Your job might require API keys, passwords, certificates, or other sensitive information for its dependencies. For Cloud Run, Google recommends storing this sensitive information in a secret you create in Secret Manager.
Make a secret available to your containers in one of the following ways:
- When you mount each secret as a volume, Cloud Run makes the secret available to the container as files. When reading a volume, Cloud Run always fetches the secret value from the Secret Manager to use the value with the latest version. This method also works well with secret rotation.
- Pass a secret using environment variables.
Environment variables are resolved at instance startup time, so if you use
this method, Google recommends that you pin the secret to a particular version
instead of using
latestas the version.
For more information, see Secret Manager best practices.
How secrets are checked at deployment and runtime
During job creation, Cloud Run checks all the secrets you use. The check ensures that the service account that runs the container has permission to access these secrets.
During runtime, when instances start up:
- If the secret is an environment variable, Cloud Run retrieves the value of the secret prior to starting the instance. If the secret retrieval process fails, the instance doesn't start.
- If you mount the secret as a volume, Cloud Run doesn't perform any checks during instance startup. However, during runtime, if a secret is inaccessible, attempts to read the mounted volume fail.
Volume ownership
The ownership of a Cloud Run secret volume differs by the execution environment and deployment type.
When you mount a secret volume using the second generation execution environment, which is always the case for job, root owns the volume.
Before you begin
-
Enable the Secret Manager API.
Roles required to enable APIs
To enable APIs, you need the Service Usage Admin IAM role (
roles/serviceusage.serviceUsageAdmin), which contains theserviceusage.services.enablepermission. Learn how to grant roles. - Use an existing secret or, create a secret in Secret Manager, as described in Create a secret.
Required roles
To get the permissions that you need to configure secrets, ask your administrator to grant you the following IAM roles:
-
Cloud Run Admin (
roles/run.admin) on the Cloud Run job -
Service Account User (
roles/iam.serviceAccountUser) on the service identity
To allow Cloud Run to access the secret, the service identity must have the following role:
- Secret Manager Secret Accessor (
roles/secretmanager.secretAccessor)
For instructions on how to add the service identity principal to the Secret Manager Secret Accessor role, see Manage access to secrets.
For a list of IAM roles and permissions that are associated with Cloud Run, see Cloud Run IAM roles and Cloud Run IAM permissions. If your Cloud Run job interfaces with Google Cloud APIs, such as Cloud Client Libraries, see the service identity configuration guide. For more information about granting roles, see deployment permissions and manage access.
Make a secret accessible to Cloud Run
You can make a secret accessible to your job using the Google Cloud console, the Google Cloud CLI, or YAML:
Console
In the Google Cloud console, go to the Cloud Run Jobs page:
Click Deploy container to fill out the initial job settings page. If you are configuring an existing job, select the job, then click View and edit job configuration.
Click Container(s), Volumes, Connections, Security to expand the job properties page.
Click the Variables & Secrets tab.
- In the Variables & Secrets tab:
To expose the secret as an environment variable:
- Click the Container(s) tab.
- In the Variables and Secrets tab, click Reference a secret.
- In the Name 1 field, enter the name of the environment variable.
- From the Secret list, select the secret you want to use.
- From the Version 1 list, select the version of the secret to reference.
- Click Done.
- Click Create or Deploy.
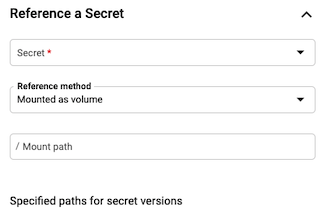
To mount secret as a volume:
- Click the Volumes tab and select Add volume.
- In the Volume type list, select Secret.
- In the Volume name field, enter a name or accept the default name.
- From the Secret list, select the secret you want to use.
- In the Path 1 field, enter the name of the file to mount.
- In the Version 1 list, select the version of the secret to reference. By default, the latest version is selected. You can select a specific version if you want.
- Click Done.
