This page describes how to enable and disable Domain Name System Security Extensions (DNSSEC), and verify DNSSEC deployment.
For a conceptual overview of DNSSEC, see the DNSSEC overview.
Enable DNSSEC for existing managed public zones
To enable DNSSEC for existing managed public zones, follow these steps.
Console
In the Google Cloud console, go to the Cloud DNS page.
Click the zone name for which you want to enable DNSSEC.
On the Zone details page, click Edit.
On the Edit a DNS zone page, click DNSSEC.
Under DNSSEC, select On.
Click Save.
Your selected DNSSEC state for the zone is displayed in the DNSSEC column on the Cloud DNS page.
gcloud
Run the following command:
gcloud dns managed-zones update EXAMPLE_ZONE \
--dnssec-state on
Replace EXAMPLE_ZONE with the zone ID.
Terraform
Enable DNSSEC when creating zones
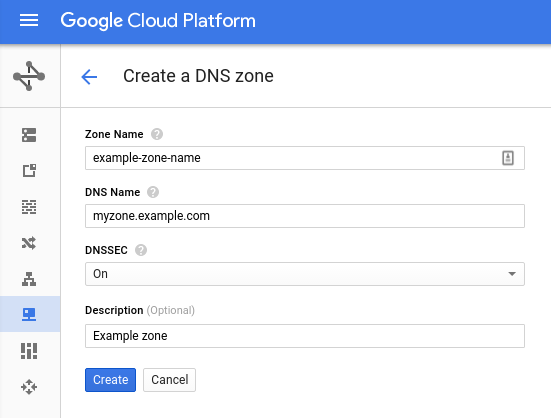
To enable DNSSEC when you are creating a zone, follow these steps.
Console
In the Google Cloud console, go to the Cloud DNS page.
Click Create zone.
In the Zone name field, enter a name.
In the DNS name field, enter a name.
Under DNSSEC, select On.
Optional: Add a description.
Click Create.
gcloud
Run the following command:
gcloud dns managed-zones create EXAMPLE_ZONE \
--description "Signed Zone" \
--dns-name myzone.example.com \
--dnssec-state on
Replace EXAMPLE_ZONE with the zone ID.
Verify DNSSEC deployment
To verify correct deployment of your DNSSEC-enabled zone, make sure that you placed the correct DS record in the parent zone. DNSSEC resolution can fail if either of the following occurs:
- The configuration is wrong, or you have mistyped it.
- You have placed the incorrect DS record in the parent zone.
To verify that you have the right configuration in place and to cross-check the DS record before placing it in the parent zone, use the following tools:
You can use the Verisign DNSSEC debugger and Zonemaster sites to validate your
DNSSEC configuration before you update your registrar with your Cloud DNS
name servers or DS record. A domain that is properly configured for DNSSEC is
example.com,
viewable using DNSViz.
Recommended TTL settings for DNSSEC-signed zones
TTL is the time to live (in seconds) for a DNSSEC-signed zone.
Unlike TTL expirations, which are relative to the time a name server sends a response to a query, DNSSEC signatures expire at a fixed absolute time. TTLs configured longer than a signature lifetime can lead to many clients requesting records at the same time as the DNSSEC signature expires. Short TTLs can also cause problems for DNSSEC-validating resolvers.
For more recommendations about TTL selection, see RFC 6781 section 4.4.1 Time Considerations and RFC 6781 Figure 11.
When reading RFC 6781 section 4.4.1, consider that many signature time parameters are fixed by Cloud DNS and you cannot change them. You cannot change the following parameters (subject to change without notice or update to this document):
- Inception offset = 1 day
- Validity period = 21 days
- Re-sign period = 3 days
- Refresh period = 18 days
- Jitter interval = ½ day (or ±6 hours)
- Minimum signature validity = refresh – jitter = 17.75 days = 1533600
You must never use a TTL longer than the minimum signature validity.
Disable DNSSEC for managed zones
After you have removed DS records and waited for them to expire from cache,
you can use the following gcloud command to turn off DNSSEC:
gcloud dns managed-zones update EXAMPLE_ZONE \
--dnssec-state off
Replace EXAMPLE_ZONE with the zone ID.
What's next
- To get information about specific DNSSEC configurations, see Use advanced DNSSEC.
- To work with managed zones, see Create, modify, and delete zones.
- To find solutions for common issues that you might encounter when using Cloud DNS, see Troubleshooting.
- To get an overview of Cloud DNS, see Cloud DNS overview.
