Microsoft Windows Sysmon 데이터 수집
이 문서:
- 배포 아키텍처와 설치 단계 그리고 Microsoft Windows Sysmon 이벤트용 Google Security Operations 파서에서 지원하는 로그를 생성하는 데 필요한 구성을 설명합니다. Google Security Operations 데이터 수집에 대한 개요는 Google Security Operations에 데이터 수집을 참조하세요.
- 파서에서 원래 로그의 필드를 Google Security Operations 통합 데이터 모델 필드에 매핑하는 방식에 대한 정보가 포함됩니다.
이 문서의 정보는 WINDOWS_SYSMON 수집 라벨이 있는 파서에 적용됩니다. 수집 라벨은 원시 로그 데이터를 구조화된 UDM 형식으로 정규화하는 파서를 식별합니다.
시작하기 전에
권장 배포 아키텍처 검토
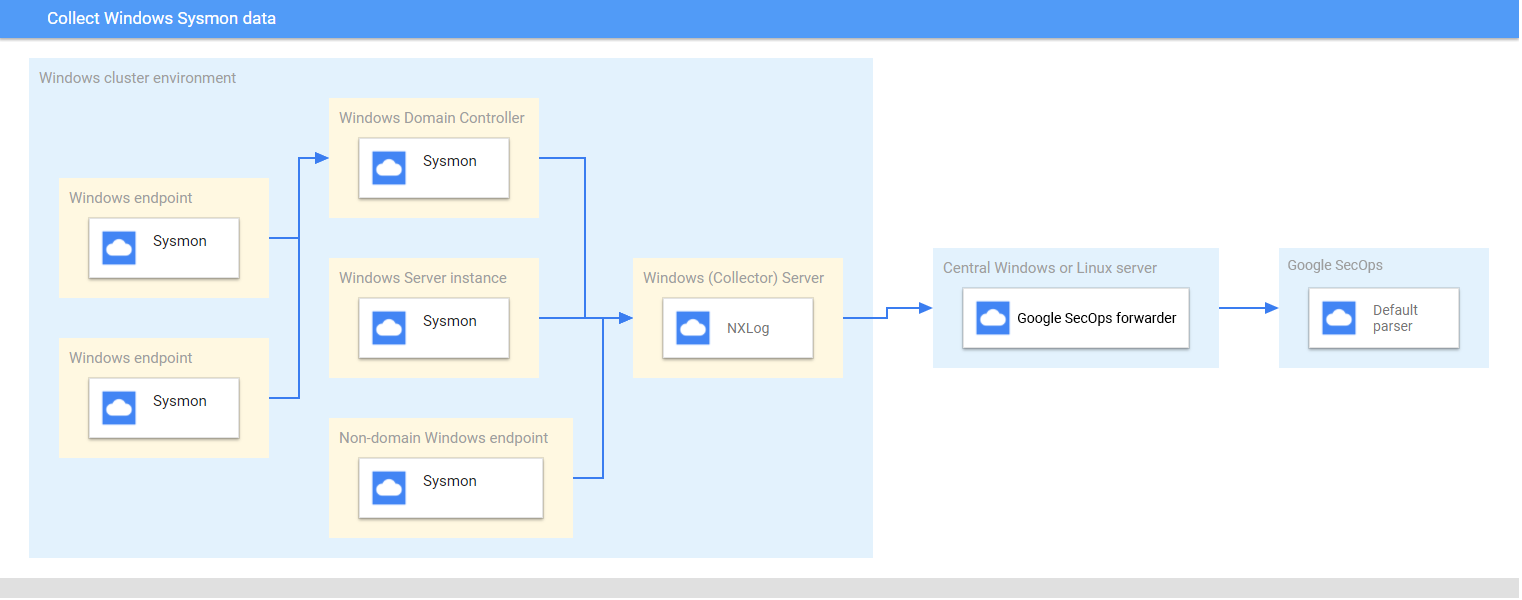
이 다이어그램은 Microsoft Windows Sysmon 데이터를 수집하고 Google Security Operations로 전송하기 위해 배포 아키텍처에서 권장되는 핵심 구성요소를 나타냅니다. 이 정보를 사용자 환경과 비교하여 이러한 구성요소가 설치되어 있는지 확인합니다. 각 고객 배포는 이 표현과 다르며, 더 복잡할 수 있습니다. 다음은 필수 항목입니다.
- 배포 아키텍처의 시스템은 UTC 시간대로 구성됩니다.
- Sysmon은 서버, 엔드포인트, 도메인 컨트롤러에 설치됩니다.
- 수집기 Microsoft Windows 서버는 서버, 엔드포인트, 도메인 컨트롤러에서 로그를 수신합니다.
배포 아키텍처의 Microsoft Windows 시스템은 다음을 사용합니다.
- 여러 기기에서 이벤트를 수집하기 위해 소스 시작 구독
- 원격 시스템 관리를 위한 WinRM 서비스
NXLog는 Google Security Operations 전달자로 로그를 전달하기 위해 수집기 창 서버에 설치됩니다.
Google Security Operations 전달자는 중앙 Microsoft Windows 서버 또는 Linux 서버에 설치됩니다.
지원되는 기기 및 버전 검토
Google Security Operations 파서는 다음 Microsoft Windows 서버 버전에서 생성된 로그를 지원합니다. Microsoft Windows Server는 Foundation, Essentials, Standard, Datacenter 버전으로 출시됩니다. 각 버전에서 생성된 로그의 이벤트 스키마는 다르지 않습니다.
