Secara default, Cloud SQL untuk MySQL mengenkripsi konten pelanggan dalam penyimpanan. Cloud SQL untuk MySQL menangani enkripsi untuk Anda tanpa tindakan tambahan dari Anda. Opsi ini disebut Enkripsi default Google.
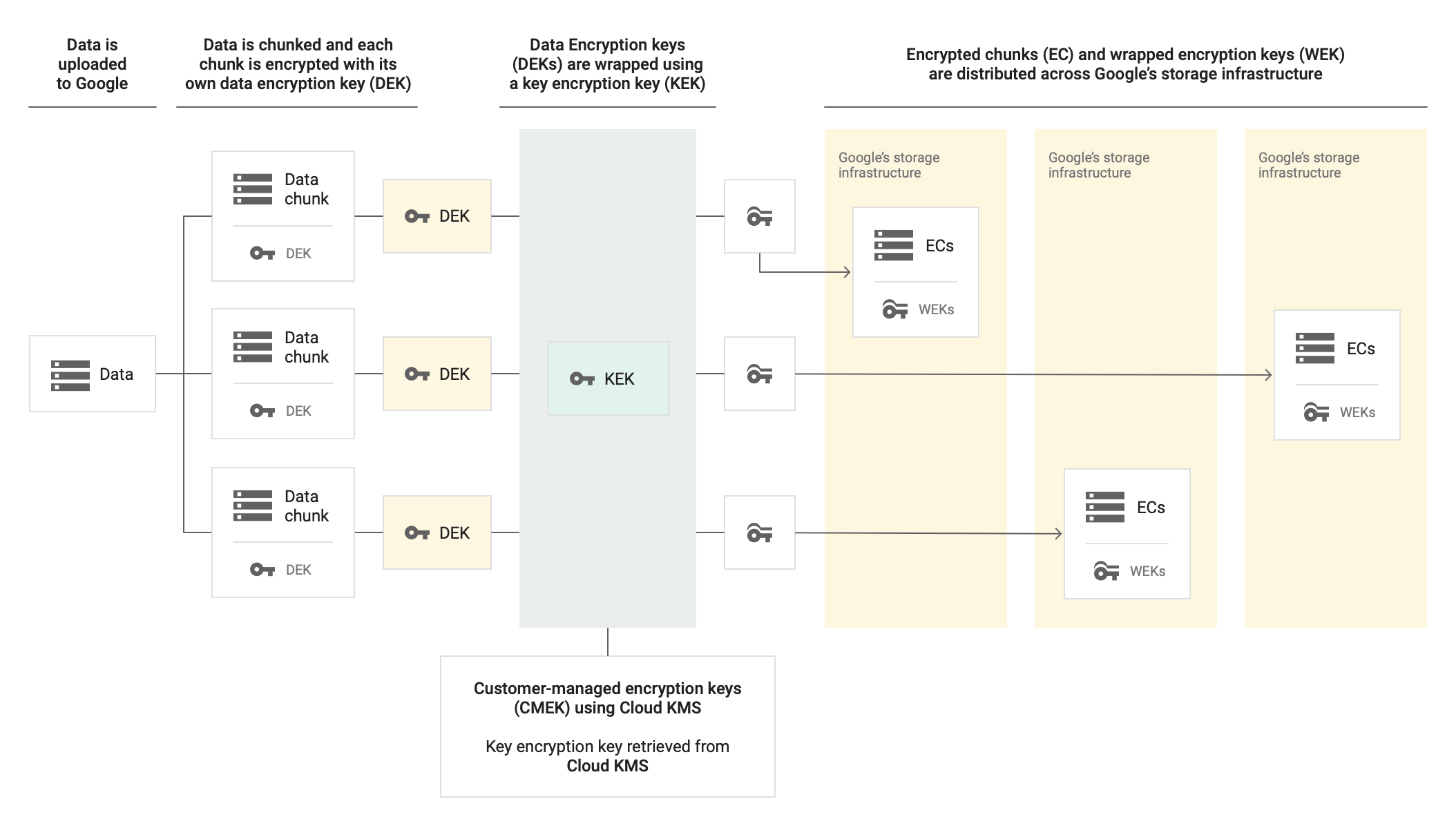
Jika ingin mengontrol kunci enkripsi, Anda dapat menggunakan kunci enkripsi yang dikelola pelanggan (CMEK) di Cloud KMS dengan layanan yang terintegrasi dengan CMEK, termasuk Cloud SQL untuk MySQL. Dengan menggunakan kunci Cloud KMS, Anda dapat mengontrol tingkat perlindungan, lokasi, jadwal rotasi, izin penggunaan dan akses, serta batasan kriptografisnya. Dengan Cloud KMS, Anda juga dapat melacak penggunaan kunci, melihat log audit, dan mengontrol siklus proses kunci. Alih-alih Google yang memiliki dan mengelola kunci enkripsi kunci (KEK) simetris yang melindungi data Anda, Anda yang mengontrol dan mengelola kunci ini di Cloud KMS.
