Halaman ini menjelaskan cara menggunakan Identity and Access Management (IAM) untuk mengontrol akses ke resource dalam aktivasi level project Security Command Center. Lihat halaman ini hanya jika Security Command Center tidak diaktifkan untuk organisasi Anda.
Lihat IAM untuk aktivasi tingkat organisasi—bukan halaman ini—jika salah satu kondisi berikut berlaku:
- Security Command Center diaktifkan di level organisasi, bukan di level project.
- Security Command Center Standard sudah diaktifkan di level organisasi. Selain itu, Anda telah mengaktifkan Security Command Center Premium di satu atau beberapa project.
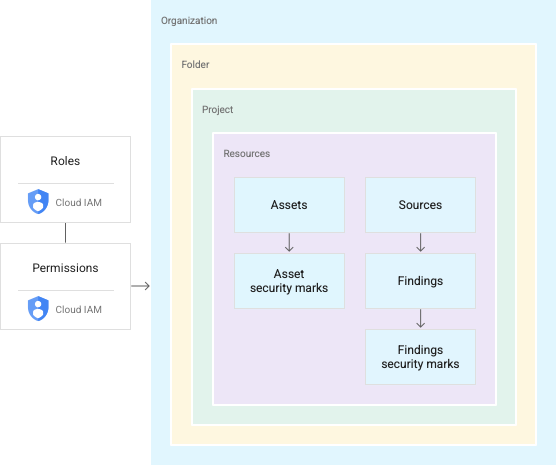
Security Command Center menggunakan peran IAM untuk memungkinkan Anda mengontrol siapa yang dapat melakukan apa pada aset, temuan, dan sumber keamanan di lingkungan Security Command Center Anda. Anda memberikan peran kepada individu dan aplikasi, dan setiap peran memberikan izin tertentu.
Izin
Untuk menyiapkan Security Command Center atau mengubah konfigurasi project, Anda memerlukan kedua peran berikut:
- Project IAM Admin (
roles/resourcemanager.projectIamAdmin) - Admin Pusat Keamanan (
roles/securitycenter.admin)
Jika pengguna tidak memerlukan izin edit, pertimbangkan untuk memberi mereka peran pelihat.
Untuk melihat semua aset dan temuan di Security Command Center, pengguna memerlukan peran Security Center Admin Viewer (roles/securitycenter.adminViewer). Pengguna yang juga
perlu melihat setelan memerlukan peran Security Center Settings Viewer
(roles/securitycenter.settingsViewer).
Meskipun Anda dapat menetapkan semua peran ini di tingkat hierarki resource mana pun, sebaiknya tetapkan peran ini di tingkat project. Praktik ini sesuai dengan prinsip hak istimewa terendah.
Untuk mengetahui petunjuk tentang cara mengelola peran dan izin, lihat Mengelola akses ke project, folder, dan organisasi.
Akses yang diwariskan ke aktivasi Security Command Center level project
Project mewarisi binding peran apa pun yang ditetapkan di tingkat folder
dan organisasi yang berisi project tersebut. Misalnya, jika akun utama memiliki
peran Editor Temuan Security Center (roles/securitycenter.findingsEditor) di
tingkat organisasi, akun utama tersebut memiliki peran yang sama di tingkat project.
Principal tersebut dapat melihat dan mengedit temuan di project organisasi tersebut yang mengaktifkan Security Command Center.
Gambar berikut mengilustrasikan hierarki resource Security Command Center dengan peran yang diberikan di tingkat organisasi.
Untuk melihat daftar akun utama yang memiliki akses ke project Anda, termasuk akun utama yang telah mewarisi izin, lihat Melihat akses saat ini.
