Private NAT for Network Connectivity Center spokes
Private NAT lets you create a Private NAT gateway that works in conjunction with Network Connectivity Center spokes to perform network address translation (NAT) between the following networks:
- Virtual Private Cloud (VPC) networks: In this scenario, the VPC networks that you want to connect are attached to a Network Connectivity Center hub as VPC spokes.
- VPC networks and networks outside of Google Cloud: In this scenario, one or more VPC networks are attached to a Network Connectivity Center hub as VPC spokes and connected to your on-premises or other cloud provider networks through hybrid spokes.
Specifications
In addition to the general Private NAT specifications, Private NAT for Network Connectivity Center spokes has the following specifications:
- Private NAT uses a NAT
configuration of
type=PRIVATEto let networks with overlapping subnet IP address ranges communicate. However, only non-overlapping subnets can connect to each other. - You need to create a custom NAT rule by referencing a Network Connectivity Center hub.
The NAT rule specifies a NAT IP address range from a subnet of purpose
PRIVATE_NATthat Private NAT uses to perform NAT on traffic between your connected networks. - When you create a VM instance in a subnet range where the Private NAT applies, all egress traffic from this VM instance is translated by the gateway if the destination spoke is in the same Network Connectivity Center hub as the gateway. Private NAT translates traffic to destination spokes within the same region as the Private NAT gateway as well as across regions.
- A Private NAT gateway is associated with subnet IP address ranges in a single region in a single VPC network. This means a Private NAT gateway created in one VPC network doesn't provide NAT services to VMs in other spokes of the Network Connectivity Center hub, even if the VMs are in the same region as the gateway.
Traffic between VPC networks
The following additional specifications apply for traffic between VPC networks (Inter-VPC NAT):
- To enable Inter-VPC NAT between two VPC networks, each VPC network must be configured as a VPC spoke of a Network Connectivity Center hub. You must ensure that there are no overlapping IP address ranges across your VPC spokes. For more information, see Create a VPC spoke.
- The Network Connectivity Center hub associated with the Private NAT gateway must have at least two VPC spokes, where one of the VPC spokes is the VPC network of the Private NAT gateway.
- Inter-VPC NAT supports NAT between Network Connectivity Center VPC spokes only, and not between VPC networks connected using VPC Network Peering.
Traffic between VPC networks and other networks
The following additional specifications apply for traffic between VPC networks and networks outside of Google Cloud:
- The source VPC network must be configured as a VPC spoke of a Network Connectivity Center hub.
- A hybrid spoke must be attached to the same Network Connectivity Center hub to establish connectivity between the VPC spoke and the destination network outside of Google Cloud. For more information, see Establishing connectivity between hybrid spokes and VPC spokes.
For information about the requirements for using VPC spokes and hybrid spokes in the same Network Connectivity Center hub, see Route exchange with VPC spokes.
Basic configuration and workflow
The following diagram shows a basic Private NAT configuration for traffic between two VPC spokes:
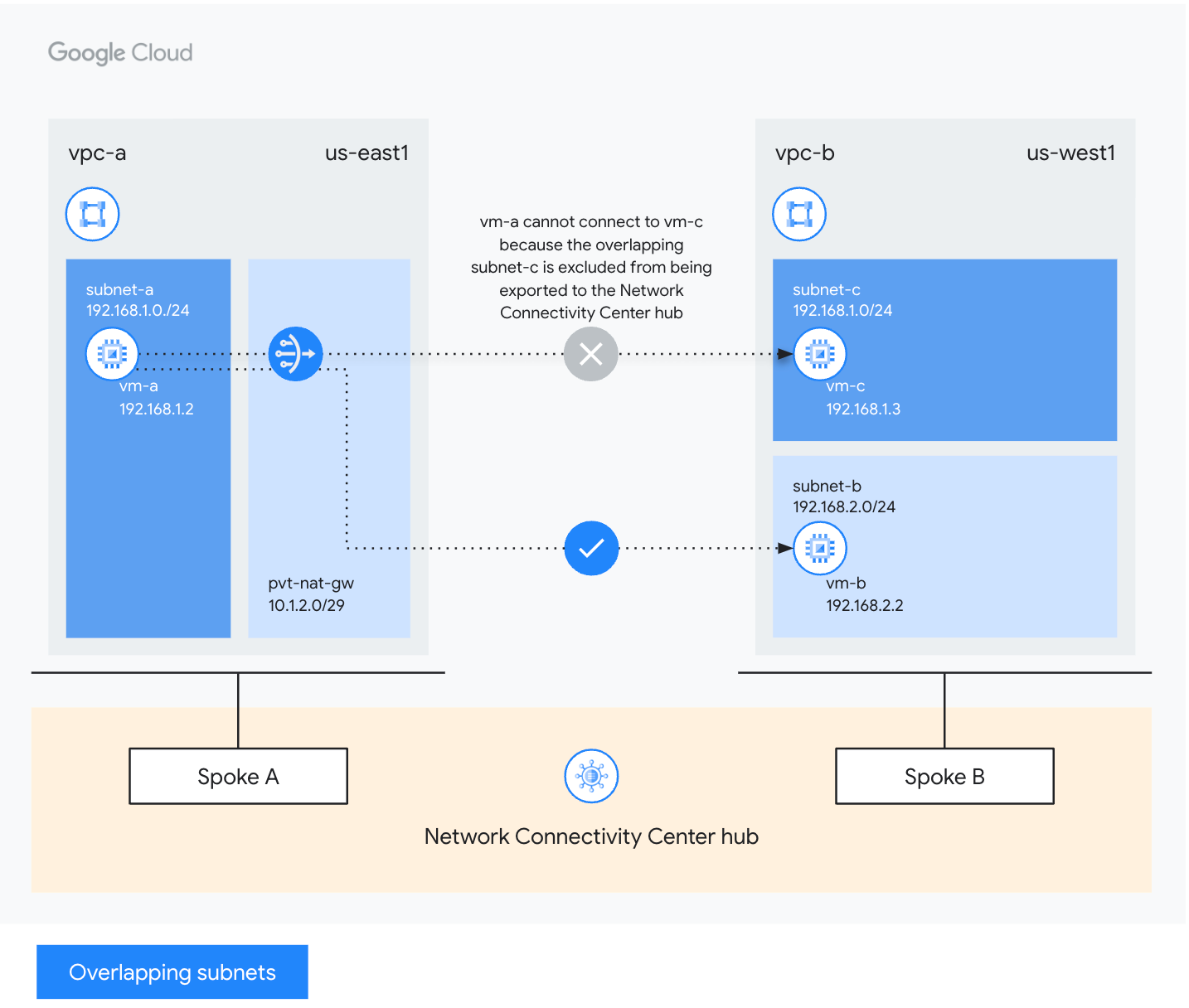
In this example, Private NAT is set up as follows:
- The
pvt-nat-gwgateway is configured invpc-ato apply to all the IP address ranges ofsubnet-ain theus-east1region. Using the NAT IP ranges ofpvt-nat-gw, a virtual machine (VM) instance insubnet-aofvpc-acan send traffic to a VM insubnet-bofvpc-b, even thoughsubnet-aofvpc-aoverlaps withsubnet-cofvpc-b. - Both
vpc-aandvpc-bare configured as spokes of a Network Connectivity Center hub. - The