- Microsoft Windows Server 2019
- Microsoft Windows Server 2016
- Microsoft Windows Server 2012
Google Security Operations 파서는 다음으로 생성된 로그를 지원합니다.
- Microsoft Windows 7 이상 클라이언트 시스템
- Sysmon 버전 13.24
Google Security Operations 파서는 NXLog Community 또는 Enterprise Edition에서 수집되는 로그를 지원합니다.
지원되는 로그 유형 검토
Google Security Operations 파서는 Microsoft Windows Sysmon에서 생성되는 다음 로그 유형을 지원합니다. 이러한 로그 유형에 대한 자세한 내용은 Microsoft Windows Sysmon 문서를 참조하세요. 영어 텍스트로 생성된 로그를 지원하며 영어가 아닌 언어로 생성된 로그에서는 지원되지 않습니다.
| 로그 유형 | 설명 |
|---|---|
| Sysmon 로그 | Sysmon 채널에는 27개의 이벤트 ID가 있습니다. (이벤트 ID: 1~26, 255) 이 로그 유형에 대한 설명은 Microsoft Windows Sysmon Events 문서를 참조하세요. |
Microsoft Windows 서버, 엔드포인트, 도메인 컨트롤러 구성
- 서버, 엔드포인트, 도메인 컨트롤러를 설치하고 구성합니다. 자세한 내용은 Microsoft Windows Sysmon Configuration 문서를 참조하세요.
- 수집기 Microsoft Windows 서버를 설정하여 여러 시스템에서 수집된 로그를 파싱합니다.
- 중앙 Microsoft Windows 또는 Linux 서버 설정
- UTC 시간대로 모든 시스템을 구성합니다.
- 수집기 Microsoft Windows 서버로 로그를 전달하도록 기기를 구성합니다.
- Microsoft Windows 시스템에서 소스 시작 구독을 구성합니다. 자세한 내용은 소스 시작 구독 설정을 참조하세요.
- Microsoft Windows 서버 및 클라이언트에서 WinRM을 사용 설정합니다. 자세한 내용은 Microsoft Windows 원격 관리 설치 및 구성을 참조하세요.
BindPlane 에이전트 구성
BindPlane 에이전트를 사용하여 Windows Sysmon 로그를 수집합니다.
설치 후 BindPlane Agent 서비스가 Windows 서비스 목록에 observerIQ 서비스로 표시됩니다.
- Windows 서버에서 실행 중인 수집기에 BindPlane 에이전트를 설치합니다. BindPlane 에이전트 설치에 대한 자세한 내용은 BindPlane 에이전트 설치 안내를 참조하세요.
다음 콘텐츠로 BindPlane 에이전트의 구성 파일을 만듭니다.
receivers: windowseventlog/sysmon: channel: Microsoft-Windows-Sysmon/Operational raw: true processors: batch: exporters: chronicle/winsysmon: endpoint: https://malachiteingestion-pa.googleapis.com creds: '{ "type": "service_account", "project_id": "malachite-projectname", "private_key_id": `PRIVATE_KEY_ID`, "private_key": `PRIVATE_KEY`, "client_email":"`SERVICE_ACCOUNT_NAME`@malachite-`PROJECT_ID`.iam.gserviceaccount.com", "client_id": `CLIENT_ID`, "auth_uri": "https://accounts.google.com/o/oauth2/auth", "token_uri": "https://oauth2.googleapis.com/token", "auth_provider_x509_cert_url":"https://www.googleapis.com/oauth2/v1/certs", "client_x509_cert_url": "https://www.googleapis.com/robot/v1/metadata/x509/`SERVICSERVICE_ACCOUNT_NAME`%40malachite-`PROJECT_ID`.iam.gserviceaccount.com", "universe_domain": "googleapis.com" }' log_type: 'WINDOWS_SYSMON' override_log_type: false raw_log_field: body customer_id: `CUSTOMER_ID` service: pipelines: logs/winsysmon: receivers: - windowseventlog/sysmon processors: [batch] exporters: [chronicle/winsysmon]PRIVATE_KEY_ID,PRIVATE_KEY,SERVICSERVICE_ACCOUNT_NAME,PROJECT_ID,CLIENT_ID,CUSTOMER_ID를 Google Cloud Platform에서 다운로드할 수 있는 서비스 계정 JSON 파일의 각 값으로 바꿉니다. 서비스 계정 키에 대한 자세한 내용은 서비스 계정 키 만들기 및 삭제 문서를 참조하세요.observerIQ 에이전트 서비스를 시작하려면 서비스 > 확장 > observerIQ 서비스 > 시작을 선택합니다.
NXLog 및 Google Security Operations 전달자 구성
- Windows 서버에서 실행되는 수집기에 NXLog를 설치합니다. Sysmon에서 로그를 수집하도록 NXLog 구성에 대한 정보를 포함한 NXLog 문서를 따르세요.
NXLog용 구성 파일을 만듭니다. im_msvistalog 입력 모듈을 사용합니다. 다음은 NXLog 구성의 예입니다.