Setelah Anda menyiapkan resource dengan CMEK, pengalaman mengakses resource Cloud SQL untuk MySQL Anda akan serupa dengan menggunakan enkripsi default Google. Untuk mengetahui informasi selengkapnya tentang opsi enkripsi, lihat Kunci enkripsi yang dikelola pelanggan (CMEK).
CMEK dengan Autokey Cloud KMS
Anda dapat membuat CMEK secara manual untuk melindungi resource Cloud SQL for MySQL atau menggunakan Kunci Otomatis Cloud KMS. Dengan Autokey, key ring dan kunci dibuat sesuai permintaan sebagai bagian dari pembuatan resource di Cloud SQL untuk MySQL. Agen layanan yang menggunakan kunci untuk operasi enkripsi dan dekripsi dibuat jika belum ada dan diberi peran Identity and Access Management (IAM) yang diperlukan. Untuk mengetahui informasi selengkapnya, lihat Ringkasan Autokey.
Autokey tidak membuat kunci untuk resource Cloud SQL for MySQL BackupRun. Saat
Anda membuat cadangan instance Cloud SQL untuk MySQL, cadangan akan
dienkripsi dengan kunci yang dikelola pelanggan dari instance utama.
Cloud SQL untuk MySQL hanya kompatibel dengan Autokey Cloud KMS saat membuat resource menggunakan Terraform atau REST API.
Untuk mempelajari cara menggunakan CMEK yang dibuat secara manual untuk melindungi resource Cloud SQL for MySQL Anda, lihat Menggunakan kunci enkripsi yang dikelola pelanggan (CMEK).
Untuk menggunakan CMEK yang dibuat oleh Autokey Cloud KMS untuk melindungi resource Cloud SQL for MySQL Anda, gunakan langkah-langkah yang disediakan untuk Secret Manager di Menggunakan Autokey dengan resource Secret Manager sebagai contoh.
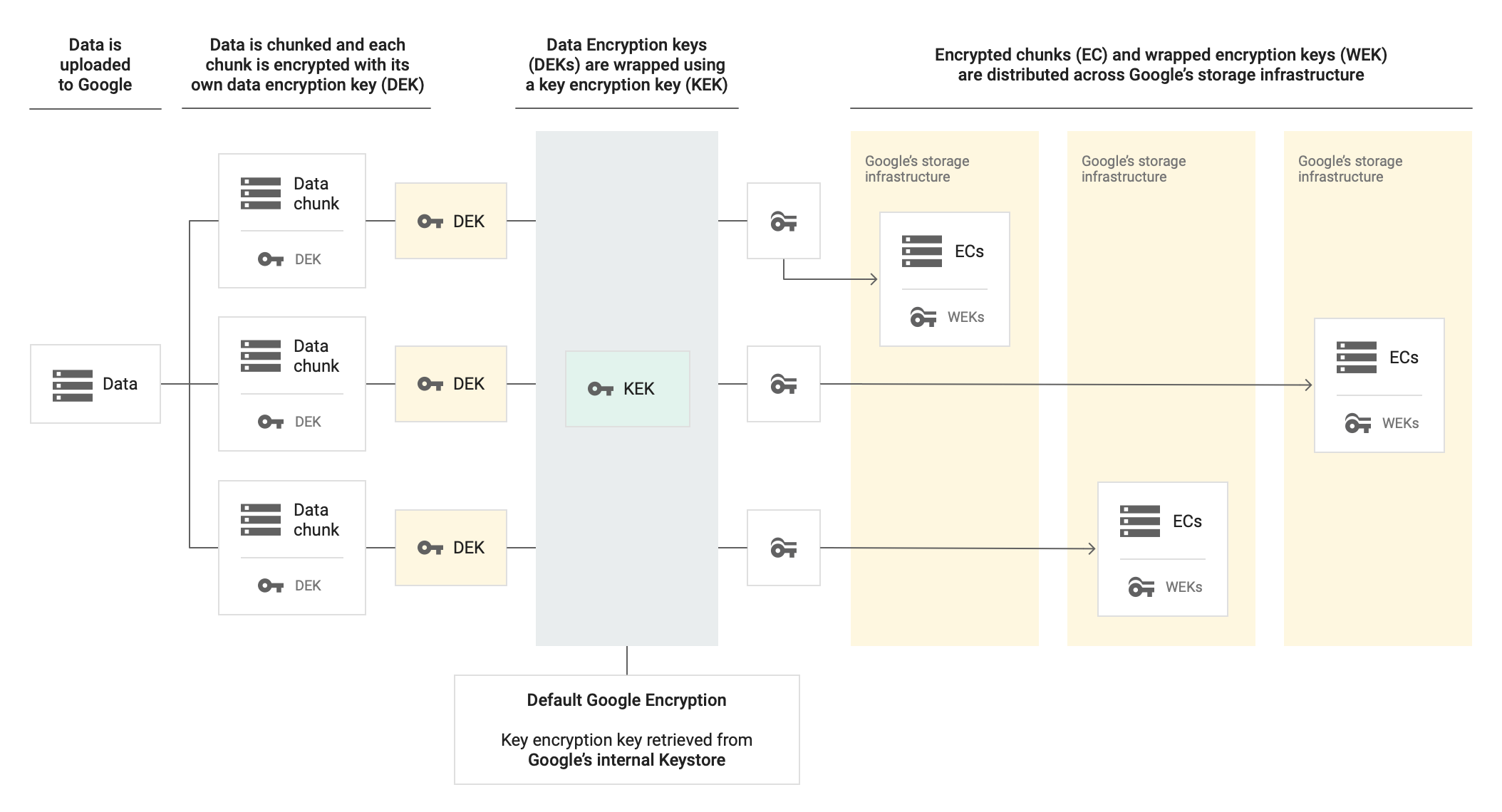
Enkripsi yang dikelola Google versus enkripsi yang dikelola pelanggan
Diagram di bawah menunjukkan cara kerja enkripsi data dalam penyimpanan di dalam instance Cloud SQL saat menggunakan enkripsi Google default dibandingkan kunci enkripsi yang dikelola pelanggan.
Tanpa CMEK
Dengan CMEK
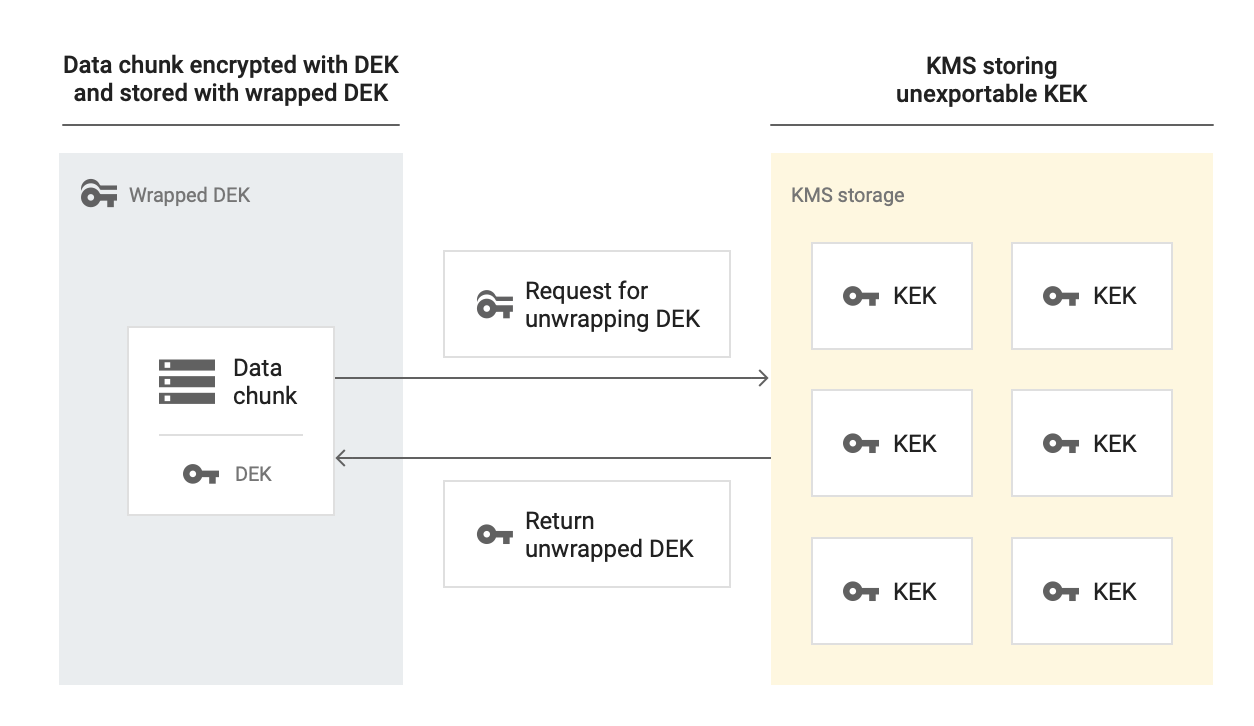
Saat mendekripsi data yang digabungkan dengan kunci enkripsi yang dikelola pelanggan, Cloud SQL menggunakan KEK untuk mendekripsi DEK dan DEK yang tidak dienkripsi untuk mendekripsi data dalam penyimpanan.
