Collect Microsoft Windows AD logs
This document includes the following information:
- Deployment architecture and installation steps, plus any required configuration that produce logs supported by the Google Security Operations parser for Microsoft Windows Active Directory events. For an overview of Google Security Operations data ingestion, see Data ingestion to Google Security Operations.
- Information about how the parser maps fields in the original log to Google Security Operations Unified Data Model fields.
Based on your deployment architecture, configure the Bindplane agent or the NXLog agent to ingest Microsoft Windows Active Directory logs into Google Security Operations. We recommend that you use Bindplane Agent to forward the logs of the Windows Active Directory into Google Security Operations.
Information in this document applies to the parser with the WINDOWS_AD ingestion label. The ingestion label identifies which parser normalizes raw log data to structured UDM format.
Before you begin
Before you configure Bindplane agent or the NXLog Agent, complete the following tasks:
- Configure all systems to use UTC time zone.
- Configure Microsoft Windows AD servers.
- Review supported devices and versions.
- Review supported log types.
Configure Microsoft Windows AD servers
On each Microsoft Windows Active Directory server, create and configure a PowerShell script to save the log data to an output file. Bindplane Agent or NXLog Agent reads the output file.
# Set the location where the log file will be written $OUTPUT_FILENAME="<Path_of_the_output_file>" If (Test-Path -Path $OUTPUT_FILENAME) { Remove-Item -path $OUTPUT_FILENAME -ErrorAction SilentlyContinue} # USER_CONTEXT: Gets all Active Directory users and their properties. Get-ADUser -Filter * -properties samAccountName | % { Get-ADUser $_.SamAccountName -properties * | ConvertTo-JSON -compress | Out-File -encoding utf8 $OUTPUT_FILENAME -Append } # ASSET_CONTEXT: Gets all Active Directory assets and their properties. Get-ADComputer -Filter * -properties samAccountName | % { Get-ADComputer $_.SamAccountName -properties * | ConvertTo-JSON -compress | Out-File -encoding utf8 $OUTPUT_FILENAME -Append }Replace the following :
- Replace the value of
$OUTPUT_FILENAMEwith the location of the output file. - Store the data in JSON format.
- Set the encoding to UTF-8.
- Use the
-Filterparameter, rather than the-LDAPFilterparameter, when calling theGet-ADUserandGet-ADComputercmdlets.
- Replace the value of
Create a recurring task that runs the script to fetch and write data to the output file.
- Open the Task Scheduler application.
- Click Create task.
- Enter a name and description for the task.
- Select the Run with highest privileges checkbox to make sure all data is retrieved.
- In the Triggers tab, define when you want to repeat the task.
- In the Action tab, add a new action and provide the path of the file where the script is stored.
Review supported devices and versions
Microsoft Windows Server is released with the following editions: Foundation, Essentials, Standard, and Datacenter. The event schema of logs generated by each edition does not differ.
The Google Security Operations Parser supports logs from the following Microsoft Windows server versions:
- Microsoft Windows Server 2019
- Microsoft Windows Server 2016
- Microsoft Windows Server 2012
The Google Security Operations parser supports logs that are collected by NXLog Community Edition or Enterprise Edition.
Review supported log types
The Google Security Operations parser will parse and normalize data retrieved from the User Context and the Asset Context. It supports logs generated with English language text and doesn't support logs generated in non-English languages.
Configure the Bindplane agent
We recommend that you use the Bindplane agent to forward the logs of the Windows Active Directory into Google Security Operations.
After installation, the Bindplane agent service appears as the observIQ service in the list of Windows services.
- Install the Bindplane agent on each Windows Active Directory server. For more information about installing the Bindplane agent, see the Bindplane Agent installation instructions.
Create a configuration file for the Bindplane agent with the following contents:
receivers: filelog: include: [ `FILE_PATH` ] operators: - type: json_parser start_at: beginning windowseventlog/activedirectoryservice: channel: Directory Service raw: true processors: batch: exporters: chronicle/activedirectory: endpoint: https://malachiteingestion-pa.googleapis.com creds: '{ "type": "service_account", "project_id": "malachite-projectname", "private_key_id": `PRIVATE_KEY_ID`, "private_key": `PRIVATE_KEY`, "client_email":"`SERVICE_ACCOUNT_NAME`@malachite-`PROJECT_ID`.iam.gserviceaccount.com", "client_id": `CLIENT_ID`, "auth_uri": "https://accounts.google.com/o/oauth2/auth", "token_uri": "https://oauth2.googleapis.com/token", "auth_provider_x509_cert_url":"https://www.googleapis.com/oauth2/v1/certs", "client_x509_cert_url": "https://www.googleapis.com/robot/v1/metadata/x509/`SERVICSERVICE_ACCOUNT_NAME`%40malachite-`PROJECT_ID`.iam.gserviceaccount.com", "universe_domain": "googleapis.com" }' log_type: 'WINDOWS_AD' override_log_type: false raw_log_field: body customer_id: `CUSTOMER_ID` service: pipelines: logs/ads: receivers: - filelog - windowseventlog/activedirectoryservice processors: [batch] exporters: [chronicle/activedirectory]Replace the following :
FILE_PATHwith the path of the file where the output of the PowerShell script mentioned in the Configure Microsoft Windows AD servers has been stored.PRIVATE_KEY_ID,PRIVATE_KEYSERVICSERVICE_ACCOUNT_NAME,PROJECT_ID,CLIENT_IDandCUSTOMER_IDwith the respective values from the service account JSON file which you can download from Google Cloud. For more information about service account keys, see Create and delete service account keys.
To start the Bindplane (formally known as observIQ) agent service, select Services > Extended > the observIQ Service > Start.
Configure NXLog Agent
The following diagram shows an architecture in which NXLog Agents are installed to collect and send Microsoft Windows events to Google Security Operations. Compare this information with your environment to be sure these components are installed. Your deployment might be different from this architecture and might be more complex.
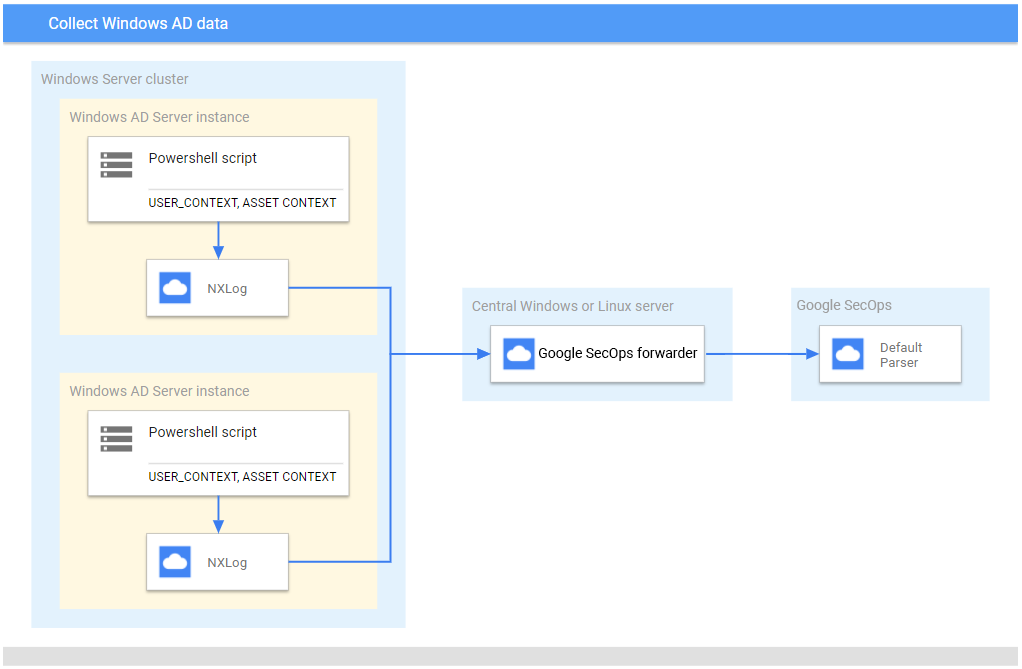
If you use the NXLog agent instead of the Bindplane agent, verify the following:
- A PowerShell script is created and configured on each Microsoft Windows Server that runs Active Directory to
collect
USER_CONTEXTandASSET_CONTEXTdata. For more information, see the Configure Microsoft Windows AD servers. - NXLog is installed on each Microsoft Windows AD server to send data to the central Microsoft Windows Server or Linux server.
- Google Security Operations forwarder is installed on the central Microsoft Windows Server or Linux server to forward log data to Google Security Operations.
Configure NXLog
- Install the NXLog agent on each collector that runs on the Windows Active Directory server. This application forwards logs to the central Microsoft Windows or Linux server. For more information, see the NXLog documentation.
Create a configuration file for each NXLog instance. Use the NXLog
im_filemodule to read from the file and parse the lines into fields. Useom_tcpto forward data to the central Microsoft Windows or Linux server.The following is an example of the NXLog configuration. Replace
<hostname>and<port>values with information about the destination central Microsoft Windows or Linux Server. In the<Input in_adcontext>section andFileproperty, add the path of the output log file written by the PowerShell script. Always setDirCheckIntervalandPollInterval. If these are not defined, NXLog polls for files every 1 second.define ROOT C:\Program Files\nxlog define ADCONTEXT_OUTPUT_DESTINATION_ADDRESS <hostname> define ADCONTEXT_OUTPUT_DESTINATION_PORT <port> Moduledir %ROOT%\modules CacheDir %ROOT%\data Pidfile %ROOT%\data\nxlog.pid SpoolDir %ROOT%\data LogFile %ROOT%\data\nxlog.log <Input in_adcontext> Module im_file File "<Path_of_the_output_file>" DirCheckInterval 3600 PollInterval 3600 </Input> <Output out_chronicle_adcontext> Module om_tcp Host %ADCONTEXT_OUTPUT_DESTINATION_ADDRESS% Port %ADCONTEXT_OUTPUT_DESTINATION_PORT% </Output> <Route ad_context_to_chronicle> Path in_adcontext => out_chronicle_adcontext </Route>Start the NXLog service in each system.
Configure the forwarder on a central server
For information about installing and configuring the forwarder on Linux, see Installing and configuring the forwarder on Linux. For information about installing and configuring the forwarder on Microsoft Windows, see Installing and configuring the forwarder on Microsoft Windows.
- Configure the system with the UTC time zone.
- Install the Google Security Operations forwarder on the central Microsoft Windows or Linux server.
Configure the Google Security Operations forwarder to send logs to Google Security Operations. The following is an example forwarder configuration:
- syslog: common: enabled: true data_type: WINDOWS_AD batch_n_seconds: 10 batch_n_bytes: 1048576 tcp_address: 0.0.0.0:10518 connection_timeout_sec: 60
Supported Windows AD log formats
The Windows AD parser supports logs in JSON format.