- Navigate to the Container(s) tab to mount your secret to the container.
- In the Volume mounts tab, and click Mount volume.
- From the Name 1 list, select your volume name.
- In the Mount path 1 field, enter the mount path for this secret. This is the directory where all versions of your secret are placed.
- Click Done.
- Click Create or Deploy.
- In the Variables & Secrets tab:
Click Create or Update.
gcloud
To specify the secret in an environment variable when creating a new job:
gcloud run jobs create JOB_NAME \ --image IMAGE_URL \ --set-secrets ENV_VAR_NAME=SECRET_NAME:VERSION
Replace the following:
- JOB_NAME: the name of your job.
- ENV_VAR_NAME: the name of the environment variable to use for the secret.
- SECRET_NAME: the secret name in the same project—for
example,
mysecret. - VERSION: the secret version. Use
latestfor latest version, or a number—for example,2. - IMAGE_URL: a reference to the
container image—for
example,
us-docker.pkg.dev/cloudrun/container/job:latest.
You can specify several environment variable/secret pairs, using a comma delimited list.
To specify the secret in an environment variable when updating a job:
gcloud run jobs update JOB_NAME \ --set-secrets ENV_VAR_NAME=SECRET_NAME:VERSION
To mount the secret as a volume when creating a job:
gcloud run jobs create JOB_NAME \ --image IMAGE_URL \ --set-secrets=PATH=SECRET_NAME:VERSION
Replace the following:
- JOB_NAME: the name of your job.
- IMAGE_URL: a reference to the
container image—for
example,
us-docker.pkg.dev/cloudrun/container/job:latest. - PATH: the mount path of the volume and
filename of the secret. It must start with a leading slash—for example,
/etc/secrets/dbconfig/password, where/etc/secrets/dbconfig/is the mount path of the volume, andpasswordis the filename of the secret. - SECRET_NAME: the secret name in the same project—for
example,
mysecret. - VERSION: the secret version. Use
latestfor latest version, or a number—for example,2.
To update a secret in an existing job:
gcloud run jobs update JOB_NAME \ --update-secrets=PATH=SECRET_NAME:VERSION
YAML
Due to constraints around API compatibility, the secret locations must be stored in an annotation.
If you are creating a new job, skip this step. If you are updating an existing job, download its YAML configuration:
gcloud run jobs describe JOB_NAME --format export > job.yaml
For secrets exposed as environment variables:
apiVersion: run.googleapis.com/v1 kind: Job metadata: name: JOB spec: template: spec: template: spec: containers: - env: - name: SECRET_NAME valueFrom: secretKeyRef: key: VERSION name: SECRET_LOOKUP_NAME image: IMAGE_URL
Replace the following:
- JOB: the name of your job.
- IMAGE_URL: a reference to the
container image—for
example,
us-docker.pkg.dev/cloudrun/container/job:latest. - SECRET_NAME: the secret name—for example,
mysecret. - VERSION: the secret version. Use
latestfor latest version, or a number—for example,2. - SECRET_LOOKUP_NAME: any name that has a
valid secret name syntax—for example,
my-secret. It can be the same as SECRET_NAME.
For secrets mounted as file paths:
apiVersion: run.googleapis.com/v1 kind: Job metadata: name: JOB_NAME spec: template: spec: template: spec: containers: - image: IMAGE_URL volumeMounts: - mountPath: MOUNT_PATH name: VOLUME_NAME volumes: - name: VOLUME_NAME secret: items: - key: VERSION path: FILENAME secretName: SECRET_LOOKUP_NAME
Replace the following:
- JOB_NAME: the name of your job.
- IMAGE_URL: a reference to the
container image—for
example,
us-docker.pkg.dev/cloudrun/container/job:latest. - PATH: the mount path of the volume and
filename of the secret. It must start with a leading slash—for example,
/etc/secrets/dbconfig/password, where/etc/secrets/dbconfig/is the mount path of the volume, andpasswordis the filename of the secret. - PROJECT_NUMBER: the project number for the project the secret was created in.
