Questa pagina descrive come eseguire il deployment delle risorse di Kubernetes Gateway per il bilanciamento del carico del traffico in entrata su più cluster (o flotte) di Google Kubernetes Engine (GKE). Prima di eseguire il deployment di gateway multi-cluster, consulta la sezione Attivazione di gateway multi-cluster per preparare l'ambiente.
Per il deployment dei gateway per bilanciare il carico del traffico in entrata in un singolo cluster GKE, consulta Deployment dei gateway.
Gateway multi-cluster
Un gateway multi-cluster è una risorsa Gateway che bilancia il carico del traffico su più cluster Kubernetes. In GKE, gke-l7-cross-regional-internal-managed-mc, gke-l7-global-external-managed-mc,
gke-l7-regional-external-managed-mc, gke-l7-rilb-mc e gke-l7-gxlb-mc
GatewayClasses distribuiscono gateway multicluster che forniscono routing HTTP, suddivisione del traffico, mirroring del traffico, failover basato sullo stato e altro ancora in diversi cluster GKE, spazi dei nomi Kubernetes e in diverse regioni.
I gateway multi-cluster semplificano la gestione del networking delle applicazioni in più cluster
e team, rendendola facile, sicura e scalabile per gli amministratori dell'infrastruttura.
Questa pagina introduce tre esempi per insegnarti a eseguire il deployment di gateway multicluster utilizzando il controller GKE Gateway:
- Esempio 1: un gateway esterno multi-cluster che fornisce il bilanciamento del carico su due cluster GKE per il traffico internet.
- Esempio 2: un gateway cross-region privato di livello 7.
- Esempio 3: suddivisione del traffico basata sul peso e mirroring del traffico blu/verde in due cluster GKE per il traffico VPC interno.
- Esempio 4: un gateway basato sulla capacità per bilanciare il carico delle richieste a diversi backend in base alla loro capacità massima.
Ciascuno degli esempi utilizzerà le stesse applicazioni store e site per modellare uno scenario reale in cui un servizio di shopping online e un servizio di siti web sono di proprietà e gestiti da team separati e vengono implementati in un parco risorse di cluster GKE condivisi. Ciascuno degli esempi mette in evidenza topologie e casi d'uso diversi abilitati dai gateway multicluster.
I gateway multicluster richiedono una preparazione dell'ambiente prima di poter essere implementati. Prima di procedere, segui i passaggi descritti in Attivazione di gateway multi-cluster:
Esegui il deployment dei cluster GKE.
Registra i cluster in un parco risorse.
Abilita i controller del servizio multi-cluster e del gateway multi-cluster.
Infine, esamina le limitazioni e i problemi noti del controller GKE Gateway prima di utilizzarlo nel tuo ambiente.
Gateway esterno multi-cluster e multiregionale
In questo tutorial creerai un gateway multi-cluster esterno che gestisce il traffico esterno in un'applicazione in esecuzione in due cluster GKE.
Nei seguenti passaggi:
- Esegui il deployment dell'applicazione
storedi esempio nei clustergke-west-1egke-east-1. - Configura i servizi su ogni cluster da esportare nel tuo parco risorse (servizi multi-cluster).
- Esegui il deployment di un gateway multicluster esterno e di un HTTPRoute
nel cluster di configurazione (
gke-west-1).
Dopo il deployment delle risorse dell'applicazione e del gateway, puoi controllare il traffico nei due cluster GKE utilizzando il routing basato sul percorso:
- Le richieste a
/westvengono instradate ai podstorenel clustergke-west-1. - Le richieste a
/eastvengono instradate ai podstorenel clustergke-east-1. - Le richieste a qualsiasi altro percorso vengono indirizzate a uno dei due cluster, in base alla sua integrità, capacità e vicinanza al client richiedente.
Deployment dell'applicazione demo
Crea il deployment e lo spazio dei nomi
storein tutti e tre i cluster di cui è stato eseguito il deployment in Attivazione di gateway multi-cluster:kubectl apply --context gke-west-1 -f https://raw.githubusercontent.com/GoogleCloudPlatform/gke-networking-recipes/main/gateway/gke-gateway-controller/multi-cluster-gateway/store.yaml kubectl apply --context gke-west-2 -f https://raw.githubusercontent.com/GoogleCloudPlatform/gke-networking-recipes/main/gateway/gke-gateway-controller/multi-cluster-gateway/store.yaml kubectl apply --context gke-east-1 -f https://raw.githubusercontent.com/GoogleCloudPlatform/gke-networking-recipes/main/gateway/gke-gateway-controller/multi-cluster-gateway/store.yamlVengono eseguite le seguenti operazioni:
namespace/store created deployment.apps/store createdTutti gli esempi in questa pagina utilizzano l'app di cui è stato eseguito il deployment in questo passaggio. Assicurati che l'app venga eseguita il deployment in tutti e tre i cluster prima di provare uno dei passaggi rimanenti. Questo esempio utilizza solo i cluster
gke-west-1egke-east-1, mentregke-west-2viene utilizzato in un altro esempio.
Servizi multi-cluster
I servizi sono il modo in cui i pod vengono esposti ai client. Poiché il controller Gateway GKE utilizza il bilanciamento del carico nativo del container, non utilizza ClusterIP o il bilanciamento del carico Kubernetes per raggiungere i pod. Il traffico viene inviato direttamente dal bilanciatore del carico agli indirizzi IP dei pod. Tuttavia, i servizi svolgono ancora un ruolo fondamentale come identificatore logico per il raggruppamento dei pod.
Multi-cluster Services (MCS) è uno standard API per i servizi che si estendono ai cluster e il relativo controller GKE fornisce Service Discovery nei cluster GKE. Il controller Gateway multi-cluster utilizza le risorse API MCS per raggruppare i pod in un servizio indirizzabile su più cluster.
L'API multi-cluster Services definisce le seguenti risorse personalizzate:
- Le ServiceExports vengono mappate a un servizio Kubernetes, esportando gli endpoint di quel servizio in tutti i cluster registrati nel parco risorse. Quando un servizio ha un ServiceExport corrispondente, significa che il servizio può essere indirizzato da un gateway multi-cluster.
- ServiceImports vengono generati automaticamente dal controller del servizio multi-cluster. ServiceExport e ServiceImport sono in coppia. Se esiste un ServiceExport nel parco risorse, viene creato un ServiceImport corrispondente per consentire l'accesso al servizio mappato a ServiceExport da tutti i cluster.
L'esportazione dei servizi funziona nel seguente modo. Esiste un servizio di archiviazione in
gke-west-1 che seleziona un gruppo di pod in quel cluster. Un ServiceExport viene creato nel cluster, il che consente ai pod in gke-west-1 di diventare accessibili dagli altri cluster nel parco risorse. ServiceExport verrà mappato ed esporrà
i servizi che hanno lo stesso nome e spazio dei nomi della risorsa ServiceExport.
apiVersion: v1
kind: Service
metadata:
name: store
namespace: store
spec:
selector:
app: store
ports:
- port: 8080
targetPort: 8080
---
kind: ServiceExport
apiVersion: net.gke.io/v1
metadata:
name: store
namespace: store
Il seguente diagramma mostra cosa succede dopo il deployment di un ServiceExport. Se esiste una coppia ServiceExport e Service, il controller del servizio multi-cluster esegue il deployment di un ServiceImport corrispondente in ogni cluster GKE del parco risorse. ServiceImport è la rappresentazione locale del servizio store in ogni cluster. In questo modo, il pod client in gke-east-1 può utilizzare ClusterIP o
servizi headless per raggiungere i pod store in gke-west-1. Se utilizzati in questo modo, i servizi multicluster forniscono il bilanciamento del carico est-ovest tra i cluster senza richiedere un servizio LoadBalancer interno.
Per utilizzare i servizi multi-cluster per il bilanciamento del carico da cluster a cluster, consulta
Configurazione dei servizi multi-cluster.
I gateway multi-cluster utilizzano anche ServiceImport, ma non per il bilanciamento del carico da cluster a cluster. I gateway utilizzano invece ServiceImport come identificatori logici per un servizio che esiste in un altro cluster o che si estende su più cluster. La seguente HTTPRoute fa riferimento a un ServiceImport anziché a una risorsa Service. Il riferimento a un ServiceImport indica che il traffico viene inoltrato a un gruppo di pod di backend che vengono eseguiti su uno o più cluster.
kind: HTTPRoute
apiVersion: gateway.networking.k8s.io/v1
metadata:
name: store-route
namespace: store
labels:
gateway: multi-cluster-gateway
spec:
parentRefs:
- kind: Gateway
namespace: store
name: external-http
hostnames:
- "store.example.com"
rules:
- backendRefs:
- group: net.gke.io
kind: ServiceImport
name: store
port: 8080
Il seguente diagramma mostra come HTTPRoute indirizza il traffico store.example.com ai pod store su gke-west-1 e gke-east-1. Il bilanciatore del carico li tratta come un unico
pool di backend. Se i pod di uno dei cluster non sono integri, non sono raggiungibili o non hanno capacità di traffico, il carico di traffico viene bilanciato sui pod rimanenti dell'altro cluster. È possibile aggiungere o rimuovere nuovi cluster con
il servizio store e ServiceExport. In questo modo, i pod di backend vengono aggiunti o rimossi
in modo trasparente senza modifiche esplicite alla configurazione del routing.
Servizi di esportazione
A questo punto, l'applicazione è in esecuzione su entrambi i cluster. Successivamente, esporrai ed esporterai le applicazioni eseguendo il deployment di servizi e ServiceExport in ogni cluster.
