This document provides an overview of a push subscription, its workflow, and associated properties.
In push delivery, Pub/Sub initiates requests to your subscriber application to deliver messages. Messages are delivered to a publicly addressable server or a webhook, such as an HTTPS POST request.
Push subscriptions minimize dependencies on Pub/Sub-specific client libraries and authentication mechanisms. They also work well with serverless and autoscaling service technologies, such as Cloud Run functions, Cloud Run, and Google Kubernetes Engine.
Before you begin
Before reading this document, ensure that you are familiar with the following:
How Pub/Sub works and the different Pub/Sub terms.
The different kinds of subscriptions that Pub/Sub supports and why you might want to use a push subscription.
Push subscription workflow
In a push subscription, a Pub/Sub server initiates a request to your subscriber client to deliver messages.
The following image shows the workflow between a subscriber client and a push subscription.
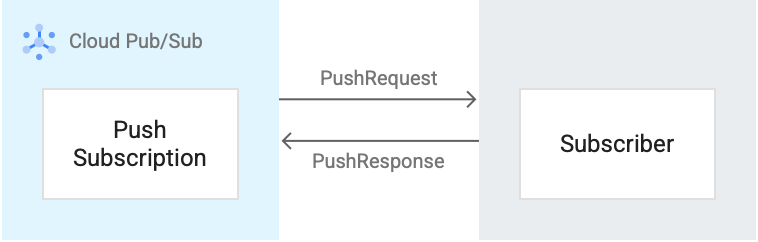
Here's a brief description of the workflow that references Figure 3:
- The Pub/Sub server sends each message as an HTTPS request to
the subscriber client at a pre-configured endpoint. This request is shown as
a
PushRequestin the image. - The endpoint acknowledges the message by returning an HTTP success status
code. A non-success response indicates that Pub/Sub must
resend the messages. This response is shown as a
PushResponsein the image. - Pub/Sub dynamically adjusts the rate of push requests based on the rate at which it receives success responses.
Properties of a push subscription
The properties that you configure for a push subscription determines how you write messages to your subscription. For more information, see subscription properties.
How push endpoints receive messages
When Pub/Sub delivers a message to a push endpoint, you can choose to send it wrapped or unwrapped. By default, messages are sent wrapped.
- Wrapped. Pub/Sub sends the message in the JSON body of a
POSTrequest. - Unwrapped. Pub/Sub sends the raw message data directly as the HTTP body.
The following examples show a wrapped body of a JSON POST request to a push
endpoint that contains the string Hello there in the message.data field
The body of a POST request is a JSON object. The message data is in the
message.data field and is base64-encoded.
Example of a request with the minimum values
{ "message": { "data": "SGVsbG8gQ2xvdWQgUHViL1N1YiEgSGVyZSBpcyBteSBtZXNzYWdlIQ==", "messageId": "2070443601311540", "message_id": "2070443601311540", "publishTime": "2021-02-26T19:13:55.749Z", "publish_time": "2021-02-26T19:13:55.749Z" }, "subscription": "projects/myproject/subscriptions/mysubscription" }
Example of a request with the maximum values
Note that this example shows the current maximum values, which might change over time. Additionally, the attributes map can contain a variety of values.
{ "deliveryAttempt": 5, "message": { "attributes": { "key": "value" }, "data": "SGVsbG8gQ2xvdWQgUHViL1N1YiEgSGVyZSBpcyBteSBtZXNzYWdlIQ==", "messageId": "2070443601311540", "message_id": "2070443601311540", "orderingKey": "key", "publishTime": "2021-02-26T19:13:55.749Z", "publish_time": "2021-02-26T19:13:55.749Z" }, "subscription": "projects/myproject/subscriptions/mysubscription" }
To receive messages from push subscriptions, use a webhook and process the
POST requests that Pub/Sub sends to the push endpoint. For more
information about processing these POST requests in App Engine, see
Writing and responding to Pub/Sub messages.
After you receive a push request, return an HTTP status code. To acknowledge the message, return one of the following status codes:
102200201202204
To send a negative acknowledgment for the message, return any other status code. If you send a negative acknowledgment or the acknowledgment deadline expires, Pub/Sub resends the message. You can't modify the acknowledgment deadline of individual messages that you receive from push subscriptions.
Authentication for push subscriptions
If a push subscription uses authentication, the Pub/Sub service signs a JWT and sends the JWT in the authorization header of the push request.
For more information about setting up authentication, see Authenticate push requests.
Stop and resume message delivery
To temporarily stop Pub/Sub from sending requests to the push endpoint, change the subscription to pull. The changeover can take several minutes to take effect.
To resume push delivery, set the URL to a valid endpoint again. To permanently stop delivery, delete the subscription.
Push backoff
If a push subscriber sends too many negative acknowledgments, Pub/Sub might start delivering messages using a push backoff. When Pub/Sub uses a push backoff, it stops delivering messages for a predetermined amount of time. This time span can range between 100 milliseconds to 60 seconds. After the time has elapsed, Pub/Sub starts delivering messages again.
Push backoff uses an exponential backoff algorithm to determine the delay Pub/Sub that uses between sending messages. This amount of time is calculated based on the number of negative acknowledgments that push subscribers send.
For example, if a push subscriber receives five messages per second and sends one negative acknowledgment per second, Pub/Sub delivers messages approximately every 500 milliseconds. Or, if the push subscriber sends five negative acknowledgments per second, Pub/Sub delivers messages every 30 through 60 seconds.
Note the following considerations about push backoff:
- Push backoff can't be turned on or off. You also can't modify the values used to calculate the delay.
- Push backoff triggers on the following actions:
- When a negative acknowledgment is received.
- When the acknowledgment deadline of a message expires.
- Push backoff applies to all the messages in a subscription (global).
Delivery rate
Pub/Sub adjusts the number of concurrent push requests using a slow-start algorithm. The maximum allowed number of concurrent push requests is the push window. The push window increases on any successful delivery and decreases on any failure. The system starts with a small single-digit window size.
When a subscriber acknowledges messages, the window increases exponentially. For subscriptions where subscribers acknowledge greater than 99% of messages and average less than one second of push request latency, the push window should expand enough to keep up with any publish throughput.
The push request latency includes the following:
The round-trip network latency between Pub/Sub servers and the push endpoint
The processing time of the subscriber
After 3,000 outstanding messages per region, the window increases linearly to prevent the push endpoint from receiving too many messages. If the average latency exceeds one second or the subscriber acknowledges less than 99% of requests, the window decreases to the lower limit of 3,000 outstanding messages.
For more information about the metrics you can use to monitor push delivery, see Monitoring push subscriptions.
Quotas and limits
Push subscriptions are subject to a set of quotas and resource limits.
What's next
Create a push subscription for your topic.
Troubleshoot a push subscription.
Create or modify a subscription with gcloud CLI.
Create or modify a subscription with REST APIs.
Create or modify a subscription with RPC APIs.
