本页面介绍了安装和配置必要组件以创建备份的步骤。此外,还介绍了如何从备份中恢复和重新获得对历史审核日志的访问权限。
在远程存储桶中设置备份
本部分包含在符合 S3 标准的存储桶中创建审核日志备份的步骤。
准备工作
在为审核日志创建备份之前,您必须有权访问以下资源:
- 具有端点、私有访问密钥和访问密钥 ID 的远程 S3 存储桶。
- 存储系统的证书授权机构 (CA) 证书。
- 一个正常运行的集群。
获取访问源存储桶的凭据
请按以下步骤操作,找到包含审核日志的存储桶的凭据:
在根管理员集群上,列出项目命名空间中的存储分区:
kubectl get bucket -n PROJECT_NAMESPACE输出必须如下例所示,其中审核日志记录存储分区显示名称和端点:
NAME BUCKET NAME DESCRIPTION STORAGE CLASS FULLY-QUALIFIED-BUCKET-NAME ENDPOINT REGION BUCKETREADY REASON MESSAGE audit-logs-loki-all audit-logs-loki-all Bucket for storing audit-logs-loki-all logs Standard wwq2y-audit-logs-loki-all https://appliance-objectstorage.zone1.google.gdch.test zone1 True BucketCreationSucceeded Bucket successfully created. cortex-metrics-alertmanager cortex-metrics-alertmanager storage bucket for cortex metrics alertmanager configuration data Standard wwq2y-cortex-metrics-alertmanager https://appliance-objectstorage.zone1.google.gdch.test zone1 True BucketCreationSucceeded Bucket successfully created. cortex-metrics-blocks cortex-metrics-blocks storage bucket for cortex metrics data Standard wwq2y-cortex-metrics-blocks https://appliance-objectstorage.zone1.google.gdch.test zone1 True BucketCreationSucceeded Bucket successfully created. cortex-metrics-ruler cortex-metrics-ruler storage bucket for cortex metrics rules data Standard wwq2y-cortex-metrics-ruler https://appliance-objectstorage.zone1.google.gdch.test zone1 True BucketCreationSucceeded Bucket successfully created. ops-logs-loki-all ops-logs-loki-all Bucket for storing ops-logs-loki-all logs Standard wwq2y-ops-logs-loki-all https://appliance-objectstorage.zone1.google.gdch.test```使用您获得的输出中的信息,为迁移设置以下环境变量:
SRC_BUCKET= BUCKET_NAME SRC_ENDPOINT = ENDPOINT SRC_PATH= FULLY_QUALIFIED_BUCKET_NAME替换以下内容:
BUCKET_NAME:包含您要为其创建备份的审核日志的存储桶的名称。此值位于输出的BUCKET NAME字段中。ENDPOINT:包含您要为其创建备份的审核日志的存储桶的端点。此值位于输出的ENDPOINT字段中。FULLY_QUALIFIED_BUCKET_NAME:包含您要创建备份的审核日志的存储桶的完全限定名称。此值位于输出的FULLY-QUALIFIED-BUCKET-NAME字段中。
获取您在上一步中选择的存储桶的 Secret:
kubectl get secret -n PROJECT_NAMESPACE -o json| jq --arg jq_src $SRC_BUCKET '.items[].metadata|select(.annotations."object.gdc.goog/subject"==$jq_src)|.name'输出必须类似于以下示例,其中显示了相应存储桶的 Secret 名称:
"object-storage-key-sysstd-sa-olxv4dnwrwul4bshu37ikebgovrnvl773owaw3arx225rfi56swa"使用您获得的输出中的 Secret 名称,设置以下环境变量:
SRC_CREDENTIALS="PROJECT_NAMESPACE/SECRET_NAME"将
SECRET_NAME替换为您在上一个输出中获得的 Secret 名称。为存储系统的 CA 证书创建 Secret:
kubectl create secret generic -n PROJECT_NAMESPACE audit-log-loki-ca \ --from-literal=ca.crt=CERTIFICATE将
CERTIFICATE替换为存储系统的 CA 证书。设置以下环境变量:
SRC_CA_CERTIFICATE=PROJECT_NAMESPACE/audit-log-loki-ca
获取访问远程存储桶的凭据
请按以下步骤操作,找到要创建备份的存储桶的凭据:
设置以下环境变量:
DST_ACCESS_KEY_ID= ACCESS_KEY DST_SECRET_ACCESS_KEY= ACCESS_SECRET DST_ENDPOINT= REMOTE_ENDPOINT DST_PATH= REMOTE_BUCKET_NAME替换以下内容:
ACCESS_KEY:目标远程存储桶的访问密钥。ACCESS_SECRET:目标远程存储桶的访问密钥。REMOTE_ENDPOINT:目标远程存储桶的端点。REMOTE_BUCKET_NAME:目标远程存储桶的名称。
为远程存储桶创建 Secret:
kubectl create secret generic -n PROJECT_NAMESPACE s3-bucket-credentials \ --from-literal=access-key-id=$DST_ACCESS_KEY_ID \ --from-literal=secret-access-key=$DST_SECRET_ACCESS_KEY设置以下环境变量,并指定相应 Secret 的位置:
DST_CREDENTIALS=PROJECT_NAMESPACE/s3-bucket-credentials如果目标存储桶需要设置 CA 证书,请使用该存储桶的 CA 证书创建 Secret:
kubectl create secret generic -n PROJECT_NAMESPACE s3-bucket-ca \ --from-literal=ca.crt=REMOTE_CERTIFICATE将
REMOTE_CERTIFICATE替换为目标远程存储桶的 CA 证书。使用证书的位置设置以下环境变量:
DST_CA_CERTIFICATE=PROJECT_NAMESPACE/s3-bucket-ca
设置审核日志转移
请按以下步骤操作,以配置将审核日志从源存储桶转移到目标存储桶以进行备份:
为审核日志转移作业创建服务账号。您必须向服务账号授予读取项目命名空间中的源存储桶和 Secret 的权限。
kubectl apply -f - <<EOF --- apiVersion: v1 kind: ServiceAccount metadata: name: audit-log-transfer-sa namespace: PROJECT_NAMESPACE --- apiVersion: rbac.authorization.k8s.io/v1 kind: Role metadata: name: read-secrets-role namespace: PROJECT_NAMESPACE rules: - apiGroups: [""] resources: ["secrets"] verbs: ["get", "watch", "list"] --- apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: read-secrets-rolebinding namespace: PROJECT_NAMESPACE subjects: - kind: ServiceAccount name: audit-log-transfer-sa namespace: PROJECT_NAMESPACE roleRef: kind: Role name: read-secrets-role apiGroup: rbac.authorization.k8s.io --- apiVersion: rbac.authorization.k8s.io/v1 kind: Role metadata: name: audit-log-read-bucket-role namespace: PROJECT_NAMESPACE rules: - apiGroups: - object.gdc.goog resourceNames: - $SRC_BUCKET # Source bucket name resources: - buckets verbs: - read-object --- apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: audit-log-transfer-role-binding namespace: PROJECT_NAMESPACE roleRef: apiGroup: rbac.authorization.k8s.io kind: Role name: audit-log-read-bucket-role subjects: - kind: ServiceAccount name: audit-log-transfer-sa namespace: PROJECT_NAMESPACE --- EOF创建转移作业,将日志导出到远程存储桶:
kubectl apply -f - <<EOF --- apiVersion: batch/v1 kind: Job metadata: name: audit-log-transfer-job namespace: PROJECT_NAMESPACE spec: template: spec: serviceAccountName: audit-log-transfer-sa containers: - name: storage-transfer-pod image: gcr.io/private-cloud-staging/storage-transfer:latest imagePullPolicy: Always command: - /storage-transfer args: - '--src_endpoint=$SRC_ENDPOINT - '--dst_endpoint=$DST_ENDPOINT - '--src_path=\$SRC_PATH - '--dst_path=\$DST_PATH - '--src_credentials=$SRC_CREDENTIALS - '--dst_credentials=$DST_CREDENTIALS - '--dst_ca_certificate_reference=$DST_CA_CERTIFICATE # Optional. Based on destination type. - '--src_ca_certificate_reference=$SRC_CA_CERTIFICATE - '--src_type=s3' - '--dst_type=s3' - '--bandwidth_limit=100M' # Optional of the form '10K', '100M', '1G' bytes per second restartPolicy: OnFailure # Will restart on failure. --- EOF
安排作业后,您可以提供作业名称 (audit-log-transfer-job) 和项目命名空间来监控数据转移。
当所有数据都已转移到目标存储桶时,作业即会结束。
从备份中恢复审核日志
本部分包含从备份中恢复审核日志的步骤。
准备工作
在恢复审核日志之前,您必须有权访问以下资源:
- 具有端点、私有访问密钥和访问密钥 ID 的审核日志备份存储桶。
- 存储系统的证书授权机构 (CA) 证书。
- 一个正常运行的集群。
创建用于恢复审核日志的存储桶
请按以下步骤操作,创建一个存储桶来存储恢复的审核日志:
创建存储桶资源和服务账号:
kubectl apply -f - <<EOF --- apiVersion: object.gdc.goog/v1 kind: Bucket metadata: annotations: object.gdc.goog/audit-logs: IO labels: logging.private.gdch.goog/loggingpipeline-name: default name: audit-logs-loki-restore namespace: PROJECT_NAMESPACE spec: bucketPolicy: lockingPolicy: defaultObjectRetentionDays: 1 description: Bucket for storing audit-logs-loki logs restore storageClass: Standard --- apiVersion: rbac.authorization.k8s.io/v1 kind: Role metadata: name: audit-logs-loki-restore-buckets-role namespace: PROJECT_NAMESPACE rules: - apiGroups: - object.gdc.goog resourceNames: - audit-logs-loki-restore resources: - buckets verbs: - read-object - write-object --- apiVersion: v1 automountServiceAccountToken: false kind: ServiceAccount metadata: labels: logging.private.gdch.goog/loggingpipeline-name: default name: audit-logs-loki-restore-sa namespace: PROJECT_NAMESPACE --- apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: audit-logs-loki-restore namespace: PROJECT_NAMESPACE roleRef: apiGroup: rbac.authorization.k8s.io kind: Role name: audit-logs-loki-restore-buckets-role subjects: - kind: ServiceAccount name: audit-logs-loki-restore-sa namespace: PROJECT_NAMESPACE EOF存储桶和 Secret 已创建。
查看已创建的存储桶:
kubectl get bucket audit-logs-loki-restore -n PROJECT_NAMESPACE输出内容必须如下例所示。创建存储桶可能需要几分钟的时间。
NAME BUCKET NAME DESCRIPTION STORAGE CLASS FULLY-QUALIFIED-BUCKET-NAME ENDPOINT REGION BUCKETREADY REASON MESSAGE audit-logs-loki-restore audit-logs-loki-restore Bucket for storing audit-logs-loki logs restore Standard dzbl6-audit-logs-loki-restore https://objectstorage.zone1.google.gdch.test zone1 True BucketCreationSucceeded Bucket successfully created.输出必须显示您创建的存储桶。创建存储桶可能需要几分钟的时间。
使用您获得的输出中的信息,设置以下环境变量:
DST_BUCKET= RESTORE_BUCKET_NAME DST_ENDPOINT = RESTORE_ENDPOINT DST_PATH= RESTORE_FULLY_QUALIFIED_BUCKET_NAME替换以下内容:
RESTORE_BUCKET_NAME:用于恢复审核日志的存储桶的名称。此值位于输出的BUCKET NAME字段中。RESTORE_ENDPOINT:用于恢复审核日志的存储桶的端点。此值位于输出的ENDPOINT字段中。RESTORE_FULLY_QUALIFIED_BUCKET_NAME:用于恢复审核日志的存储桶的完全限定名称。此值位于输出的FULLY-QUALIFIED-BUCKET-NAME字段中。
获取已创建存储桶的密钥:
kubectl get secret -n PROJECT_NAMESPACE -o json| jq --arg jq_src $DST_BUCKET '.items[].metadata|select(.annotations."object.gdc.goog/subject"==$jq_src)|.name'输出必须类似于以下示例,其中显示了相应存储桶的 Secret 名称:
"object-storage-key-sysstd-sa-olxv4dnwrwul4bshu37ikebgovrnvl773owaw3arx225rfi56swa"使用您获得的输出中的 Secret 名称,设置以下环境变量:
DST_SECRET_NAME=RESTORE_SECRET_NAME DST_CREDENTIALS="PROJECT_NAMESPACE/RESTORE_SECRET_NAME"将
RESTORE_SECRET_NAME替换为您在上一个输出中获得的 Secret 名称。为存储系统的 CA 证书创建 Secret:
kubectl create secret generic -n PROJECT_NAMESPACE audit-log-loki-restore-ca \ --from-literal=ca.crt=CERTIFICATE将
CERTIFICATE替换为存储系统的 CA 证书。为证书的位置设置以下环境变量:
DST_CA_CERTIFICATE=PROJECT_NAMESPACE/audit-log-loki-restore-ca
获取访问备份存储桶的凭据
请按照以下步骤操作,找到包含审核日志备份的存储桶的凭据:
设置以下环境变量:
SRC_ACCESS_KEY_ID= ACCESS_KEY SRC_SECRET_ACCESS_KEY= ACCESS_SECRET SRC_ENDPOINT= REMOTE_ENDPOINT SRC_PATH= REMOTE_BUCKET_NAME替换以下内容:
ACCESS_KEY:备份存储桶的访问密钥。ACCESS_SECRET:备份存储桶的访问密钥。REMOTE_ENDPOINT:备份存储桶的端点。REMOTE_BUCKET_NAME:备份存储桶的名称。
为备份存储桶创建 Secret:
kubectl create secret generic -n PROJECT_NAMESPACE s3-backup-bucket-credentials \ --from-literal=access-key-id=$SRC_ACCESS_KEY_ID \ --from-literal=secret-access-key=$SRC_SECRET_ACCESS_KEY设置以下环境变量,并指定相应 Secret 的位置:
SRC_CREDENTIALS=PROJECT_NAMESPACE/s3-backup-bucket-credentials创建包含相应存储桶的 CA 证书的 Secret:
kubectl create secret generic -n PROJECT_NAMESPACE s3-backup-bucket-ca \ --from-literal=ca.crt=BACKUP_CERTIFICATE将
BACKUP_CERTIFICATE替换为备份存储桶的 CA 证书。使用证书的位置设置以下环境变量:
SRC_CA_CERTIFICATE=PROJECT_NAMESPACE/s3-backup-bucket-ca
设置审核日志的恢复
请按以下步骤操作,将审核日志从备份存储桶转移到恢复存储桶:
为审核日志转移作业创建服务账号。您必须向服务账号授予在项目命名空间中读取和写入存储桶及 Secret 的权限。
kubectl apply -f - <<EOF --- apiVersion: v1 kind: ServiceAccount metadata: name: audit-log-restore-sa namespace: PROJECT_NAMESPACE --- apiVersion: rbac.authorization.k8s.io/v1 kind: Role metadata: name: read-secrets-role namespace: PROJECT_NAMESPACE rules: - apiGroups: [""] resources: ["secrets"] verbs: ["get", "watch", "list"] --- apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: read-secrets-rolebinding-restore namespace: PROJECT_NAMESPACE subjects: - kind: ServiceAccount name: audit-log-restore-sa namespace: PROJECT_NAMESPACE roleRef: kind: Role name: read-secrets-role apiGroup: rbac.authorization.k8s.io --- apiVersion: rbac.authorization.k8s.io/v1 kind: Role metadata: name: audit-log-restore-bucket-role namespace: PROJECT_NAMESPACE rules: - apiGroups: - object.gdc.goog resourceNames: - $DST_BUCKET # Source bucket name resources: - buckets verbs: - read-object - write-object --- apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: audit-log-restore-role-binding namespace: PROJECT_NAMESPACE roleRef: apiGroup: rbac.authorization.k8s.io kind: Role name: audit-log-restore-bucket-role subjects: - kind: ServiceAccount name: audit-log-restore-sa namespace: PROJECT_NAMESPACE --- EOF创建转移作业以从远程备份存储桶恢复日志:
kubectl apply -f - <<EOF --- apiVersion: batch/v1 kind: Job metadata: name: audit-log-restore-job namespace: PROJECT_NAMESPACE spec: template: spec: serviceAccountName: audit-log-restore-sa containers: - name: storage-transfer-pod image: gcr.io/private-cloud-staging/storage-transfer:latest imagePullPolicy: Always command: - /storage-transfer args: - '--src_endpoint=$SRC_ENDPOINT - '--dst_endpoint=$DST_ENDPOINT - '--src_path=\$SRC_PATH - '--dst_path=\$DST_PATH - '--src_credentials=$SRC_CREDENTIALS - '--dst_credentials=$DST_CREDENTIALS - '--dst_ca_certificate_reference=$DST_CA_CERTIFICATE - '--src_ca_certificate_reference=$SRC_CA_CERTIFICATE # Optional. Based on destination type - '--src_type=s3' - '--dst_type=s3' - '--bandwidth_limit=100M' # Optional of the form '10K', '100M', '1G' bytes per second restartPolicy: OnFailure # Will restart on failure. --- EOF
安排作业后,您可以提供作业名称 (audit-log-restore-job) 和项目命名空间来监控数据转移。
当所有数据都已转移到目标存储桶时,作业即会结束。
部署审核日志实例以访问日志
您必须部署 Loki 实例(也称为审核日志实例)才能访问已恢复的日志。
如需设置审核日志实例,请使用您为恢复作业创建的 audit-log-restore-sa 服务账号。请按以下步骤部署实例:
为实例的配置创建
ConfigMap对象:kubectl apply -f - <<EOF apiVersion: v1 kind: ConfigMap metadata: name: audit-logs-loki-restore namespace: PROJECT_NAMESPACE data: loki.yaml: |- auth_enabled: true common: ring: kvstore: store: inmemory chunk_store_config: max_look_back_period: 0s compactor: shared_store: s3 working_directory: /data/loki/boltdb-shipper-compactor compaction_interval: 10m retention_enabled: true retention_delete_delay: 2h retention_delete_worker_count: 150 ingester: chunk_target_size: 1572864 chunk_encoding: snappy max_chunk_age: 2h chunk_idle_period: 90m chunk_retain_period: 30s autoforget_unhealthy: true lifecycler: ring: kvstore: store: inmemory replication_factor: 1 heartbeat_timeout: 10m max_transfer_retries: 0 wal: enabled: true flush_on_shutdown: true dir: /wal checkpoint_duration: 1m replay_memory_ceiling: 20GB limits_config: retention_period: 48h enforce_metric_name: false reject_old_samples: false ingestion_rate_mb: 256 ingestion_burst_size_mb: 256 max_streams_per_user: 20000 max_global_streams_per_user: 20000 per_stream_rate_limit: 256MB per_stream_rate_limit_burst: 256MB shard_streams: enabled: false desired_rate: 3MB schema_config: configs: - from: "2020-10-24" index: period: 24h prefix: index_ object_store: s3 schema: v11 store: boltdb-shipper server: http_listen_port: 3100 grpc_server_max_recv_msg_size: 104857600 grpc_server_max_send_msg_size: 104857600 analytics: reporting_enabled: false storage_config: boltdb_shipper: active_index_directory: /data/loki/boltdb-shipper-active cache_location: /data/loki/boltdb-shipper-cache cache_ttl: 24h shared_store: s3 aws: endpoint: $DST_ENDPOINT bucketnames: $DST_PATH access_key_id: ${S3_ACCESS_KEY_ID} secret_access_key: ${S3_SECRET_ACCESS_KEY} s3forcepathstyle: true EOF部署实例,并使用一项服务来访问恢复存储桶中的日志:
kubectl apply -f - <<EOF --- apiVersion: apps/v1 kind: StatefulSet metadata: labels: app: audit-logs-loki-restore logging.private.gdch.goog/loggingpipeline-name: default name: audit-logs-loki-restore namespace: PROJECT_NAMESPACE spec: persistentVolumeClaimRetentionPolicy: whenDeleted: Retain whenScaled: Retain podManagementPolicy: OrderedReady replicas: 1 revisionHistoryLimit: 10 selector: matchLabels: app: audit-logs-loki-restore serviceName: audit-logs-loki-restore template: metadata: labels: app: audit-logs-loki-restore app.kubernetes.io/part-of: audit-logs-loki-restore egress.networking.gke.io/enabled: "true" istio.io/rev: default logging.private.gdch.goog/log-type: audit spec: affinity: nodeAffinity: preferredDuringSchedulingIgnoredDuringExecution: - preference: matchExpressions: - key: node-role.kubernetes.io/control-plane operator: DoesNotExist - key: node-role.kubernetes.io/master operator: DoesNotExist weight: 1 podAntiAffinity: preferredDuringSchedulingIgnoredDuringExecution: - podAffinityTerm: labelSelector: matchExpressions: - key: app operator: In values: - audit-logs-loki-restore topologyKey: kubernetes.io/hostname weight: 100 containers: - args: - -config.file=/etc/loki/loki.yaml - -config.expand-env=true - -target=all env: - name: S3_ACCESS_KEY_ID valueFrom: secretKeyRef: key: access-key-id name: $DST_SECRET_NAME optional: false - name: S3_SECRET_ACCESS_KEY valueFrom: secretKeyRef: key: secret-access-key name: $DST_SECRET_NAME optional: false image: gcr.io/private-cloud-staging/loki:v2.8.4-gke.2 imagePullPolicy: Always livenessProbe: failureThreshold: 3 httpGet: path: /ready port: http-metrics scheme: HTTP initialDelaySeconds: 330 periodSeconds: 10 successThreshold: 1 timeoutSeconds: 1 name: audit-logs-loki-restore ports: - containerPort: 3100 name: http-metrics protocol: TCP - containerPort: 7946 name: gossip-ring protocol: TCP readinessProbe: failureThreshold: 3 httpGet: path: /ready port: http-metrics scheme: HTTP initialDelaySeconds: 45 periodSeconds: 10 successThreshold: 1 timeoutSeconds: 1 resources: limits: ephemeral-storage: 2000Mi memory: 8000Mi requests: cpu: 300m ephemeral-storage: 2000Mi memory: 1000Mi securityContext: readOnlyRootFilesystem: true terminationMessagePath: /dev/termination-log terminationMessagePolicy: File volumeMounts: - mountPath: /etc/loki name: config - mountPath: /data name: loki-storage - mountPath: /tmp name: temp - mountPath: /tmp/loki/rules-temp name: tmprulepath - mountPath: /etc/ssl/certs/storage-cert.crt name: storage-cert subPath: ca.crt - mountPath: /wal name: loki-storage dnsPolicy: ClusterFirst priorityClassName: audit-logs-loki-priority restartPolicy: Always schedulerName: default-scheduler securityContext: fsGroup: 10001 runAsGroup: 10001 runAsUser: 10001 serviceAccount: audit-logs-loki-restore-sa serviceAccountName: audit-logs-loki-restore-sa terminationGracePeriodSeconds: 4800 volumes: - emptyDir: {} name: temp - configMap: defaultMode: 420 name: audit-logs-loki-restore name: config - emptyDir: {} name: tmprulepath - name: storage-cert secret: defaultMode: 420 secretName: web-tls updateStrategy: type: RollingUpdate volumeClaimTemplates: - apiVersion: v1 kind: PersistentVolumeClaim metadata: creationTimestamp: null name: loki-storage spec: accessModes: - ReadWriteOnce resources: requests: storage: 50Gi storageClassName: standard-rwo volumeMode: Filesystem --- apiVersion: v1 kind: Service metadata: name: audit-logs-loki-restore namespace: PROJECT_NAMESPACE spec: internalTrafficPolicy: Cluster ipFamilies: - IPv4 ipFamilyPolicy: SingleStack ports: - name: http-metrics port: 3100 protocol: TCP targetPort: http-metrics selector: app: audit-logs-loki-restore sessionAffinity: None type: ClusterIP --- EOF
配置监控实例以查看数据源中的日志
请按照以下步骤配置 Grafana(也称为监控实例),以查看审核日志实例中恢复的审核日志:
- 前往项目的监控实例的端点。
- 在界面 (UI) 的导航菜单中,依次点击管理 > 数据源。
- 点击 添加新的数据源。
- 在添加数据源页面上,选择 Loki。
- 在设置页面上,为名称字段输入值
Audit Logs - Restore。 在 HTTP 部分,为 网址 字段输入以下值:
http://audit-logs-loki-restore.PROJECT_NAMESPACE.svc:3100在自定义 HTTP 标头部分,在相应字段中输入以下值:
- Header:
X-Scope-OrgID - 值:
infra-obs
- Header:
在图 1 中,Loki 显示为监控实例界面添加数据源页面上的一个选项。在图 2 中,“设置”页面显示了您必须填写才能设置数据源的字段。
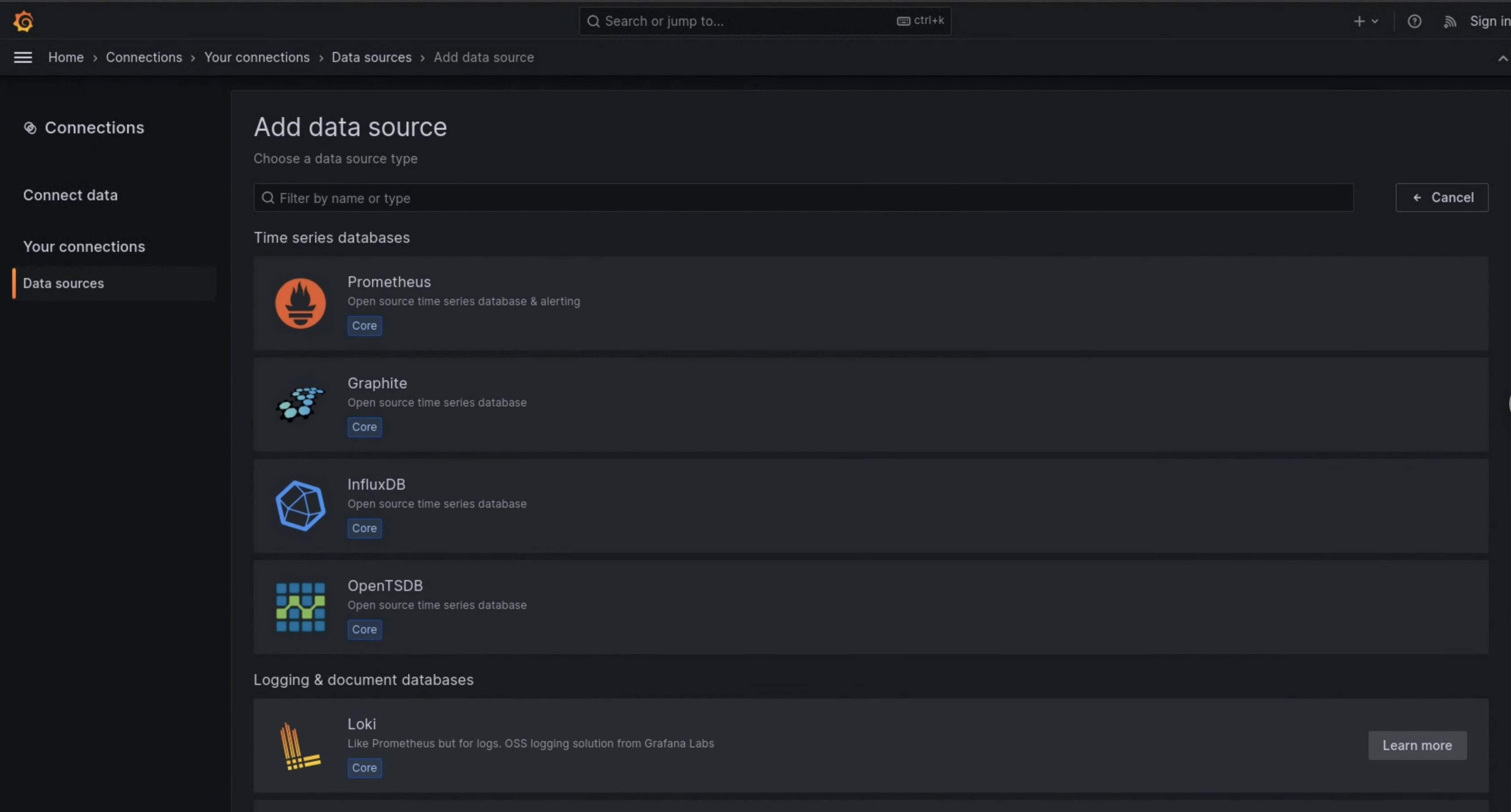
图 1. 监控实例界面上的添加数据源页面。
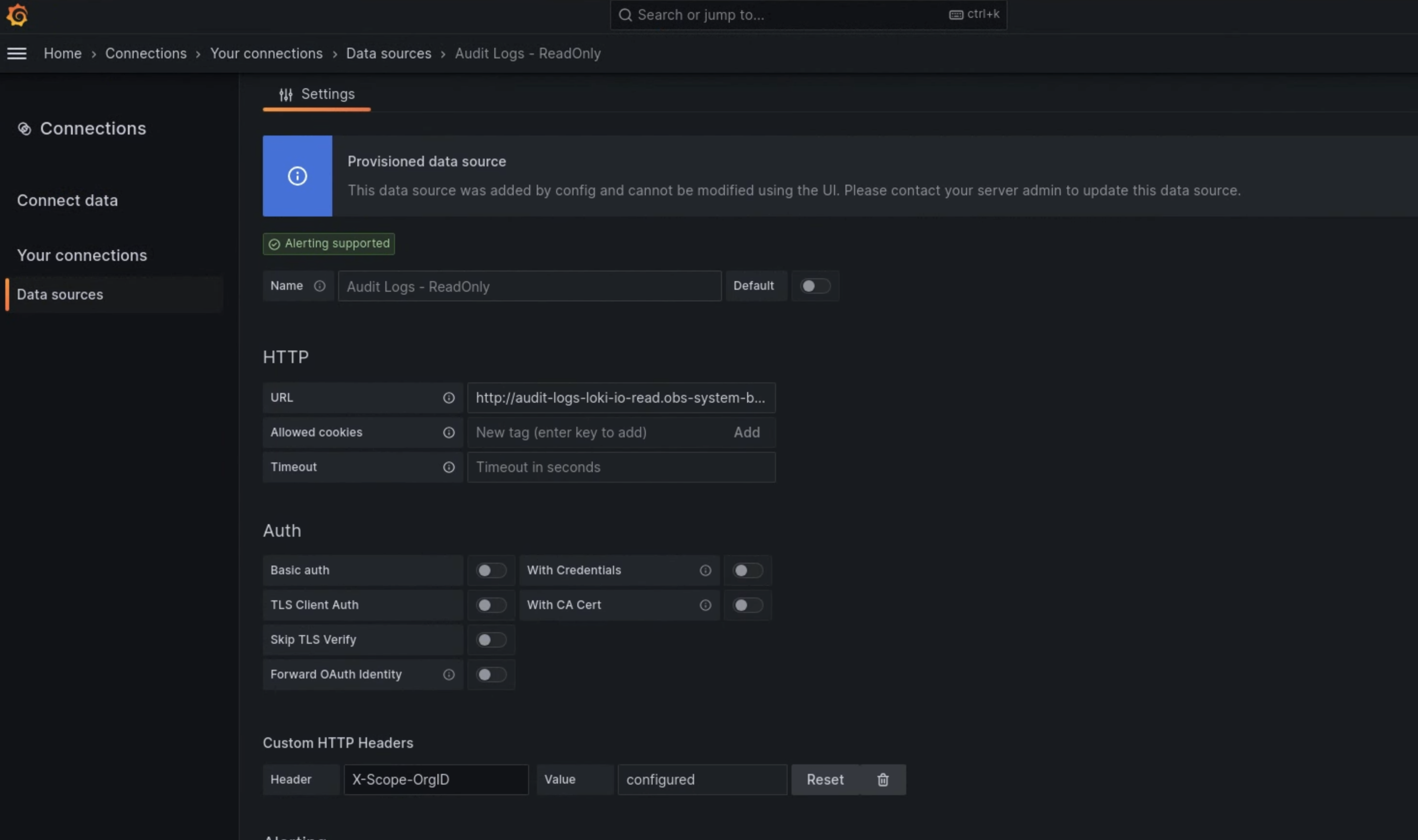
图 2. 监控实例界面上的设置页面。
Audit Logs - Restore 选项现在可在日志浏览器中用作数据源。