Applica il seguente manifest al cluster
gke-west-1per creare i servizi e le esportazioni di servizistoreestore-west-1:cat << EOF | kubectl apply --context gke-west-1 -f - apiVersion: v1 kind: Service metadata: name: store namespace: store spec: selector: app: store ports: - port: 8080 targetPort: 8080 --- kind: ServiceExport apiVersion: net.gke.io/v1 metadata: name: store namespace: store --- apiVersion: v1 kind: Service metadata: name: store-west-1 namespace: store spec: selector: app: store ports: - port: 8080 targetPort: 8080 --- kind: ServiceExport apiVersion: net.gke.io/v1 metadata: name: store-west-1 namespace: store EOFApplica il seguente manifest al cluster
gke-east-1per creare i servizi e le esportazioni di servizistoreestore-east-1:cat << EOF | kubectl apply --context gke-east-1 -f - apiVersion: v1 kind: Service metadata: name: store namespace: store spec: selector: app: store ports: - port: 8080 targetPort: 8080 --- kind: ServiceExport apiVersion: net.gke.io/v1 metadata: name: store namespace: store --- apiVersion: v1 kind: Service metadata: name: store-east-1 namespace: store spec: selector: app: store ports: - port: 8080 targetPort: 8080 --- kind: ServiceExport apiVersion: net.gke.io/v1 metadata: name: store-east-1 namespace: store EOFVerifica che nei cluster siano stati creati i ServiceExport corretti.
kubectl get serviceexports --context CLUSTER_NAME --namespace storeSostituisci CLUSTER_NAME con
gke-west-1egke-east-1. L'output dovrebbe essere simile al seguente:# gke-west-1 NAME AGE store 2m40s store-west-1 2m40s # gke-east-1 NAME AGE store 2m25s store-east-1 2m25sCiò dimostra che il servizio
storecontienestorepod in entrambi i cluster, mentre i servizistore-west-1estore-east-1contengono solostorepod nei rispettivi cluster. Questi servizi sovrapposti vengono utilizzati per scegliere come target i pod in più cluster o un sottoinsieme di pod in un singolo cluster.Dopo qualche minuto, verifica che i
ServiceImportsassociati siano stati creati automaticamente dal controller multi-cluster Services in tutti i cluster del parco progetti.kubectl get serviceimports --context CLUSTER_NAME --namespace storeSostituisci CLUSTER_NAME con
gke-west-1egke-east-1. L'output dovrebbe essere simile al seguente:# gke-west-1 NAME TYPE IP AGE store ClusterSetIP ["10.112.31.15"] 6m54s store-east-1 ClusterSetIP ["10.112.26.235"] 5m49s store-west-1 ClusterSetIP ["10.112.16.112"] 6m54s # gke-east-1 NAME TYPE IP AGE store ClusterSetIP ["10.72.28.226"] 5d10h store-east-1 ClusterSetIP ["10.72.19.177"] 5d10h store-west-1 ClusterSetIP ["10.72.28.68"] 4h32mCiò dimostra che tutti e tre i servizi sono accessibili da entrambi i cluster nel parco risorse. Tuttavia, poiché esiste un solo cluster di configurazione attivo per flotta, puoi eseguire il deployment solo di gateway e HTTPRoute che fanno riferimento a questi ServiceImport in
gke-west-1. Quando un HTTPRoute nel cluster di configurazione fa riferimento a questi ServiceImport come backend, il gateway può inoltrare il traffico a questi servizi indipendentemente dal cluster da cui vengono esportati.
Deployment del gateway e di HTTPRoute
Una volta eseguito il deployment delle applicazioni, puoi configurare un gateway utilizzando
la risorsa gke-l7-global-external-managed-mc GatewayClass. Questo gateway crea un bilanciatore del carico delle applicazioni esterno configurato per distribuire il traffico tra i cluster di destinazione.
Applica il seguente manifest
Gatewayal cluster di configurazione,gke-west-1in questo esempio:cat << EOF | kubectl apply --context gke-west-1 -f - kind: Gateway apiVersion: gateway.networking.k8s.io/v1 metadata: name: external-http namespace: store spec: gatewayClassName: gke-l7-global-external-managed-mc listeners: - name: http protocol: HTTP port: 80 allowedRoutes: kinds: - kind: HTTPRoute EOFQuesta configurazione del gateway esegue il deployment delle risorse del bilanciatore del carico delle applicazioni esterno con la seguente convenzione di denominazione:
gkemcg1-NAMESPACE-GATEWAY_NAME-HASH.Le risorse predefinite create con questa configurazione sono:
- 1 bilanciatore del carico:
gkemcg1-store-external-http-HASH - 1 indirizzo IP pubblico:
gkemcg1-store-external-http-HASH - 1 regola di forwarding:
gkemcg1-store-external-http-HASH - 2 servizi di backend:
- Servizio di backend 404 predefinito:
gkemcg1-store-gw-serve404-HASH - Servizio di backend predefinito 500:
gkemcg1-store-gw-serve500-HASH
- Servizio di backend 404 predefinito:
- 1 Controllo di integrità:
- Controllo di integrità 404 predefinito:
gkemcg1-store-gw-serve404-HASH
- Controllo di integrità 404 predefinito:
- 0 regole di routing (URLmap è vuota)
In questa fase, qualsiasi richiesta a GATEWAY_IP:80 risulterà in una pagina predefinita che mostra il seguente messaggio:
fault filter abort.- 1 bilanciatore del carico:
Applica il seguente manifest
HTTPRouteal cluster di configurazione,gke-west-1in questo esempio:cat << EOF | kubectl apply --context gke-west-1 -f - kind: HTTPRoute apiVersion: gateway.networking.k8s.io/v1 metadata: name: public-store-route namespace: store labels: gateway: external-http spec: hostnames: - "store.example.com" parentRefs: - name: external-http rules: - matches: - path: type: PathPrefix value: /west backendRefs: - group: net.gke.io kind: ServiceImport name: store-west-1 port: 8080 - matches: - path: type: PathPrefix value: /east backendRefs: - group: net.gke.io kind: ServiceImport name: store-east-1 port: 8080 - backendRefs: - group: net.gke.io kind: ServiceImport name: store port: 8080 EOFIn questa fase, qualsiasi richiesta a GATEWAY_IP:80 risulterà in una pagina predefinita che mostra il seguente messaggio:
fault filter abort.Una volta implementata, questa HTTPRoute configurerà il seguente comportamento di routing:
- Le richieste a
/westvengono instradate ai podstorenel clustergke-west-1, perché i pod selezionati da ServiceExportstore-west-1esistono solo nel clustergke-west-1. - Le richieste a
/eastvengono instradate ai podstorenel clustergke-east-1, perché i pod selezionati da ServiceExportstore-east-1esistono solo nel clustergke-east-1. - Le richieste a qualsiasi altro percorso vengono indirizzate ai pod
storein uno dei due cluster, in base alla loro integrità, capacità e vicinanza al client richiedente. - Le richieste a GATEWAY_IP:80 restituiranno una
pagina predefinita che mostra il seguente messaggio:
fault filter abort.
Tieni presente che se tutti i pod di un determinato cluster non sono integri (o non esistono), il traffico verso il servizio
storeverrà inviato solo ai cluster che hanno effettivamente podstore. L'esistenza di un ServiceExport e di un Service su un determinato cluster non garantisce che il traffico verrà inviato a quel cluster. I pod devono esistere e rispondere in modo affermativo al controllo di integrità del bilanciatore del carico, altrimenti il bilanciatore del carico invierà il traffico solo ai podstoreintegri in altri cluster.Le nuove risorse vengono create con questa configurazione:
- 3 servizi di backend:
- Il servizio di backend
store:gkemcg1-store-store-8080-HASH - Il servizio di backend
store-east-1:gkemcg1-store-store-east-1-8080-HASH - Il servizio di backend
store-west-1:gkemcg1-store-store-west-1-8080-HASH
- Il servizio di backend
- 3 controlli di integrità:
- Controllo di integrità di
store:gkemcg1-store-store-8080-HASH - Controllo di integrità di
store-east-1:gkemcg1-store-store-east-1-8080-HASH - Controllo di integrità di
store-west-1:gkemcg1-store-store-west-1-8080-HASH
- Controllo di integrità di
- 1 regola di routing in URLmap:
- La regola di routing
store.example.com: - 1 host:
store.example.com - Più
matchRulesper il routing ai nuovi servizi di backend
- La regola di routing
- Le richieste a
Il seguente diagramma mostra le risorse che hai eseguito il deployment in entrambi i cluster.
Poiché gke-west-1 è il cluster di configurazione del gateway, è il cluster in cui il controller del gateway monitora il gateway, le HTTPRoute e le ServiceImport. Ogni cluster ha un ServiceImport store e un altro ServiceImport specifico per quel cluster. Entrambi puntano agli stessi pod. In questo modo, HTTPRoute può specificare esattamente dove deve andare il traffico: ai pod store su un cluster specifico o ai pod store su tutti i cluster.
Tieni presente che si tratta di un modello di risorse logiche, non di una rappresentazione del flusso di traffico. Il percorso del traffico va direttamente dal bilanciatore del carico ai pod di backend e non ha alcuna relazione diretta con il cluster di configurazione.
Convalida del deployment
Ora puoi inviare richieste al nostro gateway multicluster e distribuire il traffico su entrambi i cluster GKE.