<hostname>및<port>값을 대상 중앙 Microsoft Windows 또는 Linux 서버에 대한 정보로 바꿉니다. 자세한 내용은 om_tcp 모듈에 대한 NXLog 문서를 참조하세요.define ROOT C:\Program Files (x86)\nxlog define SYSMON_OUTPUT_DESTINATION_ADDRESS <hostname> define SYSMON_OUTPUT_DESTINATION_PORT <port> define CERTDIR %ROOT%\cert define CONFDIR %ROOT%\conf define LOGDIR %ROOT%\data define LOGFILE %LOGDIR%\nxlog.log LogFile %LOGFILE% Moduledir %ROOT%\modules CacheDir %ROOT%\data Pidfile %ROOT%\data\nxlog.pid SpoolDir %ROOT%\data <Extension _json> Module xm_json </Extension> <Input windows_sysmon_eventlog> Module im_msvistalog <QueryXML> <QueryList> <Query Id="0"> <Select Path="Microsoft-Windows-Sysmon/Operational">*</Select> </Query> </QueryList> </QueryXML> ReadFromLast False SavePos False </Input> <Output out_chronicle_sysmon> Module om_tcp Host %SYSMON_OUTPUT_DESTINATION_ADDRESS% Port %SYSMON_OUTPUT_DESTINATION_PORT% Exec $EventTime = integer($EventTime) / 1000; Exec $EventReceivedTime = integer($EventReceivedTime) / 1000; Exec to_json(); </Output> <Route r2> Path windows_sysmon_eventlog => out_chronicle_sysmon </Route>중앙 Microsoft Windows 또는 Linux 서버에 Google Security Operations 전달자를 설치합니다. 전달자 설치 및 구성에 대한 자세한 내용은 Linux에서 전달자 설치 및 구성 또는 Microsoft Windows에서 전달자 설치 및 구성을 참조하세요.
Google Security Operations 전달자를 구성하여 로그를 Google Security Operations에 전송합니다. 다음은 전달자 구성의 예입니다.
- syslog: common: enabled: true data_type: WINDOWS_SYSMON Data_hint: batch_n_seconds: 10 batch_n_bytes: 1048576 tcp_address: 0.0.0.0:10518 connection_timeout_sec: 60NXLog 서비스를 시작합니다.
필드 매핑 참조: 기기 이벤트 필드에서 UDM 필드로
이 섹션에서는 파서가 원래 통합 로그 모델을 통합 데이터 모델(UDM) 필드에 매핑하는 방법을 설명합니다. 필드 매핑은 이벤트 ID별로 다를 수 있습니다.
필드 매핑 참조: 이벤트 식별자에서 이벤트 유형으로
다음 표에는WINDOWS_SYSMON 로그 유형과 해당 UDM 이벤트 유형이 나와 있습니다.
| Event Identifier | Event Type | Security Category |
|---|---|---|
1 |
PROCESS_LAUNCH |
|
2 |
FILE_MODIFICATION |
|
3 |
NETWORK_CONNECTION |
|
4 |
SETTING_MODIFICATION |
|
5 |
PROCESS_TERMINATION |
|
6 |
PROCESS_MODULE_LOAD |
|
7 |
PROCESS_MODULE_LOAD |
|
8 |
PROCESS_MODULE_LOAD |
|
9 |
FILE_READ |
|
10 |
PROCESS_OPEN |
|
11 |
FILE_CREATION |
|
12 |
If the Message log field value matches the regular expression pattern CreateKey|CreateValue then, the metadata.event_type UDM field is set to REGISTRY_CREATION. Else if the Message log field value matches the regular expression pattern DeleteKey|DeleteValue then, the target.resource.name UDM field is set to REGISTRY_DELETION.Else, the target.resource.name UDM field is set to REGISTRY_MODIFICATION. |
|
13 |
REGISTRY_MODIFICATION |
|
14 |
REGISTRY_MODIFICATION |
|
15 |
FILE_CREATION |
|
16 |
SETTING_MODIFICATION |
|
17 |
PROCESS_UNCATEGORIZED |
|
18 |
PROCESS_UNCATEGORIZED |
|
19 |
USER_RESOURCE_ACCESS |
|
20 |
USER_RESOURCE_ACCESS |
|
21 |
USER_RESOURCE_ACCESS |
|
22 |
NETWORK_DNS |
|
23 |
FILE_DELETION |
|
24 |
RESOURCE_READ |
|
25 |
PROCESS_LAUNCH |
|
26 |
FILE_DELETION |
|
255 |
SERVICE_UNSPECIFIED |
|
필드 매핑 참조: WINDOWS_SYSMON
다음 표에는 WINDOWS_SYSMON 로그 유형의 로그 필드와 해당 UDM 필드가 나와 있습니다.
