Agentic Defense with Google Security Operations
The Google Cloud agentic SOC is here. Automate the manual toil of security operations and free-up your team to focus on high-value, high-impact work. Fight AI-enabled attackers with machine scale and speed.
Google Security Operations provides Gemini-native agentic defense to help autonomously handle workflows like alert triage, threat hunting, and detection engineering.
Benefits
Transforming security operations with agentic AI
Accelerate threat detection and response
Accelerate threat detection and response
Dramatically shrink response time by autonomously triaging and investigating alerts and hunting for threats in real time. The Triage and Investigation agent helps reduce a typical 30-minute manual analysis to 60 seconds.
Apply real-time intelligence
Apply real-time intelligence
To observe and act like an elite human analyst, Google Security Operations agents are trained on real-world intelligence and insights from Mandiant experts.
Harden your defenses
Harden your defenses
Shift from reactive to proactive security by continuously assessing your environment, identifying coverage gaps, and dynamically generating detections.
Key features
Realizing the Agentic SOC
A dynamic system of AI agents in Google Security Operations automates complex security tasks, counters advanced threats at machine speed, and improves security productivity.
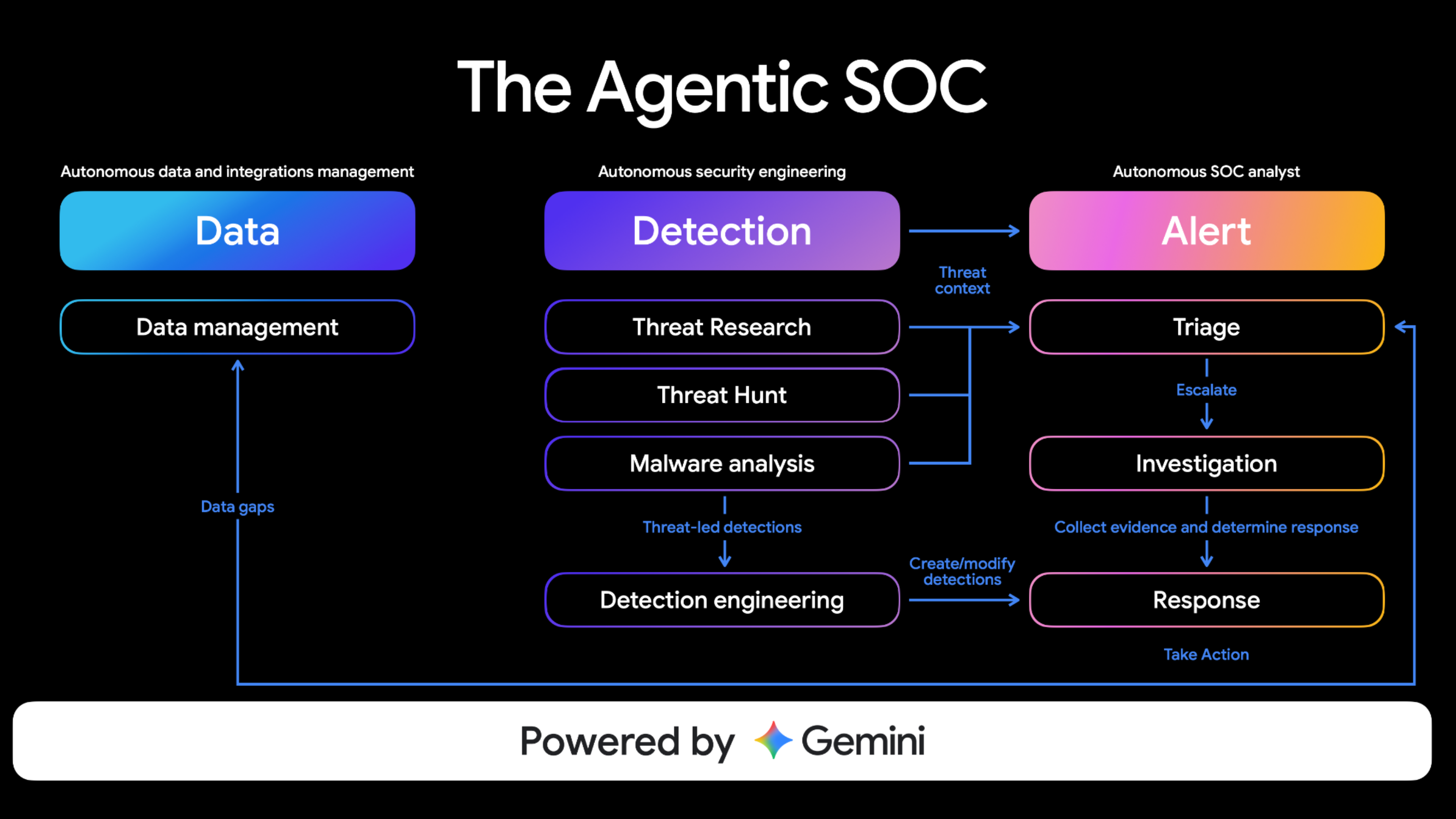
Autonomous triage and investigation
The Triage and Investigation agent helps prioritize threats by autonomously investigating alerts, enriching them with threat intelligence, and providing a verdict with comprehensive explanations–reducing mean time to resolution
Proactive threat hunting
The Threat Hunting agent proactively searches your environment for novel attack patterns and stealthy behaviors that bypass traditional defenses, leveraging intelligence from Mandiant, VirusTotal, and Google to find adversaries before they strike.
Dynamic detection engineering
The Detection Engineering agent continuously analyzes your organization's threat profile to create, test, and generate detection rules, closing coverage gaps as they emerge.
Learn more about how Google is supercharging agentic defense with frontline threat intelligence here.
Leveraging AI agents for security
Embarking on your journey to an Agentic SOC? Explore these resources to kickstart your progress.
Customers
See how Google SecOps customers are using AI today
Documentation
Explore features of Gemini in Google Security Operations
Take the next step
Tell us what you’re solving for. A Google Cloud expert will help you find the best solution.
Work with a trusted partner
Find a partnerStart using Google Cloud
Sign up for a trialDeploy ready-to-go solutions
Explore marketplace