Verifica che Gateway e HTTPRoute siano stati implementati correttamente esaminando lo stato e gli eventi di Gateway.
kubectl describe gateways.gateway.networking.k8s.io external-http --context gke-west-1 --namespace storeDovresti vedere un output simile al seguente:
Name: external-http Namespace: store Labels: <none> Annotations: networking.gke.io/addresses: /projects/PROJECT_NUMBER/global/addresses/gkemcg1-store-external-http-laup24msshu4 networking.gke.io/backend-services: /projects/PROJECT_NUMBER/global/backendServices/gkemcg1-store-gw-serve404-80-n65xmts4xvw2, /projects/PROJECT_NUMBER/global/backendServices/gke... networking.gke.io/firewalls: /projects/PROJECT_NUMBER/global/firewalls/gkemcg1-l7-default-global networking.gke.io/forwarding-rules: /projects/PROJECT_NUMBER/global/forwardingRules/gkemcg1-store-external-http-a5et3e3itxsv networking.gke.io/health-checks: /projects/PROJECT_NUMBER/global/healthChecks/gkemcg1-store-gw-serve404-80-n65xmts4xvw2, /projects/PROJECT_NUMBER/global/healthChecks/gkemcg1-s... networking.gke.io/last-reconcile-time: 2023-10-12T17:54:24Z networking.gke.io/ssl-certificates: networking.gke.io/target-http-proxies: /projects/PROJECT_NUMBER/global/targetHttpProxies/gkemcg1-store-external-http-94oqhkftu5yz networking.gke.io/target-https-proxies: networking.gke.io/url-maps: /projects/PROJECT_NUMBER/global/urlMaps/gkemcg1-store-external-http-94oqhkftu5yz API Version: gateway.networking.k8s.io/v1 Kind: Gateway Metadata: Creation Timestamp: 2023-10-12T06:59:32Z Finalizers: gateway.finalizer.networking.gke.io Generation: 1 Resource Version: 467057 UID: 1dcb188e-2917-404f-9945-5f3c2e907b4c Spec: Gateway Class Name: gke-l7-global-external-managed-mc Listeners: Allowed Routes: Kinds: Group: gateway.networking.k8s.io Kind: HTTPRoute Namespaces: From: Same Name: http Port: 80 Protocol: HTTP Status: Addresses: Type: IPAddress Value: 34.36.127.249 Conditions: Last Transition Time: 2023-10-12T07:00:41Z Message: The OSS Gateway API has deprecated this condition, do not depend on it. Observed Generation: 1 Reason: Scheduled Status: True Type: Scheduled Last Transition Time: 2023-10-12T07:00:41Z Message: Observed Generation: 1 Reason: Accepted Status: True Type: Accepted Last Transition Time: 2023-10-12T07:00:41Z Message: Observed Generation: 1 Reason: Programmed Status: True Type: Programmed Last Transition Time: 2023-10-12T07:00:41Z Message: The OSS Gateway API has altered the "Ready" condition semantics and reservedit for future use. GKE Gateway will stop emitting it in a future update, use "Programmed" instead. Observed Generation: 1 Reason: Ready Status: True Type: Ready Listeners: Attached Routes: 1 Conditions: Last Transition Time: 2023-10-12T07:00:41Z Message: Observed Generation: 1 Reason: Programmed Status: True Type: Programmed Last Transition Time: 2023-10-12T07:00:41Z Message: The OSS Gateway API has altered the "Ready" condition semantics and reservedit for future use. GKE Gateway will stop emitting it in a future update, use "Programmed" instead. Observed Generation: 1 Reason: Ready Status: True Type: Ready Name: http Supported Kinds: Group: gateway.networking.k8s.io Kind: HTTPRoute Events: Type Reason Age From Message ---- ------ ---- ---- ------- Normal UPDATE 35m (x4 over 10h) mc-gateway-controller store/external-http Normal SYNC 4m22s (x216 over 10h) mc-gateway-controller SYNC on store/external-http was a successUna volta eseguito il deployment del gateway, recupera l'indirizzo IP esterno dal gateway
external-http.kubectl get gateways.gateway.networking.k8s.io external-http -o=jsonpath="{.status.addresses[0].value}" --context gke-west-1 --namespace storeSostituisci
VIPnei passaggi successivi con l'indirizzo IP che ricevi come output.Inviare traffico al percorso principale del dominio. Questo bilancia il carico del traffico sul servizio
store, che si trova nel clustergke-west-1egke-east-1. Il bilanciatore del carico invia il traffico alla regione più vicina a te e potresti non visualizzare risposte dall'altra regione.curl -H "host: store.example.com" http://VIPL'output conferma che la richiesta è stata gestita dal pod del cluster
gke-east-1:{ "cluster_name": "gke-east-1", "zone": "us-east1-b", "host_header": "store.example.com", "node_name": "gke-gke-east-1-default-pool-7aa30992-t2lp.c.agmsb-k8s.internal", "pod_name": "store-5f5b954888-dg22z", "pod_name_emoji": "⏭", "project_id": "agmsb-k8s", "timestamp": "2021-06-01T17:32:51" }Poi invia il traffico al percorso
/west. In questo modo il traffico viene indirizzato al ServiceImportstore-west-1che ha solo pod in esecuzione sul clustergke-west-1. Un ServiceImport specifico per il cluster, comestore-west-1, consente al proprietario di un'applicazione di inviare esplicitamente il traffico a un cluster specifico, anziché lasciare che sia il bilanciatore del carico a prendere la decisione.curl -H "host: store.example.com" http://VIP/westL'output conferma che la richiesta è stata gestita dal pod del cluster
gke-west-1:{ "cluster_name": "gke-west-1", "zone": "us-west1-a", "host_header": "store.example.com", "node_name": "gke-gke-west-1-default-pool-65059399-2f41.c.agmsb-k8s.internal", "pod_name": "store-5f5b954888-d25m5", "pod_name_emoji": "🍾", "project_id": "agmsb-k8s", "timestamp": "2021-06-01T17:39:15", }Infine, invia traffico al percorso
/east.curl -H "host: store.example.com" http://VIP/eastL'output conferma che la richiesta è stata gestita dal pod del cluster
gke-east-1:{ "cluster_name": "gke-east-1", "zone": "us-east1-b", "host_header": "store.example.com", "node_name": "gke-gke-east-1-default-pool-7aa30992-7j7z.c.agmsb-k8s.internal", "pod_name": "store-5f5b954888-hz6mw", "pod_name_emoji": "🧜🏾", "project_id": "agmsb-k8s", "timestamp": "2021-06-01T17:40:48" }
Esegui il deployment di un gateway multi-cluster interno in più regioni
Puoi eseguire il deployment di gateway multi-cluster che forniscono il bilanciamento del carico interno di livello 7 nei cluster GKE in più regioni. Questi gateway utilizzano gke-l7-cross-regional-internal-managed-mc GatewayClass. Questa GatewayClass esegue il provisioning di un bilanciatore del carico delle applicazioni interno tra regioni gestito da Google Cloud e che abilita VIP interni a cui possono accedere i client all'interno della rete VPC. Questi gateway possono essere esposti dai frontend nelle regioni di tua scelta semplicemente utilizzando il gateway per richiedere indirizzi in queste regioni. Il VIP interno può essere un singolo indirizzo IP oppure indirizzi IP in più regioni, con un indirizzo IP per regione specificato nel gateway. Il traffico viene indirizzato al cluster GKE di backend integro più vicino in grado di gestire la richiesta.
Prima di iniziare
Configura il progetto e la shell impostando l'ambiente
gcloudcon l'ID progetto:export PROJECT_ID="YOUR_PROJECT_ID" gcloud config set project ${PROJECT_ID}Crea cluster GKE in regioni diverse.
Questo esempio utilizza due cluster:
gke-west-1inus-west1egke-east-1inus-east1. Assicurati che l'API Gateway sia abilitata (--gateway-api=standard) e che i cluster siano registrati in un parco risorse.gcloud container clusters create gke-west-1 \ --location=us-west1-a \ --workload-pool=${PROJECT_ID}.svc.id.goog \ --project=${PROJECT_ID} \ --enable-fleet \ --gateway-api=standard gcloud container clusters create gke-east-1 \ --location=us-east1-c \ --workload-pool=${PROJECT_ID}.svc.id.goog \ --project=${PROJECT_ID} \ --enable-fleet \ --gateway-api=standardRinomina i contesti per accedervi più facilmente:
gcloud container clusters get-credentials gke-west-1 \ --location=us-west1-a \ --project=${PROJECT_ID} gcloud container clusters get-credentials gke-east-1 \ --location=us-east1-c \ --project=${PROJECT_ID} kubectl config rename-context gke_${PROJECT_ID}_us-west1-a_gke-west-1 gke-west1 kubectl config rename-context gke_${PROJECT_ID}_us-east1-c_gke-east-1 gke-east1Abilita i servizi multi-cluster (MCS) e Ingress multi-cluster (MCI/gateway):
gcloud container fleet multi-cluster-services enable --project=${PROJECT_ID} # Set the config membership to one of your clusters (e.g., gke-west-1) # This cluster will be the source of truth for multi-cluster Gateway and Route resources. gcloud container fleet ingress enable \ --config-membership=projects/${PROJECT_ID}/locations/us-west1/memberships/gke-west-1 \ --project=${PROJECT_ID}Configura le subnet solo proxy. È necessaria una subnet solo proxy in ogni regione in cui si trovano i cluster GKE e in cui opererà il bilanciatore del carico. I bilanciatori del carico delle applicazioni interni tra regioni richiedono che lo scopo di questa subnet sia impostato su
GLOBAL_MANAGED_PROXY.# Proxy-only subnet for us-west1 gcloud compute networks subnets create us-west1-proxy-only-subnet \ --purpose=GLOBAL_MANAGED_PROXY \ --role=ACTIVE \ --region=us-west1 \ --network=default \ --range=10.129.0.0/23 # Choose an appropriate unused CIDR range # Proxy-only subnet for us-east1 gcloud compute networks subnets create us-east1-proxy-only-subnet \ --purpose=GLOBAL_MANAGED_PROXY \ --role=ACTIVE \ --region=us-east1 \ --network=default \ --range=10.130.0.0/23 # Choose an appropriate unused CIDR rangeSe non utilizzi la rete predefinita, sostituisci
defaultcon il nome della tua rete VPC. Assicurati che gli intervalli CIDR siano univoci e non si sovrappongano.Esegui il deployment delle applicazioni demo, ad esempio
store, in entrambi i cluster. Il file di esempiostore.yamldigke-networking-recipescrea uno spazio dei nomistoree un deployment.kubectl apply --context gke-west1 -f https://raw.githubusercontent.com/GoogleCloudPlatform/gke-networking-recipes/main/gateway/gke-gateway-controller/multi-cluster-gateway/store.yaml kubectl apply --context gke-east1 -f https://raw.githubusercontent.com/GoogleCloudPlatform/gke-networking-recipes/main/gateway/gke-gateway-controller/multi-cluster-gateway/store.yamlEsporta i servizi da ogni cluster creando risorse
ServiceeServiceExportdi Kubernetes in ogni cluster, in modo che i servizi siano rilevabili in tutto il parco risorse. L'esempio seguente esporta un serviziostoregenerico e servizi specifici per regione (store-west-1,store-east-1) da ogni cluster, tutti all'interno dello spazio dei nomistore.Applica a
gke-west1:cat << EOF | kubectl apply --context gke-west1 -f - apiVersion: v1 kind: Service metadata: name: store namespace: store spec: selector: app: store ports: - port: 8080 targetPort: 8080 --- kind: ServiceExport apiVersion: net.gke.io/v1 metadata: name: store namespace: store --- apiVersion: v1 kind: Service metadata: name: store-west-1 # Specific to this cluster namespace: store spec: selector: app: store ports: - port: 8080 targetPort: 8080 --- kind: ServiceExport apiVersion: net.gke.io/v1 metadata: name: store-west-1 # Exporting the region-specific service namespace: store EOFApplica a
gke-east1:cat << EOF | kubectl apply --context gke-east1 -f - apiVersion: v1 kind: Service metadata: name: store namespace: store spec: selector: app: store ports: - port: 8080 targetPort: 8080 --- kind: ServiceExport apiVersion: net.gke.io/v1 metadata: name: store namespace: store --- apiVersion: v1 kind: Service metadata: name: store-east-1 # Specific to this cluster namespace: store spec: selector: app: store ports: - port: 8080 targetPort: 8080 --- kind: ServiceExport apiVersion: net.gke.io/v1 metadata: name: store-east-1 # Exporting the region-specific service namespace: store EOFControlla ServiceImports: Verifica che le risorse
ServiceImportsiano create in ogni cluster all'interno dello spazio dei nomistore. La loro creazione potrebbe richiedere alcuni minuti.bash kubectl get serviceimports --context gke-west1 -n store kubectl get serviceimports --context gke-east1 -n storeDovresti visualizzarestore,store-west-1estore-east-1(o le voci pertinenti in base alla propagazione).