pvt-nat-gwgateway is configured to provide NAT between VPC networks that are configured as VPC spokes in the same Network Connectivity Center hub.
Example workflow
In the preceding diagram, vm-a with the internal IP address 192.168.1.2 in
subnet-a of vpc-a needs to download an update from vm-b with the internal
IP address 192.168.2.2 in subnet-b of vpc-b. Both the VPC
networks are connected to the same Network Connectivity Center hub as VPC
spokes. Assume that vpc-b contains another subnet 192.168.1.0/24 that overlaps
with the subnet in vpc-a. For subnet-a of vpc-a to communicate with subnet-b
of vpc-b, you need to configure a Private NAT gateway, pvt-nat-gw,
in vpc-a as follows:
Private NAT subnet: Before configuring the Private NAT gateway, create a Private NAT subnet of purpose
PRIVATE_NAT, for example,10.1.2.0/29. Ensure that this subnet doesn't overlap with an existing subnet in any of the VPC spokes attached to the same Network Connectivity Center hub.A NAT rule whose
nexthop.hubmatches the Network Connectivity Center hub URL.NAT for all address ranges of
subnet-a.
The following table summarizes the network configuration specified in the preceding example:
| Network name | Network component | IP address/range | Region |
|---|---|---|---|
| vpc-a | subnet-a | 192.168.1.0/24 | us-east1 |
| vm-a | 192.168.1.2 | ||
| pvt-nat-gw | 10.1.2.0/29 | ||
| vpc-b | subnet-b | 192.168.2.0/24 | us-west1 |
| vm-b | 192.168.2.2 | ||
| subnet-c | 192.168.1.0/24 | ||
| vm-c | 192.168.1.3 |
Private NAT for Network Connectivity Center spokes follows the
port reservation procedure
to reserve the following NAT source IP address
and source port tuples for each of the VMs in the network. For example, the
Private NAT gateway reserves 64 source ports for vm-a:
10.1.2.2:34000 through 10.1.2.2:34063.
When the VM uses the TCP protocol to send a packet to the update server
192.168.2.2 on destination port 80, the following occurs:
The VM sends a request packet with these attributes:
- Source IP address:
192.168.1.2, the internal IP address of the VM - Source port:
24000, the ephemeral source port chosen by the VM's operating system - Destination address:
192.168.2.2, the update server's IP address - Destination port:
80, the destination port for HTTP traffic to the update server - Protocol: TCP
- Source IP address:
The
pvt-nat-gwgateway performs source network address translation (SNAT or source NAT) on egress, rewriting the request packet's NAT source IP address and source port:- NAT source IP address:
10.1.2.2, from one of the VM's reserved NAT source IP address and source port tuples - Source port:
34022, an unused source port from one of the VM's reserved source port tuples - Destination address:
192.168.2.2, unchanged - Destination port:
80, unchanged - Protocol: TCP, unchanged
- NAT source IP address:
The update server sends a response packet that arrives on the
pvt-nat-gwgateway with these attributes:- Source IP address:
192.168.2.2, the update server's internal IP address - Source port:
80, the HTTP response from the update server - Destination address:
10.1.2.2, which matches the original NAT source IP address of the request packet - Destination port:
34022, which matches the source port of the request packet - Protocol: TCP, unchanged
- Source IP address:
The
pvt-nat-gwgateway performs destination network address translation (DNAT) on the response packet, rewriting the response packet's destination address and destination port so that the packet is delivered to the VM that requested the update with the following attributes:- Source IP address:
192.168.2.2, unchanged - Source port:
80, unchanged - Destination address:
192.168.1.2, the internal IP address of the VM - Destination port:
24000, matching the original ephemeral source port of the request packet - Protocol: TCP, unchanged
- Source IP address:
What's next
- Set up Private NAT for Network Connectivity Center spokes.
- Learn about Cloud NAT product interactions.
- Learn about Cloud NAT addresses and ports.
- Learn about Cloud NAT rules.
- Troubleshoot common issues.