Supported Windows AD sample logs
JSON:
{ "GivenName": "user1", "Surname": "itadmin", "UserPrincipalName": "user1.itadmin@testdhcp2.local", "Enabled": true, "SamAccountName": "user1.itadmin", "SID": { "BinaryLength": 28, "AccountDomainSid": { "BinaryLength": 24, "AccountDomainSid": "S-1-2-3", "Value": "S-1-2-3" }, "Value": "S-1-2-3-4000" }, "DistinguishedName": "CN=test,CN=Users,DC=testdhcp2,DC=local", "Name": "test", "ObjectClass": "user", "ObjectGuid": "4bde3f8d-8e9e-4ded-9d71-126ba9cd1300", "PropertyNames": [ "AccountExpirationDate", "accountExpires", "AccountLockoutTime", "AccountNotDelegated", "AllowReversiblePasswordEncryption", "AuthenticationPolicy", "AuthenticationPolicySilo", "BadLogonCount", "badPasswordTime", "badPwdCount", "c", "CannotChangePassword", "CanonicalName", "Certificates", "City", "CN", "co", "codePage", "Company", "CompoundIdentitySupported", "Country", "countryCode", "Created", "createTimeStamp", "Deleted", "Department", "Description", "DisplayName", "DistinguishedName", "Division", "DoesNotRequirePreAuth", "dSCorePropagationData", "EmailAddress", "EmployeeID", "EmployeeNumber", "Enabled", "facsimileTelephoneNumber", "Fax", "GivenName", "HomeDirectory", "HomedirRequired", "HomeDrive", "HomePage", "HomePhone", "Initials", "instanceType", "ipPhone", "isDeleted", "KerberosEncryptionType", "l", "LastBadPasswordAttempt", "LastKnownParent", "lastLogoff", "lastLogon", "LastLogonDate", "lastLogonTimestamp", "LockedOut", "lockoutTime", "logonCount", "logonHours", "LogonWorkstations", "mail", "Manager", "MemberOf", "MNSLogonAccount", "mobile", "MobilePhone", "Modified", "modifyTimeStamp", "msDS-SupportedEncryptionTypes", "msDS-User-Account-Control-Computed", "Name", "nTSecurityDescriptor", "ObjectCategory", "ObjectClass", "ObjectGUID", "objectSid", "Office", "OfficePhone", "Organization", "OtherName", "pager", "PasswordExpired", "PasswordLastSet", "PasswordNeverExpires", "PasswordNotRequired", "physicalDeliveryOfficeName", "POBox", "PostalCode", "postOfficeBox", "PrimaryGroup", "primaryGroupID", "PrincipalsAllowedToDelegateToAccount", "ProfilePath", "ProtectedFromAccidentalDeletion", "pwdLastSet", "SamAccountName", "sAMAccountType", "ScriptPath", "sDRightsEffective", "ServicePrincipalNames", "SID", "SIDHistory", "SmartcardLogonRequired", "sn", "st", "State", "StreetAddress", "Surname", "telephoneNumber", "Title", "TrustedForDelegation", "TrustedToAuthForDelegation", "UseDESKeyOnly", "userAccountControl", "userCertificate", "userParameters", "UserPrincipalName", "uSNChanged", "uSNCreated", "whenChanged", "whenCreated", "wWWHomePage" ], "AddedProperties": [], "RemovedProperties": [], "ModifiedProperties": [], "PropertyCount": 123, "AccountExpirationDate": null, "accountExpires": 0, "AccountLockoutTime": "\\/Date(1631175863106)\\/", "AccountNotDelegated": true, "AllowReversiblePasswordEncryption": false, "AuthenticationPolicy": [], "AuthenticationPolicySilo": [], "BadLogonCount": 3, "badPasswordTime": 132756494631068585, "badPwdCount": 3, "c": "IN", "CannotChangePassword": false, "CanonicalName": "testdhcp2.local/Users/test", "Certificates": [], "City": "Ahmedabad", "CN": "test", "co": "India", "codePage": 0, "Company": "user", "CompoundIdentitySupported": [ false ], "Country": "IN", "countryCode": 356, "Created": "\\/Date(1628229355000)\\/", "createTimeStamp": "\\/Date(1628229355000)\\/", "Deleted": null, "Department": "it", "Description": "itadmin", "DisplayName": "user1", "Division": "test", "DoesNotRequirePreAuth": false, "dSCorePropagationData": [ "\\/Date(1631191510000)\\/", "\\/Date(-11644473600000)\\/" ], "EmailAddress": "user@dummy.local", "EmployeeID": null, "EmployeeNumber": null, "facsimileTelephoneNumber": "12345678", "Fax": "12345678", "HomeDirectory": "\\\\\\\\DHCP-AD01\\\\ADContext", "HomedirRequired": false, "HomeDrive": "G:", "HomePage": "www.test.com", "HomePhone": "123456789", "Initials": "user1", "instanceType": 4, "ipPhone": "1121", "isDeleted": null, "KerberosEncryptionType": [ 0 ], "l": "ahmedabad", "LastBadPasswordAttempt": "\\/Date(1631175863106)\\/", "LastKnownParent": null, "lastLogoff": 0, "lastLogon": 132756492460689244, "LastLogonDate": "\\/Date(1631175025098)\\/", "lastLogonTimestamp": 132756486250985369, "LockedOut": false, "lockoutTime": 132756494631068585, "logonCount": 2, "logonHours": [ 0, 0, 248, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 7, 0, 0, 0, 0, 0, 0 ], "LogonWorkstations": null, "mail": "user@dummy.local", "Manager": "CN=Administrator,CN=Users,DC=testdhcp2,DC=local", "MemberOf": [ "CN=Netwrix Auditor Client Users,CN=Users,DC=dnstest2,DC=local", "CN=Netwrix Auditor Administrators,CN=Users,DC=dnstest2,DC=local", "CN=Group Policy Creator Owners,CN=Users,DC=dnstest2,DC=local", "CN=Domain Admins,CN=Users,DC=dnstest2,DC=local", "CN=Enterprise Admins,CN=Users,DC=dnstest2,DC=local", "CN=Schema Admins,CN=Users,DC=dnstest2,DC=local", "CN=Remote Desktop Users,CN=Builtin,DC=dnstest2,DC=local", "CN=Administrators,CN=Builtin,DC=dnstest2,DC=local" ], "MNSLogonAccount": false, "mobile": "923456789", "MobilePhone": "823456789", "Modified": "\\/Date(1631277960000)\\/", "modifyTimeStamp": "\\/Date(1631277960000)\\/", "msDS-SupportedEncryptionTypes": 0, "msDS-User-Account-Control-Computed": 0, "nTSecurityDescriptor": { "AccessRightType": { "Module": "System.DirectoryServices.dll", "Assembly": "System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a", "TypeHandle": "System.RuntimeTypeHandle", "DeclaringMethod": null, "BaseType": "System.Enum", "UnderlyingSystemType": "System.DirectoryServices.ActiveDirectoryRights", "FullName": "System.DirectoryServices.ActiveDirectoryRights", "AssemblyQualifiedName": "System.DirectoryServices.ActiveDirectoryRights, System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a", "Namespace": "System.DirectoryServices", "GUID": "f65acb9b-4c77-33ff-8523-43e9cc2c5798", "IsEnum": true, "GenericParameterAttributes": null, "IsSecurityCritical": false, "IsSecuritySafeCritical": false, "IsSecurityTransparent": true, "IsGenericTypeDefinition": false, "IsGenericParameter": false, "GenericParameterPosition": null, "IsGenericType": false, "IsConstructedGenericType": false, "ContainsGenericParameters": false, "StructLayoutAttribute": "System.Runtime.InteropServices.StructLayoutAttribute", "Name": "ActiveDirectoryRights", "MemberType": 32, "DeclaringType": null, "ReflectedType": null, "MetadataToken": 33554438, "GenericTypeParameters": "", "DeclaredConstructors": "", "DeclaredEvents": "", "DeclaredFields": "Int32 value__ System.DirectoryServices.ActiveDirectoryRights Delete System.DirectoryServices.ActiveDirectoryRights ReadControl System.DirectoryServices.ActiveDirectoryRights WriteDacl System.DirectoryServices.ActiveDirectoryRights WriteOwner System.DirectoryServices.ActiveDirectoryRights Synchronize System.DirectoryServices.ActiveDirectoryRights AccessSystemSecurity System.DirectoryServices.ActiveDirectoryRights GenericRead System.DirectoryServices.ActiveDirectoryRights GenericWrite System.DirectoryServices.ActiveDirectoryRights GenericExecute System.DirectoryServices.ActiveDirectoryRights GenericAll System.DirectoryServices.ActiveDirectoryRights CreateChild System.DirectoryServices.ActiveDirectoryRights DeleteChild System.DirectoryServices.ActiveDirectoryRights ListChildren System.DirectoryServices.ActiveDirectoryRights Self System.DirectoryServices.ActiveDirectoryRights ReadProperty System.DirectoryServices.ActiveDirectoryRights WriteProperty System.DirectoryServices.ActiveDirectoryRights DeleteTree System.DirectoryServices.ActiveDirectoryRights ListObject System.DirectoryServices.ActiveDirectoryRights ExtendedRight", "DeclaredMembers": "Int32 value__ System.DirectoryServices.ActiveDirectoryRights Delete System.DirectoryServices.ActiveDirectoryRights ReadControl System.DirectoryServices.ActiveDirectoryRights WriteDacl System.DirectoryServices.ActiveDirectoryRights WriteOwner System.DirectoryServices.ActiveDirectoryRights Synchronize System.DirectoryServices.ActiveDirectoryRights AccessSystemSecurity System.DirectoryServices.ActiveDirectoryRights GenericRead System.DirectoryServices.ActiveDirectoryRights GenericWrite System.DirectoryServices.ActiveDirectoryRights GenericExecute System.DirectoryServices.ActiveDirectoryRights GenericAll System.DirectoryServices.ActiveDirectoryRights CreateChild System.DirectoryServices.ActiveDirectoryRights DeleteChild System.DirectoryServices.ActiveDirectoryRights ListChildren System.DirectoryServices.ActiveDirectoryRights Self System.DirectoryServices.ActiveDirectoryRights ReadProperty System.DirectoryServices.ActiveDirectoryRights WriteProperty System.DirectoryServices.ActiveDirectoryRights DeleteTree System.DirectoryServices.ActiveDirectoryRights ListObject System.DirectoryServices.ActiveDirectoryRights ExtendedRight", "DeclaredMethods": "", "DeclaredNestedTypes": "", "DeclaredProperties": "", "ImplementedInterfaces": "System.IComparable System.IFormattable System.IConvertible", "TypeInitializer": null, "IsNested": false, "Attributes": 257, "IsVisible": true, "IsNotPublic": false, "IsPublic": true, "IsNestedPublic": false, "IsNestedPrivate": false, "IsNestedFamily": false, "IsNestedAssembly": false, "IsNestedFamANDAssem": false, "IsNestedFamORAssem": false, "IsAutoLayout": true, "IsLayoutSequential": false, "IsExplicitLayout": false, "IsClass": false, "IsInterface": false, "IsValueType": true, "IsAbstract": false, "IsSealed": true, "IsSpecialName": false, "IsImport": false, "IsSerializable": true, "IsAnsiClass": true, "IsUnicodeClass": false, "IsAutoClass": false, "IsArray": false, "IsByRef": false, "IsPointer": false, "IsPrimitive": false, "IsCOMObject": false, "HasElementType": false, "IsContextful": false, "IsMarshalByRef": false, "GenericTypeArguments": "", "CustomAttributes": "[System.FlagsAttribute()]" }, "AccessRuleType": { "Module": "System.DirectoryServices.dll", "Assembly": "System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a", "TypeHandle": "System.RuntimeTypeHandle", "DeclaringMethod": null, "BaseType": "System.Security.AccessControl.ObjectAccessRule", "UnderlyingSystemType": "System.DirectoryServices.ActiveDirectoryAccessRule", "FullName": "System.DirectoryServices.ActiveDirectoryAccessRule", "AssemblyQualifiedName": "System.DirectoryServices.ActiveDirectoryAccessRule, System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a", "Namespace": "System.DirectoryServices", "GUID": "0db7ea8c-53d9-3d6d-8b09-bb209cf0d0ae", "IsEnum": false, "GenericParameterAttributes": null, "IsSecurityCritical": false, "IsSecuritySafeCritical": false, "IsSecurityTransparent": true, "IsGenericTypeDefinition": false, "IsGenericParameter": false, "GenericParameterPosition": null, "IsGenericType": false, "IsConstructedGenericType": false, "ContainsGenericParameters": false, "StructLayoutAttribute": "System.Runtime.InteropServices.StructLayoutAttribute", "Name": "ActiveDirectoryAccessRule", "MemberType": 32, "DeclaringType": null, "ReflectedType": null, "MetadataToken": 33554445, "GenericTypeParameters": "", "DeclaredConstructors": "Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, Int32, System.Security.AccessControl.AccessControlType, System.Guid, Boolean, System.Security.AccessControl.InheritanceFlags, System.Security.AccessControl.PropagationFlags, System.Guid)", "DeclaredEvents": "", "DeclaredFields": "", "DeclaredMembers": "System.DirectoryServices.ActiveDirectoryRights get_ActiveDirectoryRights() System.DirectoryServices.ActiveDirectorySecurityInheritance