Questa pagina descrive come utilizzare Identity and Access Management (IAM) per controllare l'accesso alle risorse in un'attivazione a livello di organizzazione di Security Command Center. Questa pagina ti riguarda se si verifica una delle seguenti condizioni:
- Security Command Center è attivato a livello di organizzazione e non a livello di progetto.
- Security Command Center Standard è già attivato a livello di organizzazione. Inoltre, hai attivato Security Command Center Premium su uno o più progetti.
Se hai attivato Security Command Center a livello di progetto e non a livello di organizzazione, consulta IAM per le attivazioni a livello di progetto.
In un'attivazione di Security Command Center a livello di organizzazione, puoi controllare l'accesso alle risorse a diversi livelli della gerarchia delle risorse. Security Command Center utilizza i ruoli IAM per consentirti di controllare chi può fare cosa con asset, risultati e origini di sicurezza nel tuo ambiente Security Command Center. Concedi ruoli a persone e applicazioni e ogni ruolo fornisce autorizzazioni specifiche.
Autorizzazioni
Obbligatorio per l'attivazione
Per attivare Security Command Center, consulta una delle seguenti sezioni in base al tuo livello di servizio.
Necessario per l'amministrazione e l'utilizzo continui
Questa sezione descrive le autorizzazioni necessarie per amministrare e utilizzare Security Command Center Premium e Standard. Per informazioni su Security Command Center Enterprise, vedi Configurare le autorizzazioni per l'utilizzo continuo di Security Command Center Enterprise.
Per modificare la configurazione della tua organizzazione, devi disporre di entrambi i seguenti ruoli a livello di organizzazione:
-
Amministratore dell'organizzazione (
roles/resourcemanager.organizationAdmin) -
Security Center Admin (
roles/securitycenter.admin)
Se un utente non richiede autorizzazioni di modifica, valuta la possibilità di concedergli ruoli di visualizzatore.
Per visualizzare tutti gli asset, i risultati e i percorsi di attacco in Security Command Center, gli utenti devono disporre del ruolo
Visualizzatore amministratore del Centro sicurezza
(roles/securitycenter.adminViewer) a livello di organizzazione.
Per visualizzare le impostazioni, gli utenti devono disporre del ruolo
Amministratore del Centro sicurezza (roles/securitycenter.admin) a livello di organizzazione.
Per limitare l'accesso a singoli progetti e cartelle, non concedere tutti i ruoli a livello di organizzazione. Concedi invece i seguenti ruoli a livello di cartella o progetto:
-
Visualizzatore asset Centro sicurezza (
roles/securitycenter.assetsViewer) - Visualizzatore risultati Centro sicurezza
(
roles/securitycenter.findingsViewer)
Ogni servizio di rilevamento potrebbe richiedere autorizzazioni aggiuntive per essere abilitato o configurato. Per ulteriori informazioni, consulta la documentazione specifica di ogni servizio.
Ruoli a livello di organizzazione
Quando i ruoli IAM vengono applicati a livello di organizzazione, i progetti e le cartelle sotto l'organizzazione ne ereditano i binding dei ruoli.
La figura seguente illustra una tipica gerarchia delle risorse di Security Command Center con ruoli concessi a livello di organizzazione.
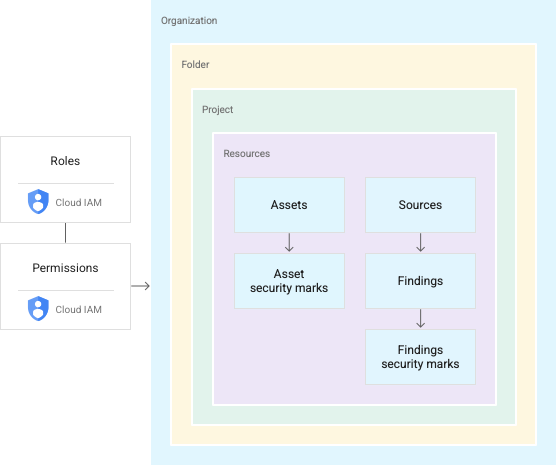
I ruoli IAM includono autorizzazioni per visualizzare, modificare, aggiornare, creare o eliminare risorse. I ruoli concessi a livello di organizzazione in Security Command Center
ti consentono di eseguire azioni prescritte su risultati, asset e origini di sicurezza
in tutta l'organizzazione. Ad esempio, un utente a cui è stato concesso il
ruolo Editor risultati del Centro sicurezza (roles/securitycenter.findingsEditor)
può visualizzare o modificare i risultati allegati a qualsiasi risorsa in qualsiasi progetto o cartella della tua organizzazione. Con questa struttura, non devi concedere ruoli agli utenti in
ogni cartella o progetto.
