Raccogliere i dati di Microsoft Windows AD
Questo documento include le seguenti informazioni:
- Architettura di deployment e passaggi di installazione, oltre a qualsiasi configurazione obbligatoria che produca log supportati dal parser di Google Security Operations per gli eventi di Microsoft Windows Active Directory. Per una panoramica dell'importazione dati in Google Security Operations, consulta Importazione dei dati in Google Security Operations.
- Informazioni su come il parser mappa i campi nel log originale ai campi del modello di dati unificato di Google Security Operations.
In base all'architettura di deployment, configura l'agente Bindplane o l'agente NXLog per importare i log di Microsoft Windows Active Directory in Google Security Operations. Ti consigliamo di utilizzare Bindplane Agent per inoltrare i log di Windows Active Directory a Google Security Operations.
Le informazioni in questo documento si applicano al parser con l'etichetta di importazione WINDOWS_AD. L'etichetta di importazione identifica il parser che normalizza i dati di log non elaborati in formato UDM strutturato.
Prima di iniziare
Prima di configurare l'agente Bindplane o l'agente NXLog, completa le seguenti attività:
- Configura tutti i sistemi in modo che utilizzino il fuso orario UTC.
- Configura i server Microsoft Windows AD.
- Esamina le versioni e i dispositivi supportati.
- Esamina i tipi di log supportati.
Configurare i server AD Microsoft Windows
Su ogni server Microsoft Windows Active Directory, crea e configura uno script PowerShell per salvare i dati dei log in un file di output. L'agente Bindplane o NXLog legge il file di output.
# Set the location where the log file will be written $OUTPUT_FILENAME="<Path_of_the_output_file>" If (Test-Path -Path $OUTPUT_FILENAME) { Remove-Item -path $OUTPUT_FILENAME -ErrorAction SilentlyContinue} # USER_CONTEXT: Gets all Active Directory users and their properties. Get-ADUser -Filter * -properties samAccountName | % { Get-ADUser $_.SamAccountName -properties * | ConvertTo-JSON -compress | Out-File -encoding utf8 $OUTPUT_FILENAME -Append } # ASSET_CONTEXT: Gets all Active Directory assets and their properties. Get-ADComputer -Filter * -properties samAccountName | % { Get-ADComputer $_.SamAccountName -properties * | ConvertTo-JSON -compress | Out-File -encoding utf8 $OUTPUT_FILENAME -Append }Sostituisci quanto segue :
- Sostituisci il valore di
$OUTPUT_FILENAMEcon la posizione del file di output. - Memorizza i dati in formato JSON.
- Imposta la codifica su UTF-8.
- Utilizza il parametro
-Filteranziché-LDAPFilterquando chiami i cmdletGet-ADUsereGet-ADComputer.
- Sostituisci il valore di
Crea un'attività ricorrente che esegua lo script per recuperare e scrivere i dati nel file di output.
- Apri l'applicazione Utilità di pianificazione.
- Fai clic su Crea attività.
- Inserisci un nome e una descrizione per l'attività.
- Seleziona la casella di controllo Esegui con i privilegi più elevati per assicurarti che tutti i dati vengano recuperati.
- Nella scheda Trigger, definisci quando vuoi ripetere l'attività.
- Nella scheda Azione, aggiungi una nuova azione e specifica il percorso del file in cui è memorizzato lo script.
Esamina i dispositivi e le versioni supportati
Microsoft Windows Server viene rilasciato con le seguenti versioni: Foundation, Essentials, Standard e Datacenter. Lo schema degli eventi dei log generati da ogni versione non è diverso.
Il parser di Google Security Operations supporta i log delle seguenti versioni di server Microsoft Windows:
- Microsoft Windows Server 2019
- Microsoft Windows Server 2016
- Microsoft Windows Server 2012
Il parser di Google Security Operations supporta i log raccolti da NXLog Community Edition o Enterprise Edition.
Esamina i tipi di log supportati
Il parser di Google Security Operations analizzerà e normalizzerà i dati recuperati dal contesto utente e dal contesto asset. Supporta i log generati con testo in lingua inglese e non supporta i log generati in lingue diverse dall'inglese.
