如需其他來源代管選項,請使用 Secure Source Manager。這項服務是在區域部署的單一租戶管理型原始碼存放區,代管於 Google Cloud。這項服務支援 Git 版本管控,並與 Cloud Build、Cloud Deploy 和 Artifact Registry 整合。
自 2024 年 6 月 17 日起,新客戶無法使用 Cloud Source Repositories。如果貴機構先前未使用過 Cloud Source Repositories,您就無法啟用 API 或使用 Cloud Source Repositories。未連結至機構的新專案無法啟用 Cloud Source Repositories API。在 2024 年 6 月 17 日前使用 Cloud Source Repositories 的機構不會受到這項異動影響。
特徵
Cloud Source Repositories 提供功能完善的私人 Git 存放區,由 Google Cloud 代管。
您可以使用 Cloud Source Repositories 協作開發任何應用程式或服務,並透過版本控制功能進行開發,包括在 App Engine 和 Compute Engine 上執行的應用程式或服務。
如果您熟悉 Git,可以快速開始使用 Cloud Source Repositories。例如,您可以將 Cloud Source Repositories 新增至本機 Git 存放區做為遠端存放區,或在 GitHub 或 Bitbucket 代管。您可以從本機存放區使用標準的 Git 指令與雲端的存放區互動,包括 push、pull、clone 和 log。
多個存放區
您可以針對單一 Google Cloud 專案建立多個存放區,讓您以最適合自己的方式整理與雲端專案關聯的程式碼。
已連結的存放區
您可以將現有的 GitHub 或 Bitbucket 存放區連結至 Cloud Source Repositories。已連結的存放區會自動與 Cloud Source Repositories 同步。
編輯器支援
Cloud Source Repositories 中的存放區為 Git 存放區,因此您可以繼續使用您選擇的編輯器處理程式碼。如需更完善整合的體驗,請參閱下列主題:
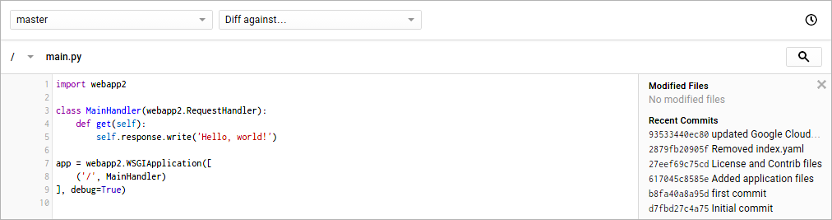
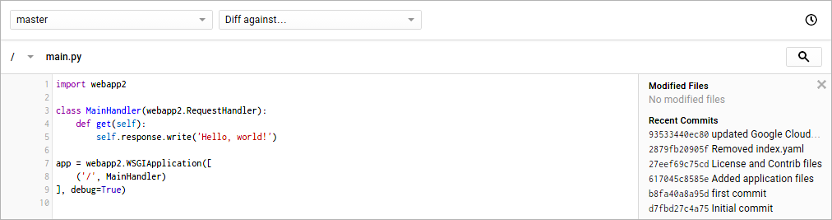
來源瀏覽器
Cloud Source Repositories 也提供來源瀏覽器,可讓您從Google Cloud 主控台內檢視存放區檔案。
自動記錄
Cloud Source Repositories 會自動將存放區活動記錄傳送至 Cloud Logging,以協助追蹤及排解資料存取問題。
您可以使用這些記錄,查看近期的存放區同步作業、其他使用者的存放區存取權,以及建立、刪除和變更權限等管理員動作。此外,您可以設定通知設定,在存放區同步期間記錄到錯誤時傳送提醒給您。
如要進一步瞭解在 Logging 中讀取和寫入記錄項目,請參閱此快速入門。如需瞭解可能的帳單設定以管理記錄的儲存,請參閱記錄定價。
安全金鑰偵測
Cloud Source Repositories 提供安全金鑰偵測功能,可封鎖包含機密資訊的 git push 交易。這項功能旨在提升原始碼的安全性。最佳做法是啟用此功能。詳情請參閱「偵測安全金鑰」。
使用者資料
後續步驟
除非另有註明,否則本頁面中的內容是採用創用 CC 姓名標示 4.0 授權,程式碼範例則為阿帕契 2.0 授權。詳情請參閱《Google Developers 網站政策》。Java 是 Oracle 和/或其關聯企業的註冊商標。
上次更新時間:2025-10-19 (世界標準時間)。
[[["容易理解","easyToUnderstand","thumb-up"],["確實解決了我的問題","solvedMyProblem","thumb-up"],["其他","otherUp","thumb-up"]],[["難以理解","hardToUnderstand","thumb-down"],["資訊或程式碼範例有誤","incorrectInformationOrSampleCode","thumb-down"],["缺少我需要的資訊/範例","missingTheInformationSamplesINeed","thumb-down"],["翻譯問題","translationIssue","thumb-down"],["其他","otherDown","thumb-down"]],["上次更新時間:2025-10-19 (世界標準時間)。"],[],[]]