Kapan Cloud SQL berinteraksi dengan kunci CMEK?
| Operasi | Catatan |
| Pembuatan instance | Selama pembuatan instance, Anda mengonfigurasi instance untuk menggunakan kunci enkripsi yang dikelola pelanggan. |
| Pembuatan cadangan | Selama proses pencadangan untuk instance yang mendukung CMEK, kunci enkripsi yang dikelola pelanggan akan mengenkripsi data pengguna, seperti kueri dan respons pengguna. Cadangan dari instance yang mendukung CMEK akan mewarisi enkripsinya dengan kunci Cloud KMS yang sama dengan instance sumber. |
| Pemulihan instance | Selama pemulihan untuk instance yang mendukung CMEK, Cloud SQL menggunakan kunci tersebut untuk mengakses data pada instance cadangan yang sedang dipulihkan. Saat memulihkan ke instance lain, instance target dapat menggunakan kunci berbeda untuk enkripsi. |
| Pembuatan replika | Saat Anda membuat replika baca atau failover instance Cloud SQL di region yang sama, replika tersebut akan mewarisi CMEK dari instance induk. Jika Anda membuat replika baca atau failover di region yang berbeda, Anda harus memilih CMEK dari region lain. Setiap region menggunakan kumpulan kuncinya sendiri. |
| Pembuatan clone | Clone dari instance yang mendukung CMEK mewarisi enkripsi CMEK dengan kunci Cloud KMS yang sama dengan instance sumber. |
| Update instance | Selama update pada instance yang mendukung CMEK, Cloud SQL akan memeriksa kunci CMEK. |
Lokasi mana yang mendukung instance Cloud SQL yang mendukung CMEK?
CMEK tersedia di semua lokasi instance Cloud SQL.
Tentang akun layanan
Jika instance Cloud SQL telah mengaktifkan CMEK, Anda harus menggunakan akun layanan untuk meminta akses kunci dari Cloud KMS.
Untuk menggunakan kunci enkripsi yang dikelola pelanggan pada sebuah project, Anda harus memiliki akun layanan dan harus memberikan akses kunci enkripsi yang dikelola pelanggan ke akun layanan. Akun layanan harus ada di dalam project. Akun layanan dapat dilihat di semua region.
Jika Anda menggunakan Console untuk membuat instance, Cloud SQL akan otomatis membuat akun layanan saat Anda pertama kali memilih opsi Kunci yang dikelola pelanggan (jika akun layanan belum ada). Anda tidak perlu memiliki izin khusus pada akun pengguna Anda saat Cloud SQL secara otomatis membuat akun layanan.
Tentang kunci
Di Cloud KMS, Anda perlu membuat key ring dengan kunci kriptografis, yang dilengkapi dengan lokasi. Saat membuat instance Cloud SQL baru, Anda memilih kunci ini untuk mengenkripsi instance.
Anda perlu mengetahui ID kunci dan region kunci saat Anda membuat instance Cloud SQL baru yang menggunakan kunci enkripsi yang dikelola pelanggan. Anda harus menempatkan instance Cloud SQL baru di region yang sama dengan kunci enkripsi yang dikelola pelanggan yang terkait dengan instance tersebut. Anda dapat membuat satu project untuk kunci dan instance Cloud SQL, atau project yang berbeda untuk masing-masing kunci.
Kunci enkripsi yang dikelola pelanggan menggunakan format berikut:
projects/[KMS_PROJECT_ID]/locations/[LOCATION]/keyRings/[KEY_RING]/cryptoKeys/[KEY_NAME]
Jika Cloud SQL tidak dapat mengakses kunci (misalnya jika Anda menonaktifkan versi kunci), Cloud SQL akan menangguhkan instance. Setelah kunci dapat diakses kembali, Cloud SQL akan otomatis melanjutkan instance.