Configura un gateway multiregionale interno
Definisci una risorsa Gateway che fa riferimento a GatewayClass gke-l7-cross-regional-internal-managed-mc. Applica questo manifest al cluster di configurazione designato, ad esempio gke-west-1.
Il campo spec.addresses consente di richiedere indirizzi IP temporanei in regioni specifiche o di utilizzare indirizzi IP statici preassegnati.
Per utilizzare gli indirizzi IP temporanei, salva il seguente manifest
Gatewaycomecross-regional-gateway.yaml:# cross-regional-gateway.yaml kind: Gateway apiVersion: gateway.networking.k8s.io/v1 metadata: name: internal-cross-region-gateway namespace: store # Namespace for the Gateway resource spec: gatewayClassName: gke-l7-cross-regional-internal-managed-mc addresses: # Addresses across regions. Address value is allowed to be empty or matching # the region name. - type: networking.gke.io/ephemeral-ipv4-address/us-west1 value: "us-west1" - type: networking.gke.io/ephemeral-ipv4-address/us-east1 value: "us-east1" listeners: - name: http protocol: HTTP port: 80 allowedRoutes: kinds: - kind: HTTPRoute # Only allow HTTPRoute to attachL'elenco seguente definisce alcuni dei campi nel file YAML precedente:
metadata.namespace: lo spazio dei nomi in cui viene creata la risorsa Gateway, ad esempiostore.spec.gatewayClassName: il nome di GatewayClass. Deve esseregke-l7-cross-regional-internal-managed-mc.spec.listeners.allowedRoutes.kinds: i tipi di oggetti Route che possono essere allegati, ad esempioHTTPRoute.spec.addresses:type: networking.gke.io/ephemeral-ipv4-address/REGION: richiede un indirizzo IP temporaneo.value: specifica la regione dell'indirizzo, ad esempio"us-west1"o"us-east1".
Applica il manifest al cluster di configurazione, ad esempio
gke-west1:kubectl apply --context gke-west1 -f cross-regional-gateway.yaml
Collega HTTPRoute al gateway
Definisci le risorse HTTPRoute per gestire il routing del traffico e applicale al cluster di configurazione.
Salva il seguente manifest
HTTPRoutecomestore-route.yaml:# store-route.yaml kind: HTTPRoute apiVersion: gateway.networking.k8s.io/v1 metadata: name: store-route namespace: store labels: gateway: cross-regional-internal spec: parentRefs: - name: internal-cross-region-gateway namespace: store # Namespace where the Gateway is deployed hostnames: - "store.example.internal" # Hostname clients will use rules: - matches: # Rule for traffic to /west - path: type: PathPrefix value: /west backendRefs: - group: net.gke.io # Indicates a multi-cluster ServiceImport kind: ServiceImport name: store-west-1 # Targets the ServiceImport for the west cluster port: 8080 - matches: # Rule for traffic to /east - path: type: PathPrefix value: /east backendRefs: - group: net.gke.io kind: ServiceImport name: store-east-1 # Targets the ServiceImport for the east cluster port: 8080 - backendRefs: # Default rule for other paths (e.g., /) - group: net.gke.io kind: ServiceImport name: store # Targets the generic 'store' ServiceImport (any region) port: 8080L'elenco seguente definisce alcuni dei campi nel file YAML precedente:
spec.parentRefs: collega questa route ainternal-cross-region-gatewaynello spazio dei nomistore.spec.hostnames: rappresenta il nome host utilizzato dai client per accedere al servizio.spec.rules: definisce la logica di routing. Questo esempio utilizza il routing basato su percorso:- Il traffico
/westva a ServiceImportstore-west-1. - Il traffico
/eastva a ServiceImportstore-east-1. - Tutto il resto del traffico, ad esempio
/, viene indirizzato all'importazione di servizistoregenerica.
- Il traffico
backendRefs:group: net.gke.ioekind: ServiceImporthanno come target i servizi multi-cluster.
Applica il manifest
HTTPRouteal cluster di configurazione:kubectl apply --context gke-west1 -f store-route.yaml
Verifica lo stato del gateway e della route
Controlla lo stato del gateway:
kubectl get gateway internal-cross-region-gateway -n store -o yaml --context gke-west1Cerca una condizione con stato
type:Programmatoand: "True". You should see IP addresses assigned in thestatus.addressesfield, corresponding to the regions you specified (e.g., one forus-west1and one forus-east1`).Controlla lo stato di HTTPRoute:
kubectl get httproute store-route -n store -o yaml --context gke-west1Cerca una condizione in
status.parents[].conditionscontype: Accepted(oResolvedRefs) estatus: "True".
Conferma il traffico
Dopo aver assegnato gli indirizzi IP al gateway, puoi testare il traffico da una VM client che si trova all'interno della rete VPC e in una delle regioni, o in una regione che può connettersi all'indirizzo IP del gateway.
Recupera gli indirizzi IP del gateway.
Il seguente comando tenta di analizzare l'output JSON. Potrebbe essere necessario modificare
jsonpathin base alla struttura esatta.kubectl get gateway cross-region-gateway -n store --context gke-west1 -o=jsonpath="{.status.addresses[*].value}".L'output di questo comando deve includere i VIP, ad esempio
VIP1_WESToVIP2_EAST.Invia richieste di test: Da una VM client nel tuo VPC:
# Assuming VIP_WEST is an IP in us-west1 and VIP_EAST is an IP in us-east1 # Traffic to /west should ideally be served by gke-west-1 curl -H "host: store.example.internal" http://VIP_WEST/west curl -H "host: store.example.internal" http://VIP_EAST/west # Still targets store-west-1 due to path # Traffic to /east should ideally be served by gke-east-1 curl -H "host: store.example.internal" http://VIP_WEST/east # Still targets store-east-1 due to path curl -H "host: store.example.internal" http://VIP_EAST/east # Traffic to / (default) could be served by either cluster curl -H "host: store.example.internal" http://VIP_WEST/ curl -H "host: store.example.internal" http://VIP_EAST/La risposta deve includere dettagli dell'applicazione
storeche indicano quale pod di backend ha gestito la richiesta, ad esempiocluster_nameozone.
Utilizza indirizzi IP statici
Anziché indirizzi IP temporanei, puoi utilizzare indirizzi IP interni statici preassegnati.
Crea indirizzi IP statici nelle regioni che vuoi utilizzare:
gcloud compute addresses create cross-region-gw-ip-west --region us-west1 --subnet default --project=${PROJECT_ID} gcloud compute addresses create cross-region-gw-ip-east --region us-east1 --subnet default --project=${PROJECT_ID}Se non utilizzi la subnet predefinita, sostituisci
defaultcon il nome della subnet che ha l'indirizzo IP che vuoi allocare. Queste subnet sono subnet normali, non le subnet solo proxy.Aggiorna il manifest del gateway modificando la sezione
spec.addressesnel filecross-regional-gateway.yaml:# cross-regional-gateway-static-ip.yaml kind: Gateway apiVersion: gateway.networking.k8s.io/v1 metadata: name: internal-cross-region-gateway # Or a new name if deploying alongside namespace: store spec: gatewayClassName: gke-l7-cross-regional-internal-managed-mc addresses: - type: networking.gke.io/named-address-with-region # Use for named static IP value: "regions/us-west1/addresses/cross-region-gw-ip-west" - type: networking.gke.io/named-address-with-region value: "regions/us-east1/addresses/cross-region-gw-ip-east" listeners: - name: http protocol: HTTP port: 80 allowedRoutes: kinds: - kind: HTTPRouteApplica il manifest del gateway aggiornato.
kubectl apply --context gke-west1 -f cross-regional-gateway.yaml
Considerazioni speciali per le subnet non predefinite
Tieni presenti le seguenti considerazioni quando utilizzi subnet non predefinite:
Stessa rete VPC:tutte le risorse create dall'utente, come indirizzi IP statici, subnet solo proxy e cluster GKE, devono risiedere nella stessa rete VPC.