get_InheritanceType() Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, Int32, System.Security.AccessControl.AccessControlType, System.Guid, Boolean, System.Security.AccessControl.InheritanceFlags, System.Security.AccessControl.PropagationFlags, System.Guid) System.DirectoryServices.ActiveDirectoryRights ActiveDirectoryRights System.DirectoryServices.ActiveDirectorySecurityInheritance InheritanceType", "DeclaredMethods": "System.DirectoryServices.ActiveDirectoryRights get_ActiveDirectoryRights() System.DirectoryServices.ActiveDirectorySecurityInheritance get_InheritanceType()", "DeclaredNestedTypes": "", "DeclaredProperties": "System.DirectoryServices.ActiveDirectoryRights ActiveDirectoryRights System.DirectoryServices.ActiveDirectorySecurityInheritance InheritanceType", "ImplementedInterfaces": "", "TypeInitializer": null, "IsNested": false, "Attributes": 1048577, "IsVisible": true, "IsNotPublic": false, "IsPublic": true, "IsNestedPublic": false, "IsNestedPrivate": false, "IsNestedFamily": false, "IsNestedAssembly": false, "IsNestedFamANDAssem": false, "IsNestedFamORAssem": false, "IsAutoLayout": true, "IsLayoutSequential": false, "IsExplicitLayout": false, "IsClass": true, "IsInterface": false, "IsValueType": false, "IsAbstract": false, "IsSealed": false, "IsSpecialName": false, "IsImport": false, "IsSerializable": false, "IsAnsiClass": true, "IsUnicodeClass": false, "IsAutoClass": false, "IsArray": false, "IsByRef": false, "IsPointer": false, "IsPrimitive": false, "IsCOMObject": false, "HasElementType": false, "IsContextful": false, "IsMarshalByRef": false, "GenericTypeArguments": "", "CustomAttributes": "" }, "AuditRuleType": { "Module": "System.DirectoryServices.dll", "Assembly": "System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a", "TypeHandle": "System.RuntimeTypeHandle", "DeclaringMethod": null, "BaseType": "System.Security.AccessControl.ObjectAuditRule", "UnderlyingSystemType": "System.DirectoryServices.ActiveDirectoryAuditRule", "FullName": "System.DirectoryServices.ActiveDirectoryAuditRule", "AssemblyQualifiedName": "System.DirectoryServices.ActiveDirectoryAuditRule, System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a", "Namespace": "System.DirectoryServices", "GUID": "4ad0312a-2ed0-3526-97ec-f9c6f310c5e0", "IsEnum": false, "GenericParameterAttributes": null, "IsSecurityCritical": false, "IsSecuritySafeCritical": false, "IsSecurityTransparent": true, "IsGenericTypeDefinition": false, "IsGenericParameter": false, "GenericParameterPosition": null, "IsGenericType": false, "IsConstructedGenericType": false, "ContainsGenericParameters": false, "StructLayoutAttribute": "System.Runtime.InteropServices.StructLayoutAttribute", "Name": "ActiveDirectoryAuditRule", "MemberType": 32, "DeclaringType": null, "ReflectedType": null, "MetadataToken": 33554453, "GenericTypeParameters": "", "DeclaredConstructors": "Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, Int32, System.Security.AccessControl.AuditFlags, System.Guid, Boolean, System.Security.AccessControl.InheritanceFlags, System.Security.AccessControl.PropagationFlags, System.Guid)", "DeclaredEvents": "", "DeclaredFields": "", "DeclaredMembers": "System.DirectoryServices.ActiveDirectoryRights get_ActiveDirectoryRights() System.DirectoryServices.ActiveDirectorySecurityInheritance get_InheritanceType() Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, Int32, System.Security.AccessControl.AuditFlags, System.Guid, Boolean, System.Security.AccessControl.InheritanceFlags, System.Security.AccessControl.PropagationFlags, System.Guid) System.DirectoryServices.ActiveDirectoryRights ActiveDirectoryRights System.DirectoryServices.ActiveDirectorySecurityInheritance InheritanceType", "DeclaredMethods": "System.DirectoryServices.ActiveDirectoryRights get_ActiveDirectoryRights() System.DirectoryServices.ActiveDirectorySecurityInheritance get_InheritanceType()", "DeclaredNestedTypes": "", "DeclaredProperties": "System.DirectoryServices.ActiveDirectoryRights ActiveDirectoryRights System.DirectoryServices.ActiveDirectorySecurityInheritance InheritanceType", "ImplementedInterfaces": "", "TypeInitializer": null, "IsNested": false, "Attributes": 1048577, "IsVisible": true, "IsNotPublic": false, "IsPublic": true, "IsNestedPublic": false, "IsNestedPrivate": false, "IsNestedFamily": false, "IsNestedAssembly": false, "IsNestedFamANDAssem": false, "IsNestedFamORAssem": false, "IsAutoLayout": true, "IsLayoutSequential": false, "IsExplicitLayout": false, "IsClass": true, "IsInterface": false, "IsValueType": false, "IsAbstract": false, "IsSealed": false, "IsSpecialName": false, "IsImport": false, "IsSerializable": false, "IsAnsiClass": true, "IsUnicodeClass": false, "IsAutoClass": false, "IsArray": false, "IsByRef": false, "IsPointer": false, "IsPrimitive": false, "IsCOMObject": false, "HasElementType": false, "IsContextful": false, "IsMarshalByRef": false, "GenericTypeArguments": "", "CustomAttributes": "" }, "AreAccessRulesProtected": false, "AreAuditRulesProtected": false, "AreAccessRulesCanonical": true, "AreAuditRulesCanonical": true }, "ObjectCategory": "CN=Person,CN=Schema,CN=Configuration,DC=testdhcp2,DC=local", "ObjectGUID": "4bde3f8d-8e9e-4ded-9d71-126ba9cd1300", "objectSid": { "BinaryLength": 28, "AccountDomainSid": { "BinaryLength": 24, "AccountDomainSid": "S-1-2-3", "Value": "S-1-2-3" }, "Value": "S-1-2-3-4000m" }, "Office": "db office", "OfficePhone": "91-123456789", "Organization": null, "OtherName": null, "pager": "234567890", "PasswordExpired": false, "PasswordLastSet": "\\/Date(1631174951326)\\/", "PasswordNeverExpires": false, "PasswordNotRequired": false, "physicalDeliveryOfficeName": "db office", "POBox": "dummy", "PostalCode": "380015", "postOfficeBox": [ "dummy" ], "PrimaryGroup": "CN=Domain Users,CN=Users,DC=testdhcp2,DC=local", "primaryGroupID": 513, "PrincipalsAllowedToDelegateToAccount": [], "ProfilePath": null, "ProtectedFromAccidentalDeletion": false, "pwdLastSet": 132756485513268133, "sAMAccountType": 805306368, "ScriptPath": null, "sDRightsEffective": 15, "ServicePrincipalNames": [], "SIDHistory": [], "SmartcardLogonRequired": false, "sn": "itadmin", "st": "Gujarat", "State": "Gujarat", "StreetAddress": "1,user street ,dummy,dummy", "telephoneNumber": "91-123456789", "Title": "it admin", "TrustedForDelegation": false, "TrustedToAuthForDelegation": false, "UseDESKeyOnly": false, "userAccountControl": 1049088, "userCertificate": [], "userParameters": null, "uSNChanged": 57594, "uSNCreated": 32800, "whenChanged": "\\/Date(1631277960000)\\/", "whenCreated": "\\/Date(1628229355000)\\/", "wWWHomePage": "www.test.com" }
Field mapping reference: device log fields to UDM fields
This section describes how the parser maps original log fields to Unified Data Model fields.
Field mapping reference: WINDOWS_AD
The following table lists the log fields of the WINDOWS_AD log type and their corresponding UDM fields.
| Log field | UDM mapping | Logic |
|---|---|---|
|
metadata.entity_type |
If the ObjectClass log field value is equal to user or is empty, then the metadata.entity_type UDM field is set to USER. Else, if the ObjectClass log field value is equal to computer, then the metadata.entity_type UDM field is set to ASSET. Else, if the ObjectClass log field value is equal to group, then the metadata.entity_type UDM field is set to GROUP. |
ObjectGuid |
entity.user.product_object_id |
If the ObjectClass log field value is equal to user or is empty, then if the ObjectGuid log field value is not empty, then the ObjectGuid log field is mapped to the entity.user.product_object_id UDM field. Else, if the ObjectClass log field value is equal to computer, then if the ObjectGuid log field value is not empty, then the ObjectGuid log field is mapped to the entity.asset.product_object_id UDM field. |
whenCreated |
metadata.creation_timestamp |
If the ObjectClass log field value is equal to user or is empty, then if the whenCreated log field value is not empty, then when_created is extracted from the whenCreated log field using a Grok pattern, and mapped to the entity.asset.attribute.creation_time UDM field. Else, if the ObjectClass log field value is equal to computer, then if the whenCreated log field value is not empty, then when_created is extracted from the whenCreated log field using a Grok pattern, and mapped to the metadata.creation_timestamp UDM field. Else, timestamp tz_left tz_right is extracted from the whenCreated log field using a Grok pattern, and mapped to the entity.asset.attribute.creation_time UDM field. |
DisplayName |
entity.user.user_display_name |
If the ObjectClass log field value is equal to user or is empty, then if the DisplayName log field value is not empty, then the DisplayName log field is mapped to the entity.user.user_display_name UDM field. |
GivenName |
entity.user.first_name |
If the ObjectClass log field value is equal to user or is empty, then if the GivenName log field value is not empty, then the GivenName log field is mapped to the entity.user.first_name UDM field. |
SamAccountName |
entity.user.userid |
If the ObjectClass log field value is equal to user or is empty, then if the SamAccountName log field value is not empty, then the SamAccountName log field is mapped to the entity.user.userid UDM field. If the ObjectClass log field value is equal to computer, then the SamAccountName log field is mapped to the entity.asset.asset_id UDM field. |
EmployeeID |
entity.user.employee_id |
If the EmployeeID log field value is not empty, then the EmployeeID log field is mapped to the entity.user.employee_id UDM field.Else the employeeID.0 log field is mapped to the entity.user.employee_id UDM field. |
Title |
entity.user.title |
If the Title log field value is not empty, then the Title log field is mapped to the entity.user.title UDM field. |
Surname |
entity.user.last_name |
If the ObjectClass log field value is equal to user or is empty, then if the Surname log field value is not empty, then if the sn log field is mapped to the entity.user.last_name UDM field. Else if Surname log field value is not empty, then the Surname log field is mapped to the entity.user.last_name UDM field. |
Company |
entity.user.company_name |
If the ObjectClass log field value is equal to user or is empty, then if the Company log field value is not empty, then the Company log field is mapped to the entity.user.company_name UDM field. |
City |
entity.user.personal_address.city |
If the ObjectClass log field value is equal to user or is empty, then if the City log field value is not empty, then the City log field is mapped to the entity.user.personal_address.city UDM field. |
Department |
entity.user.department |
If the ObjectClass log field value is equal to user or is empty, then if the Department log field value is not empty, then the Department log field is mapped to the entity.user.department UDM field. |
|
entity.user.email_addresses |
If the ObjectClass log field value is equal to user or is empty, then if the EmailAddress log field value is not empty, then the EmailAddress log field is mapped to the entity.user.email_addresses UDM field. Else, if the mail log field value is not empty, then the mail log field is mapped to the entity.user.email_addresses UDM field. |
HomePhone |
entity.user.phone_numbers |
If the ObjectClass log field value is equal to user or is empty, then if the HomePhone log field value is not empty, then the HomePhone log field is mapped to the entity.user.phone_numbers UDM field. Else if the telephoneNumber log field value is not empty, then the telephoneNumber log field is mapped to the entity.user.phone_numbers UDM field.