| Log field | UDM mapping | Logic |
|---|---|---|
SourceName |
|
|
|
metadata.vendor_name |
The metadata.vendor_name UDM field is set to Microsoft. |
|
metadata.product_name |
The metadata.product_name UDM field is set to Microsoft-Windows-Sysmon. |
UtcTime |
metadata.event_timestamp |
|
EventID |
metadata.product_event_type |
If the EventID log field value is equal to 255 then, the metadata.product_event_type UDM field is set to Error - [255]. Else EventID log field is mapped to the metadata.product_event_type UDM field. |
RecordNumber |
metadata.product_log_id |
|
EventRecordID |
metadata.product_log_id |
|
Version |
metadata.product_version |
If the EventID log field value is equal to 4 then, Version log field is mapped to the metadata.product_version UDM field. |
QueryResults |
network.dns.answers.data |
The type_value and data_value fields are extracted from QueryResults log field using the Grok pattern. If the EventID log field value is equal to 22 then, the data_value log field is mapped to the network.dns.answers.data UDM field. |
QueryResults |
network.dns.answers.type |
The type_value and data_value fields are extracted from QueryResults log field using the Grok pattern. If the EventID log field value is equal to 22 then, the type_value log field is mapped to the network.dns.answers.type UDM field. |
QueryName |
network.dns.questions.name |
If the EventID log field value is equal to 22 then, QueryName log field is mapped to the network.dns.questions.name UDM field. |
Protocol |
network.ip_protocol |
If the EventID log field value is equal to 3 then, Protocol log field is mapped to the network.ip_protocol UDM field. |
ParentCommandLine |
principal.process.command_line |
If the EventID log field value is equal to 1 then, ParentCommandLine log field is mapped to the principal.process.command_line UDM field. |
User |
principal.administrative_domain |
The principal_user_userid and principal_administrative_domain fields are extracted from User log field using the Grok pattern. If the principal_administrative_domain log field value is not empty and the User log field value is not empty then, principal_administrative_domain extracted field is mapped to the principal.administrative_domain UDM field. Else Domain log field is mapped to the principal.administrative_domain UDM field. |
Domain |
principal.administrative_domain |
The principal_user_userid and principal_administrative_domain fields are extracted from User log field using the Grok pattern. If the principal_administrative_domain log field value is not empty and the User log field value is not empty then, principal_administrative_domain extracted field is mapped to the principal.administrative_domain UDM field. Else Domain log field is mapped to the principal.administrative_domain UDM field. |
HostName |
principal.hostname |
If the Hostname log field value is empty then, Computer log field is mapped to the principal.hostname UDM field. Else HostName log field is mapped to the principal.hostname UDM field and Hostname log field is mapped to the principal.hostname UDM field. |
Computer |
principal.hostname |
If the Hostname log field value is empty then, Computer log field is mapped to the principal.hostname UDM field. Else HostName log field is mapped to the principal.hostname UDM field and Hostname log field is mapped to the principal.hostname UDM field. |
HostName |
principal.asset.hostname |
If the Hostname log field value is empty then, Computer log field is mapped to the principal.asset.hostname UDM field. Else HostName log field is mapped to the principal.asset.hostname UDM field and Hostname log field is mapped to the principal.asset.hostname UDM field. |
Computer |
principal.asset.hostname |
If the Hostname log field value is empty then, Computer log field is mapped to the principal.asset.hostname UDM field. Else HostName log field is mapped to the principal.asset.hostname UDM field and Hostname log field is mapped to the principal.asset.hostname UDM field. |
SourceIp |
principal.ip |
If the EventID log field value is equal to 3 then, SourceIp log field is mapped to the principal.ip UDM field. |
SourcePort |
principal.port |
If the EventID log field value is equal to 3 then, SourcePort log field is mapped to the principal.port UDM field. |
ImageLoaded |
principal.process.file.full_path |
If the EventID log field value is equal to 6 then, ImageLoaded log field is mapped to the principal.process.file.full_path UDM field. |
Image |
principal.process.file.full_path |
If the EventID log field value contain one of the following values:
Image log field is mapped to the principal.process.file.full_path UDM field. |
SourceImage |
principal.process.file.full_path |
If the EventID log field value contain one of the following values:
SourceImage log field is mapped to the principal.process.file.full_path UDM field. |
ParentImage |
principal.process.file.full_path |
If the EventID log field value is equal to 1 then, ParentImage log field is mapped to the principal.process.file.full_path UDM field. |
ProcessId |
principal.process.pid |
If the EventID log field value contain one of the following values:
ExecutionProcessID log field value is not empty then, ExecutionProcessID log field is mapped to the principal.process.pid UDM field. Else ProcessId log field is mapped to the principal.process.pid UDM field. |
SourceProcessId |
principal.process.pid |
If the EventID log field value is equal to 8 then, SourceProcessId log field is mapped to the principal.process.pid UDM field. |
ParentProcessId |
principal.process.pid |
If the EventID log field value is equal to 1 then, ParentProcessId log field is mapped to the principal.process.pid UDM field. |
ProcessID |
observer.process.pid |
|
ProcessGuid |
principal.process.product_specific_process_id |
If the EventID log field value contain one of the following values:
principal.process.product_specific_process_id UDM field is set to SYSMON:%{ProcessGuid}. |
ParentProcessGuid |
principal.process.product_specific_process_id |
