Anda sedang melihat dokumentasi Apigee dan Apigee hybrid.
Lihat dokumentasi
Apigee Edge.
IPDeniedAccess
Kode error
accesscontrol.IPDeniedAccess
Isi respons error
{
"fault": {
"faultstring": "Access Denied for client ip : client_IP",
"detail": {
"errorcode": "accesscontrol.IPDeniedAccess"
}
}
}Contoh pesan error
{
"fault": {
"faultstring": "Access Denied for client ip : 104.132.196.83",
"detail": {
"errorcode": "accesscontrol.IPDeniedAccess"
}
}
}
Penyebab
Error ini terjadi jika alamat IP klien, atau alamat IP apa pun yang diteruskan sebagai bagian dari permintaan API, cocok dengan alamat IP apa pun yang ditentukan dalam elemen <SourceAddress> dalam elemen <MatchRule> dari Kebijakan Kontrol Akses, dan atribut action dari elemen <MatchRule> ditetapkan ke DENY.
Misalnya, misalkan <SourceAddress> ditentukan seperti yang ditunjukkan di bawah ini:
<SourceAddress mask="32">104.132.196.83</SourceAddress>
Jika alamat IP di atas cocok dengan alamat IP sistem klien (ditunjukkan oleh variabel proxy.client.ip), atau salah satu alamat IP yang diteruskan sebagai bagian dari permintaan API, error akan terjadi.
Diagnosis
Identifikasi alamat IP yang ditolak aksesnya untuk permintaan API tertentu. Anda dapat menemukan informasi ini di elemen
faultstringrespons error.Misalnya, dalam
faultstringberikut, alamat IP-nya adalah104.132.196.83:"faultstring": "Access Denied for client ip : 104.132.196.83"Periksa semua kebijakan Kontrol Akses di Proxy API yang gagal dan tentukan kebijakan spesifik tempat alamat IP yang ditentukan dalam elemen
<SourceAddress>cocok dengan alamat IP yang diidentifikasi dalamfaultstring(Langkah 1 di atas).Misalnya, kebijakan berikut menentukan IP
<SourceAddress>sebagai104.132.196.83,yang cocok dengan yang ada difaultstring:<?xml version="1.0" encoding="UTF-8" standalone="yes"?> <AccessControl async="false" continueOnError="false" enabled="true" name="Access-Control"> <DisplayName>Access-Control</DisplayName> <Properties/> <IPRules noRuleMatchAction="ALLOW"> <MatchRule action="DENY"> <SourceAddress mask="32">104.132.196.83</SourceAddress> </MatchRule> </IPRules> </AccessControl>Menentukan alamat IP tempat permintaan API dibuat. Hal ini dapat dilakukan dengan beberapa cara:
Menggunakan UI Trace
- Rekam rekaman aktivitas untuk permintaan API yang gagal.
- Pilih Kebijakan Kontrol Akses tertentu yang telah gagal dari panel sebelah kanan.
Di panel Phase Details, periksa nilai variabel
