This page explains how you can use Identity-Aware Proxy (IAP) TCP forwarding to enable administrative access to VM instances that do not have external IP addresses or do not permit direct access over the internet.
IAP TCP forwarding allows you to establish an encrypted tunnel over which you can forward SSH, RDP, and other traffic to VM instances. IAP TCP forwarding also provides you fine-grained control over which users are allowed to establish tunnels and which VM instances users are allowed to connect to.
To learn more about how IAP TCP forwarding works, see the TCP forwarding overview.
Preparing your project for IAP TCP forwarding
This section walks you through the necessary steps to enable IAP TCP forwarding in your Google Cloud project.
Create a firewall rule
To allow IAP to connect to your VM instances, create a firewall rule that:
- applies to all VM instances that you want to be accessible by using IAP.
- allows ingress traffic from the IP range
35.235.240.0/20. This range contains all IP addresses that IAP uses for TCP forwarding.For IPv6 VMs, use the following IP range:
2600:2d00:1:7::/64. - allows connections to all ports that you want to be accessible by
using IAP TCP forwarding, for example, port
22for SSH and port3389for RDP.
Console
To allow RDP and SSH access to all VM instances in your network, do the following:
- Open the Firewall Rules page.
The remaining steps appear in the Google Cloud console.
- Select a Google Cloud project.
Show me . - On the Firewall Rules page, click
Create firewall rule . - Configure the following settings:
- Name:
allow-ingress-from-iap - Direction of traffic: Ingress
- Target: All instances in the network
- Source filter: IP ranges
- Source IP ranges:
35.235.240.0/20 - Protocols and ports: Select TCP and enter
22,3389to allow both RDP and SSH.
- Name:
- Click Create.
gcloud
To allow RDP access to all VM instances in your network, run:
gcloud compute firewall-rules create allow-rdp-ingress-from-iap \ --direction=INGRESS \ --action=allow \ --rules=tcp:3389 \ --source-ranges=35.235.240.0/20
For SSH access, run:
gcloud compute firewall-rules create allow-ssh-ingress-from-iap \ --direction=INGRESS \ --action=allow \ --rules=tcp:22 \ --source-ranges=35.235.240.0/20
For other protocols, run
gcloud compute firewall-rules create allow-ingress-from-iap \ --direction=INGRESS \ --action=allow \ --rules=tcp:PORT \ --source-ranges=35.235.240.0/20
where PORT is the port used by the protocol.
Grant roles for IAP TCP forwarding
To control which users and groups are allowed to use IAP TCP forwarding and which VM instances they're allowed to connect to, grant the appropriate Identity and Access Management (IAM) roles on the project.
If you are using OS Login (recommended), see Configuring OS Login roles on user accounts.
The following table shows the predefined roles you need to grant to trusted administrators for TCP forwarding and related tasks:
| Task | Roles | More information |
|---|---|---|
| TCP forwarding |
IAP-secured Tunnel User (roles/iap.tunnelResourceAccessor)
|
See Grant access to all VM instances in a project or Grant access to a specific VM. |
| SSH access |
Compute Instance Admin (v1) (roles/compute.instanceAdmin.v1)
|
|
| Use a service account | Service Account User (roles/iam.serviceAccountUser) |
See The serviceAccountUser role. |
If you want to create custom roles with only the specific permissions needed for this task, see Permissions details.
You can grant a user or group access to all VM instances in a project, or to a specific VM, depending on how you grant the required roles.
Tags are not supported
Granting permission using tags for IAP TCP forwarding is not currently supported.
Grant access to all VM instances in a project
You can give a user or group access to all VM instances in a project by granting the required IAM roles at the project level:
Console
- Open the IAM & Admin page in the Google Cloud console.
The remaining steps appear in the Google Cloud console.
- On the IAM & Admin page, click Add and configure the following:
- New principals: Specify the user or group you want to grant access.
- Select a role: Select Cloud IAP > IAP-Secured Tunnel User.
- Optionally, click Add condition and configure a condition:
- Title: Enter a name for the condition.
- Expression: Enter a condition that a user must meet to gain the permissions in the IAP-Secured Tunnel User role.
For example, the following CEL expression grants access only to port 22:
destination.port == 22You can also grant access based on the access level:
destination.port == 22 && "FULL_ACCESS_LEVEL_NAME" in request.auth.access_levelsWhere
FULL_ACCESS_LEVEL_NAMEis an existing access level and uses the following format:accessPolicies/POLICY_NAME/accessLevels/ACCESS_LEVEL_NAME - Click Add another role and configure the following:
- Select a role Select Compute Engine > Compute Instance Admin (v1).