If the EventID log field value is equal to 1 then, principal.process.product_specific_process_id UDM field is set to SYSMON:%{ParentProcessGuid}. |
SourceProcessGuid |
principal.process.product_specific_process_id |
If the EventID log field value is equal to 8 then, principal.process.product_specific_process_id UDM field is set to SYSMON:%{SourceProcessGuid}. |
SourceProcessGUID |
principal.process.product_specific_process_id |
If the EventID log field value is equal to 10 then, principal.process.product_specific_process_id UDM field is set to SYSMON:%{SourceProcessGUID}. |
User |
principal.user.userid |
The principal_user_userid and principal_administrative_domain fields are extracted from User log field using the Grok pattern. If the EventID log field value is not equal to 24 and if the principal_user_userid log field value is not empty and the User log field value is not empty then, principal_user_userid extracted field is mapped to the principal.user.userid UDM field. |
ClientInfo |
principal.user.userid |
The host and user_id fields are extracted from ClientInfo log field using the Grok pattern. If the EventID log field value is equal to 24 and if the user_id log field value is not empty and the ClientInfo log field value is not empty then, user_id extracted field is mapped to the principal.user.userid UDM field. Else ClientInfo log field is mapped to the principal.user.userid UDM field. |
AccountName |
principal.user.userid |
The principal_user_userid and principal_administrative_domain fields are extracted from User log field using the Grok pattern. If the EventID log field value is not equal to 24 and if the principal_user_userid log field value is not empty and the User log field value is not empty then, principal_user_userid extracted field is mapped to the principal.user.userid UDM field. Else AccountName log field is mapped to the principal.user.userid UDM field. |
SourceUser |
principal.user.userid |
|
UserID |
principal.user.windows_sid |
|
Description |
security_result.description |
If the EventID log field value is equal to 255 and if the Description log field value is not equal to - then, Description log field is mapped to the security_result.description UDM field. |
RuleName |
security_result.rule_name |
|
EventID |
security_result.rule_name |
The security_result.rule_name UDM field is set to EventID: %{EventID}. |
|
security_result.severity |
If the Level log field value contain one of the following values:
Level log field value is equal to Information then, the security_result.severity UDM field is set to INFORMATIONAL. Else, If Level log field value is equal to 2 or the Level log field value is equal to Error then, the security_result.severity UDM field is set to ERROR. If the SeverityValue log field value does not contain one of the following values:
SeverityValue log field value contain one of the following values:
security_result.severity UDM field is set to INFORMATIONAL. Else, if SeverityValue log field value is equal to 4 then, the security_result.severity UDM field is set to ERROR. Else, if SeverityValue log field value is equal to 5 then, the security_result.severity UDM field is set to CRITICAL. |
Category |
about.labels[Category ID] |
The category_id and category_tag fields are extracted from Category log field using the Grok pattern. category_id extracted field is mapped to the about.labels.Category ID UDM field. |
QueryStatus |
security_result.summary |
If the EventID log field value is equal to 22 then, the security_result.summary UDM field is set to QueryStatus: %{QueryStatus}. |
ID |
security_result.summary |
If the EventID log field value is equal to 255 then, ID log field is mapped to the security_result.summary UDM field. |
Category |
security_result.summary |
The category_id and category_tag fields are extracted from Category log field using the Grok pattern. If the category_id log field value is not empty then, category_tag extracted field is mapped to the security_result.summary UDM field. Else Category log field is mapped to the security_result.summary UDM field. |
CurrentDirectory |
additional.fields[current_directory] |
If the EventID log field value is equal to 1 then, CurrentDirectory log field is mapped to the additional.fields.current_directory UDM field. |
OriginalFileName |
src.file.full_path |
If the EventID log field value is equal to 1 then, OriginalFileName log field is mapped to the src.file.full_path UDM field. |
TargetObject |
src.registry.registry_key |
If the EventID log field value is equal to 14 then, TargetObject log field is mapped to the src.registry.registry_key UDM field. |
Name |
target.application |
If the EventID log field value is equal to 19 then, Name log field is mapped to the target.application UDM field. If the EventID log field value is equal to 255 then, the target.application UDM field is set to Microsoft Sysmon. |
Description |
target.asset.software.description |
If the EventID log field value contain one of the following values:
Description log field value is not equal to - then, Description log field is mapped to the target.asset.software.description UDM field. |
Product |
target.asset.software.name |
If the EventID log field value contain one of the following values:
Product log field value is not equal to - then, Product log field is mapped to the target.asset.software.name UDM field. |
Company |
target.asset.software.vendor_name |
If the EventID log field value contain one of the following values:
Company log field value is not equal to - then, Company log field is mapped to the target.asset.software.vendor_name UDM field. |
FileVersion |
target.asset.software.version |
If the EventID log field value contain one of the following values:
FileVersion log field value is not equal to - then, FileVersion log field is mapped to the target.asset.software.version UDM field. |
EventNamespace |
target.file.full_path |
If the EventID log field value is equal to 19 then, EventNamespace log field is mapped to the target.file.full_path UDM field. |
Device |
target.file.full_path |
If the EventID log field value is equal to 9 then, Device log field is mapped to the target.file.full_path UDM field. |
