Esta página descreve como usar a gestão de identidade e acesso (IAM) para controlar o acesso aos recursos numa ativação ao nível da organização do Security Command Center. Esta página é relevante para si se se aplicar uma das seguintes condições:
- O Security Command Center é ativado ao nível da organização e não ao nível do projeto.
- O Security Command Center Standard já está ativado ao nível da organização. Além disso, tem o Security Command Center Premium ativado num ou mais projetos.
Se ativou o Security Command Center ao nível do projeto e não ao nível da organização, consulte o artigo IAM para ativações ao nível do projeto.
Numa ativação do Security Command Center ao nível da organização, pode controlar o acesso aos recursos a diferentes níveis da hierarquia de recursos. O Security Command Center usa funções do IAM para lhe permitir controlar quem pode fazer o quê com os recursos, os resultados e as origens de segurança no seu ambiente do Security Command Center. Concede funções a indivíduos e aplicações, e cada função fornece autorizações específicas.
Autorizações
Necessário para a ativação
Para ativar o Security Command Center, consulte uma das seguintes opções com base no seu nível de serviço.
Necessário para a administração e a utilização contínuas
Esta secção descreve as autorizações necessárias para administrar e usar o Security Command Center Premium e Standard. Para ver informações sobre o Security Command Center Enterprise, consulte o artigo Configure autorizações para a utilização contínua do Security Command Center Enterprise
Para alterar a configuração da sua organização, precisa de ter as seguintes funções ao nível da organização:
-
Administrador da organização (
roles/resourcemanager.organizationAdmin) -
Administrador do centro de segurança (
roles/securitycenter.admin)
Se um utilizador não precisar de autorizações de edição, pondere conceder-lhe funções de visualizador.
Para ver todos os recursos, as conclusões e os caminhos de ataque no Security Command Center, os utilizadores precisam da função
Visualizador de administração do centro de segurança
(roles/securitycenter.adminViewer) ao nível da organização.
Para ver as definições, os utilizadores precisam da função
Administrador do centro de segurança (roles/securitycenter.admin) ao nível da organização.
Para restringir o acesso a pastas e projetos individuais, não conceda todas as funções ao nível da organização. Em alternativa, conceda as seguintes funções ao nível da pasta ou projeto:
-
Visualizador de recursos do Centro de segurança (
roles/securitycenter.assetsViewer) - Visualizador de resultados do Centro de segurança
(
roles/securitycenter.findingsViewer)
Cada serviço de deteção pode exigir autorizações adicionais para o ativar ou configurar. Consulte a documentação específica de cada serviço para mais informações.
Funções ao nível da organização
Quando as funções do IAM são aplicadas ao nível da organização, os projetos e as pastas nessa organização herdam as respetivas associações de funções.
A figura seguinte ilustra uma hierarquia de recursos típica do Security Command Center com funções concedidas ao nível da organização.
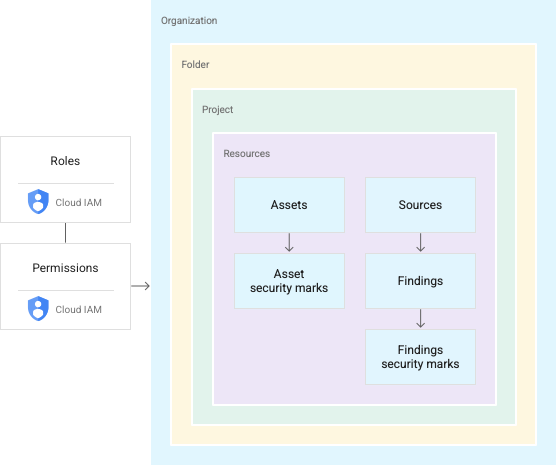
As funções de IAM incluem autorizações para ver, editar, atualizar, criar ou eliminar recursos. As funções concedidas ao nível da organização no Security Command Center
permitem-lhe realizar ações prescritas em conclusões, recursos e origens de segurança
em toda a sua organização. Por exemplo, um utilizador ao qual foi concedida a
função de editor de resultados do Centro de Segurança (roles/securitycenter.findingsEditor)
pode ver ou editar resultados anexados a qualquer recurso em qualquer projeto ou pasta na
sua organização. Com esta estrutura, não tem de conceder funções aos utilizadores em cada pasta ou projeto.