Subnet di indirizzi:quando crei indirizzi IP statici per il gateway, questi vengono allocati dalle subnet regolari nelle regioni specificate.
Denominazione delle subnet del cluster:ogni regione deve avere una subnet con lo stesso nome della subnet in cui si trova il cluster di configurazione MCG.
- Ad esempio, se il cluster di configurazione
gke-west-1si trova inprojects/YOUR_PROJECT/regions/us-west1/subnetworks/my-custom-subnet, anche le regioni per cui richiedi gli indirizzi devono avere la subnetmy-custom-subnet. Se richiedi indirizzi nelle regionius-east1eus-centra1, deve esistere anche una subnet denominatamy-custom-subnetin queste regioni.
- Ad esempio, se il cluster di configurazione
Routing blu/verde multi-cluster con Gateway
Le GatewayClass gke-l7-global-external-managed-*, gke-l7-regional-external-managed-* e gke-l7-rilb-* hanno molte funzionalità avanzate di routing del traffico, tra cui suddivisione del traffico, corrispondenza delle intestazioni, manipolazione delle intestazioni, mirroring del traffico e altro ancora. In questo esempio, mostrerai come utilizzare la suddivisione del traffico basata sul peso per controllare esplicitamente la proporzione di traffico tra due cluster GKE.
Questo esempio illustra alcuni passaggi realistici che un proprietario del servizio eseguirebbe per spostare o espandere la propria applicazione in un nuovo cluster GKE. L'obiettivo dei deployment blu/verde è ridurre il rischio attraverso più passaggi di convalida che confermano il corretto funzionamento del nuovo cluster. Questo esempio illustra quattro fasi di deployment:
- 100% - Canary basato sull'intestazione: Utilizza il routing delle intestazioni HTTP per inviare solo traffico di test o sintetico al nuovo cluster.
- 100% - Traffico mirror: Duplica il traffico degli utenti nel cluster canary. In questo modo viene testata la capacità del cluster canary copiando il 100% del traffico utenti in questo cluster.
- 90%-10%: Canary a traffic split del 10% per esporre lentamente il nuovo cluster al traffico live.
- 0%-100%: Esegui il cutover completo al nuovo cluster con la possibilità di tornare indietro in caso di errori.
Questo esempio è simile al precedente, tranne per il fatto che viene eseguito il deployment di un gateway multicluster interno. Viene implementato un bilanciatore del carico delle applicazioni interno accessibile solo privatamente dall'interno del VPC. Utilizzerai i cluster e la stessa applicazione che hai eseguito il deployment nei passaggi precedenti, ma li eseguirai il deployment tramite un gateway diverso.
Prerequisiti
L'esempio seguente si basa su alcuni passaggi descritti in Deployment di un gateway multi-cluster esterno. Assicurati di aver completato i seguenti passaggi prima di procedere con questo esempio:
Deployment di un'applicazione demo
Questo esempio utilizza i cluster
gke-west-1egke-west-2che hai già configurato. Questi cluster si trovano nella stessa regione perchégke-l7-rilb-mcGatewayClass è regionale e supporta solo i backend dei cluster nella stessa regione.Esegui il deployment dei servizi e delle ServiceExport necessari su ogni cluster. Se hai eseguito il deployment di Services e ServiceExports dell'esempio precedente, hai già eseguito il deployment di alcuni di questi.
kubectl apply --context gke-west-1 -f https://raw.githubusercontent.com/GoogleCloudPlatform/gke-networking-recipes/main/gateway/gke-gateway-controller/multi-cluster-gateway/store-west-1-service.yaml kubectl apply --context gke-west-2 -f https://raw.githubusercontent.com/GoogleCloudPlatform/gke-networking-recipes/main/gateway/gke-gateway-controller/multi-cluster-gateway/store-west-2-service.yamlEsegue il deployment di un insieme simile di risorse in ogni cluster:
service/store created serviceexport.net.gke.io/store created service/store-west-2 created serviceexport.net.gke.io/store-west-2 created
Configurazione di una subnet solo proxy
Se non l'hai ancora fatto, configura una subnet solo proxy per ogni regione in cui stai eseguendo il deployment dei gateway interni. Questa subnet viene utilizzata
per fornire indirizzi IP interni ai proxy del bilanciatore del carico e deve essere
configurata con un --purpose impostato solo su REGIONAL_MANAGED_PROXY.
Prima di creare gateway che gestiscono bilanciatori del carico delle applicazioni interni, devi creare una subnet solo proxy. Ogni regione di una rete Virtual Private Cloud (VPC) in cui utilizzi i bilanciatori del carico delle applicazioni interni deve avere una subnet solo proxy.
Il comando gcloud compute networks subnets create
crea una subnet solo proxy.
gcloud compute networks subnets create SUBNET_NAME \
--purpose=REGIONAL_MANAGED_PROXY \
--role=ACTIVE \
--region=REGION \
--network=VPC_NETWORK_NAME \
--range=CIDR_RANGE
Sostituisci quanto segue:
SUBNET_NAME: il nome della subnet solo proxy.REGION: la regione della subnet solo proxy.VPC_NETWORK_NAME: il nome della rete VPC che contiene la subnet.CIDR_RANGE: l'intervallo di indirizzi IP principale della subnet. Devi utilizzare una subnet mask non superiore a/26in modo che siano disponibili almeno 64 indirizzi IP per i proxy nella regione. La subnet mask consigliata è/23.
Deployment del gateway
Il seguente gateway viene creato dalla GatewayClass gke-l7-rilb-mc, che è
un gateway interno regionale che può avere come target solo i cluster GKE nella
stessa regione.
Applica il seguente manifest
Gatewayal cluster di configurazione,gke-west-1in questo esempio:cat << EOF | kubectl apply --context gke-west-1 -f - kind: Gateway apiVersion: gateway.networking.k8s.io/v1 metadata: name: internal-http namespace: store spec: gatewayClassName: gke-l7-rilb-mc listeners: - name: http protocol: HTTP port: 80 allowedRoutes: kinds: - kind: HTTPRoute EOFVerifica che il gateway sia stato avviato correttamente. Puoi filtrare solo gli eventi di questo gateway con il seguente comando:
kubectl get events --field-selector involvedObject.kind=Gateway,involvedObject.name=internal-http --context=gke-west-1 --namespace storeIl deployment del gateway è riuscito se l'output è simile al seguente:
LAST SEEN TYPE REASON OBJECT MESSAGE 5m18s Normal ADD gateway/internal-http store/internal-http 3m44s Normal UPDATE gateway/internal-http store/internal-http 3m9s Normal SYNC gateway/internal-http SYNC on store/internal-http was a success
Canary basato sull'intestazione
Il canarying basato sull'intestazione consente al proprietario del servizio di abbinare il traffico di test sintetico che non proviene da utenti reali. Questo è un modo semplice per verificare che il networking di base dell'applicazione funzioni senza esporre direttamente gli utenti.
Applica il seguente manifest
HTTPRouteal cluster di configurazione,gke-west-1in questo esempio:cat << EOF | kubectl apply --context gke-west-1 -f - kind: HTTPRoute apiVersion: gateway.networking.k8s.io/v1 metadata: name: internal-store-route namespace: store labels: gateway: internal-http spec: parentRefs: - kind: Gateway namespace: store name: internal-http hostnames: - "store.example.internal" rules: # Matches for env=canary and sends it to store-west-2 ServiceImport - matches: - headers: - name: env value: canary backendRefs: - group: net.gke.io kind: ServiceImport name: store-west-2 port: 8080 # All other traffic goes to store-west-1 ServiceImport - backendRefs: - group: net.gke.io kind: ServiceImport name: store-west-1 port: 8080 EOFUna volta implementata, questa HTTPRoute configura il seguente comportamento di routing:
- Le richieste interne a
store.example.internalsenza l'intestazione HTTPenv: canaryvengono indirizzate ai podstoresul clustergke-west-1 - Le richieste interne a
store.example.internalcon l'intestazione HTTPenv: canaryvengono indirizzate ai podstoresul clustergke-west-2
Verifica che HTTPRoute funzioni correttamente inviando traffico all'indirizzo IP del gateway.
- Le richieste interne a
Recupera l'indirizzo IP interno da
internal-http.kubectl get gateways.gateway.networking.k8s.io internal-http -o=jsonpath="{.status.addresses[0].value}" --context gke-west-1 --namespace storeSostituisci VIP nei passaggi successivi con l'indirizzo IP che ricevi come output.
Invia una richiesta al gateway utilizzando l'intestazione HTTP
env: canary. In questo modo verificherai che il traffico venga indirizzato agke-west-2. Utilizza un client privato nello stesso VPC dei cluster GKE per verificare che le richieste vengano instradate correttamente. Il seguente comando deve essere eseguito su una macchina che abbia accesso privato all'indirizzo IP del gateway, altrimenti non funzionerà.curl -H "host: store.example.internal" -H "env: canary" http://VIPL'output conferma che la richiesta è stata gestita da un pod del cluster
gke-west-2:{ "cluster_name": "gke-west-2", "host_header": "store.example.internal", "node_name": "gke-gke-west-2-default-pool-4cde1f72-m82p.c.agmsb-k8s.internal", "pod_name": "store-5f5b954888-9kdb5", "pod_name_emoji": "😂", "project_id": "agmsb-k8s", "timestamp": "2021-05-31T01:21:55", "zone": "us-west1-a" }
Specchio stradale
Questa fase invia il traffico al cluster di destinazione, ma lo duplica anche nel cluster canary.