Configura l'agente Bindplane
Ti consigliamo di utilizzare l'agente Bindplane per inoltrare i log di Windows Active Directory a Google Security Operations.
Dopo l'installazione, il servizio dell'agente Bindplane viene visualizzato come servizio observIQ nell'elenco dei servizi Windows.
- Installa l'agente Bindplane su ogni server Windows Active Directory. Per ulteriori informazioni sull'installazione dell'agente Bindplane, consulta le istruzioni di installazione dell'agente Bindplane.
Crea un file di configurazione per l'agente Bindplane con i seguenti contenuti:
receivers: filelog: include: [ `FILE_PATH` ] operators: - type: json_parser start_at: beginning windowseventlog/activedirectoryservice: channel: Directory Service raw: true processors: batch: exporters: chronicle/activedirectory: endpoint: https://malachiteingestion-pa.googleapis.com creds: '{ "type": "service_account", "project_id": "malachite-projectname", "private_key_id": `PRIVATE_KEY_ID`, "private_key": `PRIVATE_KEY`, "client_email":"`SERVICE_ACCOUNT_NAME`@malachite-`PROJECT_ID`.iam.gserviceaccount.com", "client_id": `CLIENT_ID`, "auth_uri": "https://accounts.google.com/o/oauth2/auth", "token_uri": "https://oauth2.googleapis.com/token", "auth_provider_x509_cert_url":"https://www.googleapis.com/oauth2/v1/certs", "client_x509_cert_url": "https://www.googleapis.com/robot/v1/metadata/x509/`SERVICSERVICE_ACCOUNT_NAME`%40malachite-`PROJECT_ID`.iam.gserviceaccount.com", "universe_domain": "googleapis.com" }' log_type: 'WINDOWS_AD' override_log_type: false raw_log_field: body customer_id: `CUSTOMER_ID` service: pipelines: logs/ads: receivers: - filelog - windowseventlog/activedirectoryservice processors: [batch] exporters: [chronicle/activedirectory]Sostituisci quanto segue :
FILE_PATHcon il percorso del file in cui è stato memorizzato l'output dello script di PowerShell menzionato in Configurare i server Microsoft Windows AD.PRIVATE_KEY_ID,PRIVATE_KEYSERVICSERVICE_ACCOUNT_NAME,PROJECT_ID,CLIENT_IDeCUSTOMER_IDcon i rispettivi valori del file JSON dell'account di servizio che puoi scaricare da Google Cloud. Per ulteriori informazioni sulle chiavi degli account di servizio, vedi Creare ed eliminare le chiavi degli account di servizio.
Per avviare il servizio dell'agente Bindplane (in precedenza noto come observIQ), seleziona Servizi > Estensioni > il servizio observIQ > Avvia.
Configurare l'agente NXLog
Il seguente diagramma mostra un'architettura in cui sono installati agenti NXLog per raccogliere e inviare eventi Microsoft Windows a Google Security Operations. Confronta queste informazioni con il tuo ambiente per assicurarti che questi componenti siano installati. Il tuo deployment potrebbe essere diverso da questa architettura e potrebbe essere più complesso.