TargetFilename |
target.file.full_path |
If the EventID log field value contain one of the following values:
TargetFilename log field is mapped to the target.file.full_path UDM field. |
DestinationHostname |
target.asset.hostname |
If the EventID log field value is equal to 3 then, DestinationHostname log field is mapped to the target.asset.hostname UDM field. |
ClientInfo |
target.asset.hostname |
The host and user_id fields are extracted from ClientInfo log field using the Grok pattern. The target_ip and host fields are extracted from ClientInfo log field using the Grok pattern. If the EventID log field value is equal to 24 then, host extracted field is mapped to the target.asset.hostname UDM field. |
DestinationHostname |
target.hostname |
If the EventID log field value is equal to 3 then, DestinationHostname log field is mapped to the target.hostname UDM field. |
ClientInfo |
target.hostname |
The host and user_id fields are extracted from ClientInfo log field using the Grok pattern. The target_ip and host fields are extracted from ClientInfo log field using the Grok pattern. If the EventID log field value is equal to 24 then, host extracted field is mapped to the target.hostname UDM field. |
ClientInfo |
target.ip |
The target_ip and host fields are extracted from ClientInfo log field using the Grok pattern. If the EventID log field value is equal to 24 then, target_ip extracted field is mapped to the target.ip UDM field. |
DestinationIp |
target.ip |
If the EventID log field value is equal to 3 then, DestinationIp log field is mapped to the target.ip UDM field. |
DestinationPort |
target.port |
If the EventID log field value is equal to 3 then, DestinationPort log field is mapped to the target.port UDM field. |
CommandLine |
target.process.command_line |
If the EventID log field value is equal to 1 then, CommandLine log field is mapped to the target.process.command_line UDM field. |
Configuration |
target.process.command_line |
If the EventID log field value is equal to 16 and if the ConfigurationFileHash log field value contain one of the following values:
Configuration log field is mapped to the target.process.command_line UDM field. |
ImageLoaded |
target.process.file.full_path |
If the EventID log field value is equal to 7 then, ImageLoaded log field is mapped to the target.process.file.full_path UDM field. |
TargetImage |
target.process.file.full_path |
If the EventID log field value contain one of the following values:
TargetImage log field is mapped to the target.process.file.full_path UDM field. |
Image |
target.process.file.full_path |
If the EventID log field value contain one of the following values:
Image log field is mapped to the target.process.file.full_path UDM field. |
Configuration |
target.process.file.full_path |
If the EventID log field value is equal to 16 and if the ConfigurationFileHash log field value does not contain one of the following values:
Configuration log field is mapped to the target.process.file.full_path UDM field. |
Hashes |
target.process.file.md5 |
The KV filter is used to extract the MD5 from the Hashes log field.If the EventID log field value contain one of the following values:
MD5 extracted field is mapped to the target.process.file.md5 UDM field. |
Hash |
target.process.file.md5 |
The KV filter is used to extract the MD5 from the Hashe log field.If the EventID log field value contain one of the following values:
MD5 extracted field is mapped to the target.process.file.md5 UDM field. |
ConfigurationFileHash |
target.process.file.md5 |
The KV filter is used to extract the MD5 from the ConfigurationFileHash log field.If the EventID log field value contain one of the following values:
MD5 extracted field is mapped to the target.process.file.md5 UDM field. |
Hashes |
target.process.file.sha1 |
The KV filter is used to extract the SHA1 from the Hashes log field.If the EventID log field value contain one of the following values:
SHA1 extracted field is mapped to the target.process.file.sha1 UDM field. |
Hash |
target.process.file.sha1 |
The KV filter is used to extract the SHA1 from the Hash log field.If the EventID log field value contain one of the following values:
SHA1 extracted field is mapped to the target.process.file.sha1 UDM field. |
ConfigurationFileHash |
target.process.file.sha1 |
The KV filter is used to extract the SHA1 from the ConfigurationFileHash log field.If the EventID log field value contain one of the following values:
SHA1 extracted field is mapped to the target.process.file.sha1 UDM field. |
Hashes |
target.process.file.sha256 |
The KV filter is used to extract the SHA256 from the Hashes log field.If the EventID log field value contain one of the following values:
SHA256 extracted field is mapped to the target.process.file.sha256 UDM field. |
Hash |
target.process.file.sha256 |
The KV filter is used to extract the SHA256 from the Hash log field.If the EventID log field value contain one of the following values:
SHA256 extracted field is mapped to the target.process.file.sha256 UDM field. |
ConfigurationFileHash |
target.process.file.sha256 |
The KV filter is used to extract the SHA256 from the ConfigurationFileHash log field.If the EventID log field value contain one of the following values:
SHA256 extracted field is mapped to the target.process.file.sha256 UDM field. |
Hashes |
target.process.file.file_metadata.pe.import_hash |
The KV filter is used to extract the IMPHASH from the Hashes log field.IMPHASH extracted field is mapped to the target.process.file.file_metadata.pe.import_hash UDM field. |
Hash |
target.process.file.file_metadata.pe.import_hash |
The KV filter is used to extract the IMPHASH from the Hash log field.IMPHASH extracted field is mapped to the target.process.file.file_metadata.pe.import_hash UDM field. |
ConfigurationFileHash |
target.process.file.file_metadata.pe.import_hash |
The KV filter is used to extract the IMPHASH from the ConfigurationFileHash log field.IMPHASH extracted field is mapped to the target.process.file.file_metadata.pe.import_hash UDM field. |
TargetProcessId |
