Deploy on Cloud Run and view security insights
This quickstart explains how to deploy a container image to Cloud Run and view security insights for the deployment on the Security tab in the Google Cloud console. You will:
- Deploy an image to Cloud Run using Cloud Deploy. Cloud Deploy is a Google Cloud service that automates delivery of your applications to a series of target environments in a defined promotion sequence.
View the following security insights for the deployment:
- Identity and encryption information for the deployment.
- Supply-chain Levels for Software Artifacts (SLSA) level, which identifies the level of assurance for the deployment.
- Vulnerabilities in build artifacts.
- Software bill of materials (SBOM) for the build artifacts.
- Build provenance, which is a collection of verifiable metadata about a build. It includes details such as the digests of the built images, the input source locations, the build toolchain, build steps, and the build duration.
Before you begin
- Sign in to your Google Cloud account. If you're new to Google Cloud, create an account to evaluate how our products perform in real-world scenarios. New customers also get $300 in free credits to run, test, and deploy workloads.
-
Install the Google Cloud CLI.
-
If you're using an external identity provider (IdP), you must first sign in to the gcloud CLI with your federated identity.
-
To initialize the gcloud CLI, run the following command:
gcloud init -
Create or select a Google Cloud project.
-
Create a Google Cloud project:
gcloud projects create PROJECT_ID
Replace
PROJECT_IDwith a name for the Google Cloud project you are creating. -
Select the Google Cloud project that you created:
gcloud config set project PROJECT_ID
Replace
PROJECT_IDwith your Google Cloud project name.
-
-
Verify that billing is enabled for your Google Cloud project.
-
Enable the Cloud Build, Artifact Registry, Cloud Deploy, Cloud Run, and Container Scanning APIs:
gcloud services enable cloudbuild.googleapis.com
artifactregistry.googleapis.com clouddeploy.googleapis.com run.googleapis.com containerscanning.googleapis.com -
Install the Google Cloud CLI.
-
If you're using an external identity provider (IdP), you must first sign in to the gcloud CLI with your federated identity.
-
To initialize the gcloud CLI, run the following command:
gcloud init -
Create or select a Google Cloud project.
-
Create a Google Cloud project:
gcloud projects create PROJECT_ID
Replace
PROJECT_IDwith a name for the Google Cloud project you are creating. -
Select the Google Cloud project that you created:
gcloud config set project PROJECT_ID
Replace
PROJECT_IDwith your Google Cloud project name.
-
-
Verify that billing is enabled for your Google Cloud project.
-
Enable the Cloud Build, Artifact Registry, Cloud Deploy, Cloud Run, and Container Scanning APIs:
gcloud services enable cloudbuild.googleapis.com
artifactregistry.googleapis.com clouddeploy.googleapis.com run.googleapis.com containerscanning.googleapis.com
Set default settings
Set an environment variable for project ID:
export PROJECT_ID=$(gcloud config get project)Set the default region for Cloud Deploy:
gcloud config set deploy/region us-central1
Grant access
Grant IAM roles to the default Compute Engine service account. This is required for Cloud Deploy to deploy workloads into Cloud Run.
gcloud projects add-iam-policy-binding $PROJECT_ID \
--member=serviceAccount:$(gcloud projects describe $PROJECT_ID \
--format="value(projectNumber)")-compute@developer.gserviceaccount.com \
--role="roles/clouddeploy.jobRunner"
gcloud iam service-accounts add-iam-policy-binding $(gcloud projects describe $PROJECT_ID \
--format="value(projectNumber)")-compute@developer.gserviceaccount.com \
--member=serviceAccount:$(gcloud projects describe $PROJECT_ID \
--format="value(projectNumber)")-compute@developer.gserviceaccount.com \
--role="roles/iam.serviceAccountUser" \
--project=$PROJECT_ID
gcloud projects add-iam-policy-binding $PROJECT_ID \
--member=serviceAccount:$(gcloud projects describe $PROJECT_ID \
--format="value(projectNumber)")-compute@developer.gserviceaccount.com \
--role="roles/run.developer"
If you have trouble adding either of these roles, contact your project administrator.
Create a Docker repository in Artifact Registry
Create a new Docker repository named
containersin the locationus-central1with the description "Docker repository":gcloud artifacts repositories create containers --repository-format=docker \ --location=us-central1 --description="Docker repository"Verify that your repository was created:
gcloud artifacts repositories listYou should see
containersin the list of displayed repositories.