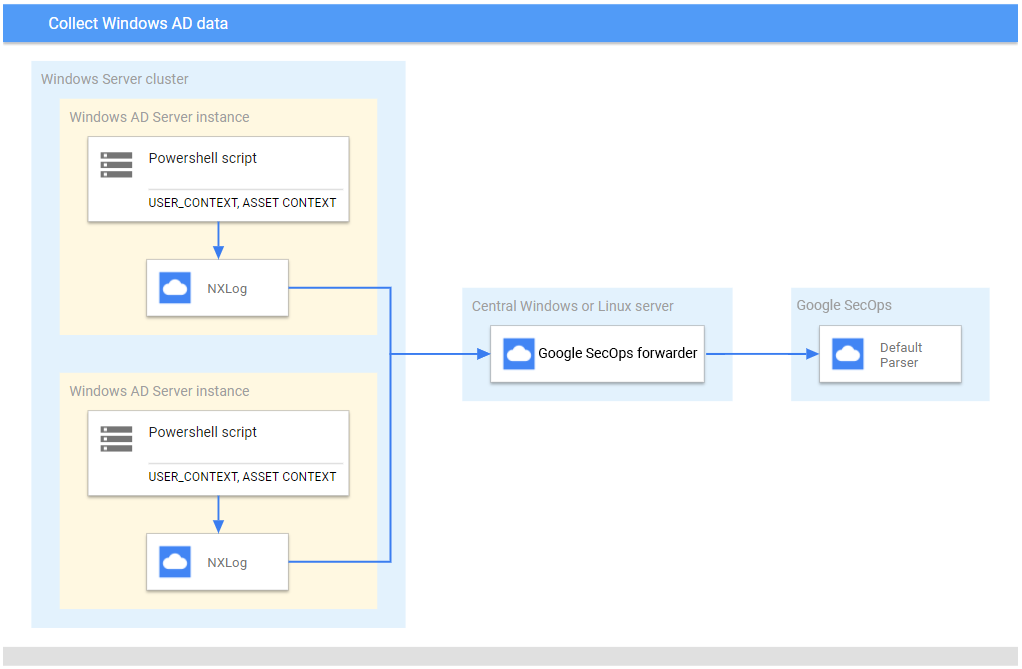
Se utilizzi l'agente NXLog anziché l'agente Bindplane, verifica quanto segue:
- Su ogni server Microsoft Windows che esegue Active Directory viene creato e configurato uno script PowerShell per raccogliere i dati di
USER_CONTEXTeASSET_CONTEXT. Per ulteriori informazioni, consulta Configurare i server Microsoft Windows AD. - NXLog è installato su ogni server AD Microsoft Windows per inviare i dati al server Linux o Microsoft Windows Server centrale.
- Il forwarder di Google Security Operations viene installato sul server Microsoft Windows Server o Linux centrale per inoltrare i dati dei log a Google Security Operations.
Configura NXLog
- Installa l'agente NXLog su ogni raccoglitore in esecuzione sul server Windows Active Directory. Questa applicazione inoltra i log al server Microsoft Windows o Linux centrale. Per ulteriori informazioni, consulta la documentazione di NXLog.
Crea un file di configurazione per ogni istanza NXLog. Utilizza il modulo NXLog
im_fileper leggere il file e analizzare le righe in campi. Utilizzaom_tcpper inoltrare i dati al server Microsoft Windows o Linux centrale.Di seguito è riportato un esempio di configurazione di NXLog. Sostituisci i valori
<hostname>e<port>con le informazioni sul server Microsoft Windows o Linux centrale di destinazione. Nella sezione<Input in_adcontext>e nella proprietàFile, aggiungi il percorso del file di log di output scritto dallo script PowerShell. Imposta sempreDirCheckIntervalePollInterval. Se non sono definiti, NXLog esamina i file ogni 1 secondo.define ROOT C:\Program Files\nxlog define ADCONTEXT_OUTPUT_DESTINATION_ADDRESS <hostname> define ADCONTEXT_OUTPUT_DESTINATION_PORT <port> Moduledir %ROOT%\modules CacheDir %ROOT%\data Pidfile %ROOT%\data\nxlog.pid SpoolDir %ROOT%\data LogFile %ROOT%\data\nxlog.log <Input in_adcontext> Module im_file File "<Path_of_the_output_file>" DirCheckInterval 3600 PollInterval 3600 </Input> <Output out_chronicle_adcontext> Module om_tcp Host %ADCONTEXT_OUTPUT_DESTINATION_ADDRESS% Port %ADCONTEXT_OUTPUT_DESTINATION_PORT% </Output> <Route ad_context_to_chronicle> Path in_adcontext => out_chronicle_adcontext </Route>Avvia il servizio NXLog in ogni sistema.
Configurare il forwarder su un server centrale
Per informazioni sull'installazione e sulla configurazione del forwarder su Linux, consulta Installare e configurare il forwarder su Linux. Per informazioni sull'installazione e sulla configurazione del forwarder su Microsoft Windows, vedi Installare e configurare il forwarder su Microsoft Windows.
