Standardmäßig verschlüsselt Google Cloud Daten im Ruhezustand automatisch mit von Google verwalteten Verschlüsselungsschlüsseln.
Wenn Sie bestimmte Compliance- oder behördliche Anforderungen in Bezug auf die Schlüssel zum Schutz Ihrer Daten haben, können Sie für Document AI vom Kunden verwaltete Verschlüsselungsschlüssel (Customer-Managed Encryption Keys, CMEK) verwenden. Anstatt die Verschlüsselungsschlüssel zum Schutz Ihrer Daten von Google verwalten zu lassen, wird Ihr Document AI-Prozessor mit einem Schlüssel geschützt, den Sie in Cloud Key Management Service (KMS) steuern und verwalten.
In diesem Leitfaden wird CMEK für Document AI beschrieben. Weitere allgemeine Informationen zu CMEK einschließlich ihrer Aktivierung finden Sie in der Dokumentation zum Cloud Key Management Service.
Voraussetzungen
Der Document AI-Dienst-Agent muss die Rolle „Cloud KMS CryptoKey Encrypter/Decrypter“ für den verwendeten Schlüssel haben.
Im folgenden Beispiel wird eine Rolle zugewiesen, die den Zugriff auf einen Cloud KMS-Schlüssel ermöglicht:
gcloud
gcloud kms keys add-iam-policy-binding key \
--keyring key-ring \
--location location \
--project key_project_id \
--member serviceAccount:service-project_number@gcp-sa-prod-dai-core.iam.gserviceaccount.com \
--role roles/cloudkms.cryptoKeyEncrypterDecrypter
Ersetzen Sie key durch den Namen des Schlüssels. Ersetzen Sie key-ring durch den Namen des Schlüsselbunds, in dem sich der Schlüssel befindet. Ersetzen Sie location durch den Document AI-Standort für den Schlüsselbund. Ersetzen Sie key_project_id durch das Projekt für den Schlüsselbund. Ersetzen Sie project_number durch die Nummer Ihres Projekts.
C#
Weitere Informationen finden Sie in der Referenzdokumentation zur Document AI C# API.
Richten Sie zur Authentifizierung bei Document AI Standardanmeldedaten für Anwendungen ein. Weitere Informationen finden Sie unter Authentifizierung für eine lokale Entwicklungsumgebung einrichten.
Go
Weitere Informationen finden Sie in der Referenzdokumentation zur Document AI Go API.
Richten Sie zur Authentifizierung bei Document AI Standardanmeldedaten für Anwendungen ein. Weitere Informationen finden Sie unter Authentifizierung für eine lokale Entwicklungsumgebung einrichten.
Java
Weitere Informationen finden Sie in der Referenzdokumentation zur Document AI Java API.
Richten Sie zur Authentifizierung bei Document AI Standardanmeldedaten für Anwendungen ein. Weitere Informationen finden Sie unter Authentifizierung für eine lokale Entwicklungsumgebung einrichten.
Node.js
Weitere Informationen finden Sie in der Referenzdokumentation zur Document AI Node.js API.
Richten Sie zur Authentifizierung bei Document AI Standardanmeldedaten für Anwendungen ein. Weitere Informationen finden Sie unter Authentifizierung für eine lokale Entwicklungsumgebung einrichten.
PHP
Weitere Informationen finden Sie in der Referenzdokumentation zur Document AI PHP API.
Richten Sie zur Authentifizierung bei Document AI Standardanmeldedaten für Anwendungen ein. Weitere Informationen finden Sie unter Authentifizierung für eine lokale Entwicklungsumgebung einrichten.
Python
Weitere Informationen finden Sie in der Referenzdokumentation zur Document AI Python API.
Richten Sie zur Authentifizierung bei Document AI Standardanmeldedaten für Anwendungen ein. Weitere Informationen finden Sie unter Authentifizierung für eine lokale Entwicklungsumgebung einrichten.
Ruby
Weitere Informationen finden Sie in der Referenzdokumentation zur Document AI Ruby API.
Richten Sie zur Authentifizierung bei Document AI Standardanmeldedaten für Anwendungen ein. Weitere Informationen finden Sie unter Authentifizierung für eine lokale Entwicklungsumgebung einrichten.