L'utilizzo del mirroring è utile per determinare in che modo il carico di traffico influirà sulle prestazioni dell'applicazione senza influire in alcun modo sulle risposte ai tuoi clienti. Potrebbe non essere necessario per tutti i tipi di implementazione, ma può essere utile quando si implementano modifiche di grandi dimensioni che potrebbero influire sul rendimento o sul carico.
Applica il seguente manifest
HTTPRouteal cluster di configurazione,gke-west-1in questo esempio:cat << EOF | kubectl apply --context gke-west-1 -f - kind: HTTPRoute apiVersion: gateway.networking.k8s.io/v1 metadata: name: internal-store-route namespace: store labels: gateway: internal-http spec: parentRefs: - kind: Gateway namespace: store name: internal-http hostnames: - "store.example.internal" rules: # Sends all traffic to store-west-1 ServiceImport - backendRefs: - name: store-west-1 group: net.gke.io kind: ServiceImport port: 8080 # Also mirrors all traffic to store-west-2 ServiceImport filters: - type: RequestMirror requestMirror: backendRef: group: net.gke.io kind: ServiceImport name: store-west-2 port: 8080 EOFUtilizzando il tuo client privato, invia una richiesta al gateway
internal-http. Utilizza il percorso/mirrorper identificare in modo univoco questa richiesta nei log dell'applicazione in un passaggio successivo.curl -H "host: store.example.internal" http://VIP/mirrorL'output conferma che il client ha ricevuto una risposta da un pod nel cluster
gke-west-1:{ "cluster_name": "gke-west-1", "host_header": "store.example.internal", "node_name": "gke-gke-west-1-default-pool-65059399-ssfq.c.agmsb-k8s.internal", "pod_name": "store-5f5b954888-brg5w", "pod_name_emoji": "🎖", "project_id": "agmsb-k8s", "timestamp": "2021-05-31T01:24:51", "zone": "us-west1-a" }Ciò conferma che il cluster primario risponde al traffico. Devi comunque confermare che il cluster a cui stai eseguendo la migrazione riceve il traffico mirroring.
Controlla i log dell'applicazione di un pod
storenel clustergke-west-2. I log devono confermare che il pod ha ricevuto il traffico sottoposto a mirroring dal bilanciamento del carico.kubectl logs deployment/store --context gke-west-2 -n store | grep /mirrorQuesto output conferma che anche i pod del cluster
gke-west-2ricevono le stesse richieste, ma le loro risposte a queste richieste non vengono inviate al client. Gli indirizzi IP visualizzati nei log sono gli indirizzi IP interni del bilanciatore del carico che comunicano con i tuoi pod.Found 2 pods, using pod/store-5c65bdf74f-vpqbs [2023-10-12 21:05:20,805] INFO in _internal: 192.168.21.3 - - [12/Oct/2023 21:05:20] "GET /mirror HTTP/1.1" 200 - [2023-10-12 21:05:27,158] INFO in _internal: 192.168.21.3 - - [12/Oct/2023 21:05:27] "GET /mirror HTTP/1.1" 200 - [2023-10-12 21:05:27,805] INFO in _internal: 192.168.21.3 - - [12/Oct/2023 21:05:27] "GET /mirror HTTP/1.1" 200 -
Suddivisione traffico
La suddivisione del traffico è uno dei metodi più comuni per implementare nuovo codice o eseguire il deployment in nuovi ambienti in modo sicuro. Il proprietario del servizio imposta una percentuale esplicita di traffico inviato ai backend canary, che in genere è una quantità molto piccola del traffico complessivo, in modo che il successo dell'implementazione possa essere determinato con un livello di rischio accettabile per le richieste degli utenti reali.
L'esecuzione di una suddivisione del traffico con una minoranza del traffico consente al proprietario del servizio di ispezionare l'integrità dell'applicazione e le risposte. Se tutti gli indicatori sembrano integri, possono procedere al cutover completo.
Applica il seguente manifest
HTTPRouteal cluster di configurazione,gke-west-1in questo esempio:cat << EOF | kubectl apply --context gke-west-1 -f - kind: HTTPRoute apiVersion: gateway.networking.k8s.io/v1 metadata: name: internal-store-route namespace: store labels: gateway: internal-http spec: parentRefs: - kind: Gateway namespace: store name: internal-http hostnames: - "store.example.internal" rules: - backendRefs: # 90% of traffic to store-west-1 ServiceImport - name: store-west-1 group: net.gke.io kind: ServiceImport port: 8080 weight: 90 # 10% of traffic to store-west-2 ServiceImport - name: store-west-2 group: net.gke.io kind: ServiceImport port: 8080 weight: 10 EOFUtilizzando il tuo client privato, invia una richiesta curl continua al gateway
internal- http.while true; do curl -H "host: store.example.internal" -s VIP | grep "cluster_name"; sleep 1; doneL'output sarà simile a questo, a indicare che si sta verificando una suddivisione del traffico 90/10.
"cluster_name": "gke-west-1", "cluster_name": "gke-west-1", "cluster_name": "gke-west-1", "cluster_name": "gke-west-1", "cluster_name": "gke-west-1", "cluster_name": "gke-west-1", "cluster_name": "gke-west-1", "cluster_name": "gke-west-1", "cluster_name": "gke-west-2", "cluster_name": "gke-west-1", "cluster_name": "gke-west-1", ...
Trasferimento del traffico
L'ultima fase della migrazione blu/verde consiste nel passare completamente al nuovo cluster e rimuovere quello precedente. Se il proprietario del servizio stava effettivamente eseguendo l'onboarding
di un secondo cluster in un cluster esistente, questo ultimo passaggio sarebbe diverso
in quanto il passaggio finale prevederebbe il traffico verso entrambi i cluster. In questo scenario, è consigliabile un singolo store ServiceImport con pod provenienti dai cluster gke-west-1 e gke-west-2. In questo modo, il bilanciatore del carico può decidere
dove deve andare il traffico per un'applicazione active-active, in base a prossimità, integrità e capacità.
Applica il seguente manifest
HTTPRouteal cluster di configurazione,gke-west-1in questo esempio:cat << EOF | kubectl apply --context gke-west-1 -f - kind: HTTPRoute apiVersion: gateway.networking.k8s.io/v1 metadata: name: internal-store-route namespace: store labels: gateway: internal-http spec: parentRefs: - kind: Gateway namespace: store name: internal-http hostnames: - "store.example.internal" rules: - backendRefs: # No traffic to the store-west-1 ServiceImport - name: store-west-1 group: net.gke.io kind: ServiceImport port: 8080 weight: 0 # All traffic to the store-west-2 ServiceImport - name: store-west-2 group: net.gke.io kind: ServiceImport port: 8080 weight: 100 EOFUtilizzando il tuo client privato, invia una richiesta curl continua al gateway
internal- http.while true; do curl -H "host: store.example.internal" -s VIP | grep "cluster_name"; sleep 1; doneL'output sarà simile a questo, a indicare che tutto il traffico ora è diretto a
gke-west-2."cluster_name": "gke-west-2", "cluster_name": "gke-west-2", "cluster_name": "gke-west-2", "cluster_name": "gke-west-2", ...
Questo passaggio finale completa una migrazione completa dell'applicazione blue-green da un cluster GKE a un altro cluster GKE.
Esegui il deployment del bilanciamento del carico basato sulla capacità
L'esercizio in questa sezione illustra i concetti di bilanciamento del carico globale e capacità del servizio eseguendo il deployment di un'applicazione in due cluster GKE in regioni diverse. Il traffico generato viene inviato a vari livelli di richieste al secondo (RPS) per mostrare come viene bilanciato il carico del traffico tra cluster e regioni.
Il seguente diagramma mostra la topologia che verrà implementata e come il traffico si riversa tra cluster e regioni quando ha superato la capacità del servizio:
Per saperne di più sulla gestione del traffico, consulta la sezione Gestione del traffico GKE.
prepara l'ambiente
Segui la procedura descritta in Attivazione di gateway multi-cluster per preparare l'ambiente.
Verifica che le risorse GatewayClass siano installate sul cluster di configurazione:
kubectl get gatewayclasses --context=gke-west-1L'output è simile al seguente:
NAME CONTROLLER ACCEPTED AGE gke-l7-global-external-managed networking.gke.io/gateway True 16h gke-l7-global-external-managed-mc networking.gke.io/gateway True 14h gke-l7-gxlb networking.gke.io/gateway True 16h gke-l7-gxlb-mc networking.gke.io/gateway True 14h gke-l7-regional-external-managed networking.gke.io/gateway True 16h gke-l7-regional-external-managed-mc networking.gke.io/gateway True 14h gke-l7-rilb networking.gke.io/gateway True 16h gke-l7-rilb-mc networking.gke.io/gateway True 14h
Esegui il deployment di un'applicazione
Esegui il deployment del server dell'applicazione web di esempio in entrambi i cluster:
kubectl apply --context gke-west-1 -f https://raw.githubusercontent.com/GoogleCloudPlatform/gke-networking-recipes/master/gateway/docs/store-traffic-deploy.yaml
kubectl apply --context gke-east-1 -f https://raw.githubusercontent.com/GoogleCloudPlatform/gke-networking-recipes/master/gateway/docs/store-traffic-deploy.yaml
L'output è simile al seguente:
namespace/store created
deployment.apps/store created
Esegui il deployment di un servizio, un gateway e un HTTPRoute
Applica il seguente manifest
Serviceai clustergke-west-1egke-east-1:cat << EOF | kubectl apply --context gke-west-1 -f - apiVersion: v1 kind: Service metadata: name: store namespace: traffic-test annotations: networking.gke.io/max-rate-per-endpoint: "10" spec: ports: - port: 8080 targetPort: 8080 name: http selector: app: store type: ClusterIP --- kind: ServiceExport apiVersion: net.gke.io/v1 metadata: name: store namespace: traffic-test EOFcat << EOF | kubectl apply --context gke-east-1 -f - apiVersion: v1 kind: Service metadata: name: store namespace: traffic-test annotations: networking.gke.io/max-rate-per-endpoint: "10" spec: ports: - port: 8080 targetPort: 8080 name: http selector: app: store type: ClusterIP --- kind: ServiceExport apiVersion: net.gke.io/v1 metadata: name: store namespace: traffic-test EOFIl servizio è annotato con
max-rate-per-endpointimpostato su 10 richieste al secondo. Con due repliche per cluster, ogni servizio ha una capacità di 20 RPS per cluster.Per maggiori informazioni su come scegliere un livello di capacità del servizio per il tuo servizio, consulta Determinare la capacità del servizio.
