This document provides configuration steps for automatically deploying the suggested rules that Adaptive Protection generates. To enable automatic rule deployment, you must create a placeholder rule with the following values:
- Match expression:
evaluateAdaptiveProtectionAutoDeploy() - Action: Any
- Priority: Any. We recommend that you set an explicit allow rule at a higher priority than your other rules for high-priority, legitimate traffic.
If you use an upstream proxy in front of your external Application Load Balancer, such as a
third-party CDN, you can configure the placeholder rule to match requests based
on the original client's IP address from a specified header or headers. To use
this preview feature, configure the userIpRequestHeaders[] option in the
advancedOptionsConfig field. For more information, see the
ComputeSecurityPolicy
resource reference.
Example placeholder rules
The following commands are example placeholder rules for security policies
called POLICY_NAME, each of which features a different rule action.
You can add these rules to an existing security policy or create a new policy. For
more information about creating security policies, see
Configure Cloud Armor security policies.
Block malicious traffic
This example rule evaluates to true for requests that Adaptive Protection
identifies as attack traffic. Cloud Armor applies the blocking
action to the attacking request:
gcloud compute security-policies rules create 1000 \
--security-policy POLICY_NAME \
--expression "evaluateAdaptiveProtectionAutoDeploy()" \
--action deny-403
Redirect malicious traffic to a reCAPTCHA challenge
This example rule redirects traffic that Adaptive Protection identifies as malicious to a reCAPTCHA challenge:
gcloud compute security-policies rules create 1000 \
--security-policy POLICY_NAME \
--expression "evaluateAdaptiveProtectionAutoDeploy()" \
--action redirect \
--redirect-type google-recaptcha
Rate limit malicious traffic
This example applies Cloud Armor rate limiting to traffic that Adaptive Protection identifies as malicious:
gcloud compute security-policies rules create 1000 \
--security-policy POLICY_NAME \
--expression "evaluateAdaptiveProtectionAutoDeploy()" \
--action throttle \
--rate-limit-threshold-count 500 \
--rate-limit-threshold-interval-sec 120 \
--conform-action allow \
--exceed-action deny-404 \
--enforce-on-key ip
Configure Adaptive Protection auto-deploy parameters
You can configure the thresholds for automatic deployment of rules by tuning the following parameters. If you don't set the value for a parameter, Cloud Armor uses the default value.
Load threshold: during an alerted attack, Adaptive Protection identifies new attackers only when the load to the backend service that is under attack exceeds this threshold. In addition, rules are only automatically deployed for alerts when the load to the backend service that is under attack exceeds this threshold.
Default value:
0.8
Confidence threshold: rules are only automatically deployed for alerts on potential attacks with confidence scores greater than this threshold.
- Default value:
0.5
- Default value:
Impacted baseline threshold: rules are only automatically deployed when the estimated impact to baseline traffic from the suggested mitigation is below this threshold.
impactedBaselineProportionandimpactedbaselinePolicyProportionshould be lower than the impacted baseline threshold.- Default value:
0.01(1%)
- Default value:
Expiration set: Cloud Armor stops applying the action in the automatically deployed rule to an identified attacker after this duration. The rule continues to operate against new requests.
- Default value:
7200seconds
- Default value:
You can use the following example command to update your security policy to use
non-default, automatically deployed thresholds. Replace NAME with
the name of your security policy, and replace the remaining variables with the
values that you want for your policy.