- Click Save.
gcloud
Grant the two roles to the user by running the following commands:
gcloud projects add-iam-policy-binding PROJECT_ID \ --member=user:EMAIL \ --role=roles/iap.tunnelResourceAccessor gcloud projects add-iam-policy-binding PROJECT_ID \ --member=user:EMAIL \ --role=roles/compute.instanceAdmin.v1
Replace the following:
PROJECT_ID: ID of the projectEMAIL: email address of the user you want to grant access, for exampleuser@example.com.
Grant access to a specific VM
To grant a user or group access to a specific VM, you grant the
roles/iap.tunnelResourceAccessor role on that VM. The other roles must be
granted on the project.
Console
- Open the IAP admin page and select the SSH and TCP Resources tab.
Open the Chrome Enterprise Premium admin page
The remaining steps appear in the Google Cloud console.
- On the SSH and TCP Resources tab of the IAP admin page, select the VM instances that you want to configure.
- Click Show info panel if the info panel is not visible.
Click Add principal and configure the following:
- New principals: Specify the user or group you want to grant access.
- Select a role: Select Cloud IAP > IAP-Secured Tunnel User.
Optionally, click Add condition and configure a condition:
- Title: Enter a name for the condition.
- Expression: Enter a condition that a user must meet to gain the permissions in the IAP-Secured Tunnel User role.
For example, the following CEL expression grants access only to port 22:
destination.port == 22You can also grant access based on the access level:
destination.port == 22 &&"FULL_ACCESS_LEVEL_NAME" in request.auth.access_levelsWhere
FULL_ACCESS_LEVEL_NAMEis an existing access level and uses the formataccessPolicies/POLICY_NAME/accessLevels/ACCESS_LEVEL_NAME.- Click Save.
API
To edit your application's policy.json file, follow the process below.
See Managing access to Chrome Enterprise Premium-secured resources
for more information about using the IAM API to manage
access policies.
Export the following variables.
export IAP_BASE_URL=https://iap.googleapis.com/v1/projects/PROJECT_NUMBER/iap_tunnel # Replace POLICY_FILE.JSON with the name of JSON file to use for setIamPolicy export JSON_NEW_POLICY=POLICY_FILE.JSON
Get the IAM policy for the Compute Engine instance using the
getIamPolicymethod. The empty data bit at the end turns thecurlrequest into POST instead of GET.curl -i -H "Authorization: Bearer $(gcloud auth print-access-token)" \ ${IAP_BASE_URL}/zones/ZONE_NAME/instances/INSTANCE_ID or INSTANCE_NAME:getIamPolicy \ -d ''Grant the
iap.tunnelResourceAccessorrole to your principals by modifying the IAM policy JSON file.Optionally, grant the role only to principals that meet specific criteria, based on IAM Conditions and access levels.
The following is an example of an edited
policy.jsonfile that grants theiap.tunnelResourceAccessorrole to a group of VM instance admins, giving them access to Chrome Enterprise Premium-secured tunnel resources. An IAM condition has been added to make the resources accessible only to principals in the VM instance admins group with a private IP address of10.0.0.1on port22using thedestination.ipanddestination.portIAM Conditions. They must also meet the requirements of the ACCESS_LEVEL_NAME access level.Note that if a principal has the Owner role, they have permission to use IAP for TCP forwarding.
Example policy.json file{ "policy": { "bindings": [ { "role": "roles/iap.tunnelResourceAccessor", "members": ["group:instance-admins@example.com"], "condition": { "expression": "\"accessPolicies/POLICY_NAME/accessLevels/ACCESS_LEVEL_NAME\" in request.auth.access_levels && destination.ip == \"10.0.0.1\" && destination.port == 22", "title": "CONDITION_NAME" } } ] } }
To find a policy name , call
accessPolicies.list:GET https://accesscontextmanager.googleapis.com/v1/accessPolicies
Set your new
policy.jsonfile using thesetIamPolicymethod.curl -i -H "Content-Type:application/json" \ -H "Authorization: Bearer $(gcloud auth print-access-token)" \ ${IAP_BASE_URL}/zones/ZONE_NAME/instances/INSTANCE_ID or INSTANCE_NAME:setIamPolicy \ -d @${JSON_NEW_POLICY}
Permissions details
The required permissions vary depending on how a user will use IAP TCP forwarding:
| Scenarios | Permissions required | |
|---|---|---|
| All |
|
|
Using gcloud compute [start-iap-tunnel, ssh, scp] |
|
|
Using gcloud compute [ssh, scp] |
|
|
| VM using OS Login | Please see these instructions | |
| Not using OS Login |
|
|
| SSH to VM using a service account |
|
|
| SSH from the browser | Please see these instructions | |
For example, if a user wants to connect using gcloud compute ssh to a VM not using OS Login,
but that uses a service account, the user would need the following permissions:
iap.tunnelInstances.accessViaIAPcompute.instances.getcompute.instances.listcompute.projects.getcompute.instances.setMetadatacompute.projects.setCommonInstanceMetadatacompute.globalOperations.getiam.serviceAccounts.actAs
Tunneling SSH connections
You can connect to Linux instances that don't have an external IP address by tunneling SSH traffic through IAP.
