You can access Google Cloud products and services from your code using Cloud APIs. These Cloud APIs expose a simple JSON REST interface that you can call via client libraries.
This document describes how to enable Cloud APIs and add Cloud Client Libraries to your project.
Browse Cloud APIs
To explore all available Google Cloud APIs in your IDE, follow these steps:
Navigate to Tools > Google Cloud Code > Cloud APIs.
The Manage Google Cloud APIs window groups Cloud APIs by category. You can also use the Search APIs search bar to find specific APIs.
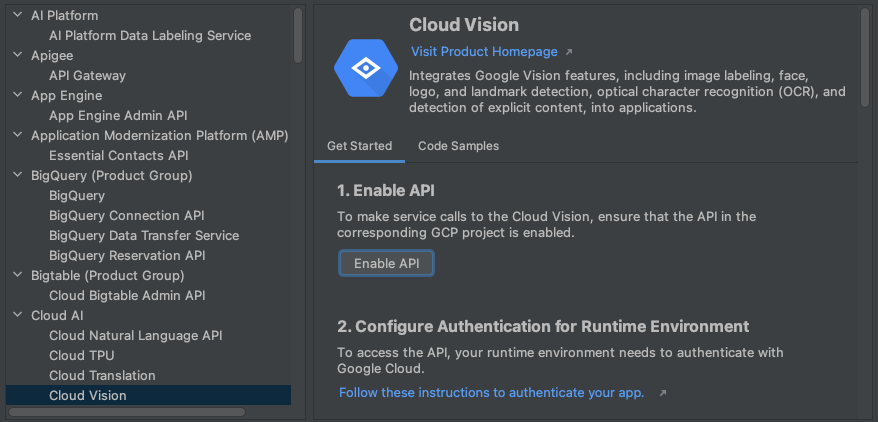
Click an API to view more details, such as its status, language-specific installation instructions for its corresponding client libraries, and relevant documentation.
Enable Cloud APIs
To enable Cloud APIs for a project using the API details, follow these steps:
In the Cloud API details view, select a Google Cloud project that you want to enable the Cloud API for.
Click Enable API.
When the API is enabled, a message appears to confirm the change.
Add the Cloud Client Libraries
To add libraries to your project in IntelliJ, follow these steps:
For Java Maven projects
- Navigate to Tools > Google Cloud Code > Cloud APIs.
- Select your preferred library type as Google Cloud Client Library (recommended for most projects) or Java Spring Google Cloud (recommended if your project uses Java Spring).
- Follow the rest of the instructions in the Install Client Library in your IDE, if applicable.
- When you're finished, click Close.
The Install Client Library section in the Manage Google Cloud APIs dialog displays the supported libraries.
For all other projects
- Navigate to Tools > Google Cloud Code > Cloud APIs.
- To install the API, follow the installation instructions listed on
the API details page for your preferred language.
If you're developing a Java application, you need to also specify your library preference as Google Cloud Client Library (recommended) or Java Spring Google Cloud.
- When you're finished, click Close.
The Install Client Library section in the Manage Google Cloud APIs dialog displays the supported libraries.
Use API code samples
To search for and use code samples for each API in the API explorer, follow these steps:
Navigate to Tools > Google Cloud Code > Cloud APIs.
To open the detail view, click the name of an API.
To view code samples for the API, click the Code Samples tab.
To filter the list of samples, type text to search for or select a programming language from the Language drop-down menu.
Set up authentication
After you've enabled the required APIs and added the necessary client libraries, you need to configure your application in order for it to be successfully authenticated. Your configuration depends on your type of development and the platform you're running on.
Once you complete the relevant authentication steps, your application can authenticate and is ready to be deployed.
Local development
Local machine
Cloud Code ensures you have your Application Default
Credentials (ADC) set if you logged into Google Cloud via your IDE. If
you're not signing in with Cloud Code, run gcloud
auth application-default login manually.
minikube
- Cloud Code ensures you have your Application Default
Credentials (ADC) set if you logged into Google Cloud via your IDE. If
you're not signing in with Cloud Code, run
gcloud auth application-default loginmanually. - Start minikube with
minikube start --addons gcp-auth. This mounts your ADC in your pods. For a detailed minikube auth guide for Google Cloud, refer to the minikube gcp-auth docs.
Other local K8s clusters
- Cloud Code ensures you have your Application Default
Credentials (ADC) set if you logged into Google Cloud via your IDE. If
you're not signing in with Cloud Code, run
gcloud auth application-default loginmanually. - Mount your local
gclouddirectory in your Kubernetes pods by editing the Pod specification in the Pod or Deployment manifests, so that the Google Cloud Client Libraries can find your credentials. Kubernetes pod configuration example:apiVersion: v1 kind: Pod metadata: name: my-app labels: name: my-app spec: containers: - name: my-app image: gcr.io/google-containers/busybox ports: - containerPort: 8080 volumeMounts: - mountPath: /root/.config/gcloud name: gcloud-volume volumes: - name: gcloud-volume hostPath: path: /path/to/home/.config/gcloud
Cloud Run
Cloud Code ensures you have your Application Default
Credentials (ADC) set if you logged into Google Cloud via your IDE. If
you're not signing in with Cloud Code, run gcloud
auth application-default login manually.