- Configura il sistema con il fuso orario UTC.
- Installa il forwarder di Google Security Operations sul server Microsoft Windows o Linux centrale.
Configura il forwarder di Google Security Operations per inviare i log a Google Security Operations. Di seguito è riportato un esempio di configurazione dell'agente di inoltro:
- syslog: common: enabled: true data_type: WINDOWS_AD batch_n_seconds: 10 batch_n_bytes: 1048576 tcp_address: 0.0.0.0:10518 connection_timeout_sec: 60
Formati dei log di Windows AD supportati
L'interprete di AD Windows supporta i log in formato JSON.
Log di esempio di AD Windows supportati
JSON:
{ "GivenName": "user1", "Surname": "itadmin", "UserPrincipalName": "user1.itadmin@testdhcp2.local", "Enabled": true, "SamAccountName": "user1.itadmin", "SID": { "BinaryLength": 28, "AccountDomainSid": { "BinaryLength": 24, "AccountDomainSid": "S-1-2-3", "Value": "S-1-2-3" }, "Value": "S-1-2-3-4000" }, "DistinguishedName": "CN=test,CN=Users,DC=testdhcp2,DC=local", "Name": "test", "ObjectClass": "user", "ObjectGuid": "4bde3f8d-8e9e-4ded-9d71-126ba9cd1300", "PropertyNames": [ "AccountExpirationDate", "accountExpires", "AccountLockoutTime", "AccountNotDelegated", "AllowReversiblePasswordEncryption", "AuthenticationPolicy", "AuthenticationPolicySilo", "BadLogonCount", "badPasswordTime", "badPwdCount", "c", "CannotChangePassword", "CanonicalName", "Certificates", "City", "CN", "co", "codePage", "Company", "CompoundIdentitySupported", "Country", "countryCode", "Created", "createTimeStamp", "Deleted", "Department", "Description", "DisplayName", "DistinguishedName", "Division", "DoesNotRequirePreAuth", "dSCorePropagationData", "EmailAddress", "EmployeeID", "EmployeeNumber", "Enabled", "facsimileTelephoneNumber", "Fax", "GivenName", "HomeDirectory", "HomedirRequired", "HomeDrive", "HomePage", "HomePhone", "Initials", "instanceType", "ipPhone", "isDeleted", "KerberosEncryptionType", "l", "LastBadPasswordAttempt", "LastKnownParent", "lastLogoff", "lastLogon", "LastLogonDate", "lastLogonTimestamp", "LockedOut", "lockoutTime", "logonCount", "logonHours", "LogonWorkstations", "mail", "Manager", "MemberOf", "MNSLogonAccount", "mobile", "MobilePhone", "Modified", "modifyTimeStamp", "msDS-SupportedEncryptionTypes", "msDS-User-Account-Control-Computed", "Name", "nTSecurityDescriptor", "ObjectCategory", "ObjectClass", "ObjectGUID", "objectSid", "Office", "OfficePhone", "Organization", "OtherName", "pager", "PasswordExpired", "PasswordLastSet", "PasswordNeverExpires", "PasswordNotRequired", "physicalDeliveryOfficeName", "POBox", "PostalCode", "postOfficeBox", "PrimaryGroup", "primaryGroupID", "PrincipalsAllowedToDelegateToAccount", "ProfilePath", "ProtectedFromAccidentalDeletion", "pwdLastSet", "SamAccountName", "sAMAccountType", "ScriptPath", "sDRightsEffective", "ServicePrincipalNames", "SID", "SIDHistory", "SmartcardLogonRequired", "sn", "st", "State", "StreetAddress", "Surname", "telephoneNumber", "Title", "TrustedForDelegation", "TrustedToAuthForDelegation", "UseDESKeyOnly", "userAccountControl", "userCertificate", "userParameters", "UserPrincipalName", "uSNChanged", "uSNCreated", "whenChanged", "whenCreated", "wWWHomePage" ], "AddedProperties": [], "RemovedProperties": [], "ModifiedProperties": [], "PropertyCount": 123, "AccountExpirationDate": null, "accountExpires": 