When you use IAP tunnelling, the IAP proxies connect to the primary internal
IPv4 address of nic0 on the VM.
Console
To connect to your instance, use the SSH button in the Google Cloud console. Your instance's access configuration (defined through IAM permissions) must allow TCP tunneling through IAP.
gcloud
To connect to your instance, use the
gcloud compute ssh command. Your
instance's access configuration
(defined through IAM permissions) must allow TCP
tunneling through IAP.
gcloud compute ssh INSTANCE_NAME
Replace INSTANCE_NAME with the name of the instance to SSH into.
If the instance doesn't have an external IP address, the connection automatically uses IAP TCP tunneling. If the instance does have an external IP address, the connection uses the external IP address instead of IAP TCP tunneling.
You can use the --tunnel-through-iap
flag so that gcloud compute ssh always uses IAP TCP tunneling.
Use the --internal-ip
flag so that gcloud compute ssh never uses IAP TCP
tunneling and instead directly connects to the internal IP of the VM. Doing
so is useful for clients that are connected to the same VPC network as the
target VM.
IAP Desktop
You can use IAP Desktop to connect to a VM instance by using SSH and IAP TCP forwarding.
In the application, select File > Add Google Cloud project.
Enter the ID or name of your project and click OK.
In the Project Explorer window, right-click the VM instance you want to connect to and select Connect.
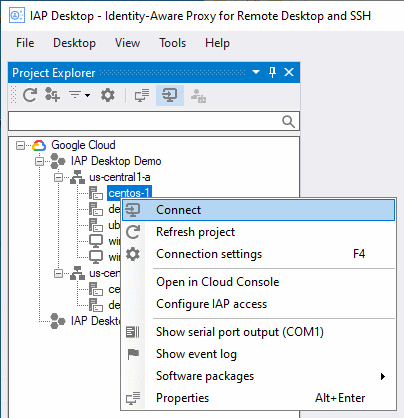
For more information on IAP Desktop, see the GitHub project page.
PuTTY app
You can set up the PuTTY Windows terminal emulator app so that it uses IAP TCP forwarding to connect to a VM instance. Your instance's access configuration (defined through IAM permissions) must allow TCP tunneling through IAP.
Before you configure the PuTTY app, use the gcloud compute ssh command once
to ensure that you have a private SSH key on your local computer and that
your public SSH key is published to Compute Engine:
Open a command prompt and run the following command to connect to the VM instance:
gcloud compute ssh INSTANCE_NAME ` --tunnel-through-iap ` --project PROJECT_ID ` --zone ZONE
Replace the following:
- INSTANCE_NAME: name of the instance to connect to
- PROJECT_ID: project ID of the project the VM instance is located in
- ZONE: zone where the VM instance is located
If necessary, confirm that you want to generate SSH keys by pressing
Y.On the VM, determine your username by running the following command:
whoami
You need this username later.
You can now configure the PuTTY app to use IAP TCP forwarding:
- Open the PuTTY app and select the category Connection > Proxy.
Configure the following proxy settings:
- For Proxy type, select Local.
In the Telnet command, or local proxy command field, enter the following:
gcloud.cmd compute start-iap-tunnel %host %port --listen-on-stdin --project PROJECT_ID --zone ZONE
Replace the following:
- PROJECT_ID: Project ID of the project the VM instance is located in
- ZONE: Zone where the VM instance is located
For Print proxy diagnostics in the terminal window, select Only until session starts.
Select the category Connection > SSH > Auth.
Click Browse and paste the following file name, then click Open:
%USERPROFILE%\.ssh\google_compute_engine.ppk
Select the category Session.