CMEK verwenden
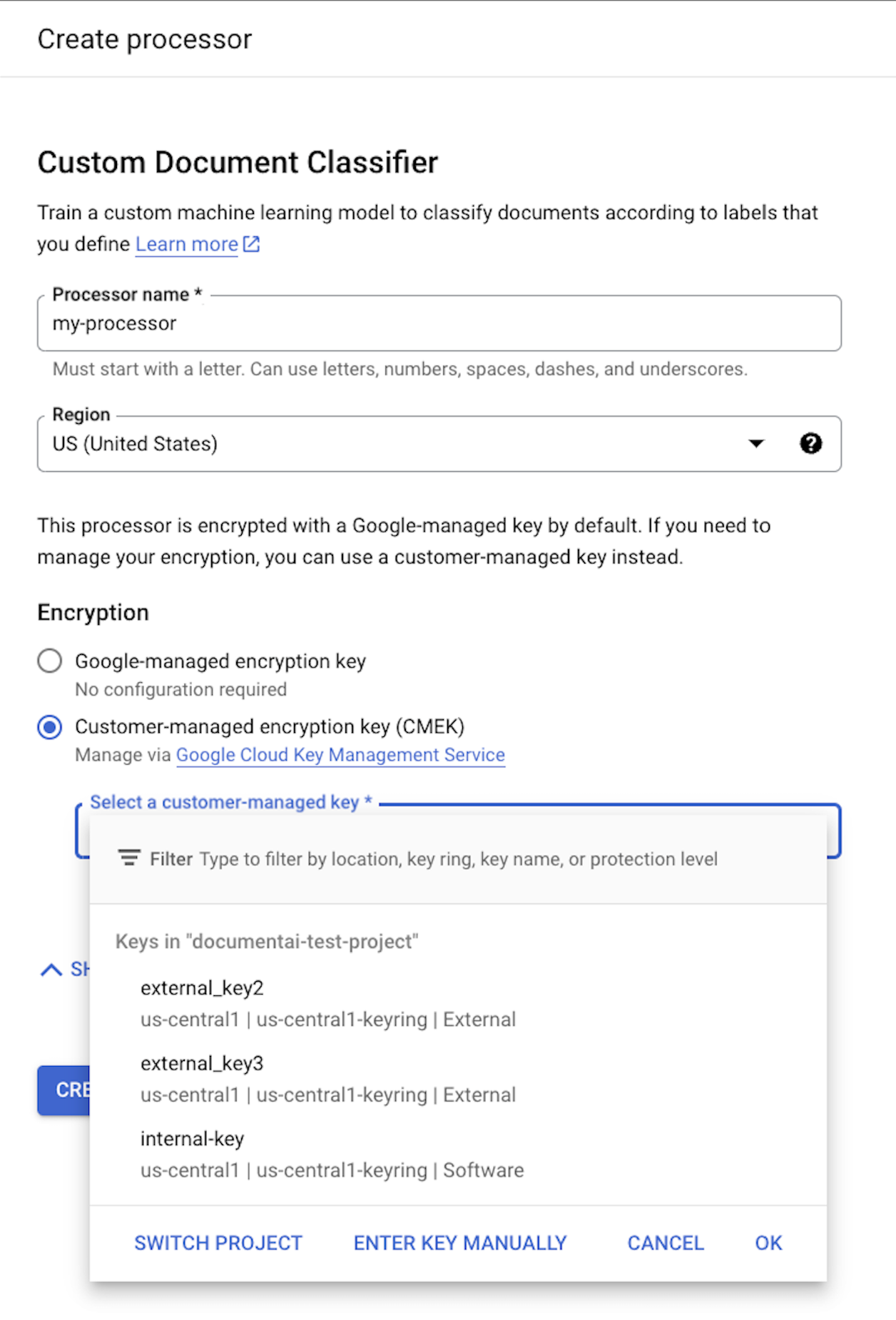
Verschlüsselungseinstellungen sind verfügbar, wenn Sie einen Prozessor erstellen. Wenn Sie CMEK verwenden möchten, wählen Sie die Option CMEK aus und wählen Sie einen Schlüssel aus.