- SECRET_NAME: the secret name—for example,
mysecret. - VERSION: the secret version. Use
latestfor latest version, or a number—for example,2. - SECRET_LOOKUP_NAME: any name that has a
valid secret name syntax—for example,
my-secret. It can be the same as SECRET_NAME. - VOLUME_NAME: any name—for example,
my-volume. It can be the same as SECRET_NAME.
Terraform
To learn how to apply or remove a Terraform configuration, see Basic Terraform commands.
Add the following to agoogle_cloud_run_v2_job
resource in your Terraform configuration:For secrets exposed as environment variables:
resource "google_cloud_run_v2_job" "default" {
name = "JOB_NAME"
location = "REGION"
template {
template {
containers {
image = "IMAGE_URL"
env {
name = "SECRET_NAME"
value_source {
secret_key_ref {
secret = "SECRET_NAME"
version = "VERSION"
}
}
}
}
}
}
}
Replace the following:
- JOB_NAME: the name of your Cloud Run job.
- REGION: the Google Cloud region. For example,
europe-west1. - IMAGE_URL: a reference to the
container image—for
example,
us-docker.pkg.dev/cloudrun/container/job:latest. - SECRET_NAME: the secret name—for example,
mysecret. - VERSION: the secret version. Use
latestfor latest version, or a number—for example,2.
For secrets mounted as file paths:
resource "google_cloud_run_v2_job" "default" {
name = "JOB_NAME"
location = "REGION"
template {
template {
containers {
image = "IMAGE_URL"
volume_mounts {
name = "VOLUME_NAME"
mount_path = "MOUNT_PATH"
}
}
volumes {
name = "VOLUME_NAME"
secret {
secret = "SECRET_NAME"
}
}
}
}
}
Replace the following:
- JOB_NAME: the name of your Cloud Run job.
- REGION: the Google Cloud region. For example,
europe-west1. - IMAGE_URL: a reference to the
container image—for
example,
us-docker.pkg.dev/cloudrun/container/job:latest. - VOLUME_NAME: any name—for example,
my-volume. It can be the same asSECRET_NAME. - MOUNT_PATH: the mount path of the volume and
filename of the secret. It must start with a leading slash—for example,
/etc/secrets/dbconfig/password, where/etc/secrets/dbconfig/is the mount path of the volume, andpasswordis the filename of the secret. - SECRET_NAME: the secret name—for example,
mysecret.
Referencing secrets from other projects
You can reference a secret from another project, if your project's service account has been allowed to access the secret.
Console
In the Google Cloud console, go to the Cloud Run Jobs page:
Click Deploy container to fill out the initial job settings page. If you are configuring an existing job, select the job, then click View and edit job configuration.
Click Container(s), Volumes, Connections, Security to expand the job properties page.
Click the Variables & Secrets tab.
- In the Variables & Secrets tab:
To expose the secret as an environment variable:
- Click the Container(s) tab.
- In the Variables and Secrets tab, click Reference a secret.
- In the Name 1 field, enter the name of the environment variable.
- From the Secret list, click Enter secret manually.
Enter the secret's resource ID in the following format:
projects/PROJECT_NUMBER/secrets/SECRET_NAMEReplace the following:
PROJECT_NUMBER with your Google Cloud project number. For detailed instructions on how to find your project number, see Creating and managing projects.
SECRET_NAME: The name of the secret in Secret Manager.
From the Version 1 list, select the version of the secret to reference.
Click Done.
Click Create or Deploy.
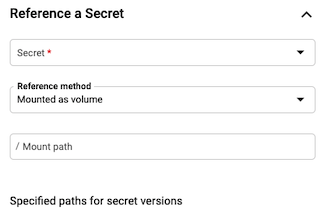
To mount secret as a volume:
- Click the Volumes tab and select Add volume.
- In the Volume type list, select Secret.
