本頁面說明如何為傳統應用程式負載平衡器設定 HTTP 至 HTTPS 的重新導向。本頁面僅適用於傳統版應用程式負載平衡器。如果您使用的是其他模式的負載平衡器,請參閱下列任一頁面:
本範例說明如何使用網址對應重新導向,將所有要求從 HTTP 重新導向至 HTTPS。本例說明如何使用眾所皆知的通訊埠 80 (HTTP) 和 443 (HTTPS) 設定重新導向。不過,您不必使用這些特定連接埠號碼。應用程式負載均衡器的每個轉送規則都可以參照 1 到 65535 之間的單一連接埠。
HTTPS 會使用 TLS (SSL) 加密 HTTP 要求和回應,讓系統更安全。使用 HTTPS 的網站網址開頭為 https://,而非 http://。
適用於新的 HTTPS 應用程式負載平衡器
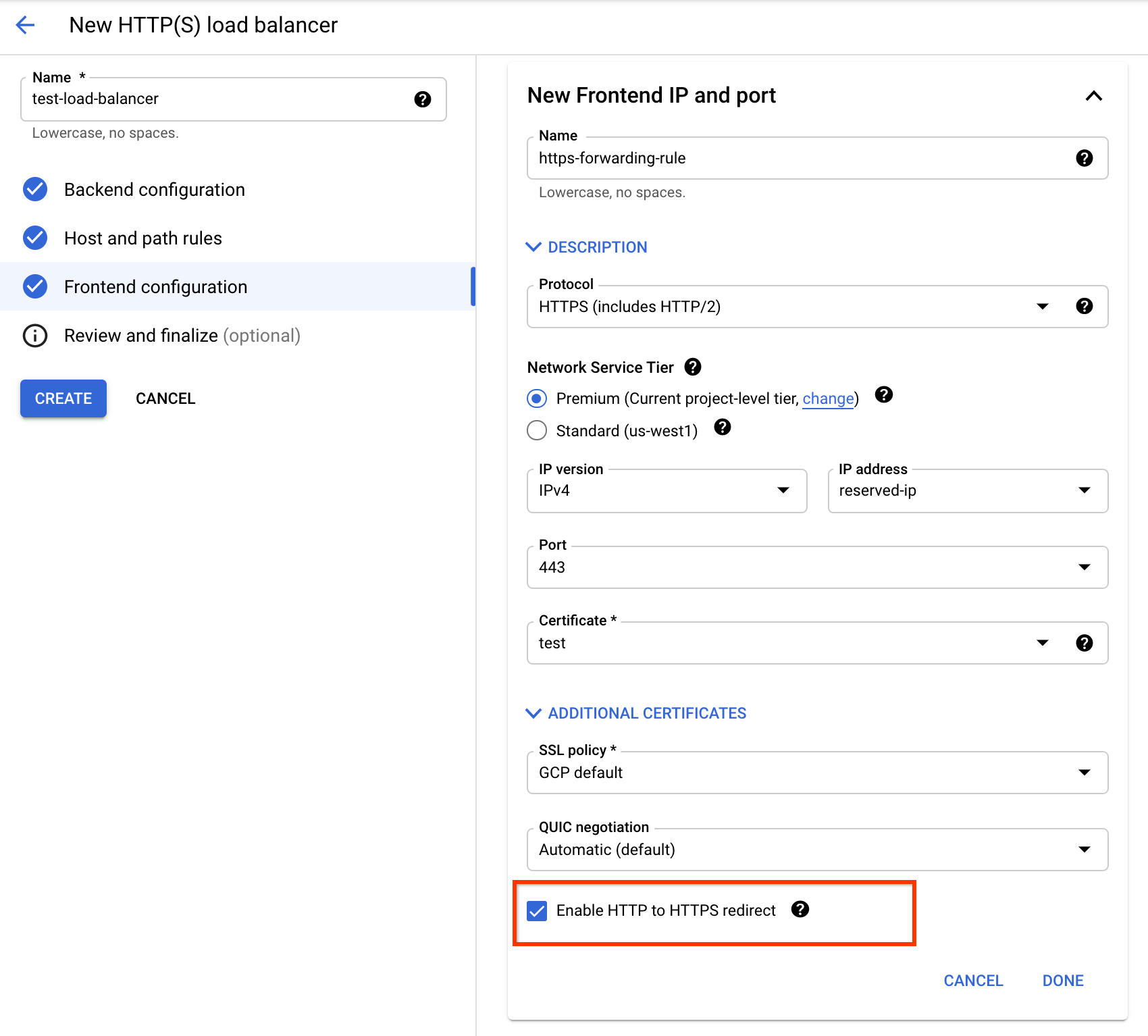
如果您要建立新的 HTTPS 應用程式負載平衡器,可以使用Google Cloud 主控台設定 HTTP 至 HTTPS 的重新導向。
建立負載平衡器前端時,請按照下列步驟操作:
- 在 Google Cloud 控制台中,前往負載平衡器的設定頁面。
- 在「負載平衡器名稱」中輸入名稱。
- 按一下「前端設定」。
- 在「Protocol」中,選取「HTTPS (含 HTTP/2)」。
- 在「IP address」(IP 位址) 部分,按一下「Create IP address」(建立 IP 位址)。輸入新的靜態 IP 位址名稱,然後按一下「保留」。
- 在「Certificate」部分,選取 SSL 憑證。
- 如要建立重新導向,請選取「啟用從 HTTP 重新導向至 HTTPS」核取方塊。
- 按一下 [完成]。
- 完成後端和其他必要設定。
- 按一下 [建立]。
您必須選取 HTTPS 通訊協定,並使用已保留的 IP 位址 (非暫時性),才能選取核取方塊。
視後端類型而定,請按照下列指南中的 Google Cloud 控制台操作說明完成設定:
設定「Enable HTTP to HTTPS Redirect」核取方塊後,系統會自動建立額外的部分 HTTP 負載平衡器,其中包含網址對應、轉送規則和目標 HTTP Proxy。這個部分 HTTP 負載平衡器會使用與 HTTPS 負載平衡器相同的 IP 位址,並將 HTTP 要求重新導向至負載平衡器的 HTTPS 前端。它會使用 301 Moved Permanently 做為預設的重新導向回應碼。
建立 HTTPS 負載平衡器後,您可以在負載平衡器清單中看到部分 HTTP 負載平衡器,並附有 -redirect 後置字串。請按照「測試 HTTP 到 HTTPS 重新導向」一文中的步驟測試設定。
現有負載平衡器
如果您已在通訊埠 443 上提供 HTTPS 流量的 HTTPS 應用程式負載平衡器 (在此稱為 LB1),則必須使用以下設定建立部分 HTTP 應用程式負載平衡器 (在此稱為 LB2):
- LB1 使用的相同前端 IP 位址
- 在網址對應中設定的重新導向
這個部分 HTTP 負載平衡器會使用與 HTTPS 負載平衡器相同的 IP 位址,並將 HTTP 要求重新導向至負載平衡器的 HTTPS 前端。
