This document shows how administrators can assign the device-based access levels to control access to applications. These applications include Google Workspace resources and the applications that are protected by Identity-Aware Proxy on Google Cloud (also known as IAP-secured resources).
Before you begin
To complete the tasks on this page, you must have one of the following roles:
- Access Context Manager Admin (
roles/accesscontextmanager.policyAdmin) - Access Context Manager Editor (
roles/accesscontextmanager.policyEditor)
Assign device-based access levels on resources
The way you assign device-based access levels depends on whether you are using Google Workspace or Google Cloud resources:
Google Workspace
As an administrator, you can assign one or more access levels for the apps by using Context-Aware Access from the Google Admin console. If you select multiple access levels, devices must satisfy the conditions only in one of the access levels to be granted access to the app.
Assign access levels for Google Workspace applications from the Google Workspace Admin console:
From the Admin console Home page, go to Security > Context-Aware Access.
Go to Context-Aware AccessClick Assign access levels.
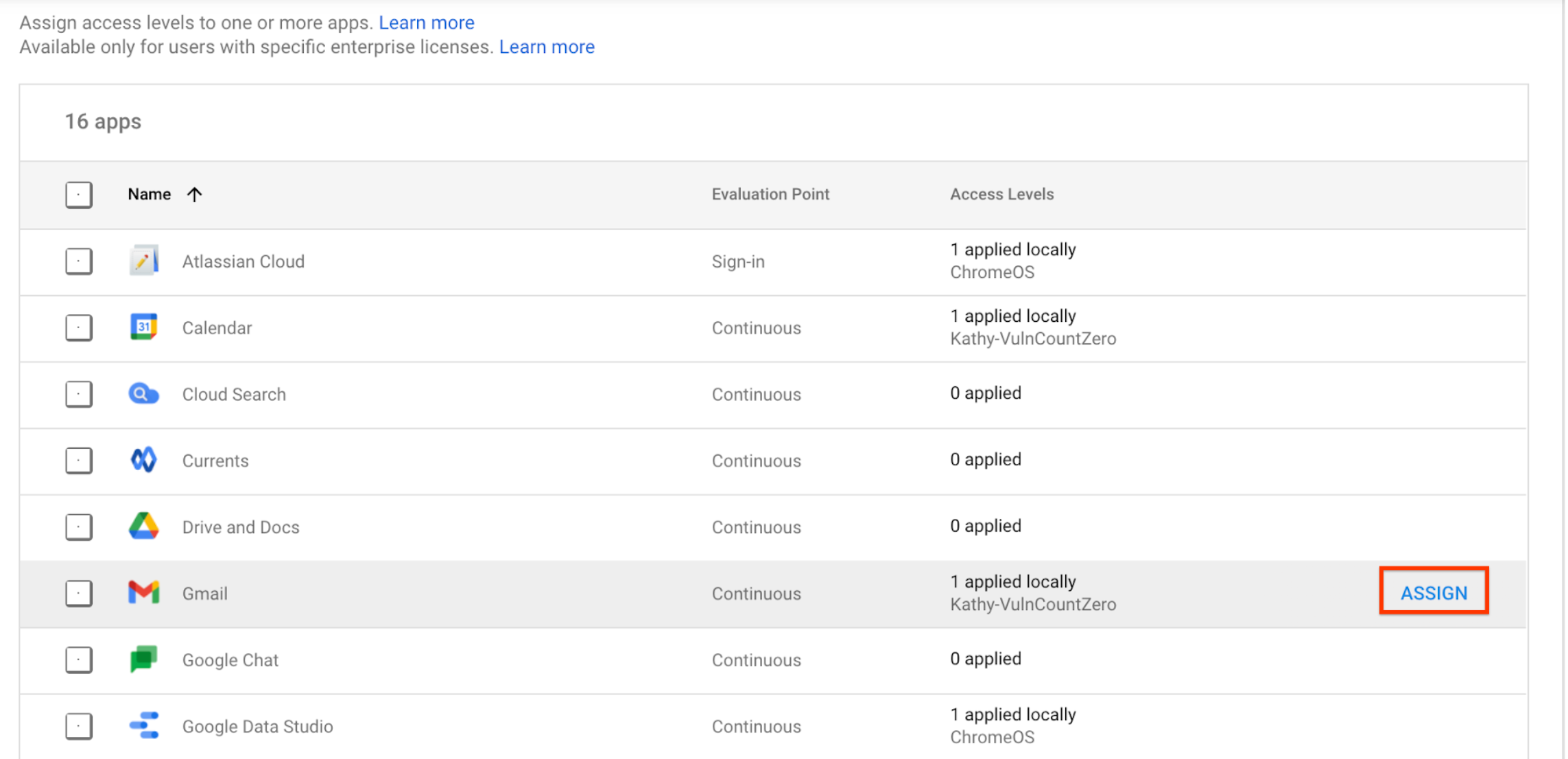
You see a list of apps.
- In the Organizational units section, select your organizational unit or group.
Select the app for which you want to assign an access level, and click Assign.
You see a list of all access levels. Access levels are a shared resource between Google Workspace, Cloud Identity, and Google Cloud so you might see access levels that you didn't create in the list.
- Select one or more access levels for the app.
- To apply the access levels to users on desktop and mobile apps (and on the browser), select Apply to Google desktop and mobile apps. This checkbox applies to built-in apps only.
- Click Save. The access level name displays in the assigned access levels list next to the app.
Google Cloud
You assign an access level to an IAP-secured resource by updating its IAM policy. For instructions, see Apply an access level for IAP-secured resources in the Chrome Enterprise Premium documentation.
