You're viewing Apigee and Apigee hybrid documentation.
View
Apigee Edge documentation.
IPDeniedAccess
Error code
accesscontrol.IPDeniedAccess
Error response body
{
"fault": {
"faultstring": "Access Denied for client ip : client_IP",
"detail": {
"errorcode": "accesscontrol.IPDeniedAccess"
}
}
}Example error message
{
"fault": {
"faultstring": "Access Denied for client ip : 104.132.196.83",
"detail": {
"errorcode": "accesscontrol.IPDeniedAccess"
}
}
}
Cause
This error occurs if the client IP address, or any IP address passed as part of the API request, matches any IP address(es) specified in the <SourceAddress> element within the <MatchRule> element of the Access Control Policy, and the action attribute of the <MatchRule> element is set to DENY.
For example, let's say the <SourceAddress> is defined as shown below:
<SourceAddress mask="32">104.132.196.83</SourceAddress>
If the above IP address matches the IP address of the client system (indicated by the variable proxy.client.ip), or any of the IP addresses passed as part of the API request, the error will occur.
Diagnosis
Identify the IP address(es) denied access for a specific API request. You can find this information in the
faultstringelement of the error response.For example, in the following
faultstring, the IP address is104.132.196.83:"faultstring": "Access Denied for client ip : 104.132.196.83"Examine all the Access Control policies in the failed API Proxy and determine the specific policy where the IP address(es) specified in the
<SourceAddress>element matches the IP address(es) identified in thefaultstring(Step 1 above).For example, the following policy defines the
<SourceAddress>IP as104.132.196.83,which matches what is in thefaultstring:<?xml version="1.0" encoding="UTF-8" standalone="yes"?> <AccessControl async="false" continueOnError="false" enabled="true" name="Access-Control"> <DisplayName>Access-Control</DisplayName> <Properties/> <IPRules noRuleMatchAction="ALLOW"> <MatchRule action="DENY"> <SourceAddress mask="32">104.132.196.83</SourceAddress> </MatchRule> </IPRules> </AccessControl>Determine the IP address(es) from which the API request was made. This can be done in multiple ways:
Using UI Trace
- Capture the trace for the failing API request.
- Select the specific Access Control Policy that has failed from the right hand panel.
In the Phase Details pane, check the value of the variable
proxy.client.ipas shown in the following screenshot of a sample trace.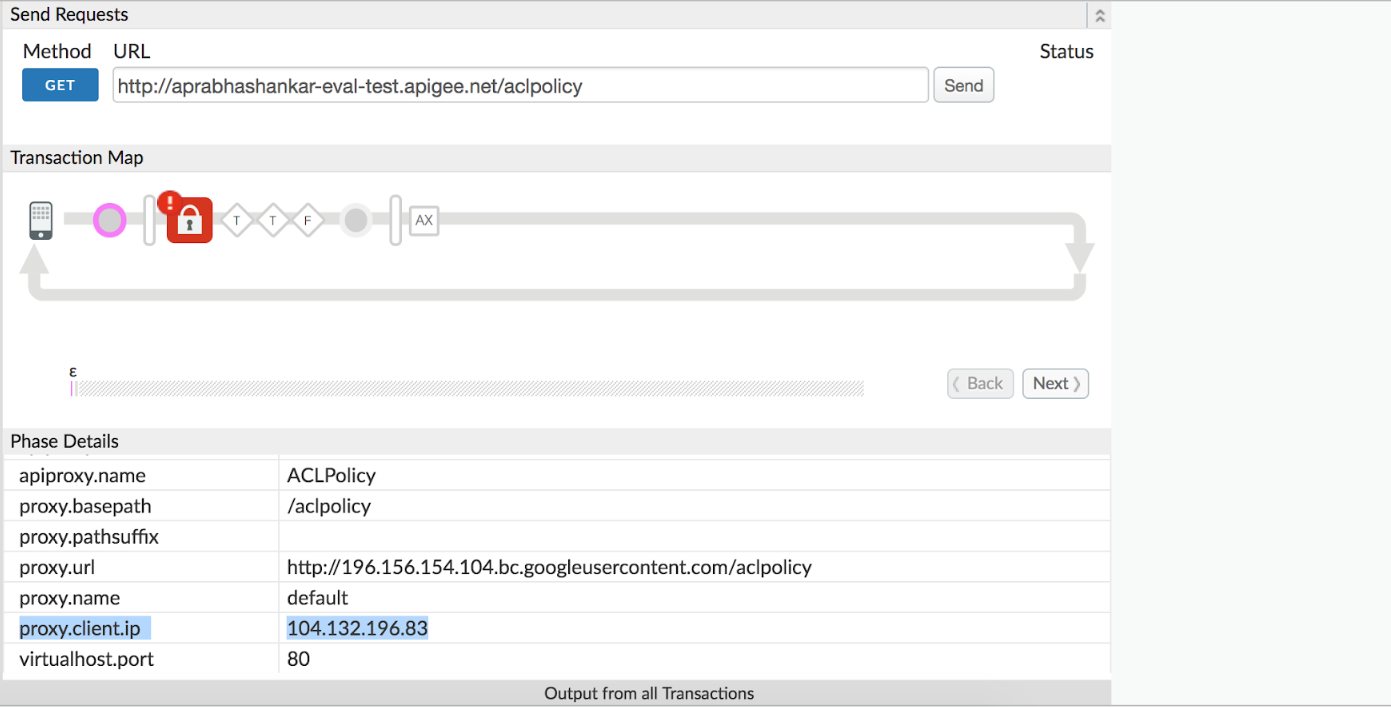
If the
proxy.client.ipis not listed, then check the value of the X-Forwarded-For or True-Client-IP message headers.
Using Custom Reports
You can create Custom Reports to determine whether a 403 status code was thrown during the execution of the Access Control policy within the API proxy and also determine the client IP address. This is particularly useful if the issue has occurred in the past or if the issue is intermittent and you are unable to capture the trace in UI.
Refer to Creating and managing custom reports to understand how to create custom reports. In the custom report, choose:
Sum of Traffic as a Metric, and
Proxy, Response Status Code, Proxy Client IP, and X-Forwarded-For-IP as Dimensions.
This should help you to determine the client IP or IP addresses passed that led to the error.
If the client IP address (indicated by the variable
proxy.client.ip), or any IP address passed as part of the API request, matches the IP address(es) specified in the<SourceAddress>element within the<MatchRule>element of Access Control Policy, where theactionattribute is set toDENY, then that is the cause of the error.In the example shown above, the value set in the reference variable
proxy.client.ip(as seen in the screenshot of the trace above) matches the IP address defined in the<SourceAddress>element of the Access Control policy, thus triggering the error response:"faultstring": "Access Denied for client ip : 104.132.196.83"
Resolution
If the Access Control policy is intended to deny access to API requests coming from the specific IP address(es) listed in the faultstring, then the error message is expected. In this case, there is no additional action is required.
However, if you determine that the specific IP address(es) can be given access to the API requests for the specific API Proxy, then modify the Access Control Policy to allow access to those IP address(es). Alternatively, you can remove the Access Control Policy from the API Proxy if you don't want to deny access to any IP address(es).
Here is an example that shows how to allow access to a specific IP Address 104.132.196.83 only and deny access for the rest:
<AccessControl name="ACL">
<IPRules noRuleMatchAction = "DENY">
<MatchRule action = "ALLOW">
<SourceAddress mask="32">104.132.196.83</SourceAddress>
</MatchRule>
</IPRules>
</AccessControl>