Der CMEK-Schlüssel wird für alle Daten verwendet, die mit dem Prozessor und seinen untergeordneten Ressourcen verknüpft sind. Alle kundenspezifischen Daten, die an den Auftragsverarbeiter gesendet werden, werden automatisch mit dem bereitgestellten Schlüssel verschlüsselt, bevor sie auf die Festplatte geschrieben werden.
Nachdem ein Prozessor erstellt wurde, können Sie seine Verschlüsselungseinstellungen nicht mehr ändern. Wenn Sie einen anderen Schlüssel verwenden möchten, müssen Sie einen neuen Prozessor erstellen.
Externe Schlüssel
Mit Cloud External Key Manager (EKM) können Sie externe Schlüssel erstellen und verwalten, um Daten in Google Cloudzu verschlüsseln.
Wenn Sie einen Cloud EKM-Schlüssel verwenden, hat Google keine Kontrolle über die Verfügbarkeit Ihres extern verwalteten Schlüssels. Wenn Sie Zugriff auf eine Ressource anfordern, die mit einem extern verwalteten Schlüssel verschlüsselt ist, und der Schlüssel nicht verfügbar ist, lehnt Document AI die Anfrage ab. Es kann bis zu 10 Minuten dauern, bis Sie auf die Ressource zugreifen können, nachdem der Schlüssel verfügbar ist.
Weitere Überlegungen zur Verwendung externer Schlüssel finden Sie unter EKM-Überlegungen.
Von CMEK unterstützte Ressourcen
Wenn eine Ressource auf der Festplatte gespeichert wird und Kundendaten als Teil der Ressource gespeichert werden, verschlüsselt Document AI die Inhalte zuerst mit dem CMEK-Schlüssel.
| Ressource | Material verschlüsselt |
|---|---|
Processor |
Nicht zutreffend – keine Nutzerdaten. Wenn Sie jedoch beim Erstellen des Prozessors einen CMEK-Schlüssel angeben, muss dieser gültig sein. |
ProcessorVersion |
Alle |
Evaluation |
Alle |
CMEK-unterstützte APIs
Die APIs, die den CMEK-Schlüssel für die Verschlüsselung verwenden, sind:
| Methode | Verschlüsselung |
|---|---|
processDocument |
N/A – es werden keine Daten auf der Festplatte gespeichert. |
batchProcessDocuments |
Daten werden vorübergehend auf der Festplatte gespeichert und mit einem sitzungsspezifischen Schlüssel verschlüsselt (siehe CMEK-Konformität). |
trainProcessorVersion |
Dokumente, die für das Training verwendet werden, werden mit dem bereitgestellten KMS-/CMEK-Schlüssel verschlüsselt. |
evaluateProcessorVersion |
Die Auswertungen werden mit dem bereitgestellten KMS-/CMEK-Schlüssel verschlüsselt. |
API-Anfragen, mit denen auf verschlüsselte Ressourcen zugegriffen wird, schlagen fehl, wenn der Schlüssel deaktiviert oder nicht erreichbar ist. Beispiele:
| Methode | Entschlüsselung |
|---|---|
getProcessorVersion |
Prozessorversionen, die mit Kundendaten trainiert wurden, werden verschlüsselt. Für den Zugriff ist eine Entschlüsselung erforderlich. |
processDocument |
Wenn Sie Dokumente mit einer verschlüsselten Prozessorversion verarbeiten, müssen sie entschlüsselt werden. |
Import Documents |
Wenn Sie Dokumente mit aktivierter auto-labeling mit einer verschlüsselten Prozessorversion importieren, müssen Sie sie entschlüsseln. |
CMEK und Cloud Storage
APIs wie batchProcess können Daten aus Cloud Storage-Buckets lesen und in Cloud Storage-Buckets schreiben.
Alle Daten, die von Document AI in Cloud Storage geschrieben werden, werden mit dem für den Bucket konfigurierten Verschlüsselungsschlüssel verschlüsselt. Dieser kann sich vom CMEK-Schlüssel Ihres Prozessors unterscheiden.
Weitere Informationen finden Sie in der CMEK-Dokumentation für Cloud Storage.

