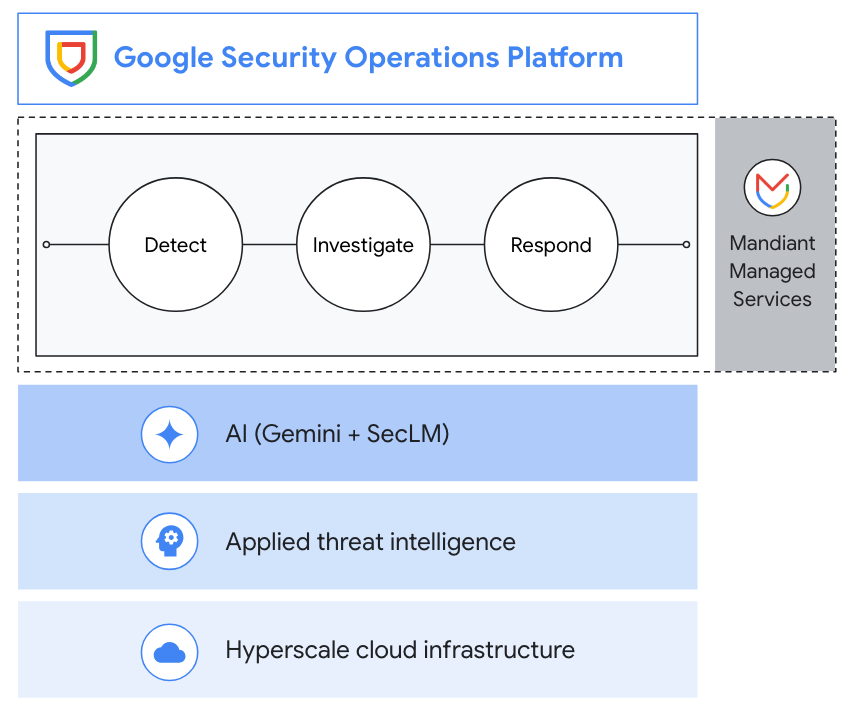
Google Security Operations (SecOps)
The intelligence-driven and AI-powered security operations platform
Google SecOps’ cloud-native security operations platform empowers security teams to better detect, investigate, and respond to cybersecurity threats.
Features
Detect more threats with less effort
Google SecOps provides a rich and growing set of curated detections out of the box. These detections are developed and continuously maintained by our team of threat researchers.
Leverage Gemini to search your data, iterate, and drill down using natural language and to create detections.
Google SecOps also allows for custom detection authoring using the intuitive Yara-L language. In a fraction of the time (and the code).
Reduce preparation and make your data actionable. Route, filter, redact, and transform your security telemetry with data pipeline management capabilities.
Investigate with the right context
Google SecOps offers a streamlined and intuitive analyst experience that includes threat-centric case management, interactive, context-rich alert graphing, and automatic stitching together of entities.
Investigate more efficiently by engaging with our Gemini investigative chat assistant to gain context and details about what's happening in cases, along with receiving AI-generated case summaries and recommendations on how to respond.
Google SecOps enables lightning fast, flexible, and context-rich search capabilities to surface any additional data that is needed as part of an investigation
Respond with speed and precision
Google SecOps includes full fledged security orchestration, automation and response (SOAR) capabilities. Build playbooks that automate common response actions, orchestrate over 300 tools (EDRs, identity management, network security and more), and collaborate with other members of the team using an auto-documenting case wall.
Interact with a context-aware AI-powered chat to easily create playbooks.
Google SecOps makes it easy to track and measure the effectiveness of response efforts such as analyst productivity and MTTR and communicate that with stakeholders.
How It Works
Google Security Operations offers a unified experience across SIEM, SOAR, and threat intelligence to drive better detection, investigation, and response. Collect security telemetry data, apply threat intel to identify high priority threats, drive response with playbook automation, case management, and collaboration.
Google Security Operations offers a unified experience across SIEM, SOAR, and threat intelligence to drive better detection, investigation, and response. Collect security telemetry data, apply threat intel to identify high priority threats, drive response with playbook automation, case management, and collaboration.