Configure the following proxy settings:
In the Host name (or IP address) field, enter the following:
USERNAME@INSTANCE_NAME
Replace the following:
- USERNAME: the Linux username you determined earlier
- INSTANCE_NAME: the name of the VM instance that you want to connect to
Saved sessions: Enter a name for the session.
Click Save.
Click Open to start the SSH session.
ssh
You can directly use the ssh command with a ProxyCommand option that uses gcloud
to start the tunnel. Use this to generate the full ssh command:
gcloud compute ssh INSTANCE_NAME --dry-run
Tunneling RDP connections
You can connect to Windows instances that don't have an external IP address by tunneling RDP traffic through IAP:
IAP Desktop
You can use IAP Desktop to connect to the Remote Desktop of one or more VM instances by using IAP TCP forwarding.
In the application, select File > Add Google Cloud project.
Enter the ID or name of your project and click OK.
In the Project Explorer window, right-click the VM instance you want to connect to and select Connect.

For more information on IAP Desktop, see the GitHub project page.
gcloud
To connect to the Remote Desktop of a VM instance, you first create a tunnel.
Use the
gcloud compute start-iap-tunnelcommand to create an encrypted tunnel to the RDP port of the VM instance.gcloud compute start-iap-tunnel INSTANCE_NAME 3389 \ --local-host-port=localhost:LOCAL_PORT \ --zone=ZONEReplace INSTANCE_NAME with the name of the VM instance you want to connect to. Replace LOCAL_PORT with the localhost port where you want the proxy to be bound or use 0 to have an unused one selected automatically. Replace ZONE with the zone where the VM instance is located.
gcloudperforms a connectivity test with the VM instance, then opens a tunnel and shows a port number.Listening on port [LOCAL_PORT].
All traffic sent to localhost:LOCAL_PORT is forwarded to the VM instance. The port is only accessible by applications running on your local computer.
Leave
gcloudrunning and open the Microsoft Windows Remote Desktop Connection app.Enter the tunnel endpoint as computer name:
localhost:LOCAL_PORT
Replace LOCAL_PORT with the port number shown when the tunnel was opened by
gcloud.Click Connect.
Tunneling other TCP connections
You can use IAP TCP forwarding for other TCP-based protocols by
using the
gcloud compute start-iap-tunnel
command to allocate a local port. The local port tunnels data traffic from the
local machine to the remote machine in an HTTPS stream. IAP
then receives the data, applies access controls, and forwards the unwrapped data
to the remote port. Conversely, any data from the remote port is also wrapped
before it's sent to the local port where it's then unwrapped.
gcloud
Create an encrypted tunnel to a port of the VM instance:
gcloud compute start-iap-tunnel INSTANCE_NAME INSTANCE_PORT \
--local-host-port=localhost:LOCAL_PORT \
--zone=ZONEReplace INSTANCE_NAME and INSTANCE_PORT with the name and port of the VM instance you want to connect to. Replace LOCAL_PORT with the localhost port where you want the proxy to be bound. Replace ZONE with the zone where the VM instance is located.
gcloud performs a connectivity test with the VM instance, then opens a
tunnel and shows a port number.
Listening on port [LOCAL_PORT].
All traffic sent to localhost:LOCAL_PORT is forwarded to the VM instance. The port is only accessible by applications running on your local computer.
Increasing the IAP TCP upload bandwidth
To increase the IAP TCP upload bandwidth consider installing NumPy in the same machine where gcloud CLI is installed.
Linux
To install NumPy using pip in Unix platforms, run the following command in a new terminal instance:
$(gcloud info --format="value(basic.python_location)") -m pip install numpy
If the error message persists after installing NumPy, complete the following step: Run the following command to allow gcloud to access external packages:
export CLOUDSDK_PYTHON_SITEPACKAGES=1
Windows
To install NumPy using pip in Windows platforms, run the following command in a new PowerShell instance:
start (gcloud info --format="value(basic.python_location)") "-m pip install numpy"
If the message still persists after installing NumPy, another step is necessary. Run the following command to allow gcloud to access external packages:
$env:CLOUDSDK_PYTHON_SITEPACKAGES="1"
Known limitations
Bandwidth: IAP's TCP forwarding feature isn't intended for bulk transfer of data. IAP reserves the right to rate-limit users abusing this service.
Connection length: IAP automatically disconnects sessions
after one hour of inactivity. Currently gcloud compute start-iap-tunnel attempts to reestablish the tunnel if it becomes disconnected.
Next steps
- Set richer context rules by applying access levels.
- See access requests by enabling Cloud Audit Logs.
- Learn more about IAP.