proxy.client.ipseperti yang ditunjukkan dalam screenshot rekaman aktivitas sampel berikut.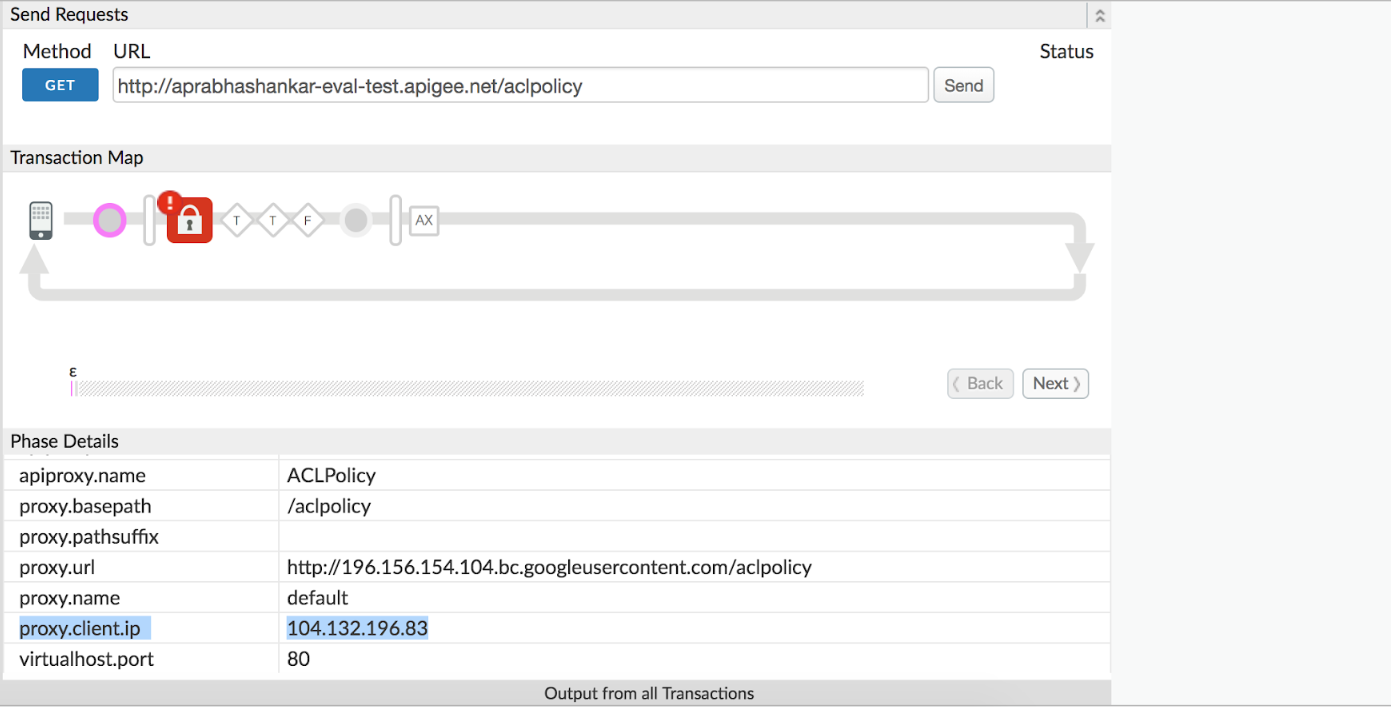
Jika
proxy.client.iptidak tercantum, periksa nilai header pesan X-Forwarded-For atau True-Client-IP.
Menggunakan Laporan Kustom
Anda dapat membuat Laporan Kustom untuk menentukan apakah kode status 403 ditampilkan selama eksekusi kebijakan Kontrol Akses dalam proxy API dan juga menentukan alamat IP klien. Hal ini sangat berguna jika masalah telah terjadi sebelumnya atau jika masalahnya bersifat intermiten dan Anda tidak dapat merekam rekaman aktivitas di UI.
Lihat Membuat dan mengelola laporan kustom untuk memahami cara membuat laporan kustom. Di laporan kustom, pilih:
Jumlah Traffic sebagai Metrik, dan
Proxy, Response Status Code, Proxy Client IP, dan X-Forwarded-For-IP sebagai Dimensi.
Hal ini akan membantu Anda menentukan IP klien atau alamat IP yang diteruskan yang menyebabkan error.
Jika alamat IP klien (ditunjukkan oleh variabel
proxy.client.ip), atau alamat IP apa pun yang diteruskan sebagai bagian dari permintaan API, cocok dengan alamat IP yang ditentukan dalam elemen<SourceAddress>dalam elemen<MatchRule>Kebijakan Kontrol Akses, dengan atributactionditetapkan keDENY, maka itulah penyebab error.Dalam contoh yang ditampilkan di atas, nilai yang ditetapkan dalam variabel referensi
proxy.client.ip(seperti yang terlihat pada screenshot rekaman aktivitas di atas) cocok dengan alamat IP yang ditentukan dalam elemen<SourceAddress>kebijakan Access Control, sehingga memicu respons error:"faultstring": "Access Denied for client ip : 104.132.196.83"
Resolusi
Jika kebijakan Kontrol Akses dimaksudkan untuk menolak akses ke permintaan API yang berasal dari alamat IP tertentu yang tercantum dalam faultstring, pesan error akan muncul. Dalam hal ini, Anda tidak perlu melakukan tindakan tambahan apa pun.
Namun, jika Anda menentukan bahwa alamat IP tertentu dapat diberi akses ke permintaan API untuk Proxy API tertentu, ubah Kebijakan Kontrol Akses untuk mengizinkan akses ke alamat IP tersebut. Atau, Anda dapat menghapus Kebijakan Kontrol Akses dari Proxy API jika tidak ingin menolak akses ke alamat IP mana pun.
Berikut adalah contoh yang menunjukkan cara mengizinkan akses hanya ke Alamat IP 104.132.196.83 tertentu dan menolak akses untuk yang lainnya:
<AccessControl name="ACL">
<IPRules noRuleMatchAction = "DENY">
<MatchRule action = "ALLOW">
<SourceAddress mask="32">104.132.196.83</SourceAddress>
</MatchRule>
</IPRules>
</AccessControl>