Para obter instruções sobre como gerir funções e autorizações, consulte o artigo Faça a gestão do acesso a projetos, pastas e organizações.
As funções ao nível da organização não são adequadas para todos os exemplos de utilização, particularmente para aplicações sensíveis ou normas de conformidade que requerem controlos de acesso rigorosos. Para criar políticas de acesso detalhadas, pode conceder funções ao nível da pasta e do projeto.
Funções ao nível da pasta e do projeto
O Security Command Center permite-lhe conceder funções da IAM do Security Command Center para pastas e projetos específicos, criando várias vistas ou silos na sua organização. Concede aos utilizadores e grupos diferentes autorizações de acesso e edição a pastas e projetos na sua organização.
O vídeo seguinte descreve como conceder funções ao nível da pasta e do projeto, e como as gerir na consola do Security Command Center.
Com as funções de pastas e projetos, os utilizadores com funções do Security Command Center têm a capacidade de gerir recursos e resultados em projetos ou pastas designados. Por exemplo, um engenheiro de segurança pode ter acesso limitado a projetos e pastas selecionados, enquanto um administrador de segurança pode gerir todos os recursos ao nível da organização.
As funções de pastas e projetos permitem que as autorizações do Security Command Center sejam aplicadas a níveis inferiores da hierarquia de recursos da sua organização, mas não alteram a hierarquia. A figura seguinte ilustra um utilizador com autorizações do Security Command Center para aceder a resultados num projeto específico.
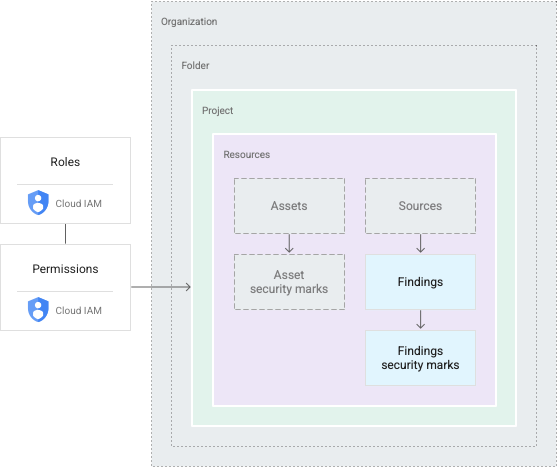
Os utilizadores com funções de pastas e projetos veem um subconjunto dos recursos de uma organização. As ações que realizam estão limitadas ao mesmo âmbito. Por exemplo, se um utilizador tiver autorizações para uma pasta, pode aceder aos recursos em qualquer projeto na pasta. As autorizações de um projeto dão aos utilizadores acesso aos recursos nesse projeto.
Para obter instruções sobre como gerir funções e autorizações, consulte o artigo Faça a gestão do acesso a projetos, pastas e organizações.
Restrições de funções
Ao conceder funções do Security Command Center ao nível da pasta ou do projeto, os administradores do Security Command Center podem fazer o seguinte:
- Limite as autorizações de visualização ou edição do Security Command Center a pastas e projetos específicos
- Conceda autorizações de visualização e edição para grupos de recursos ou resultados a utilizadores ou equipas específicos
- Restringir a capacidade de ver ou editar detalhes de descobertas, incluindo atualizações a marcas de segurança e ao estado de descoberta, a indivíduos ou grupos com acesso à descoberta subjacente
- Controlar o acesso às definições do Security Command Center, que só podem ser vistas por indivíduos com funções ao nível da organização
Funções do Security Command Center
As funções do Security Command Center também estão restritas com base nas autorizações de visualização e edição.
Na Google Cloud consola, o Security Command Center permite que os indivíduos sem autorizações ao nível da organização escolham apenas os recursos aos quais têm acesso. A seleção atualiza todos os elementos da interface do utilizador, incluindo recursos, resultados e controlos de definições. Os utilizadores veem os privilégios associados às respetivas funções e se podem aceder ou editar as conclusões no âmbito atual.