If the ObjectClass log field value is equal to user or is empty, then if the MobilePhone log field value is not empty, then the MobilePhone log field is mapped to the entity.user.phone_numbers UDM field.
If the ObjectClass log field value is equal to user or is empty, then if the otherMobile log field value is not empty, then the otherMobile log field is mapped to the entity.user.phone_numbers UDM field. |
StreetAddress |
entity.user.personal_address.name |
If the ObjectClass log field value is equal to user or is empty, then if the StreetAddress log field value is not empty, then the StreetAddress log field is mapped to the entity.user.personal_address.name UDM field. |
State |
entity.user.personal_address.state |
If the ObjectClass log field value is equal to user or is empty, then if the State log field value is not empty, then the State log field is mapped to the entity.user.personal_address.state UDM field. |
Country |
entity.user.personal_address.country_or_region |
If the ObjectClass log field value is equal to user or is empty, then if the Country log field value is not empty, then the Country log field is mapped to the entity.user.personal_address.country_or_region UDM field. |
Office |
entity.user.office_address.name |
If the ObjectClass log field value is equal to user or is empty, then if the Office log field value is not empty, then the Office log field is mapped to the entity.user.office_address.name UDM field. |
HomeDirectory |
entity.file.full_path |
If the ObjectClass log field value is equal to user or is empty, then if the HomeDirectory log field value is not empty, then the HomeDirectory log field is mapped to the entity.file.full_path UDM field. |
|
entity.user.managers.user_display_name |
If the ObjectClass log field value is equal to user or is empty, then if the Manager log field value is not empty, then manager_name is extracted from the Manager log field using a Grok pattern, and mapped to the entity.user.managers.user_display_name UDM field. |
|
entity.user.windows_sid |
If the SID.Value log field value is not empty, then the SID.Value field is mapped to the entity.user.windows_sid UDM field.Else, if the objectSid log field value is not empty, then the objectSid field is mapped to the entity.user.windows_sid UDM field.If the ObjectClass log field value is equal to user or is empty, then if the Manager log field value is not empty, then if Manager matches the regular expression pattern (S-\d-(\d+-){1,14}\d+), then the Manager log field is mapped to the entity.user.managers.windows_sid UDM field. Else, the Manager log field is mapped to the entity.user.managers.userid UDM field. |
|
relations.relationship |
If the ObjectClass log field value is equal to user or is empty, then if the MemberOf log field value is not empty, then for index in MemberOf, the relations.relationship UDM field is set to MEMBER. Else, if the ObjectClass log field value is equal to computer, then if the ManagedBy log field value is not empty, then the relations.relationship UDM field is set to ADMINISTERS.If the PrimaryGroup log field value is not empty, then group_name is extracted from the PrimaryGroup log field using a Grok pattern, if the group_name extracted field value is not empty, then the relations.relationship UDM field is set to MEMBER. |
|
relations.entity.group.group_display_name |
If the ObjectClass log field value is equal to user or is empty, then if the MemberOf log field value is not empty, then for index in MemberOf, group_name is extracted from the index using a Grok pattern and mapped to the relations.entity.group.group_display_name UDM field. If the PrimaryGroup log field value is not empty, then group_name is extracted from the PrimaryGroup log field using a Grok pattern and mapped to the relations.entity.group.group_display_name UDM field. |
|
relations.entity_type |
If the ObjectClass log field value is equal to user or is empty, then if the MemberOf log field value is not empty, then for index in MemberOf, the relations.entity_type UDM field is set to GROUP. Else, if the ObjectClass log field value is equal to computer, then if the ManagedBy log field value is not empty, then the relations.entity_type UDM field is set to ASSET.If the PrimaryGroup log field value is not empty, then group_name is extracted from the PrimaryGroup log field using a Grok pattern, if the group_name extracted field value is not empty, then the relations.entity_type UDM field is set to GROUP. |
|
relations.direction |
If the ObjectClass log field value is equal to user or is empty, then if the MemberOf log field value is not empty, then for index in MemberOf, the relations.direction UDM field is set to UNIDIRECTIONAL. Else, if the ObjectClass log field value is equal to computer, then if the ManagedBy log field value is not empty, then the relations.direction UDM field is set to UNIDIRECTIONAL.If the PrimaryGroup log field value is not empty, then group_name is extracted from the PrimaryGroup log field using a Grok pattern, if the group_name extracted field value is not empty, then the relations.direction UDM field is set to UNIDIRECTIONAL. |
|
relations.entity.user.user_display_name |
If the ObjectClass log field value is equal to computer, then if the ManagedBy log field value is not empty, then user_name is extracted from the ManagedBy log field using a Grok pattern and mapped to the relations.entity.user.user_display_name UDM field. |
proxyAddresses |
entity.user.group_identifiers |
If the ObjectClass log field value is equal to user or is empty, then for index in proxyAddresses the index is mapped to entity.user.group_identifiers UDM field. |
|
entity.user.attribute.labels[Bad Password Count] |
If the ObjectClass log field value is equal to user or is empty, then if the badPwdCount log field value is not empty, then the entity.user.attribute.labels.key UDM field is set to Bad Password Count and the badPwdCount log field is mapped to the entity.user.attribute.labels.value UDM field. |
LastBadPasswordAttempt |
entity.user.last_bad_password_attempt_time |
If the ObjectClass log field value is equal to user or is empty, then if the LastBadPasswordAttempt log field value is not empty, then last_bad_password_attempt is extracted from the LastBadPasswordAttempt log field using a Grok pattern and mapped to the entity.user.last_bad_password_attempt_time UDM field. Else, if the ObjectClass log field value is equal to computer, then last_bad_password_attempt is extracted from the LastBadPasswordAttempt log field using a Grok pattern and mapped to the entity.user.last_bad_password_attempt_time UDM field. |
AccountExpirationDate |
entity.user.account_expiration_time |
If the ObjectClass log field value is equal to user or is empty, then if the AccountExpirationDate log field value is not empty, then account_expiration_date is extracted from the AccountExpirationDate log field using a Grok pattern and mapped to the entity.user.account_expiration_time UDM field. Else, if the ObjectClass log field value is equal to computer, then if the AccountExpirationDate log field value is not empty, then account_expiration_date is extracted from the AccountExpirationDate log field using a Grok pattern and mapped to the entity.user.account_expiration_time UDM field. |
PasswordLastSet |
entity.user.last_password_change_time |
If the ObjectClass log field value is equal to user or is empty, then if the PasswordLastSet log field value is not empty, then password_last_set is extracted from the PasswordLastSet log field using a Grok pattern and mapped to the entity.user.last_password_change_time UDM field. Else, if the ObjectClass log field value is equal to computer, then if the PasswordLastSet log field value is not empty, then password_last_set is extracted from the PasswordLastSet log field using a Grok pattern and mapped to the entity.user.last_password_change_time UDM field. |
PasswordNotRequired |
entity.user.attribute.labels[Password Not Required] |
If the ObjectClass log field value is equal to user or is empty, then if the PasswordNotRequired log field value is not empty, then the PasswordNotRequired log field is mapped to the entity.user.attribute.labels.value UDM field. If the ObjectClass log field value is equal to computer, then if the PasswordNotRequired log field value is not empty, then the PasswordNotRequired log field is mapped to the entity.asset.attribute.labels.value UDM field. |
ServicePrincipalNames |
entity.user.attribute.labels[Service Principal Names] |
If the ObjectClass log field value is equal to user or is empty, then if ServicePrincipalNames log field value is not empty, then for index in ServicePrincipalNames the index is mapped to the entity.user.attribute.labels.value UDM field.Else, if the ObjectClass log field value is equal to computer, then if ServicePrincipalNames log field value is not empty, then for index in ServicePrincipalNames, if index is equal to 0, then the index is mapped to the entity.user.attribute.labels.value UDM field. |
AccountLockoutTime |
entity.user.account_lockout_time |
If the ObjectClass log field value is equal to user or is empty, then if the AccountLockoutTime log field value is not empty, then account_lockout_time is extracted from the AccountLockoutTime log field using a Grok pattern and mapped to the entity.user.account_lockout_time UDM field. Else, if the ObjectClass log field value is equal to computer, then if the AccountLockoutTime log field value is not empty, then account_lockout_time is extracted from the AccountLockoutTime log field using a Grok pattern and mapped to the entity.user.account_lockout_time UDM field. |
whenChanged |
entity.asset.attribute.last_update_time |
If the ObjectClass log field value is equal to computer, then when_changed is extracted from the whenChanged log field using a Grok pattern, if whenChanged is not empty, then when_changed is mapped to the entity.asset.attribute.last_update_time UDM field.Else, timestamp and timezone is extracted from whenChanged log field using a Grok pattern and tz_left and tz_right is extracted from the timezone using a Grok pattern and timestamp tz_left tz_right is mapped to entity.asset.attribute.creation_time UDM field. |
DNSHostName |
entity.asset.hostname |
If the ObjectClass log field value is equal to computer, and the DNSHostName log field value is not empty, then the hostname portion of the DNSHostName field is mapped to the entity.asset.hostname UDM field. To extract the hostname, we split the DNSHostName into two parts: the text that appears before the first dot (.), which represents the hostname, and the text that appears after the first dot (.), which represents the domain. Only the portion before the first dot — the hostname — is mapped to entity.asset.hostname. |
countryCode |
entity.asset.location.country_or_region |
If the ObjectClass log field value is equal to computer, then if the countryCode log field value is not empty, then the countryCode log field is mapped to the entity.asset.location.country_or_region UDM field. |
|
entity.asset.platform_software.platform |
If the ObjectClass log field value is equal to computer, then if the OperatingSystem log field value is not empty, then if the OperatingSystem log field value matches the regular expression pattern (?i)windows, then the entity.asset.platform_software.platform UDM field is set to WINDOWS.Else, if the OperatingSystem log field value matches the regular expression pattern (?i)mac or the OperatingSystem log field value matches the regular expression pattern (?i)osx, then the entity.asset.platform_software.platform UDM field is set to MAC.Else, if the OperatingSystem log field value matches the regular expression pattern (?i)linux, then the entity.asset.platform_software.platform UDM field is set to LINUX. |
OperatingSystemVersion |
entity.asset.platform_software.platform_version |
If the ObjectClass log field value is equal to computer, then if the OperatingSystem log field value is not empty, then if the OperatingSystemVersion log field value is not empty, then OperatingSystem - OperatingSystemVersion is mapped to the entity.asset.platform_software.platform_version UDM field.Else if the OperatingSystemVersion log field value is not empty, then the OperatingSystemVersion log field is mapped to the entity.asset.platform_software.platform_version UDM field. |
OperatingSystemServicePack |
entity.asset.platform_software.platform_patch_level |
If the ObjectClass log field value is equal to computer, then if the OperatingSystemServicePack log field value is not empty, then the OperatingSystemServicePack log field is mapped to the entity.asset.platform_software.platform_patch_level UDM field. |
IPv4Address |
entity.asset.ip |
If the ObjectClass log field value is equal to computer, then if the IPv4Address log field value is not empty, then the IPv4Address log field is mapped to the entity.asset.ip UDM field. |
IPv6Address |
entity.asset.ip |
If the ObjectClass log field value is equal to computer, then if the IPv6Address log field value is not empty, then the IPv6Address log field is mapped to the entity.asset.ip UDM field. |
Location |
entity.asset.location.name |
If the ObjectClass log field value is equal to computer, then if the Location log field value is not empty, then the Location log field is mapped to the entity.asset.location.name UDM field. |
ObjectCategory |
entity.asset.category |
If the ObjectClass log field value is equal to computer, then if the ObjectCategory log field value is not empty, then object_category is extracted from the ObjectCategory log field using a Grok pattern, and mapped to the entity.asset.category UDM field. |
PasswordExpired |
entity.asset.attribute.labels[Password Expired] |
If the ObjectClass log field value is equal to computer, then if the PasswordExpired log field value is not empty, then the PasswordExpired log field is mapped to the entity.asset.attribute.labels.value UDM field.If the ObjectClass log field value is equal to user or is empty, then if the PasswordExpired log field value is not empty, then the PasswordExpired log field is mapped to the entity.user.attribute.labels.value UDM field. |
PasswordNeverExpires |
entity.asset.attribute.labels[Password Never Expires] |
If the ObjectClass log field value is equal to computer, then if the PasswordNeverExpires log field value is not empty, then the PasswordNeverExpires log field is mapped to the entity.asset.attribute.labels.value UDM field.If the ObjectClass log field value is equal to user or is empty, then if the PasswordNeverExpires log field value is not empty, then the PasswordNeverExpires log field is mapped to the entity.user.attribute.labels.value UDM field. |
|
entity.user.attribute.labels[Last Logon] |
If the ObjectClass log field value is equal to user or is empty, then if the lastLogon log field value is not equal to 0, then the entity.user.attribute.labels.key UDM field is set to Last Logon and the lastLogon log field is mapped to the entity.user.attribute.labels.value UDM field. If the ObjectClass log field value is equal to computer, then if the lastLogon log field value is not equal to 0, then the entity.asset.attribute.labels.key UDM field is set to Last Logon and the lastLogon log field is mapped to the entity.asset.attribute.labels.value UDM field. |
lastLogoff |
entity.asset.attribute.labels[Last Logoff] |
If the ObjectClass log field value is equal to computer, then if the lastLogoff log field value does not contain one of the following values, then the lastLogoff log field is mapped to the entity.asset.attribute.labels.value UDM field.