Per istruzioni sulla gestione di ruoli e autorizzazioni, consulta Gestire l'accesso a progetti, cartelle e organizzazioni.
I ruoli a livello di organizzazione non sono adatti a tutti i casi d'uso, in particolare per applicazioni sensibili o standard di conformità che richiedono controlli di accesso rigorosi. Per creare criteri di accesso granulari, puoi concedere ruoli a livello di cartella e progetto.
Ruoli a livello di cartella e progetto
Security Command Center ti consente di concedere ruoli IAM di Security Command Center per cartelle e progetti specifici, creando più visualizzazioni o silos all'interno della tua organizzazione. Concedi a utenti e gruppi diversi permessi di accesso e modifica a cartelle e progetti della tua organizzazione.
Il seguente video descrive come concedere ruoli a livello di cartella e progetto e come gestirli nella console Security Command Center.
Con i ruoli di cartella e progetto, gli utenti con ruoli Security Command Center hanno la possibilità di gestire asset e risultati all'interno di progetti o cartelle designati. Ad esempio, a un ingegnere della sicurezza può essere concesso l'accesso limitato a progetti e cartelle selezionati, mentre un amministratore della sicurezza può gestire tutte le risorse a livello di organizzazione.
I ruoli di cartella e progetto consentono di applicare le autorizzazioni di Security Command Center a livelli inferiori della gerarchia delle risorse della tua organizzazione, ma non modificano la gerarchia. La figura seguente mostra un utente con autorizzazioni Security Command Center per accedere ai risultati in un progetto specifico.
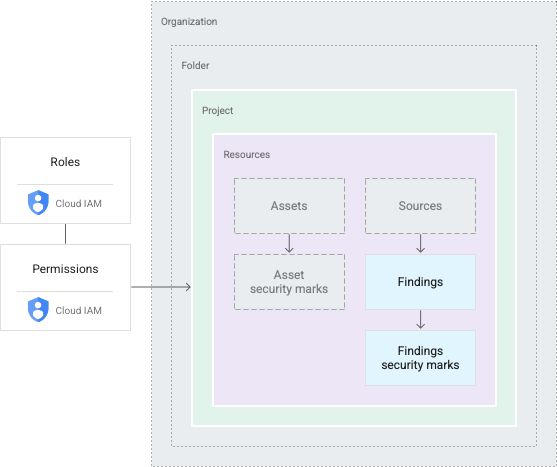
Gli utenti con ruoli a livello di cartella e progetto vedono un sottoinsieme delle risorse di un'organizzazione. Qualsiasi azione intrapresa è limitata allo stesso ambito. Ad esempio, se un utente dispone delle autorizzazioni per una cartella, può accedere alle risorse di qualsiasi progetto nella cartella. Le autorizzazioni per un progetto consentono agli utenti di accedere alle risorse del progetto.
Per istruzioni sulla gestione di ruoli e autorizzazioni, consulta Gestire l'accesso a progetti, cartelle e organizzazioni.
Limitazioni dei ruoli
Se concedi i ruoli di Security Command Center a livello di cartella o progetto, gli amministratori di Security Command Center possono:
- Limitare le autorizzazioni di visualizzazione o modifica di Security Command Center a progetti e cartelle specifici
- Concedere autorizzazioni di visualizzazione e modifica per gruppi di asset o risultati a utenti o team specifici
- Limitare la possibilità di visualizzare o modificare i dettagli dei risultati, inclusi gli aggiornamenti ai segni di sicurezza e allo stato dei risultati, a persone o gruppi con accesso al risultato sottostante
- Controllare l'accesso alle impostazioni di Security Command Center, che possono essere visualizzate solo da persone con ruoli a livello di organizzazione
Funzioni di Security Command Center
Anche le funzioni di Security Command Center sono limitate in base alle autorizzazioni di visualizzazione e modifica.