Peran Security Command Center
Peran IAM berikut tersedia untuk Security Command Center. Anda dapat memberikan peran ini di tingkat organisasi, folder, atau project.
| Role | Permissions |
|---|---|
Security Center Admin( Admin(super user) access to security center Lowest-level resources where you can grant this role:
|
|
Security Center Admin Editor( Admin Read-write access to security center Lowest-level resources where you can grant this role:
|
|
Security Center Admin Viewer( Admin Read access to security center Lowest-level resources where you can grant this role:
|
|
Security Center Asset Security Marks Writer( Write access to asset security marks Lowest-level resources where you can grant this role:
|
|
Security Center Assets Discovery Runner( Run asset discovery access to assets Lowest-level resources where you can grant this role:
|
|
Security Center Assets Viewer( Read access to assets Lowest-level resources where you can grant this role:
|
|
Security Center Attack Paths Reader( Read access to security center attack paths |
|
Attack Surface Management Scanner Service Agent( Gives Mandiant Attack Surface Management the ability to scan Cloud Platform resources. |
|
Security Center Automation Service Agent( Security Center automation service agent can configure GCP resources to enable security scanning. |
|
Security Center BigQuery Exports Editor( Read-Write access to security center BigQuery Exports |
|
Security Center BigQuery Exports Viewer( Read access to security center BigQuery Exports |
|
Security Center Compliance Reports Viewer Beta( Read access to security center compliance reports |
|
Security Center Compliance Snapshots Viewer Beta( Read access to security center compliance snapshots |
|
Security Center Control Service Agent( Security Center Control service agent can monitor and configure GCP resources and import security findings. |
|
Security Center External Systems Editor( Write access to security center external systems |
|
Security Center Finding Security Marks Writer( Write access to finding security marks Lowest-level resources where you can grant this role:
|
|
Security Center Findings Bulk Mute Editor( Ability to mute findings in bulk |
|
Security Center Findings Editor( Read-write access to findings Lowest-level resources where you can grant this role:
|
|
Security Center Findings Mute Setter( Set mute access to findings |
|
Security Center Findings State Setter( Set state access to findings Lowest-level resources where you can grant this role:
|
|
Security Center Findings Viewer( Read access to findings Lowest-level resources where you can grant this role:
|
|
Security Center Findings Workflow State Setter Beta( Set workflow state access to findings Lowest-level resources where you can grant this role:
|
|
Security Center Integration Executor Service Agent( Gives Security Center access to execute Integrations. |
|
Security Center Issues Editor( Write access to security center issues |
|
Security Center Issues Viewer( Read access to security center issues |
|
Security Center Mute Configurations Editor( Read-Write access to security center mute configurations |
|
Security Center Mute Configurations Viewer( Read access to security center mute configurations |
|
Security Center Notification Configurations Editor( Write access to notification configurations Lowest-level resources where you can grant this role:
|
|
Security Center Notification Configurations Viewer( Read access to notification configurations Lowest-level resources where you can grant this role:
|
|
Security Center Notification Service Agent( Security Center service agent can publish notifications to Pub/Sub topics. |
|
Security Center Resource Value Configurations Editor( Read-Write access to security center resource value configurations |
|
Security Center Resource Value Configurations Viewer( Read access to security center resource value configurations |
|
Security Center Risk Reports Viewer( Read access to security center risk reports |
|
Security Health Analytics Custom Modules Tester( Test access to Security Health Analytics Custom Modules |
|
Security Health Analytics Service Agent( Security Health Analytics service agent can scan GCP resource metadata to find security vulnerabilities. |
|
Google Cloud Security Response Service Agent( Gives Playbook Runner permissions to execute all Google authored Playbooks. This role will keep evolving as we add more playbooks |
|
Security Center Service Agent( Security Center service agent can scan GCP resources and import security scans. |
|
Security Center Settings Admin( Admin(super user) access to security center settings Lowest-level resources where you can grant this role:
|
|
Security Center Settings Editor( Read-Write access to security center settings Lowest-level resources where you can grant this role:
|
|
Security Center Settings Viewer( Read access to security center settings Lowest-level resources where you can grant this role:
|
|
Security Center Simulations Reader( Read access to security center simulations |
|
Security Center Sources Admin( Admin access to sources Lowest-level resources where you can grant this role:
|
|
Security Center Sources Editor( Read-write access to sources Lowest-level resources where you can grant this role:
|
|
Security Center Sources Viewer( Read access to sources Lowest-level resources where you can grant this role:
|
|
Security Center Valued Resources Reader( Read access to security center valued resources |
|
Peran Security Command Center Management API
Peran IAM berikut tersedia untuk Security Command Center Management API. Anda dapat memberikan peran ini di tingkat organisasi, folder, atau project.