|
LastLogonDate |
entity.user.last_login_time |
If the ObjectClass log field value is equal to user or is empty, then if the LastLogonDate log field value is not empty, then last_logon_date is extracted from the LastLogonDate log field using a Grok pattern, and mapped to the entity.user.last_login_time UDM field.Else if the ObjectClass log field value is equal to computer,then if the LastLogonDate log field value is not empty, then last_logon_date is extracted from the LastLogonDate log field using a Grok pattern, and mapped to the entity.user.last_login_time UDM field. |
HomePage |
entity.url |
If the HomePage log field value is not empty, then the HomePage log field is mapped to the entity.url UDM field. |
|
entity.administrative_domain |
If the CanonicalName log field value is not empty, then domain_name is extracted from the CanonicalName log field using a Grok pattern, and mapped to the entity.administrative_domain UDM field. |
|
metadata.vendor_name |
The metadata.vendor_name UDM field is set to Microsoft. |
|
metadata.product_name |
The metadata.product_name UDM field is set to Windows Active Directory. |
Description |
metadata.description |
The Description log field is mapped to the metadata.description UDM field. |
AccountNameHistory |
entity.group.attribute.labels[account_name_history] |
If the ObjectClass log field value is equal to group, then if the AccountNameHistory log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to account_name_history and the AccountNameHistory log field is mapped to the entity.group.attribute.labels.value UDM field. |
AccountNameHistory |
entity.group.attribute.labels[account_name_history] |
If the ObjectClass log field value is equal to group, then if the AccountNameHistory log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to account_name_history and the AccountNameHistory log field is mapped to the entity.group.attribute.labels.value UDM field. |
AdminCount |
entity.group.attribute.labels[admin_count] |
If the ObjectClass log field value is equal to group, then if the AdminCount log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to admin_count and the AdminCount log field is mapped to the entity.group.attribute.labels.value UDM field. |
AdminDescription |
entity.group.attribute.labels[admin_description] |
If the ObjectClass log field value is equal to group, then if the AdminDescription log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to admin_description and the AdminDescription log field is mapped to the entity.group.attribute.labels.value UDM field. |
AllowedAttributes |
entity.group.attribute.labels[allowed_attributes] |
If the ObjectClass log field value is equal to group, then if the AllowedAttributes log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to allowed_attributes and the AllowedAttributes log field is mapped to the entity.group.attribute.labels.value UDM field. |
AllowedAttributesEffective |
entity.group.attribute.labels[allowed_attributes_effective] |
If the ObjectClass log field value is equal to group, then if the AllowedAttributesEffective log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to allowed_attributes_effective and the AllowedAttributesEffective log field is mapped to the entity.group.attribute.labels.value UDM field. |
AllowedChildClasses |
entity.group.attribute.labels[allowed_child_classes] |
If the ObjectClass log field value is equal to group, then if the AllowedChildClasses log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to allowed_child_classes and the AllowedChildClasses log field is mapped to the entity.group.attribute.labels.value UDM field. |
AllowedChildClassesEffective |
entity.group.attribute.labels[allowed_child_classes_effective] |
If the ObjectClass log field value is equal to group, then if the AllowedChildClassesEffective log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to allowed_child_classes_effective and the AllowedChildClassesEffective log field is mapped to the entity.group.attribute.labels.value UDM field. |
AltSecurityIdentities |
entity.group.attribute.labels[alt_security_identities] |
If the ObjectClass log field value is equal to group, then if the AltSecurityIdentities log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to alt_security_identities and the AltSecurityIdentities log field is mapped to the entity.group.attribute.labels.value UDM field. |
BridgeheadServerListBL |
entity.group.attribute.labels[bridgehead_server_list_bl] |
If the ObjectClass log field value is equal to group, then if the BridgeheadServerListBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to bridgehead_server_list_bl and the BridgeheadServerListBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
CommonName |
entity.group.attribute.labels[common_name] |
If the ObjectClass log field value is equal to group, then if the CommonName log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to common_name and the CommonName log field is mapped to the entity.group.attribute.labels.value UDM field. |
ControlAccessRights |
entity.group.attribute.labels[control_access_rights] |
If the ObjectClass log field value is equal to group, then if the ControlAccessRights log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to control_access_rights and the ControlAccessRights log field is mapped to the entity.group.attribute.labels.value UDM field. |
DisplayNamePrintable |
entity.group.attribute.labels[display_name_printable] |
If the ObjectClass log field value is equal to group, then if the DisplayNamePrintable log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to display_name_printable and the DisplayNamePrintable log field is mapped to the entity.group.attribute.labels.value UDM field. |
DSASignature |
entity.group.attribute.labels[dsa_signature] |
If the ObjectClass log field value is equal to group, then if the DSASignature log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to dsa_signature and the DSASignature log field is mapped to the entity.group.attribute.labels.value UDM field. |
DSCorePropagationData |
entity.group.attribute.labels[ds_core_propagation_data] |
If the ObjectClass log field value is equal to group, then if the DSCorePropagationData log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ds_core_propagation_data and the DSCorePropagationData log field is mapped to the entity.group.attribute.labels.value UDM field. |
ExtensionName |
entity.group.attribute.labels[extension_name] |
If the ObjectClass log field value is equal to group, then if the ExtensionName log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to extension_name and the ExtensionName log field is mapped to the entity.group.attribute.labels.value UDM field. |
Flags |
entity.group.attribute.labels[flags] |
If the ObjectClass log field value is equal to group, then if the Flags log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to flags and the Flags log field is mapped to the entity.group.attribute.labels.value UDM field. |
FromEntry |
entity.group.attribute.labels[from_entry] |
If the ObjectClass log field value is equal to group, then if the FromEntry log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to from_entry and the FromEntry log field is mapped to the entity.group.attribute.labels.value UDM field. |
FrsComputerReferenceBL |
entity.group.attribute.labels[frs_computer_reference_bl] |
If the ObjectClass log field value is equal to group, then if the FrsComputerReferenceBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to frs_computer_reference_bl and the FrsComputerReferenceBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
FRSMemberReferenceBL |
entity.group.attribute.labels[frs_member_reference_bl] |
If the ObjectClass log field value is equal to group, then if the FRSMemberReferenceBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to frs_member_reference_bl and the FRSMemberReferenceBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
FSMORoleOwner |
entity.group.attribute.labels[fsmo_role_owner] |
If the ObjectClass log field value is equal to group, then if the FSMORoleOwner log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to fsmo_role_owner and the FSMORoleOwner log field is mapped to the entity.group.attribute.labels.value UDM field. |
GarbageCollPeriod |
entity.group.attribute.labels[garbage_coll_period] |
If the ObjectClass log field value is equal to group, then if the GarbageCollPeriod log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to garbage_coll_period and the GarbageCollPeriod log field is mapped to the entity.group.attribute.labels.value UDM field. |
GroupAttributes |
entity.group.attribute.labels[group_attributes] |
If the ObjectClass log field value is equal to group, then if the GroupAttributes log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to group_attributes and the GroupAttributes log field is mapped to the entity.group.attribute.labels.value UDM field. |
GroupMembershipSAM |
entity.group.attribute.labels[group_membership_sam] |
If the ObjectClass log field value is equal to group, then if the GroupMembershipSAM log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to group_membership_sam and the GroupMembershipSAM log field is mapped to the entity.group.attribute.labels.value UDM field. |
GroupType |
entity.group.attribute.labels[group_type] |
If the ObjectClass log field value is equal to group, then if the GroupType log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to group_type and the GroupType log field is mapped to the entity.group.attribute.labels.value UDM field. |
InstanceType |
entity.group.attribute.labels[instance_type] |
If the ObjectClass log field value is equal to group, then if the InstanceType log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to instance_type and the InstanceType log field is mapped to the entity.group.attribute.labels.value UDM field. |
IsCriticalSystemObject |
entity.group.attribute.labels[is_critical_system_object] |
If the ObjectClass log field value is equal to group, then if the IsCriticalSystemObject log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to is_critical_system_object and the IsCriticalSystemObject log field is mapped to the entity.group.attribute.labels.value UDM field. |
IsDeleted |
entity.group.attribute.labels[is_deleted] |
If the ObjectClass log field value is equal to group, then if the IsDeleted log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to is_deleted and the IsDeleted log field is mapped to the entity.group.attribute.labels.value UDM field. |
IsMemberOfDL |
entity.group.attribute.labels[is_member_of_dl] |
If the ObjectClass log field value is equal to group, then if the IsMemberOfDL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to is_member_of_dl and the IsMemberOfDL log field is mapped to the entity.group.attribute.labels.value UDM field. |
IsPrivilegeHolder |
entity.group.attribute.labels[is_privilege_holder] |
If the ObjectClass log field value is equal to group, then if the IsPrivilegeHolder log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to is_privilege_holder and the IsPrivilegeHolder log field is mapped to the entity.group.attribute.labels.value UDM field. |
LastKnownParent |
entity.group.attribute.labels[last_known_parent] |
If the ObjectClass log field value is equal to group, then if the LastKnownParent log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to last_known_parent and the LastKnownParent log field is mapped to the entity.group.attribute.labels.value UDM field. |
LegacyExchangeDN |
entity.group.attribute.labels[legacy_exchange_dn] |
If the ObjectClass log field value is equal to group, then if the LegacyExchangeDN log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to legacy_exchange_dn and the LegacyExchangeDN log field is mapped to the entity.group.attribute.labels.value UDM field. |
ManagedObjects |
entity.group.attribute.labels[managed_objects] |
If the ObjectClass log field value is equal to group, then if the ManagedObjects log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to managed_objects and the ManagedObjects log field is mapped to the entity.group.attribute.labels.value UDM field. |
MasteredBy |
entity.group.attribute.labels[mastered_by] |
If the ObjectClass log field value is equal to group, then if the MasteredBy log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to mastered_by and the MasteredBy log field is mapped to the entity.group.attribute.labels.value UDM field. |
ModifyTimeStamp |
entity.group.attribute.labels[modify_time_stamp] |
If the ObjectClass log field value is equal to group, then if the ModifyTimeStamp log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to modify_time_stamp and the ModifyTimeStamp log field is mapped to the entity.group.attribute.labels.value UDM field. |
MSDSConsistencyChildCount |
entity.group.attribute.labels[ms_ds_consistency_child_count] |
If the ObjectClass log field value is equal to group, then if the MSDSConsistencyChildCount log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_consistency_child_count and the MSDSConsistencyChildCount log field is mapped to the entity.group.attribute.labels.value UDM field. |
MSDSConsistencyGuid |
entity.group.attribute.labels[ms_ds_consistency_guid] |
If the ObjectClass log field value is equal to group, then if the MSDSConsistencyGuid log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_consistency_guid and the MSDSConsistencyGuid log field is mapped to the entity.group.attribute.labels.value UDM field. |
netbootSCPBL |
entity.group.attribute.labels[netboot_scp_bl] |
If the ObjectClass log field value is equal to group, then if the netbootSCPBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to netboot_scp_bl and the netbootSCPBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
NonSecurityMember |
entity.group.attribute.labels[non_security_member] |
If the ObjectClass log field value is equal to group, then if the NonSecurityMember log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to non_security_member and the NonSecurityMember log field is mapped to the entity.group.attribute.labels.value UDM field. |
NonSecurityMemberBL |
entity.group.attribute.labels[non_security_member_bl] |
If the ObjectClass log field value is equal to group, then if the NonSecurityMemberBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to non_security_member_bl and the NonSecurityMemberBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
NTGroupMembers |
entity.group.attribute.labels[nt_group_members] |