target.process.pid |
If the EventID log field value contain one of the following values:
TargetProcessId log field is mapped to the target.process.pid UDM field. |
ProcessId |
target.process.pid |
If the EventID log field value contain one of the following values:
ExecutionProcessID log field value is not empty then, ExecutionProcessID log field is mapped to the target.process.pid UDM field. Else ProcessId log field is mapped to the target.process.pid UDM field. |
ProcessID |
target.process.pid |
If the EventID log field value contain one of the following values:
ExecutionProcessID log field value is not empty then, ExecutionProcessID log field is mapped to the target.process.pid UDM field. Else ProcessID log field is mapped to the target.process.pid UDM field. |
TargetProcessGuid |
target.process.product_specific_process_id |
If the EventID log field value is equal to 8 then, the target.process.product_specific_process_id UDM field is set to SYSMON:%{TargetProcessGuid}. |
TargetProcessGUID |
target.process.product_specific_process_id |
If the EventID log field value is equal to 10 then, the target.process.product_specific_process_id UDM field is set to SYSMON:%{TargetProcessGUID}. |
ProcessGuid |
target.process.product_specific_process_id |
If the EventID log field value contain one of the following values:
target.process.product_specific_process_id UDM field is set to SYSMON:%{ProcessGuid}. |
NewName |
target.registry.registry_key |
If the EventID log field value is equal to 14 then, NewName log field is mapped to the target.registry.registry_key UDM field. |
TargetObject |
target.registry.registry_key |
If the EventID log field value contain one of the following values:
TargetObject log field is mapped to the target.registry.registry_key UDM field. |
Details |
target.registry.registry_value_data |
If the EventID log field value is equal to 13 then, Details log field is mapped to the target.registry.registry_value_data UDM field. |
PreviousCreationUtcTime |
target.resource.attribute.labels.key[PreviousCreationUtcTime] |
If the EventID log field value is equal to 2 then, PreviousCreationUtcTime log field is mapped to the target.resource.attribute.labels UDM field. |
Archived |
target.resource.attribute.labels[Archived] |
If the EventID log field value contain one of the following values:
Archived log field is mapped to the target.resource.attribute.labels UDM field. |
Consumer |
target.resource.attribute.labels[Consumer] |
If the EventID log field value is equal to 21 then, Consumer log field is mapped to the target.resource.attribute.labels UDM field. |
CreationUtcTime |
target.resource.attribute.labels[CreationUtcTime] |
If the EventID log field value contain one of the following values:
CreationUtcTime log field is mapped to the target.resource.attribute.labels UDM field. |
IsExecutable |
target.resource.attribute.labels[IsExecutable] |
If the EventID log field value contain one of the following values:
IsExecutable log field is mapped to the target.resource.attribute.labels UDM field. |
Name |
target.resource.attribute.labels[Name] |
If the EventID log field value is equal to 20 then, Name log field is mapped to the target.resource.attribute.labels UDM field. |
Operation |
target.resource.attribute.labels[Operation] |
If the EventID log field value contain one of the following values:
Operation log field is mapped to the target.resource.attribute.labels UDM field. |
Signature |
target.resource.attribute.labels[Signature] |
If the EventID log field value contain one of the following values:
Signature log field is mapped to the target.resource.attribute.labels UDM field. |
SignatureStatus |
target.resource.attribute.labels[SignatureStatus] |
If the EventID log field value contain one of the following values:
SignatureStatus log field is mapped to the target.resource.attribute.labels UDM field. |
Signed |
target.resource.attribute.labels[Signed] |
If the EventID log field value contain one of the following values:
Signed log field is mapped to the target.resource.attribute.labels UDM field. |
Type |
target.resource.attribute.labels[Type] |
If the EventID log field value is equal to 20 then, Type log field is mapped to the target.resource.attribute.labels UDM field. |
Type |
additional.fields[Type] |
If the EventID log field value is equal to 25 then, Type log field is mapped to the additional.fields UDM field. |
State |
target.resource.name |
If the EventID log field value is equal to 4 then, State log field is mapped to the target.resource.name UDM field. |
CreationUtcTime |
target.resource.name |
If the EventID log field value is equal to 11 then, CreationUtcTime log field is mapped to the target.resource.name UDM field. |
PipeName |
target.resource.name |
If the EventID log field value contain one of the following values:
PipeName log field is mapped to the target.resource.name UDM field. |
Filter |
target.resource.name |
If the EventID log field value is equal to 21 then, Filter log field is mapped to the target.resource.name UDM field. |
Destination |
target.resource.name |
If the EventID log field value is equal to 20 then, Destination log field is mapped to the target.resource.name UDM field. |
Query |
target.resource.name |
If the EventID log field value is equal to 19 then, Query log field is mapped to the target.resource.name UDM field. |
GrantedAccess |
target.resource.name |