| Role | Permissions |
|---|---|
Security Center Management Admin( Full access to manage Cloud Security Command Center services and custom modules configuration. |
|
Security Center Management Custom Modules Editor( Full access to manage Cloud Security Command Center custom modules. |
|
Security Center Management Custom Modules Viewer( Readonly access to Cloud Security Command Center custom modules. |
|
Security Center Management Custom ETD Modules Editor( Full access to manage Cloud Security Command Center ETD custom modules. |
|
Security Center Management ETD Custom Modules Viewer( Readonly access to Cloud Security Command Center ETD custom modules. |
|
Security Center Management Services Editor( Full access to manage Cloud Security Command Center services configuration. |
|
Security Center Management Services Viewer( Readonly access to Cloud Security Command Center services configuration. |
|
Security Center Management Settings Editor( Full access to manage Cloud Security Command Center settings |
|
Security Center Management Settings Viewer( Readonly access to Cloud Security Command Center settings |
|
Security Center Management SHA Custom Modules Editor( Full access to manage Cloud Security Command Center SHA custom modules. |
|
Security Center Management SHA Custom Modules Viewer( Readonly access to Cloud Security Command Center SHA custom modules. |
|
Security Center Management Viewer( Readonly access to Cloud Security Command Center services and custom modules configuration. |
|
Peran agen layanan
Agen layanan memungkinkan layanan mengakses resource Anda.
Setelah Anda mengaktifkan Security Command Center, dua agen layanan, yang merupakan jenis akun layanan, akan dibuat untuk Anda:
service-project-PROJECT_NUMBER@security-center-api.iam.gserviceaccount.com.Agen layanan ini memerlukan peran IAM
securitycenter.serviceAgent.service-project-PROJECT_NUMBER@gcp-sa-ktd-hpsa.iam.gserviceaccount.com.Agen layanan ini memerlukan peran IAM
roles/containerthreatdetection.serviceAgent.
Agar Security Command Center dapat berfungsi, agen layanan harus diberi peran IAM yang diperlukan. Anda akan diminta untuk memberikan peran selama proses aktivasi Security Command Center.
Untuk melihat izin setiap peran, lihat hal berikut:
Untuk memberikan peran, Anda harus memiliki peran roles/resourcemanager.projectIamAdmin.
Jika Anda tidak memiliki peran roles/resourcemanager.organizationAdmin,
administrator organisasi Anda
dapat memberikan peran kepada agen layanan untuk Anda
dengan perintah gcloud CLI berikut:
gcloud organizations add-iam-policy-binding PROJECT_ID \
--member="SERVICE_ACCOUNT_NAME" \
--role="IAM_ROLE"
Ganti kode berikut:
PROJECT_ID: project ID AndaSERVICE_AGENT_NAME: salah satu nama agen layanan berikut:service-project-PROJECT_NUMBER@security-center-api.iam.gserviceaccount.comservice-project-PROJECT_NUMBER@gcp-sa-ktd-hpsa.iam.gserviceaccount.com
IAM_ROLE: peran wajib berikut yang sesuai dengan agen layanan yang ditentukan:roles/securitycenter.serviceAgentroles/containerthreatdetection.serviceAgent
Untuk menemukan project ID dan nomor project Anda, lihat Mengidentifikasi project.
Untuk mengetahui informasi selengkapnya tentang peran IAM, lihat memahami peran.
Peran Web Security Scanner
Peran IAM berikut tersedia untuk Web Security Scanner. Anda dapat memberikan peran ini di tingkat project.
| Role | Permissions |
|---|---|
Web Security Scanner Editor( Full access to all Web Security Scanner resources Lowest-level resources where you can grant this role:
|
|
Web Security Scanner Runner( Read access to Scan and ScanRun, plus the ability to start scans Lowest-level resources where you can grant this role:
|
|
Web Security Scanner Viewer( Read access to all Web Security Scanner resources Lowest-level resources where you can grant this role:
|
|
Cloud Web Security Scanner Service Agent( Gives the Cloud Web Security Scanner service account access to compute engine details and app engine details. |
|