0, "AccountLockoutTime": "\\/Date(1631175863106)\\/", "AccountNotDelegated": true, "AllowReversiblePasswordEncryption": false, "AuthenticationPolicy": [], "AuthenticationPolicySilo": [], "BadLogonCount": 3, "badPasswordTime": 132756494631068585, "badPwdCount": 3, "c": "IN", "CannotChangePassword": false, "CanonicalName": "testdhcp2.local/Users/test", "Certificates": [], "City": "Ahmedabad", "CN": "test", "co": "India", "codePage": 0, "Company": "user", "CompoundIdentitySupported": [ false ], "Country": "IN", "countryCode": 356, "Created": "\\/Date(1628229355000)\\/", "createTimeStamp": "\\/Date(1628229355000)\\/", "Deleted": null, "Department": "it", "Description": "itadmin", "DisplayName": "user1", "Division": "test", "DoesNotRequirePreAuth": false, "dSCorePropagationData": [ "\\/Date(1631191510000)\\/", "\\/Date(-11644473600000)\\/" ], "EmailAddress": "user@dummy.local", "EmployeeID": null, "EmployeeNumber": null, "facsimileTelephoneNumber": "12345678", "Fax": "12345678", "HomeDirectory": "\\\\\\\\DHCP-AD01\\\\ADContext", "HomedirRequired": false, "HomeDrive": "G:", "HomePage": "www.test.com", "HomePhone": "123456789", "Initials": "user1", "instanceType": 4, "ipPhone": "1121", "isDeleted": null, "KerberosEncryptionType": [ 0 ], "l": "ahmedabad", "LastBadPasswordAttempt": "\\/Date(1631175863106)\\/", "LastKnownParent": null, "lastLogoff": 0, "lastLogon": 132756492460689244, "LastLogonDate": "\\/Date(1631175025098)\\/", "lastLogonTimestamp": 132756486250985369, "LockedOut": false, "lockoutTime": 132756494631068585, "logonCount": 2, "logonHours": [ 0, 0, 248, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 7, 0, 0, 0, 0, 0, 0 ], "LogonWorkstations": null, "mail": "user@dummy.local", "Manager": "CN=Administrator,CN=Users,DC=testdhcp2,DC=local", "MemberOf": [ "CN=Netwrix Auditor Client Users,CN=Users,DC=dnstest2,DC=local", "CN=Netwrix Auditor Administrators,CN=Users,DC=dnstest2,DC=local", "CN=Group Policy Creator Owners,CN=Users,DC=dnstest2,DC=local", "CN=Domain Admins,CN=Users,DC=dnstest2,DC=local", "CN=Enterprise Admins,CN=Users,DC=dnstest2,DC=local", "CN=Schema Admins,CN=Users,DC=dnstest2,DC=local", "CN=Remote Desktop Users,CN=Builtin,DC=dnstest2,DC=local", "CN=Administrators,CN=Builtin,DC=dnstest2,DC=local" ], "MNSLogonAccount": false, "mobile": "923456789", "MobilePhone": "823456789", "Modified": "\\/Date(1631277960000)\\/", "modifyTimeStamp": "\\/Date(1631277960000)\\/", "msDS-SupportedEncryptionTypes": 0, "msDS-User-Account-Control-Computed": 0, "nTSecurityDescriptor": { "AccessRightType": { "Module": "System.DirectoryServices.dll", "Assembly": "System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a", "TypeHandle": "System.RuntimeTypeHandle", "DeclaringMethod": null, "BaseType": "System.Enum", "UnderlyingSystemType": "System.DirectoryServices.ActiveDirectoryRights", "FullName": "System.DirectoryServices.ActiveDirectoryRights", "AssemblyQualifiedName": "System.DirectoryServices.ActiveDirectoryRights, System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a", "Namespace": "System.DirectoryServices", "GUID": "f65acb9b-4c77-33ff-8523-43e9cc2c5798", "IsEnum": true, "GenericParameterAttributes": null, "IsSecurityCritical": false, "IsSecuritySafeCritical": false, "IsSecurityTransparent": true, "IsGenericTypeDefinition": false, "IsGenericParameter": false, "GenericParameterPosition": null, "IsGenericType": false, "IsConstructedGenericType": false, "ContainsGenericParameters": false, "StructLayoutAttribute": "System.Runtime.InteropServices.StructLayoutAttribute", "Name": "ActiveDirectoryRights", "MemberType": 