If the ObjectClass log field value is equal to group, then if the NTGroupMembers log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to nt_group_members and the NTGroupMembers log field is mapped to the entity.group.attribute.labels.value UDM field. |
NTSecurityDescriptor |
entity.group.attribute.labels[nt_security_descriptor] |
If the ObjectClass log field value is equal to group, then if the NTSecurityDescriptor log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to nt_security_descriptor and the NTSecurityDescriptor log field is mapped to the entity.group.attribute.labels.value UDM field. |
ObjDistName |
entity.group.attribute.labels[obj_dist_name] |
If the ObjectClass log field value is equal to group, then if the ObjDistName log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to obj_dist_name and the ObjDistName log field is mapped to the entity.group.attribute.labels.value UDM field. |
ObjectCategory |
entity.group.attribute.labels[object_category] |
If the ObjectClass log field value is equal to group, then if the ObjectCategory log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to object_category and the ObjectCategory log field is mapped to the entity.group.attribute.labels.value UDM field. |
ObjectVersion |
entity.group.attribute.labels[object_version] |
If the ObjectClass log field value is equal to group, then if the ObjectVersion log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to object_version and the ObjectVersion log field is mapped to the entity.group.attribute.labels.value UDM field. |
OperatorCount |
entity.group.attribute.labels[operator_count] |
If the ObjectClass log field value is equal to group, then if the OperatorCount log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to operator_count and the OperatorCount log field is mapped to the entity.group.attribute.labels.value UDM field. |
OtherWellKnownObjects |
entity.group.attribute.labels[other_well_known_objects] |
If the ObjectClass log field value is equal to group, then if the OtherWellKnownObjects log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to other_well_known_objects and the OtherWellKnownObjects log field is mapped to the entity.group.attribute.labels.value UDM field. |
PartialAttributeDeletionList |
entity.group.attribute.labels[partial_attribute_deletion_list] |
If the ObjectClass log field value is equal to group, then if the PartialAttributeDeletionList log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to partial_attribute_deletion_list and the PartialAttributeDeletionList log field is mapped to the entity.group.attribute.labels.value UDM field. |
PartialAttributeSet |
entity.group.attribute.labels[partial_attribute_set] |
If the ObjectClass log field value is equal to group, then if the PartialAttributeSet log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to partial_attribute_set and the PartialAttributeSet log field is mapped to the entity.group.attribute.labels.value UDM field. |
PossibleInferiors |
entity.group.attribute.labels[possible_inferiors] |
If the ObjectClass log field value is equal to group, then if the PossibleInferiors log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to possible_inferiors and the PossibleInferiors log field is mapped to the entity.group.attribute.labels.value UDM field. |
PrimaryGroupToken |
entity.group.attribute.labels[primary_group_token] |
If the ObjectClass log field value is equal to group, then if the PrimaryGroupToken log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to primary_group_token and the PrimaryGroupToken log field is mapped to the entity.group.attribute.labels.value UDM field. |
ProxiedObjectName |
entity.group.attribute.labels[proxied_object_name] |
If the ObjectClass log field value is equal to group, then if the ProxiedObjectName log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to proxied_object_name and the ProxiedObjectName log field is mapped to the entity.group.attribute.labels.value UDM field. |
ProxyAddresses |
entity.group.attribute.labels[proxy_addresses] |
If the ObjectClass log field value is equal to group, then if the ProxyAddresses log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to proxy_addresses and the ProxyAddresses log field is mapped to the entity.group.attribute.labels.value UDM field. |
QueryPolicyBL |
entity.group.attribute.labels[query_policy_bl] |
If the ObjectClass log field value is equal to group, then if the QueryPolicyBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to query_policy_bl and the QueryPolicyBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
RDN |
entity.group.attribute.labels[rdn] |
If the ObjectClass log field value is equal to group, then if the RDN log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to rdn and the RDN log field is mapped to the entity.group.attribute.labels.value UDM field. |
ReplPropertyMetaData |
entity.group.attribute.labels[repl_property_meta_data] |
If the ObjectClass log field value is equal to group, then if the ReplPropertyMetaData log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to repl_property_meta_data and the ReplPropertyMetaData log field is mapped to the entity.group.attribute.labels.value UDM field. |
ReplUpToDateVector |
entity.group.attribute.labels[repl_up_to_date_vector] |
If the ObjectClass log field value is equal to group, then if the ReplUpToDateVector log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to repl_up_to_date_vector and the ReplUpToDateVector log field is mapped to the entity.group.attribute.labels.value UDM field. |
Reports |
entity.group.attribute.labels[reports] |
If the ObjectClass log field value is equal to group, then if the Reports log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to reports and the Reports log field is mapped to the entity.group.attribute.labels.value UDM field. |
RepsFrom |
entity.group.attribute.labels[reps_from] |
If the ObjectClass log field value is equal to group, then if the RepsFrom log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to reps_from and the RepsFrom log field is mapped to the entity.group.attribute.labels.value UDM field. |
RepsTo |
entity.group.attribute.labels[reps_to] |
If the ObjectClass log field value is equal to group, then if the RepsTo log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to reps_to and the RepsTo log field is mapped to the entity.group.attribute.labels.value UDM field. |
Revision |
entity.group.attribute.labels[revision] |
If the ObjectClass log field value is equal to group, then if the Revision log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to revision and the Revision log field is mapped to the entity.group.attribute.labels.value UDM field. |
Rid |
entity.group.attribute.labels[rid] |
If the ObjectClass log field value is equal to group, then if the Rid log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to rid and the Rid log field is mapped to the entity.group.attribute.labels.value UDM field. |
SAMAccountName |
entity.group.attribute.labels[sam_account_name] |
If the ObjectClass log field value is equal to group, then if the SAMAccountName log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to sam_account_name and the SAMAccountName log field is mapped to the entity.group.attribute.labels.value UDM field. |
SAMAccountType |
entity.group.attribute.labels[sam_account_type] |
If the ObjectClass log field value is equal to group, then if the SAMAccountType log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to sam_account_type and the SAMAccountType log field is mapped to the entity.group.attribute.labels.value UDM field. |
SDRightsEffective |
entity.group.attribute.labels[sd_rights_effective] |
If the ObjectClass log field value is equal to group, then if the SDRightsEffective log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to sd_rights_effective and the SDRightsEffective log field is mapped to the entity.group.attribute.labels.value UDM field. |
SecurityIdentifier |
entity.group.attribute.labels[security_identifier] |
If the ObjectClass log field value is equal to group, then if the SecurityIdentifier log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to security_identifier and the SecurityIdentifier log field is mapped to the entity.group.attribute.labels.value UDM field. |
ServerReferenceBL |
entity.group.attribute.labels[server_reference_bl] |
If the ObjectClass log field value is equal to group, then if the ServerReferenceBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to server_reference_bl and the ServerReferenceBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
ShowInAddressBook |
entity.group.attribute.labels[show_in_address_book] |
If the ObjectClass log field value is equal to group, then if the ShowInAddressBook log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to show_in_address_book and the ShowInAddressBook log field is mapped to the entity.group.attribute.labels.value UDM field. |
ShowInAdvancedViewOnly |
entity.group.attribute.labels[show_in_advanced_view_only] |
If the ObjectClass log field value is equal to group, then if the ShowInAdvancedViewOnly log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to show_in_advanced_view_only and the ShowInAdvancedViewOnly log field is mapped to the entity.group.attribute.labels.value UDM field. |
SIDHistory |
entity.group.attribute.labels[sid_history] |
If the ObjectClass log field value is equal to group, then if the SIDHistory log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to sid_history and the SIDHistory log field is mapped to the entity.group.attribute.labels.value UDM field. |
SiteObjectBL |
entity.group.attribute.labels[site_object_bl] |
If the ObjectClass log field value is equal to group, then if the SiteObjectBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to site_object_bl and the SiteObjectBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
SubRefs |
entity.group.attribute.labels[sub_refs] |
If the ObjectClass log field value is equal to group, then if the SubRefs log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to sub_refs and the SubRefs log field is mapped to the entity.group.attribute.labels.value UDM field. |
SubSchemaSubEntry |
entity.group.attribute.labels[sub_schema_sub_entry] |
If the ObjectClass log field value is equal to group, then if the SubSchemaSubEntry log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to sub_schema_sub_entry and the SubSchemaSubEntry log field is mapped to the entity.group.attribute.labels.value UDM field. |
SupplementalCredentials |
entity.group.attribute.labels[supplemental_credentials] |
If the ObjectClass log field value is equal to group, then if the SupplementalCredentials log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to supplemental_credentials and the SupplementalCredentials log field is mapped to the entity.group.attribute.labels.value UDM field. |
SystemFlags |
entity.group.attribute.labels[system_flags] |
If the ObjectClass log field value is equal to group, then if the SystemFlags log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to system_flags and the SystemFlags log field is mapped to the entity.group.attribute.labels.value UDM field. |
TelephoneNumber |
entity.group.attribute.labels[telephone_number] |
If the ObjectClass log field value is equal to group, then if the TelephoneNumber log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to telephone_number and the TelephoneNumber log field is mapped to the entity.group.attribute.labels.value UDM field. |
TextEncodedORAddress |
entity.group.attribute.labels[text_encoded_or_address] |
If the ObjectClass log field value is equal to group, then if the TextEncodedORAddress log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to text_encoded_or_address and the TextEncodedORAddress log field is mapped to the entity.group.attribute.labels.value UDM field. |
TokenGroups |
entity.group.attribute.labels[token_groups] |
If the ObjectClass log field value is equal to group, then if the TokenGroups log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to token_groups and the TokenGroups log field is mapped to the entity.group.attribute.labels.value UDM field. |
TokenGroupsGlobalAndUniversal |
entity.group.attribute.labels[token_groups_global_and_universal] |
If the ObjectClass log field value is equal to group, then if the TokenGroupsGlobalAndUniversal log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to token_groups_global_and_universal and the TokenGroupsGlobalAndUniversal log field is mapped to the entity.group.attribute.labels.value UDM field. |
TokenGroupsNoGCAcceptable |
entity.group.attribute.labels[token_groups_no_gc_acceptable] |
If the ObjectClass log field value is equal to group, then if the TokenGroupsNoGCAcceptable log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to token_groups_no_gc_acceptable and the TokenGroupsNoGCAcceptable log field is mapped to the entity.group.attribute.labels.value UDM field. |
UserCert |
entity.group.attribute.labels[user_cert] |
If the ObjectClass log field value is equal to group, then if the UserCert log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to user_cert and the UserCert log field is mapped to the entity.group.attribute.labels.value UDM field. |
UserSMIMECertificate |
entity.group.attribute.labels[user_smime_certificate] |
If the ObjectClass log field value is equal to group, then if the UserSMIMECertificate log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to user_smime_certificate and the UserSMIMECertificate log field is mapped to the entity.group.attribute.labels.value UDM field. |
USNChanged |
entity.group.attribute.labels[usn_changed] |
If the ObjectClass log field value is equal to group, then if the USNChanged log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to usn_changed and the USNChanged log field is mapped to the entity.group.attribute.labels.value UDM field. |
USNCreated |
entity.group.attribute.labels[usn_created] |
If the ObjectClass log field value is equal to group, then if the USNCreated log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to usn_created and the USNCreated log field is mapped to the entity.group.attribute.labels.value UDM field. |
USNDSALastObjRemoved |
entity.group.attribute.labels[usn_dsa_last_obj_removed] |
If the ObjectClass log field value is equal to group, then if the USNDSALastObjRemoved log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to usn_dsa_last_obj_removed and the USNDSALastObjRemoved log field is mapped to the entity.group.attribute.labels.value UDM field. |
USNIntersite |
entity.group.attribute.labels[usn_intersite] |
If the ObjectClass log field value is equal to group, then if the USNIntersite log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to usn_intersite and the USNIntersite log field is mapped to the entity.group.attribute.labels.value UDM field. |