Applica il seguente manifest
Gatewayal cluster di configurazione,gke-west-1in questo esempio:cat << EOF | kubectl apply --context gke-west-1 -f - kind: Gateway apiVersion: gateway.networking.k8s.io/v1 metadata: name: store namespace: traffic-test spec: gatewayClassName: gke-l7-global-external-managed-mc listeners: - name: http protocol: HTTP port: 80 allowedRoutes: kinds: - kind: HTTPRoute EOFIl manifest descrive un gateway esterno, globale e multicluster che esegue il deployment di un bilanciatore del carico delle applicazioni esterno con un indirizzo IP accessibile pubblicamente.
Applica il seguente manifest
HTTPRouteal cluster di configurazione,gke-west-1in questo esempio:cat << EOF | kubectl apply --context gke-west-1 -f - kind: HTTPRoute apiVersion: gateway.networking.k8s.io/v1 metadata: name: store namespace: traffic-test labels: gateway: store spec: parentRefs: - kind: Gateway namespace: traffic-test name: store rules: - backendRefs: - name: store group: net.gke.io kind: ServiceImport port: 8080 EOFIl manifest descrive un HTTPRoute che configura il gateway con una regola di routing che indirizza tutto il traffico a ServiceImport store.
storeServiceImport raggruppa i pod di serviziostorein entrambi i cluster e consente al bilanciatore del carico di indirizzarli come un unico servizio.Puoi controllare gli eventi del gateway dopo qualche minuto per vedere se il deployment è stato completato:
kubectl describe gateway store -n traffic-test --context gke-west-1L'output è simile al seguente:
... Status: Addresses: Type: IPAddress Value: 34.102.159.147 Conditions: Last Transition Time: 2023-10-12T21:40:59Z Message: The OSS Gateway API has deprecated this condition, do not depend on it. Observed Generation: 1 Reason: Scheduled Status: True Type: Scheduled Last Transition Time: 2023-10-12T21:40:59Z Message: Observed Generation: 1 Reason: Accepted Status: True Type: Accepted Last Transition Time: 2023-10-12T21:40:59Z Message: Observed Generation: 1 Reason: Programmed Status: True Type: Programmed Last Transition Time: 2023-10-12T21:40:59Z Message: The OSS Gateway API has altered the "Ready" condition semantics and reservedit for future use. GKE Gateway will stop emitting it in a future update, use "Programmed" instead. Observed Generation: 1 Reason: Ready Status: True Type: Ready Listeners: Attached Routes: 1 Conditions: Last Transition Time: 2023-10-12T21:40:59Z Message: Observed Generation: 1 Reason: Programmed Status: True Type: Programmed Last Transition Time: 2023-10-12T21:40:59Z Message: The OSS Gateway API has altered the "Ready" condition semantics and reservedit for future use. GKE Gateway will stop emitting it in a future update, use "Programmed" instead. Observed Generation: 1 Reason: Ready Status: True Type: Ready Name: http Supported Kinds: Group: gateway.networking.k8s.io Kind: HTTPRoute Events: Type Reason Age From Message ---- ------ ---- ---- ------- Normal ADD 12m mc-gateway-controller traffic-test/store Normal SYNC 6m43s mc-gateway-controller traffic-test/store Normal UPDATE 5m40s (x4 over 12m) mc-gateway-controller traffic-test/store Normal SYNC 118s (x6 over 10m) mc-gateway-controller SYNC on traffic-test/store was a successQuesto output mostra che il gateway è stato eseguito il deployment correttamente. Potrebbero essere necessari alcuni minuti prima che il traffico inizi a passare dopo il deployment del gateway. Prendi nota dell'indirizzo IP in questo output, poiché viene utilizzato in un passaggio successivo.
Conferma il traffico
Verifica che il traffico venga trasmesso all'applicazione testando l'indirizzo IP del gateway con un comando curl:
curl GATEWAY_IP_ADDRESS
L'output è simile al seguente:
{
"cluster_name": "gke-west-1",
"host_header": "34.117.182.69",
"pod_name": "store-54785664b5-mxstv",
"pod_name_emoji": "👳🏿",
"project_id": "project",
"timestamp": "2021-11-01T14:06:38",
"zone": "us-west1-a"
}
Questo output mostra i metadati del pod, che indicano la regione da cui è stata gestita la richiesta.
Verifica il traffico utilizzando il test di carico
Per verificare che il bilanciatore del carico funzioni, puoi eseguire il deployment di un generatore di traffico nel tuo cluster gke-west-1. Il generatore di traffico genera traffico a diversi
livelli di carico per dimostrare la capacità e le funzionalità di overflow del bilanciatore del carico. I seguenti passaggi mostrano tre livelli di carico:
- 10 RPS, che rientrano nella capacità del servizio Store in
gke-west-1. - 30 RPS, che supera la capacità del servizio di negozio
gke-west-1e causa l'overflow del traffico agke-east-1. - 60 RPS, che supera la capacità dei servizi in entrambi i cluster.
Configura dashboard
Recupera il nome della mappa URL sottostante per il tuo gateway:
kubectl get gateway store -n traffic-test --context=gke-west-1 -o=jsonpath="{.metadata.annotations.networking\.gke\.io/url-maps}"L'output è simile al seguente:
/projects/PROJECT_NUMBER/global/urlMaps/gkemcg1-traffic-test-store-armvfyupay1tNella console Google Cloud , vai alla pagina Esplora metriche.
Vai a Esplora metriche
In Seleziona una metrica, fai clic su CODICE: MQL.
Inserisci la seguente query per osservare le metriche del traffico per il servizio del negozio nei due cluster:
fetch https_lb_rule | metric 'loadbalancing.googleapis.com/https/backend_request_count' | filter (resource.url_map_name == 'GATEWAY_URL_MAP') | align rate(1m) | every 1m | group_by [resource.backend_scope], [value_backend_request_count_aggregate: aggregate(value.backend_request_count)]Sostituisci
GATEWAY_URL_MAPcon il nome della mappa URL del passaggio precedente.Fai clic su Esegui query. Attendi almeno 5 minuti dopo aver eseguito il deployment del generatore di carico nella sezione successiva affinché le metriche vengano visualizzate nel grafico.
Test con 10 RPS
Esegui il deployment di un pod nel cluster
gke-west-1:kubectl run --context gke-west-1 -i --tty --rm loadgen \ --image=cyrilbkr/httperf \ --restart=Never \ -- /bin/sh -c 'httperf \ --server=GATEWAY_IP_ADDRESS \ --hog --uri="/zone" --port 80 --wsess=100000,1,1 --rate 10'Sostituisci
GATEWAY_IP_ADDRESScon l'indirizzo IP del gateway del passaggio precedente.L'output è simile al seguente, il che indica che il generatore di traffico sta inviando traffico:
If you don't see a command prompt, try pressing enter.Il generatore di carico invia continuamente 10 RPS al gateway. Anche se il traffico proviene dall'interno di una regione Google Cloud , il bilanciatore del carico lo tratta come traffico client proveniente dalla costa occidentale degli Stati Uniti. Per simulare una diversità realistica dei client, il generatore di carico invia ogni richiesta HTTP come una nuova connessione TCP, il che significa che il traffico viene distribuito in modo più uniforme tra i pod di backend.
Il generatore impiega fino a 5 minuti per generare traffico per la dashboard.