下圖說明此架構。

將流量重新導向至 HTTPS 負載平衡器
確認 HTTPS 負載平衡器 (LB1) 運作正常後,您可以建立部分 HTTP 負載平衡器 (LB2),並將前端設定為將流量重新導向至 LB1。
本範例使用 301 回應碼。您可以改用其他回應碼。
如要使用 gcloud 設定重新導向,您必須匯入 YAML 檔案,並確認目標 HTTP Proxy 會將流量導向至重新導向的網址對應。如果您使用的是 Google Cloud 控制台,系統會自動處理這項作業。
Google Cloud 控制台不支援區域性外部應用程式負載平衡器。
gcloud
- 建立 YAML 檔案
/tmp/web-map-http.yaml。本範例使用 MOVED_PERMANENTLY_DEFAULT 做為回應碼。 - 驗證網址對應。
- 匯入 YAML 檔案,建立 HTTP 負載平衡器的網址對應。這個網址對應的名稱為
web-map-http。 - 確認網址對應已更新。HTTP 負載平衡器的網址對應應如下所示:
- 使用
web-map-http做為網址對應,建立新的目標 HTTP Proxy 或更新現有目標 HTTP Proxy。 - 建立轉送規則,將傳入要求轉送至 Proxy。
--address標記會指定lb-ipv4-1,這是用於外部 HTTPS 負載平衡器的 IP 位址。
kind: compute#urlMap name: web-map-http defaultUrlRedirect: redirectResponseCode: MOVED_PERMANENTLY_DEFAULT httpsRedirect: True tests: - description: Test with no query parameters host: example.com path: /test/ expectedOutputUrl: https://example.com/test/ expectedRedirectResponseCode: 301 - description: Test with query parameters host: example.com path: /test/?parameter1=value1¶meter2=value2 expectedOutputUrl: https://example.com/test/?parameter1=value1¶meter2=value2 expectedRedirectResponseCode: 301
gcloud compute url-maps validate --source /tmp/web-map-http.yaml
如果測試通過且指令輸出成功訊息,請將變更儲存至網址對應項目。
gcloud compute url-maps import web-map-http \
--source /tmp/web-map-http.yaml \
--global
如果您要更新現有的網址對應,系統會顯示下列提示:
Url Map [web-map-http] will be overwritten.
