct role in a comprehensive threat intelligence program.
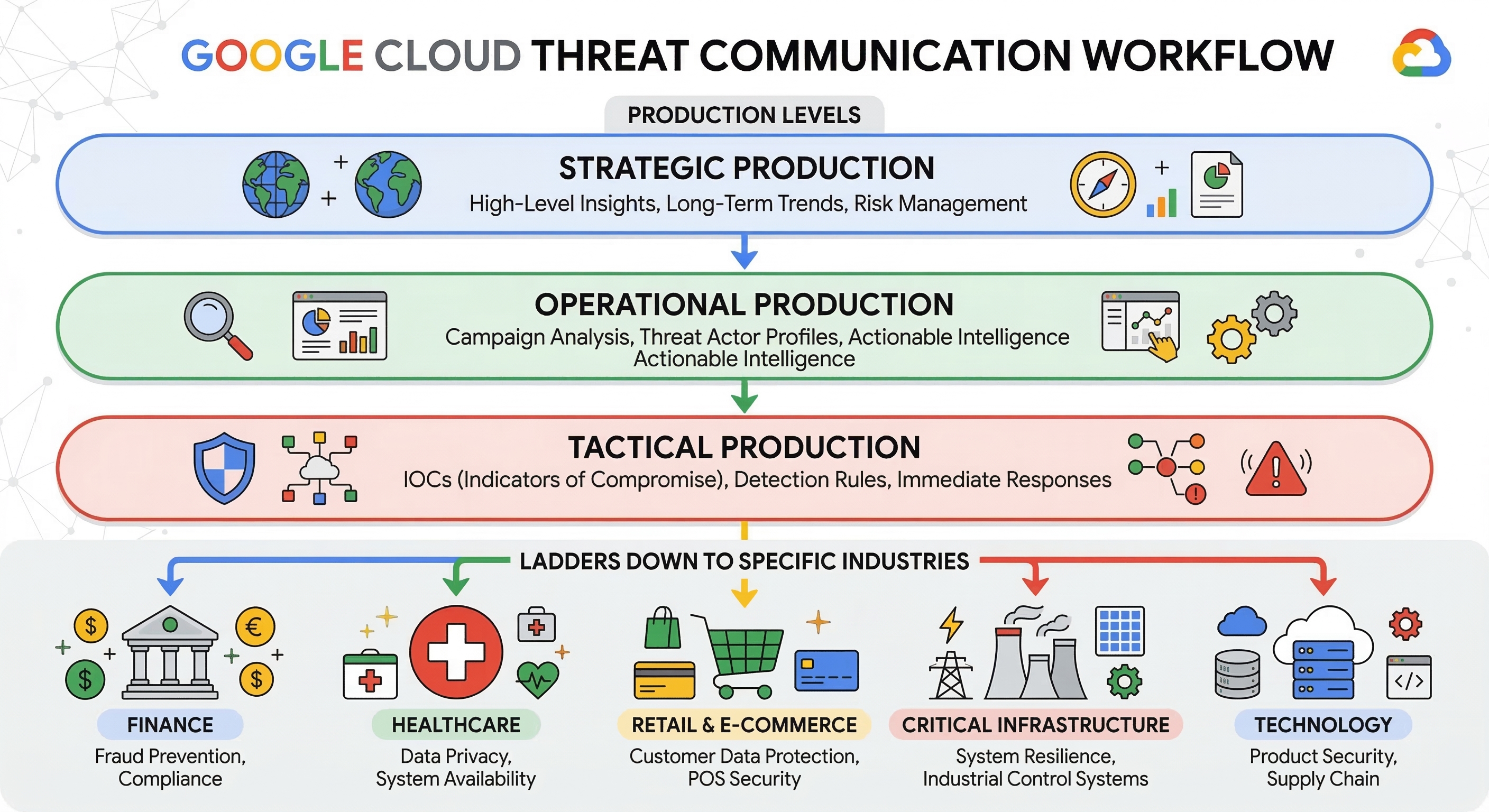
Tactical threat intelligence
Tactical threat intelligence focuses on immediate threats and the technical details needed to detect them. This includes indicators of compromise like malicious IP addresses, file hashes, domain names, and URLs associated with known attacks. Security tools consume tactical intelligence to identify and block threats automatically. Tactical intelligence tends to have a short lifespan because attackers frequently change their infrastructure, so it requires constant updates to remain effective. SOC teams and incident responders rely on tactical intelligence for day-to-day threat detection and response.
Operational threat intelligence
Operational threat intelligence provides detailed information about the TTPs that threat actors use to conduct attacks. This intelligence focuses on understanding attacker behavior and methods rather than specific technical indicators. You can use operational intelligence to identify which threat groups target your industry, how they gain initial access, and what they do once inside a network. Security teams apply operational intelligence to hunting threats, improving detection capabilities, and planning incident response procedures. Operational intelligence typically remains relevant longer than tactical intelligence because attacker methods evolve more slowly than their infrastructure.
Strategic threat intelligence
Strategic threat intelligence provides high-level insights into the threat landscape and helps leadership make informed decisions about security investments and risk management. This intelligence covers trends affecting your industry, geopolitical factors that influence threat actor behavior, and the potential business impact of different threat scenarios. Strategic intelligence is typically presented in reports and briefings for executives, board members, and other non-technical stakeholders. Organizations use strategic intelligence to align security strategy with business objectives and communicate security risks to leadership.
Understanding the threat intelligence lifecycle
The threat intelligence lifecycle is a structured process for gathering, analyzing, and disseminating information about potential threats to an organization. This cyclical framework is what security teams use to transform raw data into actionable intelligence to improve defenses. Each phase of the lifecycle feeds into the next, creating a continuous improvement process that keeps threat intelligence relevant and useful as the threat landscape evolves.
1. Planning and direction
The planning phase is when you establish what intelligence your organization needs and why. Security teams work with stakeholders to define intelligence requirements, which might include understanding which actors target your industry, identifying the vulnerabilities most likely to be exploited, or determining whether a new attack technique affects your infrastructure.
2. Collection
Collection is the process of gathering raw threat data from multiple sources to meet your intelligence requirements. Sources include threat intelligence feeds, security logs from your internal systems, information sharing communities, open source intelligence, and commercial threat intelligence providers. The goal is to collect relevant data that can meet your requirements while filtering out noise that doesn’t serve your needs.
3. Processing
Processing is the phase in which raw threat data is transformed into a format suitable for analysis. This includes normalizing data from different sources into consistent formats, removing duplicates, correlating related information, and filtering out false positives. Automated tools handle much of this work because the volume of threat data typically exceeds what analysts can process manually.
4. Analysis and production
Analysis extracts meaningful insights from processed data and produces intelligence that answers your requirements. Analysts identify patterns, assess the relevance of threats to your organization, and determine the appropriate response actions. The output of this phase is finished intelligence products like threat reports, briefings, and recommendations that stakeholders can use to make security decisions.
5. Feedback and improvement
The purpose of the feedback stage is to evaluate whether the intelligence met stakeholder needs and identify gaps or new requirements. Stakeholders provide input on the usefulness and timeliness of intelligence, which informs adjustments to collection priorities, analysis methods, and dissemination practices. This feedback restarts the cycle with refined requirements that make future intelligence more valuable.
Take the next step
Start building on Google Cloud with $300 in free credits and 20+ always free products.
Need help getting started?
Contact salesWork with a trusted partner
Find a partnerContinue browsing
See all products












