This page describes how to use ingress settings to restrict network access to your Cloud Run service.
At a network level, a Cloud Run service's endpoint is reachable from the following network ingress paths:
- Default
run.appURLs, which you can disable - Any configured domain mapping
- Any configured External Application Load Balancer or Internal Application Load Balancer
All network ingress paths are subject to the service's ingress setting. The default ingress paths and ingress setting allow any resource on the internet to reach your Cloud Run service. You can use a custom constraint to restrict ingress settings for your organization or for a set of projects. IAM authentication still applies to requests reaching the service endpoints from any of the preceding network ingress paths. For a layered approach to managing access, use both network ingress settings and IAM authentication.
Use network tags to restrict connector VM access to VPC resources.
Available network ingress settings
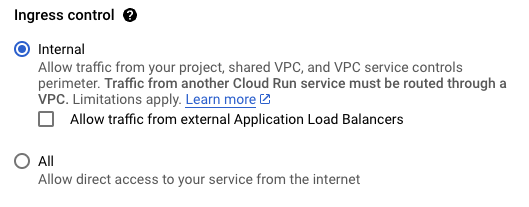
The following settings are available:
| Setting | Description |
|---|---|
| Internal |
Most restrictive. Allows requests from the following sources:
run.app URL. Requests
from other sources, including the internet, cannot reach your service at
the run.app URL or custom domains. |
| Internal and Cloud Load Balancing | This setting allows requests from the following resources:
Note: To enable this setting in the gcloud CLI, use internal-and-cloud-load-balancing.
To enable this setting in the Google Cloud console, select
Internal > Allow traffic from external Application Load Balancers.
|
| All |
Least restrictive. Allows all requests, including requests directly from
the internet to the run.app URL.
|
Access internal services
The following additional considerations apply:
When accessing internal services, call them as you would normally do using their URL, either the default
run.appURL or a custom domain set up in Cloud Run.For requests from Compute Engine VM instances, no further setup is required for machines that have external IP addresses or that use Cloud NAT. Otherwise, see Receive requests from VPC networks.
When calling from Cloud Run or App Engine to a Cloud Run service that's set to "Internal" or "Internal and Cloud Load Balancing", traffic must route through a VPC network that's considered internal. See Receive requests from other Cloud Run services or App Engine.
Requests from resources within VPC networks in the same project are "internal" even if the resource that they originate from has an external IP address.
Requests from on-premises resources connected to the VPC network using Cloud VPN and Cloud Interconnect are "internal."
Set ingress
You can set ingress by using the Google Cloud console, Google Cloud CLI, YAML, or Terraform.
Console
In the Google Cloud console, go to the Cloud Run page:
If you are configuring a new service, select Services from the menu, and click Deploy container to display the Create service form. Fill out the initial service settings page.
If you are configuring an existing service, click the service, and then click the Networking tab.
Select the ingress traffic you want to allow:
Click Create or Save.
gcloud
If you are deploying a new service, deploy your service with the
--ingressflag:gcloud run deploy SERVICE --image IMAGE_URL --ingress INGRESS
Replace the following:
INGRESS: one of the available ingress settings:allinternalinternal-and-cloud-load-balancing
SERVICE: your service name- IMAGE_URL: a reference to the container image, for
example,
us-docker.pkg.dev/cloudrun/container/hello:latest. If you use Artifact Registry, the repository REPO_NAME must already be created. The URL follows the format ofLOCATION-docker.pkg.dev/PROJECT_ID/REPO_NAME/PATH:TAG.