- In the Volume name field, enter a name or accept the default name.
- From the Secret list, click Enter secret manually.
Enter the secret's resource ID in the following format:
projects/PROJECT_NUMBER/secrets/SECRET_NAMEReplace the following:
PROJECT_NUMBER with your Google Cloud project number. For detailed instructions on how to find your project number, see Creating and managing projects.
SECRET_NAME: The name of the secret in Secret Manager.
In the Path 1 field, enter the name of the file to mount.
In the Version 1 list, select the version of the secret to reference. By default, the latest version is selected. You can select a specific version if you want.
Click Done.
Navigate to the Container(s) tab to mount your secret to the container.
In the Volume mounts tab, and click Mount volume.
From the Name 1 list, select your volume name.
In the Mount path 1 field, enter the mount path for this secret. This is the directory where all versions of your secret are placed.
Click Done.
Click Create or Deploy.
- In the Variables & Secrets tab:
Click Create or Update.
gcloud
To mount a secret as a volume when updating a job:
gcloud run jobs update JOB_NAME \ --image IMAGE_URL \ --update-secrets=PATH=projects/PROJECT_NUMBER/secrets/SECRET_NAME:VERSION
- JOB_NAME: the name of your job.
- IMAGE_URL: a reference to the
container image—for
example,
us-docker.pkg.dev/cloudrun/container/job:latest. - PATH: the mount path of the volume and
filename of the secret. It must start with a leading slash—for example,
/etc/secrets/dbconfig/password, where/etc/secrets/dbconfig/is the mount path of the volume, andpasswordis the filename of the secret. - PROJECT_NUMBER: the project number for the project the secret was created in.
- SECRET_NAME: the secret name—for example,
mysecret. - VERSION: the secret version. Use
latestfor latest version, or a number—for example,2.
YAML
If you are creating a new job, skip this step. If you are updating an existing job, download its YAML configuration:
gcloud run jobs describe JOB_NAME --format export > job.yaml
Due to constraints around API compatibility, the secret locations must be stored in an annotation.
For secrets exposed as environment variables:
apiVersion: run.googleapis.com/v1 kind: Job metadata: name: JOB spec: template: metadata: annotations: run.googleapis.com/secrets: SECRET_LOOKUP_NAME:projects/PROJECT_NUMBER/secrets/SECRET_NAME spec: template: spec: containers: - env: - name: SECRET_NAME valueFrom: secretKeyRef: key: VERSION name: SECRET_LOOKUP_NAME image: IMAGE_URL
Replace the following:
- JOB: the name of your job.
- IMAGE_URL: a reference to the
container image—for
example,
us-docker.pkg.dev/cloudrun/container/job:latest. - SECRET_NAME: the secret name—for example,
mysecret. - VERSION: the secret version. Use
latestfor latest version, or a number—for example,2. - PROJECT_NUMBER: the project number for the project the secret was created in.
- SECRET_LOOKUP_NAME: any name that has a
valid secret name syntax—for example,
my-secret. It can be the same as SECRET_NAME.
For secrets mounted as file paths:
apiVersion: run.googleapis.com/v1 kind: Job metadata: name: JOB_NAME spec: template: metadata: annotations: run.googleapis.com/secrets: SECRET_LOOKUP_NAME:projects/PROJECT_NUMBER/secrets/SECRET_NAME spec: template: spec: containers: - image: IMAGE_URL volumeMounts: - mountPath: MOUNT_PATH name: VOLUME_NAME volumes: - name: VOLUME_NAME secret: items: - key: VERSION path: FILENAME secretName: SECRET_LOOKUP_NAME
Replace the following:
- JOB_NAME: the name of your job.
- IMAGE_URL: a reference to the
container image—for
example,
us-docker.pkg.dev/cloudrun/container/job:latest. - PATH: the mount path of the volume and
filename of the secret. It must start with a leading slash—for example,
/etc/secrets/dbconfig/password, where/etc/secrets/dbconfig/is the mount path of the volume, andpasswordis the filename of the secret. - PROJECT_NUMBER: the project number for the project the secret was created in.