If the EventID log field value is equal to 10 and if the GrantedAccess log field value matches the regular expression pattern ^0x0080$ then, the target.resource.name UDM field is set to PROCESS_CREATE_PROCESS. Else, If the GrantedAccess log field value matches the regular expression pattern ^0x0002$ then, the target.resource.name UDM field is set to PROCESS_CREATE_THREAD. Else, If the GrantedAccess log field value matches the regular expression pattern ^0x0040$ then, the target.resource.name UDM field is set to PROCESS_DUP_HANDLE. Else, If the GrantedAccess log field value matches the regular expression pattern ^0x0400$ then, the target.resource.name UDM field is set to PROCESS_QUERY_INFORMATION. Else, If the GrantedAccess log field value matches the regular expression pattern ^0x1000$ then, the target.resource.name UDM field is set to PROCESS_QUERY_LIMITED_INFORMATION. Else, If the GrantedAccess log field value matches the regular expression pattern ^0x0200$ then, the target.resource.name UDM field is set to PROCESS_SET_INFORMATION. Else, If the GrantedAccess log field value matches the regular expression pattern ^0x0100$ then, the target.resource.name UDM field is set to PROCESS_SET_QUOTA. Else, If the GrantedAccess log field value matches the regular expression pattern ^0x0800$ and if the GrantedAccess log field value matches the regular expression pattern ^0x0001$ then, the target.resource.name UDM field is set to PROCESS_TERMINATE. Else, If the GrantedAccess log field value matches the regular expression pattern ^0x0008$ then, the target.resource.name UDM field is set to PROCESS_VM_OPERATION. Else, If the GrantedAccess log field value matches the regular expression pattern ^0x0010$ then, the target.resource.name UDM field is set to PROCESS_VM_READ. Else, If the GrantedAccess log field value matches the regular expression pattern ^0x0020$ then, the target.resource.name UDM field is set to PROCESS_VM_WRITE. Else, If the GrantedAccess log field value matches the regular expression pattern ^0x00100000L$ then, the target.resource.name UDM field is set to SYNCHRONIZE. |
|
target.resource.resource_type |
If the EventID log field value contain one of the following values:
target.resource.resource_type UDM field is set to SETTING. Else, If EventID log field value contain one of the following values:
target.resource.resource_type UDM field is set to PIPE. |
|
target.resource.resource_subtype |
If the EventID log field value is equal to 11 then, the target.resource.resource_subtype UDM field is set to CreationUtcTime. Else, If EventID log field value is equal to 10 then, the target.resource.resource_subtype UDM field is set to GrantedAccess. Else, If EventID log field value is equal to 4 then, the target.resource.resource_subtype UDM field is set to State. |
TargetUser |
target.user.userid |
|
|
network.direction |
If the EventID log field value is equal to 3 then, the network.direction UDM field is set to OUTBOUND. |
|
security_result.action |
If the EventID log field value is equal to 3 then, the security_result.action UDM field is set to ALLOW. |
ProviderGuid |
observer.asset_id |
ProviderGuid log field is mapped to the observer.asset_id UDM field. |
Keywords |
additional.fields[Keywords] |
|
ThreadID |
additional.fields[thread_id] |
|
ThreadID |
additional.fields[ThreadID] |
|
Channel |
additional.fields[channel] |
|
Opcode |
additional.fields[Opcode] |
|
LogonId |
principal.network.session_id |
|
LogonGuid |
additional.fields[LogonGuid] |
|
TerminalSessionId |
additional.fields[TerminalSessionId] |
|
SourcePortName |
additional.fields[SourcePortName] |
|
SourceIsIpv6 |
additional.fields[SourceIsIpv6] |
|
DestinationPortName |
additional.fields[DestinationPortName] |
|
DestinationIsIpv6 |
additional.fields[DestinationIsIpv6] |
|
Initiated |
additional.fields[Initiated] |
|
SchemaVersion |
additional.fields[SchemaVersion] |
|
CallTrace |
additional.fields[CallTrace] |
|
|
network.application_protocol |
If the EventID log field value is equal to 22 then, the network.application_protocol UDM field is set to DNS. |
NewThreadId |
additional.fields[NewThreadId] |
|
StartAddress |
additional.fields[StartAddress] |
|
StartFunction |
additional.fields[StartFunction] |
|
StartModule |
additional.fields[StartModule] |
|
ParentUser |
additional.fields[ParentUser] |
|
IntegrityLevel |
target.process.integrity_level_rid |
If the EventID log field value contain one of the following values:
IntegrityLevel log field value matches the regular expression pattern (?i)(Untrusted) then, the target.process.integrity_level_rid UDM field is set to 0. Else, if IntegrityLevel log field value matches the regular expression pattern (?i)(Low) then, the target.process.integrity_level_rid UDM field is set to 4096. Else, if IntegrityLevel log field value matches the regular expression pattern (?i)(Medium) then, the target.process.integrity_level_rid UDM field is set to 8192. Else, if IntegrityLevel log field value matches the regular expression pattern (?i)(High) then, the target.process.integrity_level_rid UDM field is set to 12288. Else, if IntegrityLevel log field value matches the regular expression pattern (?i)(System) then, the target.process.integrity_level_rid UDM field is set to 16384. Else, if IntegrityLevel log field value matches the regular expression pattern (?i)(Protected) then, the target.process.integrity_level_rid UDM field is set to 20480. |
IntegrityLevel |
principal.process.integrity_level_rid |
If the EventID log field value does not contain one of the following values:
IntegrityLevel log field value matches the regular expression pattern (?i)(Untrusted) then, the principal.process.integrity_level_rid UDM field is set to 0. Else, if IntegrityLevel log field value matches the regular expression pattern (?i)(Low) then, the principal.process.integrity_level_rid UDM field is set to 4096. Else, if IntegrityLevel log field value matches the regular expression pattern (?i)(Medium) then, the principal.process.integrity_level_rid UDM field is set to 8192. Else, if IntegrityLevel log field value matches the regular expression pattern (?i)(High) then, the principal.process.integrity_level_rid UDM field is set to 12288. Else, if IntegrityLevel log field value matches the regular expression pattern (?i)(System) then, the principal.process.integrity_level_rid UDM field is set to 16384. Else, if IntegrityLevel log field value matches the regular expression pattern (?i)(Protected) then, the principal.process.integrity_level_rid UDM field is set to 20480. |
Computer |
additional.fields[Computer] |
If the HostName log field value is not empty or the Hostname log field value is not empty then, Computer log field is mapped to the additional.fields.Computer UDM field. |
Task |
security_result.summary |