If you are changing an existing service ingress:
gcloud run services update SERVICE --ingress INGRESS
Replace the following:
INGRESS: one of the available ingress settings:allinternalinternal-and-cloud-load-balancing
SERVICE: your service name
YAML
If you are creating a new service, skip this step. If you are updating an existing service, download its YAML configuration:
gcloud run services describe SERVICE --format export > service.yaml
Update the
run.googleapis.com/ingress:annotation:apiVersion: serving.knative.dev/v1 kind: Service metadata: annotations: run.googleapis.com/ingress: INGRESS name: SERVICE spec: template: metadata: name: REVISION
Replace the following:
- SERVICE: the name of your Cloud Run
- INGRESS: one of the
available ingress settings:
allinternalinternal-and-cloud-load-balancing
- REVISION with a new revision name or delete it (if present). If you supply a new revision name, it must meet the following criteria:
- Starts with
SERVICE- - Contains only lowercase letters, numbers and
- - Does not end with a
- - Does not exceed 63 characters
- Starts with
Replace the service with its new configuration using the following command:
gcloud run services replace service.yaml
Terraform
To learn how to apply or remove a Terraform configuration, see Basic Terraform commands.
Add the following to agoogle_cloud_run_v2_service
resource in your Terraform configuration:Disable the default URL
Disable the default run.app URLs of a Cloud Run
service to only allow traffic from the service's other ingress paths:
Cloud Load Balancing and any configured domain mapping.
To disable the default URL, perform the following steps by using the Google Cloud console, Google Cloud CLI, YAML, or Terraform.
Console
In the Google Cloud console, go to the Cloud Run page:
Click an existing service.
Select the Networking tab.
In the Endpoints card, clear Enable under Default HTTPS endpoint URL.
Click Save.
To restore the default URL, select Enable and click Save.
gcloud
For an existing service, run the
gcloud run services updatecommand with the--no-default-urlflag, for example:gcloud run services update SERVICE_NAME --no-default-url
For a new service, run the
gcloud run deploycommand with the--no-default-urlflag, for example:gcloud run deploy SERVICE_NAME --no-default-url
where SERVICE_NAME is the name of your Cloud Run service.
In the output, the URL displays as
None.
To restore the default URL, use the --default-url flag.
YAML
If you are creating a new service, skip this step. If you are updating an existing service, download its YAML configuration:
gcloud run services describe SERVICE --format export > service.yaml
To disable the
run.appURL, use therun.googleapis.com/default-url-disabledannotation:apiVersion: serving.knative.dev/v1 kind: Service metadata: annotations: run.googleapis.com/default-url-disabled: true name: SERVICE spec: template: metadata: name: REVISION
Replace the following:
- SERVICE with the name of your Cloud Run service.
- REVISION with a new revision name or delete it (if present). If you supply a new revision name, it must meet the following criteria:
- Starts with
SERVICE- - Contains only lowercase letters, numbers and
- - Does not end with a
- - Does not exceed 63 characters
- Starts with
Create or update the service using the following command:
gcloud run services replace service.yaml
To restore the default URL, remove the run.googleapis.com/default-url-disabled
annotation.
Terraform
To learn how to apply or remove a Terraform configuration, see Basic Terraform commands.
Add the following to agoogle_cloud_run_v2_service
resource in your Terraform configuration: resource "google_cloud_run_v2_service" "disable_default_url_service" {
name = "cloudrun-service"
location = "europe-west1"
default_uri_disabled = true
template {
containers {
image = "us-docker.pkg.dev/cloudrun/container/hello"
}
annotations = {
"run.googleapis.com/ingress" = "all" # "all" or "internal-only"
}
}
}
Verify that the launch_stage and default_uri_disabled lines are in
your main.tf file. The preceding google_cloud_run_v2_service resource
specifies a Cloud Run service with the default URL disabled in
Preview.
To restore the default URL, remove the default_uri_disabled and
launch_stage arguments.
The following Google Cloud services are using the default run.app URL
to invoke Cloud Run. Disabling the default run.app URL prevents
these services from working as expected:
- The
cloudfunctions.netURL of Cloud Functions v2 API based on the Cloud Run service. - Cloud Scheduler
- Cloud Service Mesh
- Cloud Tasks
- Dialogflow CX
- Eventarc
- Firebase App Hosting
- Firebase Hosting
- Pub/Sub
- Synthetic monitors and uptime checks
- Workflows
What's next
- Learn about egress settings.
- Set up an internal Application Load Balancer for Cloud Run.
- Set up an external Application Load Balancer with Cloud Run.
- Configure IAM authentication methods for accessing services.