Do you want to continue (Y/n)?
如要繼續操作,請按下 Y 鍵。
gcloud compute url-maps describe web-map-http
creationTimestamp: '2020-03-23T10:53:44.976-07:00' defaultUrlRedirect: httpsRedirect: true redirectResponseCode: MOVED_PERMANENTLY_DEFAULT fingerprint: 3A5N_RLrED8= id: '2020316695093397831' kind: compute#urlMap name: web-map-http selfLink: https://www.googleapis.com/compute/v1/projects/PROJECT_ID/global/urlMaps/web-map-http
gcloud compute target-http-proxies create http-lb-proxy \
--url-map=web-map-http \
--global
gcloud compute target-http-proxies update http-lb-proxy \
--url-map=web-map-http \
--global
gcloud compute forwarding-rules create http-content-rule \
--load-balancing-scheme=EXTERNAL \
--network-tier=PREMIUM \
--address=lb-ipv4-1 \
--global \
--target-http-proxy=http-lb-proxy \
--ports=80
新增自訂 HSTS 標頭
將 HTTP Strict-Transport-Security 標頭新增至 HTTPS 負載平衡器的後端服務後,負載平衡器會將自訂標頭傳送至用戶端,這樣下次用戶端嘗試透過 HTTP 存取網址時,瀏覽器就會重新導向要求。標頭設定如下:
- 標頭名稱:
Strict-Transport-Security - 標頭值:
max-age=31536000; includeSubDomains; preload
如要將自訂標頭新增至後端服務設定,請使用 --custom-response-header 標記。
gcloud compute backend-services update BACKEND_SERVICE_NAME_LB1 \
--global \
--custom-response-header='Strict-Transport-Security:max-age=31536000; includeSubDomains; preload'
詳情請參閱「建立自訂標頭」。
測試 HTTP 至 HTTPS 的重新導向
請記下您為兩個負載平衡器使用的保留 IP 位址。
gcloud compute addresses describe lb-ipv4-1
--format="get(address)"
--global
在這個範例中,假設保留的 IP 位址為 34.98.77.106。http://34.98.77.106/ 網址會重新導向至 https://34.98.77.106/。
幾分鐘後,您可以執行下列 curl 指令來測試這項功能。
curl -v http://hostname.com
輸出內容範例:
* Connected to 34.98.77.106 (34.98.77.106) port 80 (#0) > GET / HTTP/1.1 > Host: hostname.com > User-Agent: curl/7.64.0 > Accept: */* > < HTTP/1.1 301 Moved Permanently < Cache-Control: private < Content-Type: text/html; charset=UTF-8 < Referrer-Policy: no-referrer < Location: https://hostname.com < Content-Length: 220 < Date: Fri, 30 Jul 2021 21:32:25 GMT < <HTML><HEAD><meta http-equiv="content-type" content="text/html;charset=utf-8"> <TITLE>301 Moved</TITLE></HEAD><BODY> <H1>301 Moved</H1> The document has moved <A HREF="https://hostname.com">here</A>. </BODY></HTML> * Connection #0 to host hostname.com left intact
相關程序
如需 GKE 的相關資訊,請參閱 GKE 說明文件中的 HTTP 至 HTTPS 重新導向。
如需內部應用程式負載平衡器的相關資訊,請參閱「為內部應用程式負載平衡器設定 HTTP 至 HTTPS 重新導向」。
如需瞭解其他類型的重新導向,請參閱「網址重新導向」。