Common Uses
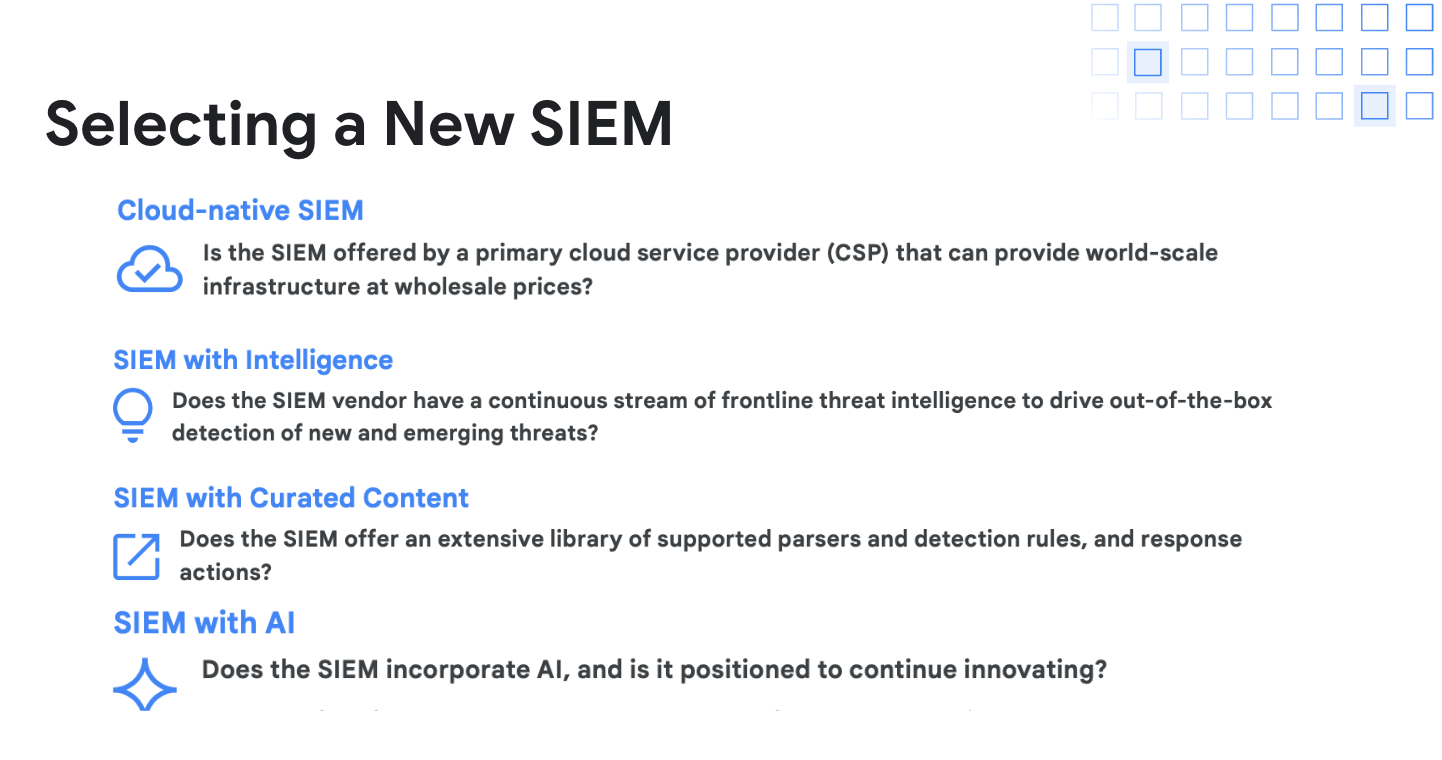
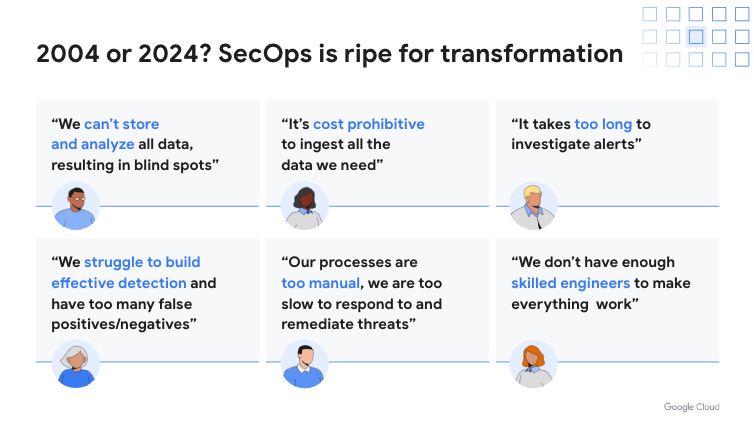
SIEM migration
Google Cloud Cybershield™
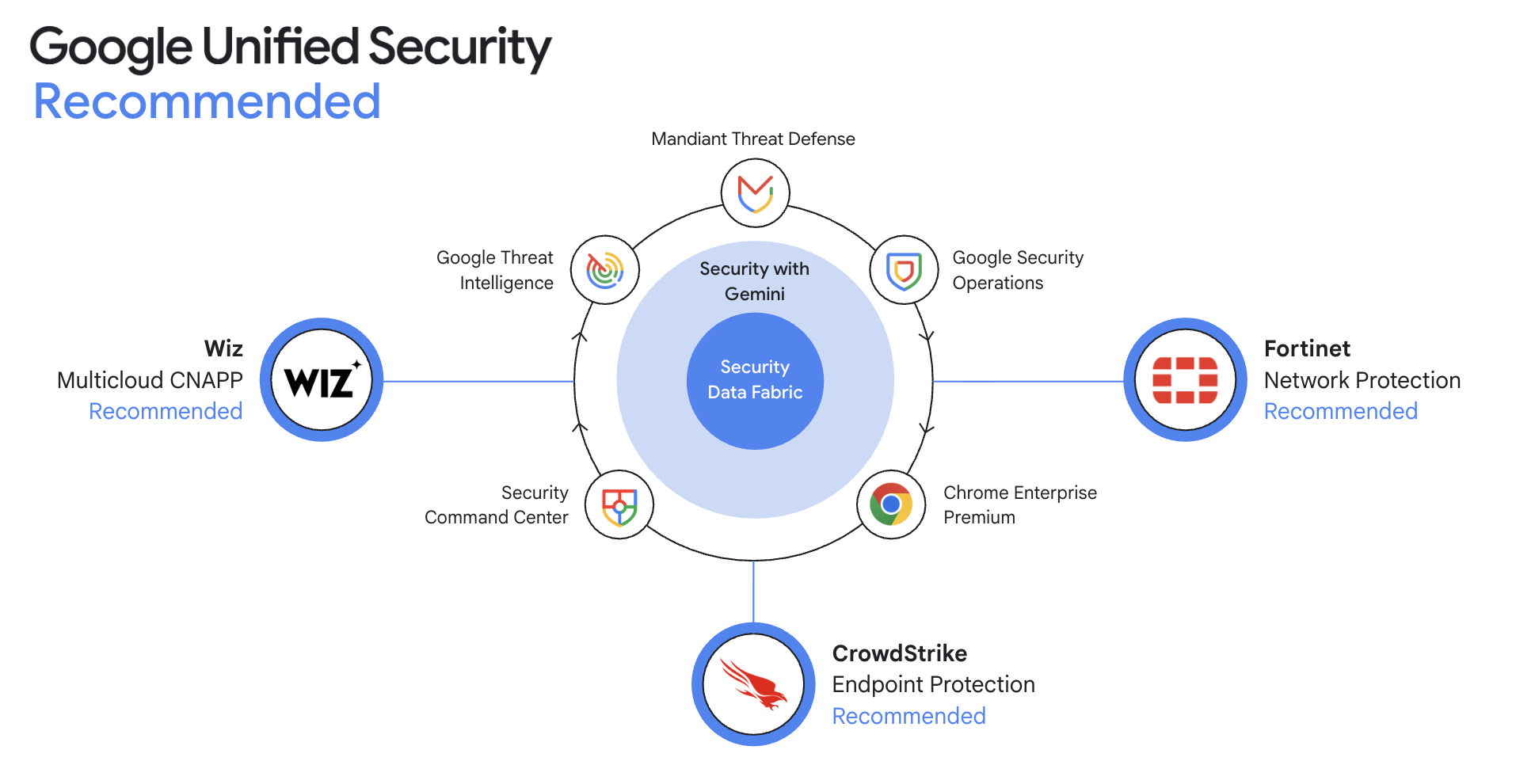
Google Unified Security Recommended
Google Unified Security Recommended establishes strategic partnerships to foster deep technical collaboration with market-leading security solutions trusted by our customers. Our recommended partner solutions represent a commitment to providing a best-in-class experience across our Google Unified Security portfolio, ensuring a unified defense for our shared customers.