Visualizza la dashboard di Esplora metriche. Vengono visualizzate due linee che indicano la quantità di traffico bilanciato del carico in ciascun cluster:
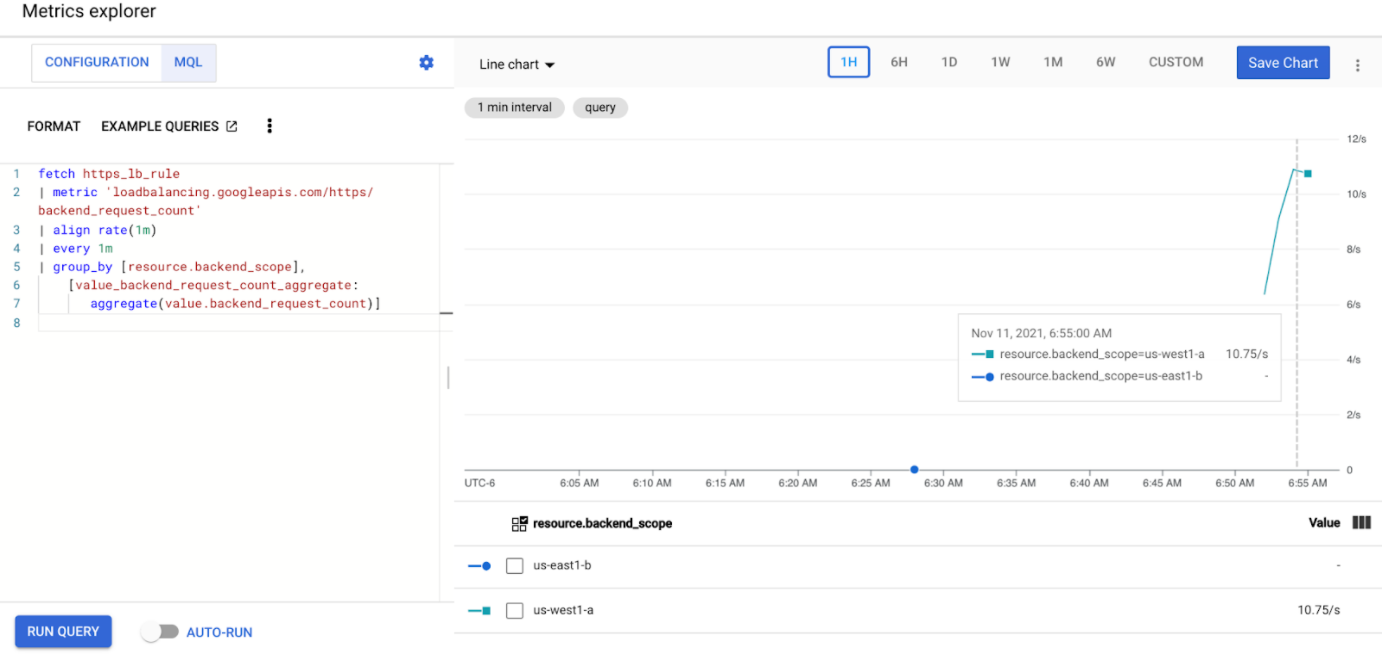
Dovresti vedere che
us-west1-ariceve circa 10 RPS di traffico mentreus-east1-bnon riceve traffico. Poiché il generatore di traffico è in esecuzione inus-west1, tutto il traffico viene inviato al servizio nel clustergke-west-1.Arresta il generatore di carico utilizzando Ctrl+C, quindi elimina il pod:
kubectl delete pod loadgen --context gke-west-1
Test con 30 RPS
Esegui di nuovo il deployment del generatore di carico, ma configurato per inviare 30 RPS:
kubectl run --context gke-west-1 -i --tty --rm loadgen \ --image=cyrilbkr/httperf \ --restart=Never \ -- /bin/sh -c 'httperf \ --server=GATEWAY_IP_ADDRESS \ --hog --uri="/zone" --port 80 --wsess=100000,1,1 --rate 30'Il generatore impiega fino a 5 minuti per generare traffico per la dashboard.
Visualizza la dashboard di Cloud Ops.
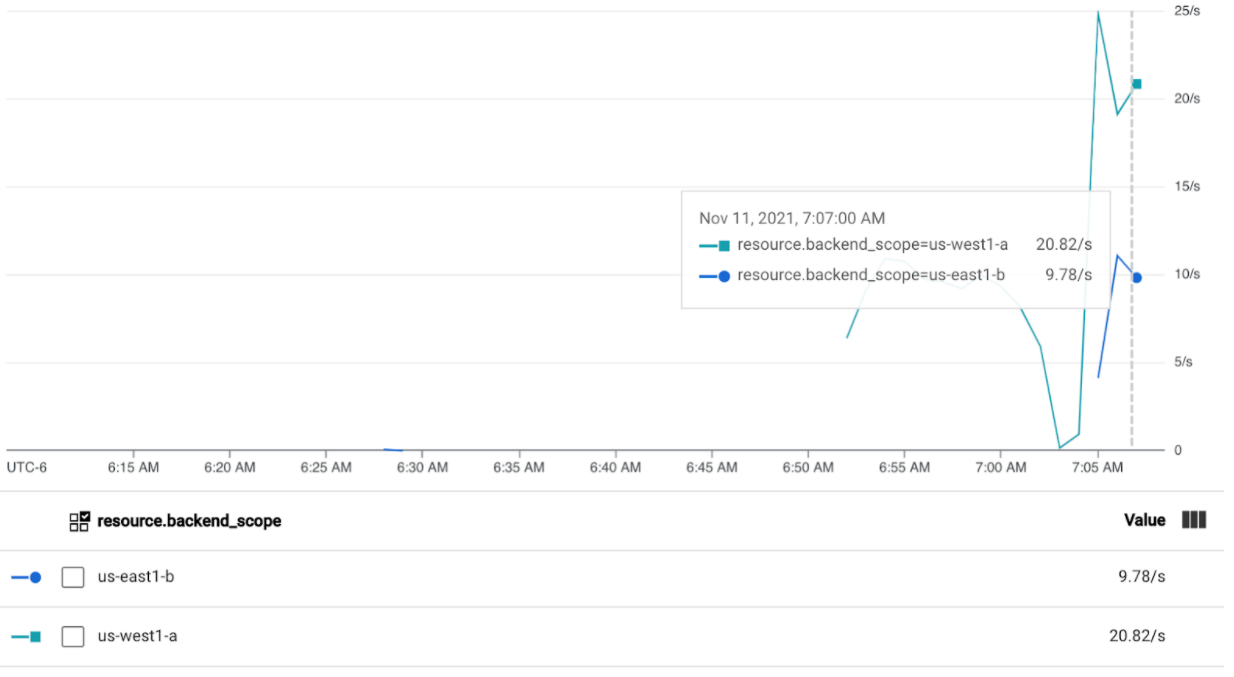
Dovresti vedere che vengono inviati circa 20 RPS a
us-west1-ae 10 RPS aus-east1-b. Ciò indica che il servizio ingke-west-1è utilizzato completamente e sta trasferendo 10 RPS di traffico al servizio ingke-east-1.Arresta il generatore di carico utilizzando Ctrl+C, quindi elimina il pod:
kubectl delete pod loadgen --context gke-west-1
Test con 60 RPS
Esegui il deployment del generatore di carico configurato per inviare 60 RPS:
kubectl run --context gke-west-1 -i --tty --rm loadgen \ --image=cyrilbkr/httperf \ --restart=Never \ -- /bin/sh -c 'httperf \ --server=GATEWAY_IP_ADDRESS \ --hog --uri="/zone" --port 80 --wsess=100000,1,1 --rate 60'Attendi 5 minuti e visualizza la dashboard di Cloud Ops. Ora dovrebbe mostrare che entrambi i cluster ricevono circa 30 RPS. Poiché tutti i servizi sono sovrautilizzati a livello globale, non si verifica un overflow del traffico e i servizi assorbono tutto il traffico possibile.

Arresta il generatore di carico utilizzando Ctrl+C, quindi elimina il pod:
kubectl delete pod loadgen --context gke-west-1
Esegui la pulizia
Dopo aver completato gli esercizi in questa pagina, segui questi passaggi per rimuovere le risorse ed evitare addebiti indesiderati sul tuo account:
Annulla la registrazione dei cluster dal parco risorse se non devono essere registrati per un altro scopo.
Disattiva la funzionalità
multiclusterservicediscovery:gcloud container fleet multi-cluster-services disableDisabilita Ingress multi-cluster:
gcloud container fleet ingress disableDisabilita le API:
gcloud services disable \ multiclusterservicediscovery.googleapis.com \ multiclusteringress.googleapis.com \ trafficdirector.googleapis.com \ --project=PROJECT_ID
Utilizzare il gateway multi-cluster con VPC condiviso
Un gateway multi-cluster può essere implementato anche in un ambiente VPC condiviso, con topologie diverse, a seconda del caso d'uso.
La tabella seguente descrive le topologie multi-cluster Gateway supportate in un ambiente VPC condiviso:
| Scenario | Progetto host del parco risorse | Configura cluster | Cluster di workload |
|---|---|---|---|
| 1 | Progetto host VPC condiviso | Progetto host VPC condiviso | Progetto host VPC condiviso |
| 2 | Progetto di servizio del VPC condiviso | Progetto di servizio del VPC condiviso (uguale al progetto di servizio del parco risorse) |
Progetto di servizio del VPC condiviso (uguale al progetto di servizio del parco risorse) |
Per creare gateway multi-cluster in un ambiente VPC condiviso, segui questi passaggi:
Segui i passaggi per configurare i servizi multi-cluster con VPC condiviso
Crea i servizi ed esportali nel cluster di configurazione
Se prevedi di utilizzare un gateway interno multi-cluster, crea una subnet solo proxy.
Crea il tuo Gateway e le tue HTTPRoute esterni o interni multi-cluster
Una volta completati questi passaggi, puoi convalidare il deployment, a seconda della topologia.
Risoluzione dei problemi
La subnet solo proxy per il gateway interno non esiste
Se sul gateway interno viene visualizzato il seguente evento, non esiste una subnet solo proxy per quella regione. Per risolvere il problema, esegui il deployment di una subnet solo proxy.
generic::invalid_argument: error ensuring load balancer: Insert: Invalid value for field 'resource.target': 'regions/us-west1/targetHttpProxies/gkegw-x5vt-default-internal-http-2jzr7e3xclhj'. A reserved and active subnetwork is required in the same region and VPC as the forwarding rule.
Nessun upstream integro
Sintomo:
Quando crei un gateway, ma non riesci ad accedere ai servizi di backend (codice di risposta 503), potrebbe verificarsi il seguente problema:
no healthy upstream
Motivo:
Questo messaggio di errore indica che il probe di controllo di integrità non riesce a trovare servizi di backend integri. È possibile che i servizi di backend siano integri, ma potrebbe essere necessario personalizzare i controlli di integrità.
Soluzione temporanea:
Per risolvere il problema, personalizza il controllo di integrità in base ai requisiti della tua applicazione (ad esempio, /health) utilizzando un HealthCheckPolicy.
Passaggi successivi
- Scopri di più sul controller del gateway.