Saat Anda merotasi kunci, instance yang dienkripsi dengan kunci tersebut tidak secara otomatis terenkripsi ulang dengan versi kunci utama yang baru. Anda dapat mengenkripsi ulang instance atau replika utama CMEK yang ada dengan versi kunci utama yang baru. Untuk mengetahui informasi selengkapnya tentang cara mengenkripsi ulang instance atau replika Cloud SQL setelah rotasi kunci, lihat Enkripsi ulang instance atau replika berkemampuan CMEK yang ada.
Pengelola kunci eksternal
Anda dapat menggunakan kunci yang disimpan di pengelola kunci eksternal, seperti Fortanix, Futurex, atau Thales, sebagai kunci enkripsi yang dikelola pelanggan. Untuk mempelajari cara menggunakan kunci eksternal dengan Cloud KMS, lihat Cloud External Key Manager (Cloud EKM).
Justifikasi Akses KunciKey Access Justifications
Anda dapat menggunakan Key Access Justifications sebagai bagian dari Cloud EKM. Key Access Justifications memungkinkan Anda melihat alasan setiap permintaan Cloud EKM. Selain itu, berdasarkan justifikasi yang diberikan, Anda dapat otomatis menyetujui atau menolak permintaan. Untuk mempelajari lebih lanjut, lihat Ringkasan Justifikasi Akses Kunci.
Dengan demikian, Key Access Justifications memberikan kontrol tambahan atas data Anda dengan memberikan justifikasi untuk setiap upaya untuk mendekripsi data.
Untuk informasi terkait tentang penggunaan kunci Anda dengan instance Cloud SQL, lihat Membuat instance Cloud SQL dengan CMEK.
Bagaimana cara membuat data terenkripsi CMEK tidak dapat diakses secara permanen?
Anda mungkin ingin menghancurkan data yang dienkripsi dengan CMEK secara permanen. Untuk melakukannya, Anda menghancurkan versi kunci enkripsi yang dikelola pelanggan. Anda tidak dapat menghancurkan key ring atau kunci, tetapi Anda dapat menghancurkan versi kunci dari kunci tersebut.
Bagaimana cara saya mengekspor serta mengimpor data dari dan ke instance yang mendukung CMEK?
Jika ingin data Anda tetap dienkripsi dengan kunci yang dikelola pelanggan selama ekspor atau impor, Anda harus menetapkan kunci enkripsi yang dikelola pelanggan di bucket Cloud Storage sebelum mengekspor data ke dalamnya. Tidak ada persyaratan atau batasan khusus untuk mengimpor data ke instance baru jika data sebelumnya disimpan di instance yang diaktifkan dengan kunci enkripsi yang dikelola pelanggan.
Pembatasan
Pembatasan berikut berlaku saat menggunakan kunci enkripsi yang dikelola pelanggan:
- Anda tidak dapat mengaktifkan kunci enkripsi yang dikelola pelanggan pada instance yang sudah ada.
- Anda tidak dapat menetapkan kunci yang berbeda ke replika di region yang sama dengan instance utama. Untuk replika lintas-region, Anda perlu membuat kunci baru untuk region replika.
- Anda tidak dapat menetapkan kunci berbeda pada clone.
- Anda tidak dapat menggunakan kunci enkripsi yang dikelola pelanggan untuk mengenkripsi:
- Server eksternal (instance utama eksternal dan replika eksternal)
- Metadata instance, seperti ID instance, versi database, jenis mesin, flag, jadwal pencadangan, dll.
- Anda tidak dapat menggunakan kunci enkripsi yang dikelola pelanggan untuk mengenkripsi data pengguna selama pengiriman, seperti kueri dan respons pengguna.
- Setelah membuat instance Cloud SQL, Anda tidak dapat mengubah jenis kunci enkripsi. Anda tidak dapat beralih dari kunci Google-owned and Google-managed encryption key ke kunci Cloud Key Management Service (KMS), atau sebaliknya.
Langkah berikutnya
- Pelajari enkripsi dalam penyimpanan di Google Cloud Platform.
- Pelajari cara membuat instance dengan CMEK yang diaktifkan.
- Pelajari Cloud Key Management Service (Cloud KMS).
- Pelajari Kuota untuk resource Cloud KMS.
- Pelajari akun layanan IAM.
- Pelajari cara menambahkan justifikasi akses kunci ke kunci Anda.
- Temukan produk lain yang menggunakan CMEK.