Partners & integrations
Google Unified Security Recommended establishes strategic partnerships to foster deep technical collaboration with market-leading security solutions trusted by our customers. Our recommended partner solutions represent a commitment to providing a best-in-class experience across our Google Unified Security portfolio, ensuring a unified defense for our shared customers.
Pricing
| About Google Security Operations pricing | Google Security Operations is available in packages and based on ingestion. Includes one year of security telemetry retention at no additional cost. | |
|---|---|---|
| Package type | Features included | Pricing |
Standard | Base SIEM and SOAR capabilities Includes the core capabilities for data ingestion, threat detection, investigation and response with 12 months hot data retention, full access to our 700+ parsers and 300+ SOAR integrations and 1 environment with remote agent. The detection engine for this package supports up to 1,000 single-event and 75 multi-event rules. Choose a subset of Curated Detection rules. Threat intelligence Bring your own threat intelligence feeds. Data pipeline management Includes limited filtering and transformations. | Contact sales for pricing |
Enterprise | Includes everything in the Standard package plus: Base SIEM and SOAR capabilities Expanded support to unlimited environments with remote agent and a detection engine that supports up to 2,000 single-event and 125 multi-event rules. UEBA Use YARA-L to create rules for your own user and entity behavior analytics, plus get a risk dashboard and out of the box user and entity behavior-style detections. Threat intelligence Adds curation of enriched open source intelligence that can be used for filtering, detections, investigation context and retro-hunts. Enriched open source intelligence includes Google Safe Browsing, remote access, Benign, and OSINT Threat Associations. Google curated detections Access out-of-the-box detections maintained by Google experts, covering on-prem and cloud threats. Gemini in security operations Take productivity to the next level with AI. Gemini in security operations provides natural language, an interactive investigation assistant, contextualized summaries, recommended response actions and detection and playbook creation. Data pipeline management Includes limited filtering and transformations. | Contact sales for pricing |
Enterprise Plus | Includes everything in the Enterprise package plus: Base SIEM and SOAR capabilities Expanded detection engine supporting up to 3,500 single-event rules and 200 multi-event rules. Applied threat intelligence Full access to Google Threat Intelligence (which includes Mandiant, VirusTotal, and Google threat intel) including intelligence gathered from active Mandiant incident response engagements. On top of the unique sources, Applied Threat Intelligence provides turnkey prioritization of IoC matches with ML-base prioritization that factors in each customer's unique environment. We will also go beyond IoCs to include TTPs in understanding how an adversary behaves and operates. Google curated detections Additional access to emerging threat detections based on Mandiant's primary research and frontline threats seen in active incident response engagements. Data pipeline management Includes advanced filtering, redaction, transformations, and routing to Google. Additionally, 12 months of routing to another destination for SIEM migrations is included. BigQuery UDM storage Free storage for BigQuery exports for Google SecOps data up to your retention period (12 months by default). | Contact sales for pricing |
About Google Security Operations pricing
Google Security Operations is available in packages and based on ingestion. Includes one year of security telemetry retention at no additional cost.
Standard
Base SIEM and SOAR capabilities
Includes the core capabilities for data ingestion, threat detection, investigation and response with 12 months hot data retention, full access to our 700+ parsers and 300+ SOAR integrations and 1 environment with remote agent.
The detection engine for this package supports up to 1,000 single-event and 75 multi-event rules. Choose a subset of Curated Detection rules.
Threat intelligence
Bring your own threat intelligence feeds.
Data pipeline management
Includes limited filtering and transformations.
Contact sales for pricing
Enterprise
Includes everything in the Standard package plus:
Base SIEM and SOAR capabilities
Expanded support to unlimited environments with remote agent and a detection engine that supports up to 2,000 single-event and 125 multi-event rules.
UEBA
Use YARA-L to create rules for your own user and entity behavior analytics, plus get a risk dashboard and out of the box user and entity behavior-style detections.
Threat intelligence
Adds curation of enriched open source intelligence that can be used for filtering, detections, investigation context and retro-hunts. Enriched open source intelligence includes Google Safe Browsing, remote access, Benign, and OSINT Threat Associations.