Nella console Google Cloud , Security Command Center consente alle persone senza autorizzazioni a livello di organizzazione di scegliere solo le risorse a cui hanno accesso. La selezione aggiorna tutti gli elementi dell'interfaccia utente, inclusi asset, risultati e controlli delle impostazioni. Gli utenti vedono i privilegi associati ai loro ruoli e se possono accedere o modificare i risultati nell'ambito attuale.
L'API Security Command Center e Google Cloud CLI limitano anche le funzioni a cartelle e progetti prescritti. Se le chiamate per elencare o raggruppare asset e risultati vengono effettuate da utenti a cui sono stati concessi ruoli di cartella o progetto, vengono restituiti solo i risultati o gli asset in questi ambiti.
Per le attivazioni di Security Command Center a livello di organizzazione, le chiamate per creare o aggiornare i risultati e le notifiche dei risultati supportano solo l'ambito dell'organizzazione. Per eseguire queste attività, devi disporre di ruoli a livello di organizzazione.
Per visualizzare i percorsi di attacco generati dalle simulazioni del percorso di attacco, devono essere concesse le autorizzazioni appropriate a livello di organizzazione e la visualizzazione della console Google Cloud deve essere impostata sull'organizzazione.
Risorse per i genitori per i risultati
In genere, un problema viene associato a una risorsa, ad esempio una macchina virtuale (VM) o un firewall. Security Command Center associa i risultati al container più immediato per la risorsa che ha generato il risultato. Ad esempio, se una VM genera un risultato, questo viene allegato al progetto che contiene la VM. I risultati non collegati a una risorsa Google Cloud sono associati all'organizzazione e sono visibili a chiunque disponga delle autorizzazioni di Security Command Center a livello di organizzazione.
Ruoli Security Command Center
Per Security Command Center sono disponibili i seguenti ruoli IAM. Puoi concedere questi ruoli a livello di organizzazione, cartella o progetto.
| Role | Permissions |
|---|---|
Security Center Admin( Admin(super user) access to security center Lowest-level resources where you can grant this role:
|
|
Security Center Admin Editor( Admin Read-write access to security center Lowest-level resources where you can grant this role:
|
|
Security Center Admin Viewer( Admin Read access to security center Lowest-level resources where you can grant this role:
|
|
Security Center Asset Security Marks Writer( Write access to asset security marks Lowest-level resources where you can grant this role:
|
|
Security Center Assets Discovery Runner( Run asset discovery access to assets Lowest-level resources where you can grant this role:
|
|
Security Center Assets Viewer( Read access to assets Lowest-level resources where you can grant this role:
|
|
Security Center Attack Paths Reader( Read access to security center attack paths |
|
Attack Surface Management Scanner Service Agent( Gives Mandiant Attack Surface Management the ability to scan Cloud Platform resources. |
|
Security Center Automation Service Agent( Security Center automation service agent can configure GCP resources to enable security scanning. |
|
Security Center BigQuery Exports Editor( Read-Write access to security center BigQuery Exports |
|
Security Center BigQuery Exports Viewer( Read access to security center BigQuery Exports |
|
Security Center Compliance Reports Viewer Beta( Read access to security center compliance reports |
|
Security Center Compliance Snapshots Viewer Beta( Read access to security center compliance snapshots |
|
Security Center Control Service Agent( Security Center Control service agent can monitor and configure GCP resources and import security findings. |
|
Security Center External Systems Editor( Write access to security center external systems |
|
Security Center Finding Security Marks Writer( Write access to finding security marks Lowest-level resources where you can grant this role:
|
|
Security Center Findings Bulk Mute Editor( Ability to mute findings in bulk |
|
Security Center Findings Editor( Read-write access to findings Lowest-level resources where you can grant this role:
|
|
Security Center Findings Mute Setter( Set mute access to findings |
|
Security Center Findings State Setter( Set state access to findings Lowest-level resources where you can grant this role:
|
|
Security Center Findings Viewer( Read access to findings Lowest-level resources where you can grant this role:
|
|
Security Center Findings Workflow State Setter Beta( Set workflow state access to findings Lowest-level resources where you can grant this role:
|
|
Security Center Integration Executor Service Agent( Gives Security Center access to execute Integrations. |
|
Security Center Issues Editor( Write access to security center issues |
|
Security Center Issues Viewer( Read access to security center issues |
|