Prepare sample application
You'll need some sample source code to build and deploy. In this section, you'll clone an existing source repository containing a Java code sample.
Clone the repository that contains the Java code sample:
git clone https://github.com/googlecloudplatform/software-delivery-shield-demo-java.git cd software-delivery-shield-demo-java/backendUpdate
cloudrun.clouddeploy.yamlto replacePROJECT_IDwith your project ID:sed -i "s/PROJECT_ID/${PROJECT_ID}/g" cloudrun.clouddeploy.yaml
Build the application
Build and containerize the Java application using Cloud Build. The following command builds and containerizes the Java application and stores the built container in the Artifact Registry docker repository:
gcloud builds submit --config=cloudbuild.yaml --region=us-central1After the build completes, you see a success status message similar to the following:
DONE ----------------------------------------------------------------------------- ID: 3e08565f-7f57-4449-bc68-51c46cf33d03 CREATE_TIME: 2022-09-19T15:41:07+00:00 DURATION: 54S SOURCE: gs://sds-docs-project_cloudbuild/source/1663602066.777581-6ebe4b2d6fd741ffa18936d7f78055e9.tgz IMAGES: us-central1-docker.pkg.dev/sds-docs-project/containers/java-guestbook-backend:quickstart STATUS: SUCCESS
Generate SBOM for the built image
An SBOM is a full inventory of an application, identifying the packages your software relies on. The contents can include third-party software from vendors, internal artifacts, and open source libraries.
Generate the SBOM for the image you built in the previous section:
gcloud artifacts sbom export \
--uri=us-central1-docker.pkg.dev/${PROJECT_ID}/containers/java-guestbook-backend:quickstart
Deploy the container on Cloud Run using Cloud Deploy
Register your pipeline and targets with the Cloud Deploy service:
gcloud deploy apply --file cloudrun.clouddeploy.yamlYou now have a pipeline, with targets, ready to deploy your application to your first target.
To verify that your pipeline exists, go to the Delivery pipelines page in the Google Cloud console:
Open the Delivery pipelines page
The delivery pipeline you just created,
cloudrun-guestbook-backend-deliveryis displayed.Click
cloudrun-guestbook-backend-deliveryto monitor progress. The Delivery pipeline details page opens.In Cloud Shell, create a release in Cloud Deploy:
gcloud deploy releases create test-release-007 \ --delivery-pipeline=cloudrun-guestbook-backend-delivery \ --skaffold-file=cloudrun.skaffold.yaml \ --images=java-guestbook-backend=us-central1-docker.pkg.dev/${PROJECT_ID}/containers/java-guestbook-backend:quickstartThe new release appears in the Releases section on the Delivery pipeline details page.
Monitor the Pipeline visualization view on the Delivery pipeline details page until the Promote button displays for
dev-cluster. You might need to refresh the page.On the first target in the delivery pipeline visualization,
cloudrun-dev, click Promote.The Promote release dialog is shown. It shows the details of the target you're promoting to.
Click Promote.
The release is now queued for deployment into
cloudrun-prod. When deployment is complete, the delivery pipeline visualization shows it as deployed: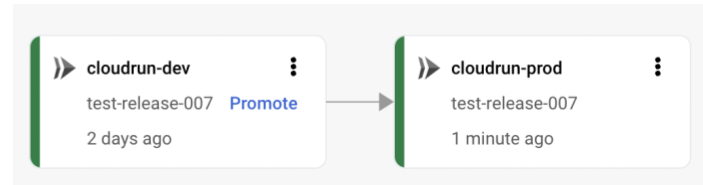
View security insights in Cloud Deploy
Open the Cloud Deploy Delivery pipelines page in the Google Cloud console.
In the Delivery pipelines table, click cloudrun-guestbook-backend-delivery.
In the Delivery pipelines details page, click test-release-008.
In the Release details page, click the Artifacts tab.
In the Build artifacts table, locate the row with the artifact java-guestbook-backend, and under the corresponding Security insights column, click View.
You see the Security tab for deployment.