USNLastObjRem |
entity.group.attribute.labels[usn_last_obj_rem] |
If the ObjectClass log field value is equal to group, then if the USNLastObjRem log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to usn_last_obj_rem and the USNLastObjRem log field is mapped to the entity.group.attribute.labels.value UDM field. |
USNSource |
entity.group.attribute.labels[usn_source] |
If the ObjectClass log field value is equal to group, then if the USNSource log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to usn_source and the USNSource log field is mapped to the entity.group.attribute.labels.value UDM field. |
WbemPath |
entity.group.attribute.labels[wbem_path] |
If the ObjectClass log field value is equal to group, then if the WbemPath log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to wbem_path and the WbemPath log field is mapped to the entity.group.attribute.labels.value UDM field. |
WellKnownObjects |
entity.group.attribute.labels[well_known_objects] |
If the ObjectClass log field value is equal to group, then if the WellKnownObjects log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to well_known_objects and the WellKnownObjects log field is mapped to the entity.group.attribute.labels.value UDM field. |
WhenChanged |
entity.group.attribute.labels[when_changed] |
If the ObjectClass log field value is equal to group, then if the WhenChanged log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to when_changed and the WhenChanged log field is mapped to the entity.group.attribute.labels.value UDM field. |
WhenCreated |
entity.group.attribute.labels[when_created] |
If the ObjectClass log field value is equal to group, then if the WhenCreated log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to when_created and the WhenCreated log field is mapped to the entity.group.attribute.labels.value UDM field. |
WWWPageOther |
entity.group.attribute.labels[www_page_other] |
If the ObjectClass log field value is equal to group, then if the WWWPageOther log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to www_page_other and the WWWPageOther log field is mapped to the entity.group.attribute.labels.value UDM field. |
X509Cert |
entity.group.attribute.labels[x509_cert] |
If the ObjectClass log field value is equal to group, then if the X509Cert log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to x509_cert and the X509Cert log field is mapped to the entity.group.attribute.labels.value UDM field. |
labeledURI |
entity.group.attribute.labels[labeled_uri] |
If the ObjectClass log field value is equal to group, then if the labeledURI log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to labeled_uri and the labeledURI log field is mapped to the entity.group.attribute.labels.value UDM field. |
msCOMPartitionSetLink |
entity.group.attribute.labels[ms_com_partition_set_link] |
If the ObjectClass log field value is equal to group, then if the msCOMPartitionSetLink log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_com_partition_set_link and the msCOMPartitionSetLink log field is mapped to the entity.group.attribute.labels.value UDM field. |
msCOMUserLink |
entity.group.attribute.labels[ms_com_user_link] |
If the ObjectClass log field value is equal to group, then if the msCOMUserLink log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_com_user_link and the msCOMUserLink log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSApproxImmedSubordinates |
entity.group.attribute.labels[ms_ds_approx_immed_subordinates] |
If the ObjectClass log field value is equal to group, then if the msDSApproxImmedSubordinates log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_approx_immed_subordinates and the msDSApproxImmedSubordinates log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSAzLDAPQuery |
entity.group.attribute.labels[ms_ds_az_ldap_query] |
If the ObjectClass log field value is equal to group, then if the msDSAzLDAPQuery log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_az_ldap_query and the msDSAzLDAPQuery log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSKeyVersionNumber |
entity.group.attribute.labels[ms_ds_key_version_number] |
If the ObjectClass log field value is equal to group, then if the msDSKeyVersionNumber log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_key_version_number and the msDSKeyVersionNumber log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSMasteredBy |
entity.group.attribute.labels[ms_ds_mastered_by] |
If the ObjectClass log field value is equal to group, then if the msDSMasteredBy log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_mastered_by and the msDSMasteredBy log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSMembersForAzRoleBL |
entity.group.attribute.labels[ms_ds_members_for_az_role_bl] |
If the ObjectClass log field value is equal to group, then if the msDSMembersForAzRoleBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_members_for_az_role_bl and the msDSMembersForAzRoleBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSNCReplCursors |
entity.group.attribute.labels[ms_ds_nc_repl_cursors] |
If the ObjectClass log field value is equal to group, then if the msDSNCReplCursors log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_nc_repl_cursors and the msDSNCReplCursors log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSNCReplInboundNeighbors |
entity.group.attribute.labels[ms_ds_nc_repl_inbound_neighbors] |
If the ObjectClass log field value is equal to group, then if the msDSNCReplInboundNeighbors log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_nc_repl_inbound_neighbors and the msDSNCReplInboundNeighbors log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSNCReplOutboundNeighbors |
entity.group.attribute.labels[ms_ds_nc_repl_outbound_neighbors] |
If the ObjectClass log field value is equal to group, then if the msDSNCReplOutboundNeighbors log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_nc_repl_outbound_neighbors and the msDSNCReplOutboundNeighbors log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSNonMembers |
entity.group.attribute.labels[ms_ds_non_members] |
If the ObjectClass log field value is equal to group, then if the msDSNonMembers log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_non_members and the msDSNonMembers log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSNonMembersBL |
entity.group.attribute.labels[ms_ds_non_members_bl] |
If the ObjectClass log field value is equal to group, then if the msDSNonMembersBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_non_members_bl and the msDSNonMembersBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSObjectReferenceBL |
entity.group.attribute.labels[ms_ds_object_reference_bl] |
If the ObjectClass log field value is equal to group, then if the msDSObjectReferenceBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_object_reference_bl and the msDSObjectReferenceBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSOperationsForAzRoleBL |
entity.group.attribute.labels[ms_ds_operations_for_az_role_bl] |
If the ObjectClass log field value is equal to group, then if the msDSOperationsForAzRoleBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_operations_for_az_role_bl and the msDSOperationsForAzRoleBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSOperationsForAzTaskBL |
entity.group.attribute.labels[ms_ds_operations_for_az_task_bl] |
If the ObjectClass log field value is equal to group, then if the msDSOperationsForAzTaskBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_operations_for_az_task_bl and the msDSOperationsForAzTaskBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSReplAttributeMetaData |
entity.group.attribute.labels[ms_ds_repl_attribute_meta_data] |
If the ObjectClass log field value is equal to group, then if the msDSReplAttributeMetaData log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_repl_attribute_meta_data and the msDSReplAttributeMetaData log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSReplValueMetaData |
entity.group.attribute.labels[ms_ds_repl_value_meta_data] |
If the ObjectClass log field value is equal to group, then if the msDSReplValueMetaData log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_repl_value_meta_data and the msDSReplValueMetaData log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSTasksForAzRoleBL |
entity.group.attribute.labels[ms_ds_tasks_for_az_role_bl] |
If the ObjectClass log field value is equal to group, then if the msDSTasksForAzRoleBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_tasks_for_az_role_bl and the msDSTasksForAzRoleBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSTasksForAzTaskBL |
entity.group.attribute.labels[ms_ds_tasks_for_az_task_bl] |
If the ObjectClass log field value is equal to group, then if the msDSTasksForAzTaskBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_tasks_for_az_task_bl and the msDSTasksForAzTaskBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msExchAssistantName |
entity.group.attribute.labels[ms_exch_assistant_name] |
If the ObjectClass log field value is equal to group, then if the msExchAssistantName log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_exch_assistant_name and the msExchAssistantName log field is mapped to the entity.group.attribute.labels.value UDM field. |
msExchLabeledURI |
entity.group.attribute.labels[ms_exch_labeled_uri] |
If the ObjectClass log field value is equal to group, then if the msExchLabeledURI log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_exch_labeled_uri and the msExchLabeledURI log field is mapped to the entity.group.attribute.labels.value UDM field. |
msExchOwnerBL |
entity.group.attribute.labels[ms_exch_owner_bl] |
If the ObjectClass log field value is equal to group, then if the msExchOwnerBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_exch_owner_bl and the msExchOwnerBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
secretary |
entity.group.attribute.labels[secretary] |
If the ObjectClass log field value is equal to group, then if the secretary log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to secretary and the secretary log field is mapped to the entity.group.attribute.labels.value UDM field. |
StructuralObjectClass |
entity.group.attribute.labels[structural_object_class] |
If the ObjectClass log field value is equal to group, then if the StructuralObjectClass log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to structural_object_class and the StructuralObjectClass log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSDisableForInstancesBL |
entity.group.attribute.labels[ms_ds_disable_for_instances_bl] |
If the ObjectClass log field value is equal to group, then if the msDSDisableForInstancesBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_disable_for_instances_bl and the msDSDisableForInstancesBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSServiceAccountBL |
entity.group.attribute.labels[ms_ds_service_account_bl] |
If the ObjectClass log field value is equal to group, then if the msDSServiceAccountBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_service_account_bl and the msDSServiceAccountBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
gidNumber |
entity.group.attribute.labels[gid_number] |
If the ObjectClass log field value is equal to group, then if the gidNumber log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to gid_number and the gidNumber log field is mapped to the entity.group.attribute.labels.value UDM field. |
memberUid |
entity.group.attribute.labels[member_uid] |
If the ObjectClass log field value is equal to group, then if the memberUid log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to member_uid and the memberUid log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDFSRComputerReferenceBL |
entity.group.attribute.labels[ms_dfsr_computer_reference_bl] |
If the ObjectClass log field value is equal to group, then if the msDFSRComputerReferenceBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_dfsr_computer_reference_bl and the msDFSRComputerReferenceBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDFSRMemberReferenceBL |
entity.group.attribute.labels[ms_dfsr_member_reference_bl] |
If the ObjectClass log field value is equal to group, then if the msDFSRMemberReferenceBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_dfsr_member_reference_bl and the msDFSRMemberReferenceBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msSFU30Name |
entity.group.attribute.labels[ms_sfu30_name] |
If the ObjectClass log field value is equal to group, then if the msSFU30Name log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_sfu30_name and the msSFU30Name log field is mapped to the entity.group.attribute.labels.value UDM field. |
msSFU30NisDomain |
entity.group.attribute.labels[ms_sfu30_nis_domain] |
If the ObjectClass log field value is equal to group, then if the msSFU30NisDomain log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_sfu30_nis_domain and the msSFU30NisDomain log field is mapped to the entity.group.attribute.labels.value UDM field. |
msSFU30PosixMember |
entity.group.attribute.labels[ms_sfu30_posix_member] |
If the ObjectClass log field value is equal to group, then if the msSFU30PosixMember log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_sfu30_posix_member and the msSFU30PosixMember log field is mapped to the entity.group.attribute.labels.value UDM field. |
msSFU30PosixMemberOf |
entity.group.attribute.labels[ms_sfu30_posix_member_of] |
If the ObjectClass log field value is equal to group, then if the msSFU30PosixMemberOf log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_sfu30_posix_member_of and the msSFU30PosixMemberOf log field is mapped to the entity.group.attribute.labels.value UDM field. |
unixUserPassword |
entity.group.attribute.labels[unix_user_password] |
If the ObjectClass log field value is equal to group, then if the unixUserPassword log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to unix_user_password and the unixUserPassword log field is mapped to the entity.group.attribute.labels.value UDM field. |
UserPassword |
entity.group.attribute.labels[user_password] |
If the ObjectClass log field value is equal to group, then if the UserPassword log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to user_password and the UserPassword log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSAuthenticatedToAccountlist |
entity.group.attribute.labels[ms_ds_authenticated_to_accountlist] |