Security Center Mute Configurations Editor( Read-Write access to security center mute configurations |
|
Security Center Mute Configurations Viewer( Read access to security center mute configurations |
|
Security Center Notification Configurations Editor( Write access to notification configurations Lowest-level resources where you can grant this role:
|
|
Security Center Notification Configurations Viewer( Read access to notification configurations Lowest-level resources where you can grant this role:
|
|
Security Center Notification Service Agent( Security Center service agent can publish notifications to Pub/Sub topics. |
|
Security Center Resource Value Configurations Editor( Read-Write access to security center resource value configurations |
|
Security Center Resource Value Configurations Viewer( Read access to security center resource value configurations |
|
Security Center Risk Reports Viewer( Read access to security center risk reports |
|
Security Health Analytics Custom Modules Tester( Test access to Security Health Analytics Custom Modules |
|
Security Health Analytics Service Agent( Security Health Analytics service agent can scan GCP resource metadata to find security vulnerabilities. |
|
Google Cloud Security Response Service Agent( Gives Playbook Runner permissions to execute all Google authored Playbooks. This role will keep evolving as we add more playbooks |
|
Security Center Service Agent( Security Center service agent can scan GCP resources and import security scans. |
|
Security Center Settings Admin( Admin(super user) access to security center settings Lowest-level resources where you can grant this role:
|
|
Security Center Settings Editor( Read-Write access to security center settings Lowest-level resources where you can grant this role:
|
|
Security Center Settings Viewer( Read access to security center settings Lowest-level resources where you can grant this role:
|
|
Security Center Simulations Reader( Read access to security center simulations |
|
Security Center Sources Admin( Admin access to sources Lowest-level resources where you can grant this role:
|
|
Security Center Sources Editor( Read-write access to sources Lowest-level resources where you can grant this role:
|
|
Security Center Sources Viewer( Read access to sources Lowest-level resources where you can grant this role:
|
|
Security Center Valued Resources Reader( Read access to security center valued resources |
|
Ruoli API Security Command Center Management
I seguenti ruoli IAM sono disponibili per l'API Security Command Center Management. Puoi concedere questi ruoli a livello di organizzazione, cartella o progetto.
| Role | Permissions |
|---|---|
Security Center Management Admin( Full access to manage Cloud Security Command Center services and custom modules configuration. |
|
Security Center Management Custom Modules Editor( Full access to manage Cloud Security Command Center custom modules. |
|
Security Center Management Custom Modules Viewer( Readonly access to Cloud Security Command Center custom modules. |
|
Security Center Management Custom ETD Modules Editor( Full access to manage Cloud Security Command Center ETD custom modules. |
|
Security Center Management ETD Custom Modules Viewer( Readonly access to Cloud Security Command Center ETD custom modules. |
|
Security Center Management Services Editor( Full access to manage Cloud Security Command Center services configuration. |
|
Security Center Management Services Viewer( Readonly access to Cloud Security Command Center services configuration. |
|
Security Center Management Settings Editor( Full access to manage Cloud Security Command Center settings |
|
Security Center Management Settings Viewer( Readonly access to Cloud Security Command Center settings |
|
Security Center Management SHA Custom Modules Editor( Full access to manage Cloud Security Command Center SHA custom modules. |
|
Security Center Management SHA Custom Modules Viewer( Readonly access to Cloud Security Command Center SHA custom modules. |
|
Security Center Management Viewer( Readonly access to Cloud Security Command Center services and custom modules configuration. |
|
Ruoli IAM in Compliance Manager
Di seguito è riportato un elenco di ruoli e autorizzazioni IAM disponibili per il servizio Compliance Manager. Puoi concedere questi ruoli a livello di organizzazione, cartella o progetto.
| Role | Permissions |
|---|---|
Compliance Manager Admin Beta( Full access to Compliance Manager resources. |
|
Cloud Security Compliance Service Agent( Gives CSC Service Account access to consumer resources. |
|
Compliance Manager Viewer Beta( Readonly access to Compliance Manager resources. |
|
Ruoli API Security Posture
I seguenti ruoli IAM sono disponibili per l'API Security Posture e la relativa funzionalità di convalida dell'infrastruttura come codice (IaC). Salvo diversa indicazione, puoi concedere questi ruoli a livello di organizzazione, cartella o progetto.