gcloud beta compute security-policies update NAME [
--layer7-ddos-defense-auto-deploy-load-threshold LOAD_THRESHOLD
--layer7-ddos-defense-auto-deploy-confidence-threshold CONFIDENCE_THRESHOLD
--layer7-ddos-defense-auto-deploy-impacted-baseline-threshold IMPACTED_BASELINE_THRESHOLD
--layer7-ddos-defense-auto-deploy-expiration-sec EXPIRATION_SEC
]
Logging
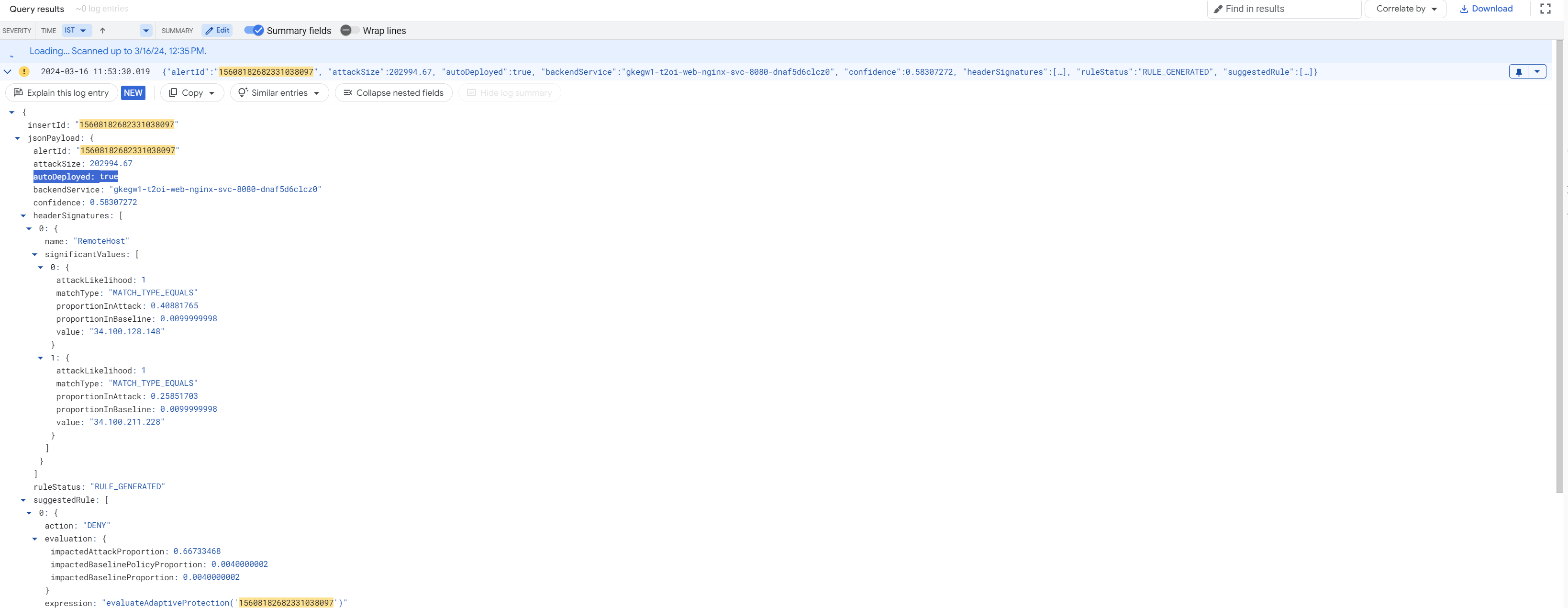
Logs generated by rules automatically deployed with Adaptive Protection have the following additional fields:
autoDeployed: after you configure automatic rule deployment, each alert log that Adaptive Protection generates has the boolean fieldautoDeployed, which indicates whether an automatic defense was triggered. WhenautoDeployedis set totrue, it indicates that theevaluateAdaptiveProtectionAutoDeploy()placeholder rule has already evaluated that the attack Confidence and Impacted baseline thresholds have exceeded the configured auto-deploy parameters. The system then begins to monitor the dynamic load. Once the load surpasses the configured load threshold, the rule is automatically deployed to mitigate the attack.adaptiveProtection.autoDeployAlertId: whenever Adaptive Protection takes an action on a request as part of an automatic defense, the request log has the additionaladaptiveProtection.autoDeployAlertIdfield, which records the alert ID. This field appears underenforcedSecurityPolicyorpreviewSecurityPolicy, depending on whether the security policy is in preview mode.
To view request logs, see Use request logging. The
following screenshot shows an example of an Adaptive Protection log entry,
with the autoDeployed and adaptiveProtection.autoDeployAlertId fields.
Limitations
- Adaptive Protection is only available for backend security policies attached to backend services that are exposed through an external Application Load Balancer. Adaptive Protection is not available for external proxy Network Load Balancers.