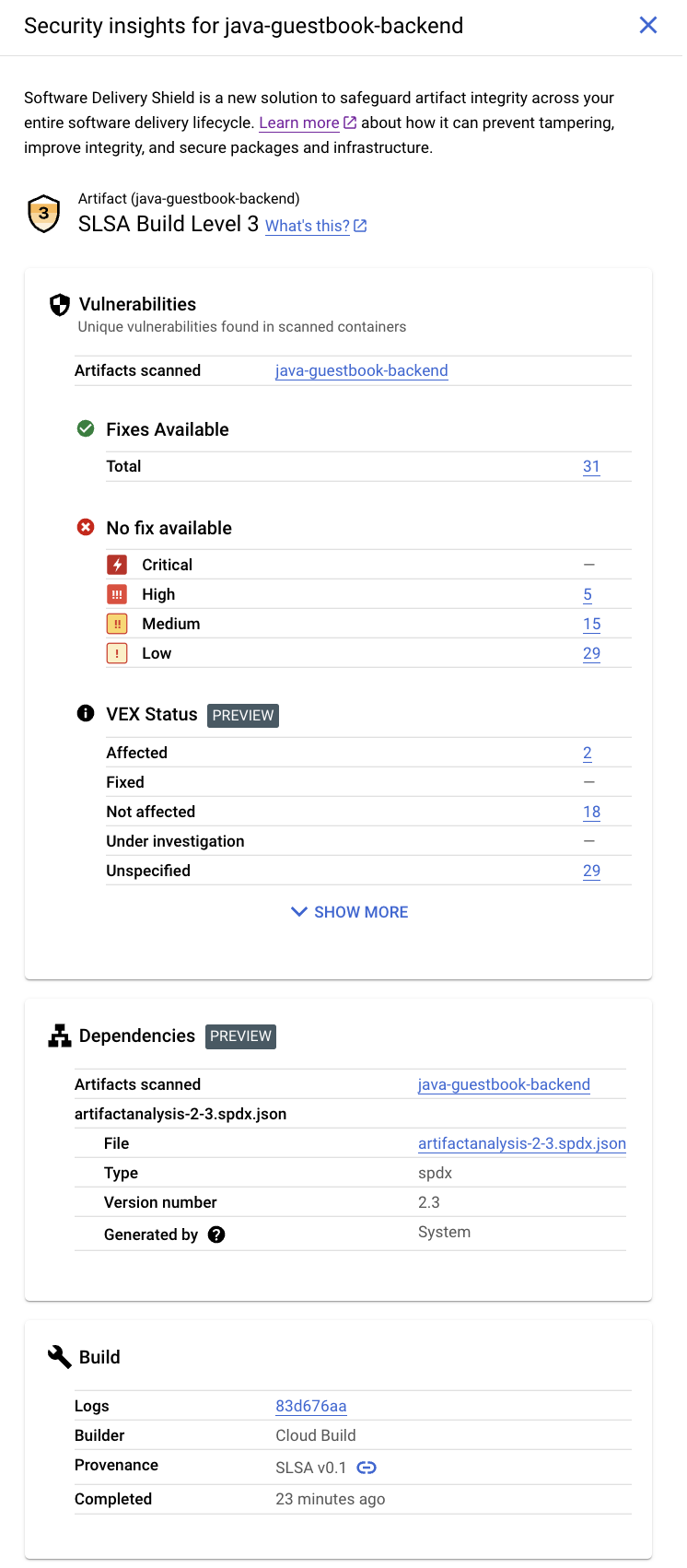
This tab displays the following information in the Security insights section:
SLSA Level: This build has achieved SLSA Level 3. Click the Learn more link to learn what this security level means.
Vulnerabilities: Any vulnerabilities found in your artifacts. Click the image name (java-guestbook-backend) to see the artifacts that have been scanned for vulnerabilities.
Dependencies for the build artifacts.
Build details: Details of the build such as the builder and the link to view logs.
View security insights in Cloud Run
Open the Cloud Run Services page.
In the Cloud Run Services table, click guestbook-backend-prod.
In the Service details page, click Revisions.
In the Revisions panel, click Security.
You see the Security tab for deployment.