| Role | Permissions |
|---|---|
Security Posture Admin( Full access to Security Posture service APIs. Lowest-level resources where you can grant this role:
|
|
Security Posture Deployer( Mutate and read permissions to the Posture Deployment resource. |
|
Security Posture Deployments Viewer( Read only access to the Posture Deployment resource. |
|
Security Posture Resource Editor( Mutate and read permissions to the Posture resource. |
|
Security Posture Resource Viewer( Read only access to the Posture resource. |
|
Security Posture Shift-Left Validator( Create access for Reports, e.g. IaC Validation Report. |
|
Security Posture Viewer( Read only access to all the SecurityPosture Service resources. |
|
Ruoli IAM in Data Security Posture Management
Di seguito è riportato un elenco di ruoli e autorizzazioni IAM disponibili per il servizio Data Security Posture Management (DSPM). Puoi concedere questi ruoli a livello di organizzazione, cartella o progetto.
| Role | Permissions |
|---|---|
Data Security Posture Management Admin( Full access to Data Security Posture Management resources. |
|
DSPM Service Agent( Gives DSPM Service Account access to consumer resources. |
|
Data Security Posture Management Viewer( Readonly access to Data Security Posture Management resources. |
|
Ruoli di agente di servizio
Un service agent consente a un servizio di accedere alle tue risorse.
Dopo aver attivato Security Command Center, vengono creati due service agent:
service-org-ORGANIZATION_ID@security-center-api.iam.gserviceaccount.com.Questo service agent richiede il ruolo IAM
roles/securitycenter.serviceAgent.service-org-ORGANIZATION_ID@gcp-sa-ktd-hpsa.iam.gserviceaccount.com.Questo service agent richiede il ruolo IAM
roles/containerthreatdetection.serviceAgent.
Durante la procedura di attivazione di Security Command Center, ti viene chiesto di concedere uno o più ruoli IAM richiesti a ogni service agent. La concessione dei ruoli a ogni service agent è necessaria per il funzionamento di Security Command Center.
Per visualizzare le autorizzazioni per ogni ruolo, consulta quanto segue:
Per concedere i ruoli, devi disporre del ruolo roles/resourcemanager.organizationAdmin.
Se non disponi del ruolo roles/resourcemanager.organizationAdmin,
l'amministratore della tua organizzazione può concedere i ruoli agli agenti di servizio per tuo conto con il seguente comando gcloud CLI:
gcloud organizations add-iam-policy-binding ORGANIZATION_ID \
--member="SERVICE_AGENT_NAME" \
--role="IAM_ROLE"
Sostituisci quanto segue:
ORGANIZATION_ID: l'ID organizzazioneSERVICE_AGENT_NAME: il nome dell'agente di servizio a cui stai concedendo il ruolo. Il nome è uno dei seguenti nomi di service agent:service-org-ORGANIZATION_ID@security-center-api.iam.gserviceaccount.comservice-org-ORGANIZATION_ID@gcp-sa-ktd-hpsa.iam.gserviceaccount.com
IAM_ROLE: il seguente ruolo obbligatorio che corrisponde all'agente di servizio specificato:roles/securitycenter.serviceAgentroles/containerthreatdetection.serviceAgent
Per saperne di più sui ruoli IAM, consulta la sezione Informazioni sui ruoli.
Ruoli Web Security Scanner
Per Web Security Scanner sono disponibili i seguenti ruoli IAM. Puoi concedere questi ruoli a livello di progetto.
| Role | Permissions |
|---|---|
Web Security Scanner Editor( Full access to all Web Security Scanner resources Lowest-level resources where you can grant this role:
|
|
Web Security Scanner Runner( Read access to Scan and ScanRun, plus the ability to start scans Lowest-level resources where you can grant this role:
|
|
Web Security Scanner Viewer( Read access to all Web Security Scanner resources Lowest-level resources where you can grant this role:
|
|
Cloud Web Security Scanner Service Agent( Gives the Cloud Web Security Scanner service account access to compute engine details and app engine details. |
|