Google curated detections
Access out-of-the-box detections maintained by Google experts, covering on-prem and cloud threats.
Gemini in security operations
Take productivity to the next level with AI. Gemini in security operations provides natural language, an interactive investigation assistant, contextualized summaries, recommended response actions and detection and playbook creation.
Data pipeline management
Includes limited filtering and transformations.
Contact sales for pricing
Enterprise Plus
Includes everything in the Enterprise package plus:
Base SIEM and SOAR capabilities
Expanded detection engine supporting up to 3,500 single-event rules and 200 multi-event rules.
Applied threat intelligence
Full access to Google Threat Intelligence (which includes Mandiant, VirusTotal, and Google threat intel) including intelligence gathered from active Mandiant incident response engagements.
On top of the unique sources, Applied Threat Intelligence provides turnkey prioritization of IoC matches with ML-base prioritization that factors in each customer's unique environment. We will also go beyond IoCs to include TTPs in understanding how an adversary behaves and operates.
Google curated detections
Additional access to emerging threat detections based on Mandiant's primary research and frontline threats seen in active incident response engagements.
Data pipeline management
Includes advanced filtering, redaction, transformations, and routing to Google. Additionally, 12 months of routing to another destination for SIEM migrations is included.
BigQuery UDM storage
Free storage for BigQuery exports for Google SecOps data up to your retention period (12 months by default).
Contact sales for pricing
Learn what Google Security Operations can do for you
Business Case
Explore how organizations like yours cut costs, increase ROI, and drive innovation with Google Security Operations
Forrester Consulting Study: Customers cite 240% ROI with Google Security Operations
CISO, Insurance company
"In simple terms, Google SecOps is a mass risk-reducer. Threats that would have impacted our business no longer do, because we have greater observability, better mean time to detect, and better mean time to respond."
Trusted and loved by security teams around the world
"With the traditional SIEM, it would typically take five to seven people with an environment our size. With Google Security Operations, we’re logging approximately 22 times the amount of data, we're seeing three times the events, and we're closing investigations in half the time." - Mike Orosz, CISO, Vertiv
"Historically, our legacy SIEM, we had to feed it a lot of the contextual enrichment and all of that threat intelligence stuff. It was data engineering to make it sing, where on the Google side, the product is more baked in, purpose-built for us to use it. It’s so intuitive and the speed was certainly really beneficial for us as well."- Mark Ruiz, Head of Cybersecurity Analytics, Pfizer
"When we moved to Google Security Operations, we were able to reduce the time to detect and time to investigate from 2 hours to about 15 to 30 minutes. No longer spending time in disparate tools but performing the job functions of a security operations analyst, it empowers them to work on more advanced workflows." - Hector Peña, Senior Director of Information Security, Apex FinTech Solutions
FAQ
Is Google Security Operations only relevant for Google Cloud?
No. Google SecOps ingests and analyzes security telemetry from across your environment, including on-premises and all major cloud providers, to help you detect, investigate and respond to cyberthreats across your organization. Check out the complete list of supported log types and parsers.
Can I bring my own threat intelligence feeds to Google Security Operations?
Yes. You can integrate any threat intelligence feeds with Google SecOps. Note that the automatic application of threat intelligence for threat detection is only supported for Google’s threat intelligence feeds.
Does Google Security Operations support data residency for specific regions?
Yes. The full list of available regions can be found here.
Does Google SecOps include AI?
Yes. We leverage AI to supercharge productivity including: the ability to use natural language to search your data, iterate, and drill down. Gemini generates underlying queries and presents full mapped syntax; the ability to investigate more efficiently with AI-generated summaries of what’s happening in cases, along with recommendations on how to respond; and the ability to interact with Google SecOps using a context-aware AI-powered chat, including the ability to create detections and playbooks.
Does Google SecOps include SIEM capabilities?
Yes. Google SecOps includes SIEM (Security Information and Event Management), SOAR (Security Orchestration, Automation, and Response), and applied threat intelligence capabilities.
Does Google have experts who can help me transform my cyber defense program with Google SecOps?
Yes. Mandiant experts can deliver personalized guidance and program management tailored to your needs to help you transform your cyber defense program with Google SecOps. Learn more here.