A API Security Command Center e a CLI gcloud também restringem as funções a pastas e projetos prescritos. Se as chamadas para listar ou agrupar recursos e resultados forem feitas por utilizadores aos quais foram concedidas funções de pasta ou projeto, apenas são devolvidos resultados ou recursos nesses âmbitos.
Para ativações do Security Command Center ao nível da organização, as chamadas para criar ou atualizar resultados e notificações de resultados só suportam o âmbito da organização. Precisa de funções ao nível da organização para realizar estas tarefas.
Para ver os caminhos de ataque gerados pelas simulações de caminhos de ataque, as autorizações adequadas têm de ser concedidas ao nível da organização e a Google Cloud vista da consola tem de estar definida para a organização.
Recursos para pais sobre as conclusões
Normalmente, uma descoberta está associada a um recurso, como uma máquina virtual (VM) ou uma firewall. O Security Command Center anexa as conclusões ao contentor mais imediato para o recurso que gerou a conclusão. Por exemplo, se uma MV gerar uma descoberta, a descoberta é anexada ao projeto que contém a MV. As conclusões que não estão associadas a um Google Cloud recurso são anexadas à organização e são visíveis para qualquer pessoa com autorizações do Security Command Center ao nível da organização.
Funções do Security Command Center
As seguintes funções da IAM estão disponíveis para o Security Command Center. Pode conceder estas funções ao nível da organização, da pasta ou do projeto.
| Role | Permissions |
|---|---|
Security Center Admin( Admin(super user) access to security center Lowest-level resources where you can grant this role:
|
|
Security Center Admin Editor( Admin Read-write access to security center Lowest-level resources where you can grant this role:
|
|
Security Center Admin Viewer( Admin Read access to security center Lowest-level resources where you can grant this role:
|
|
Security Center Asset Security Marks Writer( Write access to asset security marks Lowest-level resources where you can grant this role:
|
|
Security Center Assets Discovery Runner( Run asset discovery access to assets Lowest-level resources where you can grant this role:
|
|
Security Center Assets Viewer( Read access to assets Lowest-level resources where you can grant this role:
|
|
Security Center Attack Paths Reader( Read access to security center attack paths |
|
Attack Surface Management Scanner Service Agent( Gives Mandiant Attack Surface Management the ability to scan Cloud Platform resources. |
|
Security Center Automation Service Agent( Security Center automation service agent can configure GCP resources to enable security scanning. |
|
Security Center BigQuery Exports Editor( Read-Write access to security center BigQuery Exports |
|
Security Center BigQuery Exports Viewer( Read access to security center BigQuery Exports |
|
Security Center Compliance Reports Viewer Beta( Read access to security center compliance reports |
|
Security Center Compliance Snapshots Viewer Beta( Read access to security center compliance snapshots |
|
Security Center Control Service Agent( Security Center Control service agent can monitor and configure GCP resources and import security findings. |
|
Security Center External Systems Editor( Write access to security center external systems |
|
Security Center Finding Security Marks Writer( Write access to finding security marks Lowest-level resources where you can grant this role:
|
|
Security Center Findings Bulk Mute Editor( Ability to mute findings in bulk |
|
Security Center Findings Editor( Read-write access to findings Lowest-level resources where you can grant this role:
|
|
Security Center Findings Mute Setter( Set mute access to findings |
|
Security Center Findings State Setter( Set state access to findings Lowest-level resources where you can grant this role:
|
|
Security Center Findings Viewer( Read access to findings Lowest-level resources where you can grant this role:
|
|
Security Center Findings Workflow State Setter Beta( Set workflow state access to findings Lowest-level resources where you can grant this role:
|
|
Security Center Integration Executor Service Agent( Gives Security Center access to execute Integrations. |
|
Security Center Issues Editor( Write access to security center issues |
|
Security Center Issues Viewer( Read access to security center issues |
|
Security Center Mute Configurations Editor( Read-Write access to security center mute configurations |
|
Security Center Mute Configurations Viewer( Read access to security center mute configurations |
|
Security Center Notification Configurations Editor( Write access to notification configurations Lowest-level resources where you can grant this role:
|
|
Security Center Notification Configurations Viewer( Read access to notification configurations Lowest-level resources where you can grant this role:
|
|
Security Center Notification Service Agent( Security Center service agent can publish notifications to Pub/Sub topics. |
|
Security Center Resource Value Configurations Editor( Read-Write access to security center resource value configurations |
|
Security Center Resource Value Configurations Viewer( Read access to security center resource value configurations |
|
Security Center Risk Reports Viewer( Read access to security center risk reports |
|
Security Health Analytics Custom Modules Tester( Test access to Security Health Analytics Custom Modules |
|
Security Health Analytics Service Agent( Security Health Analytics service agent can scan GCP resource metadata to find security vulnerabilities. |
|
Google Cloud Security Response Service Agent( Gives Playbook Runner permissions to execute all Google authored Playbooks. This role will keep evolving as we add more playbooks |
|
Security Center Service Agent( Security Center service agent can scan GCP resources and import security scans. |
|
Security Center Settings Admin( Admin(super user) access to security center settings Lowest-level resources where you can grant this role:
|
|
Security Center Settings Editor( Read-Write access to security center settings Lowest-level resources where you can grant this role:
|
|
Security Center Settings Viewer( Read access to security center settings Lowest-level resources where you can grant this role:
|
|
Security Center Simulations Reader( Read access to security center simulations |
|
Security Center Sources Admin( Admin access to sources Lowest-level resources where you can grant this role:
|
|
Security Center Sources Editor( Read-write access to sources Lowest-level resources where you can grant this role:
|
|
Security Center Sources Viewer( Read access to sources Lowest-level resources where you can grant this role:
|
|
Security Center Valued Resources Reader( Read access to security center valued resources |
|
Funções da API Security Command Center Management
As seguintes funções de IAM estão disponíveis para a API Google Cloud Security Command Center Management. Pode conceder estas funções ao nível da organização, da pasta ou do projeto.
| Role | Permissions |
|---|---|
Security Center Management Admin( Full access to manage Cloud Security Command Center services and custom modules configuration. |
|
Security Center Management Custom Modules Editor( Full access to manage Cloud Security Command Center custom modules. |
|
Security Center Management Custom Modules Viewer( Readonly access to Cloud Security Command Center custom modules. |
|
Security Center Management Custom ETD Modules Editor( Full access to manage Cloud Security Command Center ETD custom modules. |
|
Security Center Management ETD Custom Modules Viewer( Readonly access to Cloud Security Command Center ETD custom modules. |
|
Security Center Management Services Editor( Full access to manage Cloud Security Command Center services configuration. |
|
Security Center Management Services Viewer( Readonly access to Cloud Security Command Center services configuration. |
|
Security Center Management Settings Editor( Full access to manage Cloud Security Command Center settings |
|
Security Center Management Settings Viewer( Readonly access to Cloud Security Command Center settings |
|
Security Center Management SHA Custom Modules Editor( Full access to manage Cloud Security Command Center SHA custom modules. |
|
Security Center Management SHA Custom Modules Viewer( Readonly access to Cloud Security Command Center SHA custom modules. |
|
Security Center Management Viewer( Readonly access to Cloud Security Command Center services and custom modules configuration. |
|
Funções de IAM no Gestor de conformidade
Segue-se uma lista de funções e autorizações de IAM disponíveis para o serviço Gestor de conformidade. Pode conceder estas funções ao nível da organização, da pasta ou do projeto.
| Role | Permissions |
|---|---|
Compliance Manager Admin Beta( Full access to Compliance Manager resources. |
|
Cloud Security Compliance Service Agent( Gives CSC Service Account access to consumer resources. |
|
Compliance Manager Viewer Beta( Readonly access to Compliance Manager resources. |
|
Funções da API Security Posture
As seguintes funções da IAM estão disponíveis para a API Security Posture e a respetiva funcionalidade de validação de infraestrutura como código (IaC). Exceto indicação em contrário, pode conceder estas funções ao nível da organização, da pasta ou do projeto.