- SECRET_NAME: the secret name—for example,
mysecret. - VERSION: the secret version. Use
latestfor latest version, or a number—for example,2. - SECRET_LOOKUP_NAME: any name that has a
valid secret name syntax—for example,
my-secret, it can be the same as SECRET_NAME. - VOLUME_NAME: any name—for example,
my-volume, it can be the same as SECRET_NAME.
Terraform
To learn how to apply or remove a Terraform configuration, see Basic Terraform commands.
Add the following to agoogle_cloud_run_v2_job
resource in your Terraform configuration:For secrets exposed as environment variables:
resource "google_cloud_run_v2_job" "default" {
name = "JOB_NAME"
location = "REGION"
template {
template {
containers {
image = "IMAGE_URL"
env {
name = "SECRET_NAME"
value_source {
secret_key_ref {
secret = "projects/PROJECT_ID/secrets/SECRET_NAME"
version = "VERSION"
}
}
}
}
}
}
}
Replace the following:
- JOB_NAME: the name of your Cloud Run job.
- REGION: the Google Cloud region. For example,
europe-west1. - IMAGE_URL: a reference to the
container image—for
example,
us-docker.pkg.dev/cloudrun/container/job:latest. - SECRET_NAME: the secret name—for example,
mysecret. - PROJECT_ID: the project ID the secret was created in.
- VERSION: the secret version. Use
latestfor latest version, or a number—for example,2.
For secrets mounted as file paths:
resource "google_cloud_run_v2_job" "default" {
name = "JOB_NAME"
location = "REGION"
template {
template {
containers {
image = "IMAGE_URL"
volume_mounts {
name = "VOLUME_NAME"
mount_path = "MOUNT_PATH"
}
}
volumes {
name = "VOLUME_NAME"
secret {
secret = "projects/PROJECT_ID/secrets/SECRET_NAME"
}
}
}
}
}
Replace the following:
- JOB_NAME: the name of your Cloud Run job.
- REGION: the Google Cloud region—for example,
europe-west1. - IMAGE_URL: a reference to the
container image—for
example,
us-docker.pkg.dev/cloudrun/container/job:latest. - VOLUME_NAME: any name—for example,
my-volume, it can be the same asSECRET_NAME. - MOUNT_PATH: the mount path of the volume and
filename of the secret. It must start with a leading slash—for example,
/etc/secrets/dbconfig/password, where/etc/secrets/dbconfig/is the mount path of the volume, andpasswordis the filename of the secret. - PROJECT_ID: the project ID the secret was created in.
- SECRET_NAME: the secret name—for example,
mysecret.
View secrets settings
To view the current secrets settings for your Cloud Run job:
Console
In the Google Cloud console, go to the Cloud Run jobs page:
Click the job you are interested in to open the Job details page.
Click View and Edit job configuration.
Locate the secrets setting in the configuration details.
gcloud
Use the following command:
gcloud run jobs describe JOB_NAME
Locate the secrets setting in the returned configuration.
Disallowed paths and limitations
The following limitations apply to mounting secrets:
- Cloud Run doesn't allow you to mount secrets at
/dev,/procand/sys, or on their subdirectories. - Cloud Run doesn't allow you to mount multiple secrets at the same path because two volume mounts can't be mounted at the same location.
Overriding a directory
If the secret is mounted as a volume in Cloud Run, and the last directory in the volume mount path already exists, then any files or folders in the existing directory become inaccessible.
For example, if a secret called my-secret is mounted to path
/etc/app_data, all the contents inside the app_data directory will be
overwritten, and the only visible file is /etc/app_data/my-secret.
To avoid overwriting files in an existing directory, create a new directory for
mounting the secret, for example, /etc/app_data/secrets, so that the mount
path for the secret is /etc/app_data/secrets/my-secret.