Remote development
Google Kubernetes Engine
Depending on the scope of your project, you can choose how you authenticate Google Cloud services on GKE:
- (Development only)
- Create a GKE cluster with the following settings:
- Ensure you're using the service account GKE uses by
default, the Compute Engine default service account, and that
Access scopes is set at Allow full access to
all Cloud APIs (both settings accessible in the Node Pools > Security section).
Since the Compute Engine service account is shared by all workloads deployed on your node, this method overprovisions permissions and should only be used for development. - Ensure Workload Identity is not enabled on your cluster (in the Cluster > Security section).
- Ensure you're using the service account GKE uses by
default, the Compute Engine default service account, and that
Access scopes is set at Allow full access to
all Cloud APIs (both settings accessible in the Node Pools > Security section).
- Assign the necessary roles to the Compute Engine default service account:
- If you're trying to access a secret, follow these Secret Manager-specific steps to set up the required roles on your service account.
- If the Compute Engine default service account is being used, the correct IAM roles may already be applied.
For a list of IAM role types and predefined roles you can grant to identities, see the Understanding roles guide.
For steps to grant the roles, see Granting, changing, and revoking access to resources.
- Create a GKE cluster with the following settings:
- (Recommended for production)
- Configure your GKE cluster and application with Workload Identity to authenticate Google Cloud services on GKE. This associates your Kubernetes service account with your Google service account.
- Configure your Kubernetes Deployment to reference the Kubernetes service
account by setting the
.spec.serviceAccountNamefield in your Kubernetes Deployment YAML file.
If you're working on an app created from a Cloud Code template, this file is located under the kubernetes-manifests folder. - If the Google Cloud service you're trying to access requires additional
roles, grant them for the Google service account you're using to develop
your app:
- If you're trying to access a secret, follow these Secret Manager-specific steps to set up the required roles on your service account.
For a list of IAM role types and predefined roles you can grant to identities, see the Understanding roles guide.
For steps to grant the roles, see Granting, changing, and revoking access to resources.
Cloud Run
-
To create a new unique service account for deploying your Cloud Run
application, on the Service Accounts page, select the project that
your secret is stored in.
- Click Create service account.
- In the Create service account dialog, enter a descriptive name for the service account.
- Change the Service account ID to a unique, recognizable value and then click Create.
- If the Google Cloud service you're trying to access requires additional roles, grant them, click Continue, and then click Done.
- To add your Kubernetes service account to your deploy configuration, navigate to Run > Edit Configurations, and then specify your service account in the Service Name field.
Cloud Run
Depending on the scope of your project, you can choose how you authenticate Google Cloud services on GKE:
- (Development only)
- Create a GKE cluster with the following settings:
- Ensure you're using the service account GKE uses by
default, the Compute Engine default service account, and that
Access scopes is set at Allow full access to
all Cloud APIs (both settings accessible in the Node Pools > Security section).
Since the Compute Engine service account is shared by all workloads deployed on your node, this method overprovisions permissions and should only be used for development.
- Ensure Workload Identity is not enabled on your cluster (in the Cluster > Security section).
- Ensure you're using the service account GKE uses by
default, the Compute Engine default service account, and that
Access scopes is set at Allow full access to
all Cloud APIs (both settings accessible in the Node Pools > Security section).
- Assign the necessary roles to the Compute Engine default service account:
- If you're trying to access a secret, follow these Secret Manager-specific steps to set up the required roles on your service account.
- If the Compute Engine default service account is being used, the correct IAM roles may already be applied.
For a list of IAM role types and predefined roles you can grant to identities, see the Understanding roles guide.
For steps to grant the roles, see Granting, changing, and revoking access to resources.
- Create a GKE cluster with the following settings:
- (Recommended for production)
- Configure your GKE cluster and application with Workload Identity to authenticate Google Cloud services on GKE. This associates your Kubernetes service account with your Google service account.
- To add your Kubernetes service account to your deploy
configuration, navigate to Run > Edit
Configurations, and then specify your Kubernetes service
account in the Service Name field.
- If the Google Cloud service you're trying to access requires additional
roles, grant them for the Google service account you're using to develop
your app:
- If you're trying to access a secret, follow these Secret Manager-specific steps to set up the required roles on your service account.
For a list of IAM role types and predefined roles you can grant to identities, see the Understanding roles guide.
For steps to grant the roles, see Granting, changing, and revoking access to resources.
Remote development with Secret Manager permissions enabled
If you're developing remotely, using a service account for authentication, and your application uses secrets, you need to complete a few more steps in addition to the remote development instructions. These steps assign your Google service account the role required to access a particular Secret Manager secret:
To open the Secret Manager tool window, navigate to Tools > Google Cloud Code > Secret Manager.
Select the secret that you want to access in your code.
Click the Permissions tab and then configure your secret's permissions by clicking edit Edit Permission.
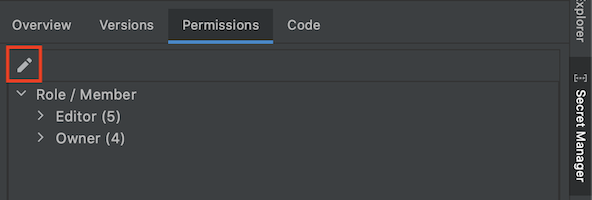
The Google Cloud console opens in a new window of your web browser, displaying the Secret Manager configuration page of your secret.
In the Google Cloud console, click the Permissions tab and then click Grant Access.
In the New principals field, enter your service account.
In the Select a role dropdown field, select the Secret Manager Secret Accessor role.
When you're finished, click Save.
Your service account has permission to access this secret.