| Role | Permissions |
|---|---|
Security Posture Admin( Full access to Security Posture service APIs. Lowest-level resources where you can grant this role:
|
|
Security Posture Deployer( Mutate and read permissions to the Posture Deployment resource. |
|
Security Posture Deployments Viewer( Read only access to the Posture Deployment resource. |
|
Security Posture Resource Editor( Mutate and read permissions to the Posture resource. |
|
Security Posture Resource Viewer( Read only access to the Posture resource. |
|
Security Posture Shift-Left Validator( Create access for Reports, e.g. IaC Validation Report. |
|
Security Posture Viewer( Read only access to all the SecurityPosture Service resources. |
|
Funções de IAM na gestão da postura de segurança dos dados
Segue-se uma lista de funções e autorizações de IAM disponíveis para o serviço de gestão da postura de segurança de dados (DSPM). Pode conceder estas funções ao nível da organização, da pasta ou do projeto.
| Role | Permissions |
|---|---|
Data Security Posture Management Admin( Full access to Data Security Posture Management resources. |
|
DSPM Service Agent( Gives DSPM Service Account access to consumer resources. |
|
Data Security Posture Management Viewer( Readonly access to Data Security Posture Management resources. |
|
Funções de agente do serviço
Um agente de serviço permite que um serviço aceda aos seus recursos.
Depois de ativar o Security Command Center, são criados dois agentes de serviço para si:
service-org-ORGANIZATION_ID@security-center-api.iam.gserviceaccount.com.Este agente do serviço requer a função do IAM.
roles/securitycenter.serviceAgentservice-org-ORGANIZATION_ID@gcp-sa-ktd-hpsa.iam.gserviceaccount.com.Este agente do serviço requer a função do IAM.
roles/containerthreatdetection.serviceAgent
Durante o processo de ativação do Security Command Center, é-lhe pedido que conceda uma ou mais funções do IAM a cada agente de serviço. A concessão das funções a cada agente de serviço é necessária para o Security Command Center funcionar.
Para ver as autorizações de cada função, consulte o seguinte:
Para conceder as funções, tem de ter a função roles/resourcemanager.organizationAdmin
Se não tiver a função roles/resourcemanager.organizationAdmin, o administrador da sua organização pode conceder as funções aos agentes de serviço com o seguinte comando da CLI gcloud:
gcloud organizations add-iam-policy-binding ORGANIZATION_ID \
--member="SERVICE_AGENT_NAME" \
--role="IAM_ROLE"
Substitua o seguinte:
ORGANIZATION_ID: o ID da sua organizaçãoSERVICE_AGENT_NAME: o nome do agente do serviço ao qual está a conceder a função. O nome é um dos seguintes nomes de agentes do serviço:service-org-ORGANIZATION_ID@security-center-api.iam.gserviceaccount.comservice-org-ORGANIZATION_ID@gcp-sa-ktd-hpsa.iam.gserviceaccount.com
IAM_ROLE: a seguinte função obrigatória que corresponde ao agente do serviço especificado:roles/securitycenter.serviceAgentroles/containerthreatdetection.serviceAgent
Para mais informações sobre as funções de IAM, consulte o artigo Compreender as funções.
Funções do Web Security Scanner
As seguintes funções IAM estão disponíveis para o Web Security Scanner. Pode conceder estas funções ao nível do projeto.
| Role | Permissions |
|---|---|
Web Security Scanner Editor( Full access to all Web Security Scanner resources Lowest-level resources where you can grant this role:
|
|
Web Security Scanner Runner( Read access to Scan and ScanRun, plus the ability to start scans Lowest-level resources where you can grant this role:
|
|
Web Security Scanner Viewer( Read access to all Web Security Scanner resources Lowest-level resources where you can grant this role:
|
|
Cloud Web Security Scanner Service Agent( Gives the Cloud Web Security Scanner service account access to compute engine details and app engine details. |
|