If the ObjectClass log field value is equal to group, then if the msDSAuthenticatedToAccountlist log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_authenticated_to_accountlist and the msDSAuthenticatedToAccountlist log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSAzApplicationData |
entity.group.attribute.labels[ms_ds_az_application_data] |
If the ObjectClass log field value is equal to group, then if the msDSAzApplicationData log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_az_application_data and the msDSAzApplicationData log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSAzBizRule |
entity.group.attribute.labels[ms_ds_az_biz_rule] |
If the ObjectClass log field value is equal to group, then if the msDSAzBizRule log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_az_biz_rule and the msDSAzBizRule log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSAzBizRuleLanguage |
entity.group.attribute.labels[ms_ds_az_biz_rule_language] |
If the ObjectClass log field value is equal to group, then if the msDSAzBizRuleLanguage log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_az_biz_rule_language and the msDSAzBizRuleLanguage log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSAzGenericData |
entity.group.attribute.labels[ms_ds_az_generic_data] |
If the ObjectClass log field value is equal to group, then if the msDSAzGenericData log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_az_generic_data and the msDSAzGenericData log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSAzLastImportedBizRulePath |
entity.group.attribute.labels[ms_ds_az_last_imported_biz_rule_path] |
If the ObjectClass log field value is equal to group, then if the msDSAzLastImportedBizRulePath log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_az_last_imported_biz_rule_path and the msDSAzLastImportedBizRulePath log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSAzObjectGuid |
entity.group.attribute.labels[ms_ds_az_object_guid] |
If the ObjectClass log field value is equal to group, then if the msDSAzObjectGuid log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_az_object_guid and the msDSAzObjectGuid log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSIsDomainFor |
entity.group.attribute.labels[ms_ds_is_domain_for] |
If the ObjectClass log field value is equal to group, then if the msDSIsDomainFor log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_is_domain_for and the msDSIsDomainFor log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSIsFullReplicaFor |
entity.group.attribute.labels[ms_ds_is_full_replica_for] |
If the ObjectClass log field value is equal to group, then if the msDSIsFullReplicaFor log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_is_full_replica_for and the msDSIsFullReplicaFor log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSIsPartialReplicaFor |
entity.group.attribute.labels[ms_ds_is_partial_replica_for] |
If the ObjectClass log field value is equal to group, then if the msDSIsPartialReplicaFor log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_is_partial_replica_for and the msDSIsPartialReplicaFor log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSKrbTgtLinkBL |
entity.group.attribute.labels[ms_ds_krb_tgt_link_bl] |
If the ObjectClass log field value is equal to group, then if the msDSKrbTgtLinkBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_krb_tgt_link_bl and the msDSKrbTgtLinkBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSNCROReplicaLocationsBL |
entity.group.attribute.labels[ms_ds_ncro_replica_locations_bl] |
If the ObjectClass log field value is equal to group, then if the msDSNCROReplicaLocationsBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_ncro_replica_locations_bl and the msDSNCROReplicaLocationsBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSNCType |
entity.group.attribute.labels[ms_ds_nc_type] |
If the ObjectClass log field value is equal to group, then if the msDSNCType log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_nc_type and the msDSNCType log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSPhoneticDisplayName |
entity.group.attribute.labels[ms_ds_phonetic_display_name] |
If the ObjectClass log field value is equal to group, then if the msDSPhoneticDisplayName log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_phonetic_display_name and the msDSPhoneticDisplayName log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSPrincipalName |
entity.group.attribute.labels[ms_ds_principal_name] |
If the ObjectClass log field value is equal to group, then if the msDSPrincipalName log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_principal_name and the msDSPrincipalName log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSPSOApplied |
entity.group.attribute.labels[ms_ds_pso_applied] |
If the ObjectClass log field value is equal to group, then if the msDSPSOApplied log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_pso_applied and the msDSPSOApplied log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSRevealedDSAs |
entity.group.attribute.labels[ms_ds_revealed_dsas] |
If the ObjectClass log field value is equal to group, then if the msDSRevealedDSAs log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_revealed_dsas and the msDSRevealedDSAs log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSRevealedListBL |
entity.group.attribute.labels[ms_ds_revealed_list_bl] |
If the ObjectClass log field value is equal to group, then if the msDSRevealedListBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_revealed_list_bl and the msDSRevealedListBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
IsRecycled |
entity.group.attribute.labels[is_recycled] |
If the ObjectClass log field value is equal to group, then if the IsRecycled log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to is_recycled and the IsRecycled log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSEnabledFeatureBL |
entity.group.attribute.labels[ms_ds_enabled_feature_bl] |
If the ObjectClass log field value is equal to group, then if the msDSEnabledFeatureBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_enabled_feature_bl and the msDSEnabledFeatureBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSHostServiceAccountBL |
entity.group.attribute.labels[ms_ds_host_service_account_bl] |
If the ObjectClass log field value is equal to group, then if the msDSHostServiceAccountBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_host_service_account_bl and the msDSHostServiceAccountBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSLastKnownRDN |
entity.group.attribute.labels[ms_ds_last_known_rdn] |
If the ObjectClass log field value is equal to group, then if the msDSLastKnownRDN log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_last_known_rdn and the msDSLastKnownRDN log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSlocalEffectiveDeletionTime |
entity.group.attribute.labels[ms_ds_local_effective_deletion_time] |
If the ObjectClass log field value is equal to group, then if the msDSlocalEffectiveDeletionTime log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_local_effective_deletion_time and the msDSlocalEffectiveDeletionTime log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSlocalEffectiveRecycleTime |
entity.group.attribute.labels[ms_ds_local_effective_recycle_time] |
If the ObjectClass log field value is equal to group, then if the msDSlocalEffectiveRecycleTime log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_local_effective_recycle_time and the msDSlocalEffectiveRecycleTime log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSOIDToGroupLinkBL |
entity.group.attribute.labels[ms_ds_oid_to_group_link_bl] |
If the ObjectClass log field value is equal to group, then if the msDSOIDToGroupLinkBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_oid_to_group_link_bl and the msDSOIDToGroupLinkBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSClaimSharesPossibleValuesWithBL |
entity.group.attribute.labels[ms_ds_claim_shares_possible_values_with_bl] |
If the ObjectClass log field value is equal to group, then if the msDSClaimSharesPossibleValuesWithBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_claim_shares_possible_values_with_bl and the msDSClaimSharesPossibleValuesWithBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSGeoCoordinatesAltitude |
entity.group.attribute.labels[ms_ds_geo_coordinates_altitude] |
If the ObjectClass log field value is equal to group, then if the msDSGeoCoordinatesAltitude log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_geo_coordinates_altitude and the msDSGeoCoordinatesAltitude log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSGeoCoordinatesLatitude |
entity.group.attribute.labels[ms_ds_geo_coordinates_latitude] |
If the ObjectClass log field value is equal to group, then if the msDSGeoCoordinatesLatitude log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_geo_coordinates_latitude and the msDSGeoCoordinatesLatitude log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSGeoCoordinatesLongitude |
entity.group.attribute.labels[ms_ds_geo_coordinates_longitude] |
If the ObjectClass log field value is equal to group, then if the msDSGeoCoordinatesLongitude log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_geo_coordinates_longitude and the msDSGeoCoordinatesLongitude log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSIsPrimaryComputerFor |
entity.group.attribute.labels[ms_ds_is_primary_computer_for] |
If the ObjectClass log field value is equal to group, then if the msDSIsPrimaryComputerFor log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_is_primary_computer_for and the msDSIsPrimaryComputerFor log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSMembersOfResourcePropertyListBL |
entity.group.attribute.labels[ms_ds_members_of_resource_property_list_bl] |
If the ObjectClass log field value is equal to group, then if the msDSMembersOfResourcePropertyListBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_members_of_resource_property_list_bl and the msDSMembersOfResourcePropertyListBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSPrimaryComputer |
entity.group.attribute.labels[ms_ds_primary_computer] |
If the ObjectClass log field value is equal to group, then if the msDSPrimaryComputer log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_primary_computer and the msDSPrimaryComputer log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSTDOEgressBL |
entity.group.attribute.labels[ms_ds_tdo_egress_bl] |
If the ObjectClass log field value is equal to group, then if the msDSTDOEgressBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_tdo_egress_bl and the msDSTDOEgressBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSTDOIngressBL |
entity.group.attribute.labels[ms_ds_tdo_ingress_bl] |
If the ObjectClass log field value is equal to group, then if the msDSTDOIngressBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_tdo_ingress_bl and the msDSTDOIngressBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
msDSValueTypeReferenceBL |
entity.group.attribute.labels[ms_ds_value_type_reference_bl] |
If the ObjectClass log field value is equal to group, then if the msDSValueTypeReferenceBL log field value is not empty, then the entity.group.attribute.labels.key UDM field is set to ms_ds_value_type_reference_bl and the msDSValueTypeReferenceBL log field is mapped to the entity.group.attribute.labels.value UDM field. |
AdminDisplayName |
entity.user.user_display_name |
If the ObjectClass log field value is equal to group, then if the ObjectClass log field value is equal to user or is empty, then if the AdminDisplayName log field value is not empty, then the AdminDisplayName log field is mapped to the entity.user.user_display_name UDM field. |
CanonicalName |
entity.administrative_domain |
If the ObjectClass log field value is equal to group, then if the CanonicalName log field value is not empty, then the CanonicalName log field is mapped to the entity.administrative_domain UDM field. |
CreateTimeStamp |
entity.group.creation_time |
If the ObjectClass log field value is equal to group, then if the CreateTimeStamp log field value is not empty, then the CreateTimeStamp log field is mapped to the entity.group.creation_time UDM field. |
Description |
metadata.description |
If the ObjectClass log field value is equal to group, then if the Description log field value is not empty, then the Description log field is mapped to the metadata.description UDM field. |
DesktopProfile |
entity.location.name |
If the ObjectClass log field value is equal to group, then if the DesktopProfile log field value is not empty, then the DesktopProfile log field is mapped to the entity.location.name UDM field. |
DisplayName |
entity.group.group_display_name |
If the ObjectClass log field value is equal to group, then if the DisplayName log field value is not empty, then the DisplayName log field is mapped to the entity.group.group_display_name UDM field. |
EmailAddresses |
entity.group.email_addresses |
If the ObjectClass log field value is equal to group, then if the EmailAddresses log field value is not empty, then the EmailAddresses log field is mapped to the entity.group.email_addresses UDM field. |
ManagedBy |
entity.relations.entity.user.user_display_name |
If the ObjectClass log field value is equal to group, then if the ManagedBy log field value is not empty, then the ManagedBy log field is mapped to the entity.relations.entity.user.user_display_name UDM field. |
Member |
entity.relations.entity.group.group_display_name |
If the ObjectClass log field value is equal to group, then if the Member log field value is not empty, then the Member log field is mapped to the entity.relations.entity.group.group_display_name UDM field. |
ObjectGuid |
entity.group.product_object_id |
If the ObjectClass log field value is equal to group, then if the ObjectGuid log field value is not empty, then the ObjectGuid log field is mapped to the entity.group.product_object_id UDM field. |
ObjectSid |
entity.group.windows_sid |
If the ObjectClass log field value is equal to group, then if the ObjectSid log field value is not empty, then the ObjectSid log field is mapped to the entity.group.windows_sid UDM field. |
WWWHomePage |
entity.url |
If the ObjectClass log field value is equal to group, then if the WWWHomePage log field value is not empty, then the WWWHomePage log field is mapped to the entity.url UDM field. |
Need more help? Get answers from Community members and Google SecOps professionals.