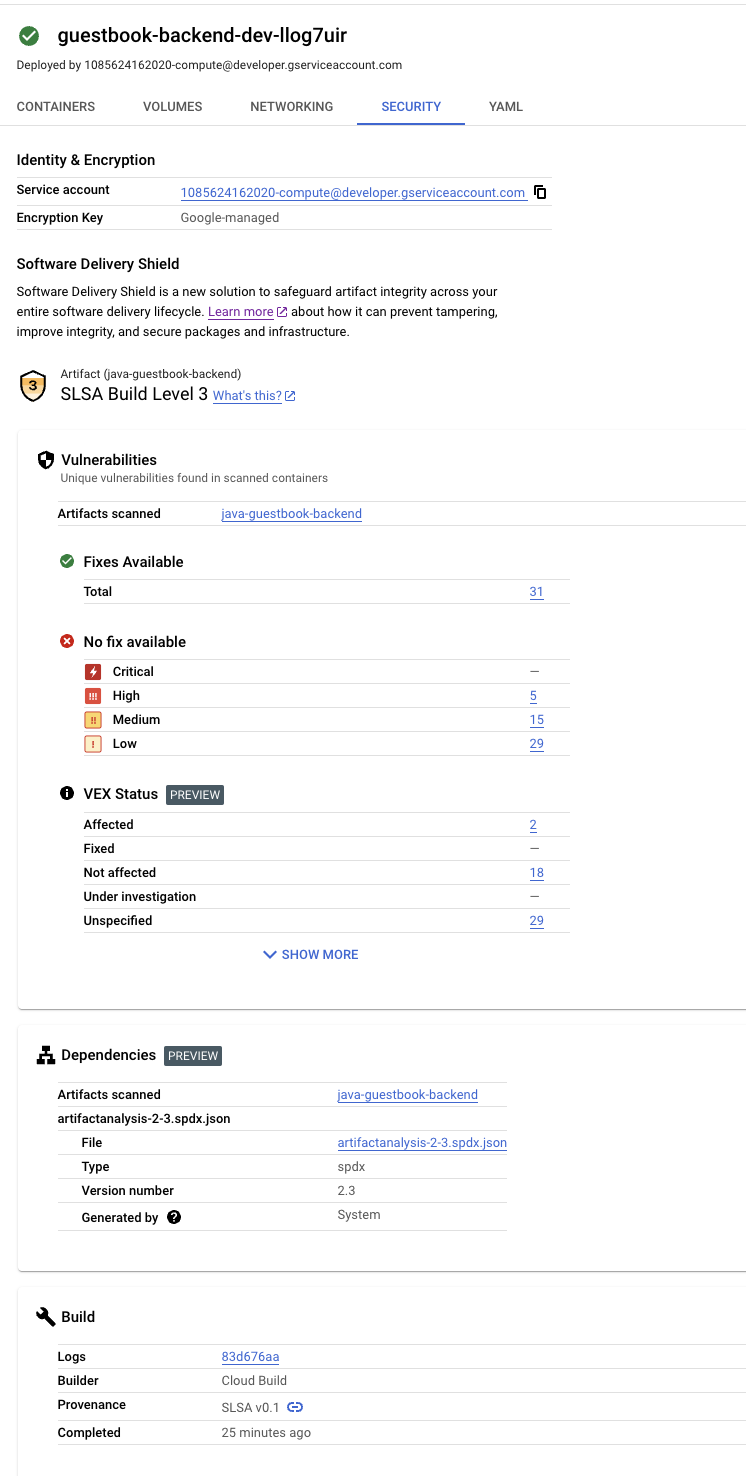
This tab displays the following information in the Security insights section:
Identity and encryption: The email address of the default Compute Engine service account and the encryption key used for the deployment.
SLSA Level: This build has achieved SLSA Level 3. Click the Learn more link to learn what this security level means.
Vulnerabilities: Any vulnerabilities found in your artifacts. Click the image name (java-guestbook-backend) to see the artifacts that have been scanned for vulnerabilities.
Dependencies for the build artifacts.
Build details: Details of the build such as the builder and the link to view logs.
Clean up
To avoid incurring charges to your Google Cloud account for the resources used on this page, delete the Google Cloud project with the resources.
Disable Container Scanning API:
gcloud services disable containerscanning.googleapis.com --forceDelete the
guestbook-backend-devCloud Run service:gcloud run services delete guestbook-backend-dev --region=us-central1 \ --project=${PROJECT_ID}Delete the
guestbook-backend-prodservice:gcloud run services delete guestbook-backend-prod --region=us-central1 \ --project=${PROJECT_ID}Delete the delivery pipeline, including the release and rollouts:
gcloud deploy delivery-pipelines delete cloudrun-guestbook-backend-delivery \ --force --region=us-central1 --project=${PROJECT_ID}This command deletes the delivery pipeline itself, plus all
releaseandrolloutresources Software supply chain security created for that pipeline.Delete the Artifact Registry repository:
gcloud artifacts repositories delete containers \ --location=us-central1 --async
That's it, you completed this quickstart!
What's next
- Learn more about security insights in Cloud Run.
- Learn how to view security insights when deploying to GKE.
- Learn how to view security insights for builds.
- Learn more about software supply chain security.