32, "DeclaringType": null, "ReflectedType": null, "MetadataToken": 33554438, "GenericTypeParameters": "", "DeclaredConstructors": "", "DeclaredEvents": "", "DeclaredFields": "Int32 value__ System.DirectoryServices.ActiveDirectoryRights Delete System.DirectoryServices.ActiveDirectoryRights ReadControl System.DirectoryServices.ActiveDirectoryRights WriteDacl System.DirectoryServices.ActiveDirectoryRights WriteOwner System.DirectoryServices.ActiveDirectoryRights Synchronize System.DirectoryServices.ActiveDirectoryRights AccessSystemSecurity System.DirectoryServices.ActiveDirectoryRights GenericRead System.DirectoryServices.ActiveDirectoryRights GenericWrite System.DirectoryServices.ActiveDirectoryRights GenericExecute System.DirectoryServices.ActiveDirectoryRights GenericAll System.DirectoryServices.ActiveDirectoryRights CreateChild System.DirectoryServices.ActiveDirectoryRights DeleteChild System.DirectoryServices.ActiveDirectoryRights ListChildren System.DirectoryServices.ActiveDirectoryRights Self System.DirectoryServices.ActiveDirectoryRights ReadProperty System.DirectoryServices.ActiveDirectoryRights WriteProperty System.DirectoryServices.ActiveDirectoryRights DeleteTree System.DirectoryServices.ActiveDirectoryRights ListObject System.DirectoryServices.ActiveDirectoryRights ExtendedRight", "DeclaredMembers": "Int32 value__ System.DirectoryServices.ActiveDirectoryRights Delete System.DirectoryServices.ActiveDirectoryRights ReadControl System.DirectoryServices.ActiveDirectoryRights WriteDacl System.DirectoryServices.ActiveDirectoryRights WriteOwner System.DirectoryServices.ActiveDirectoryRights Synchronize System.DirectoryServices.ActiveDirectoryRights AccessSystemSecurity System.DirectoryServices.ActiveDirectoryRights GenericRead System.DirectoryServices.ActiveDirectoryRights GenericWrite System.DirectoryServices.ActiveDirectoryRights GenericExecute System.DirectoryServices.ActiveDirectoryRights GenericAll System.DirectoryServices.ActiveDirectoryRights CreateChild System.DirectoryServices.ActiveDirectoryRights DeleteChild System.DirectoryServices.ActiveDirectoryRights ListChildren System.DirectoryServices.ActiveDirectoryRights Self System.DirectoryServices.ActiveDirectoryRights ReadProperty System.DirectoryServices.ActiveDirectoryRights WriteProperty System.DirectoryServices.ActiveDirectoryRights DeleteTree System.DirectoryServices.ActiveDirectoryRights ListObject System.DirectoryServices.ActiveDirectoryRights ExtendedRight", "DeclaredMethods": "", "DeclaredNestedTypes": "", "DeclaredProperties": "", "ImplementedInterfaces": "System.IComparable System.IFormattable System.IConvertible", "TypeInitializer": null, "IsNested": false, "Attributes": 257, "IsVisible": true, "IsNotPublic": false, "IsPublic": true, "IsNestedPublic": false, "IsNestedPrivate": false, "IsNestedFamily": false, "IsNestedAssembly": false, "IsNestedFamANDAssem": false, "IsNestedFamORAssem": false, "IsAutoLayout": true, "IsLayoutSequential": false, "IsExplicitLayout": false, "IsClass": false, "IsInterface": false, "IsValueType": true, "IsAbstract": false, "IsSealed": true, "IsSpecialName": false, "IsImport": false, "IsSerializable": true, "IsAnsiClass": true, "IsUnicodeClass": false, "IsAutoClass": false, "IsArray": false, "IsByRef": false, "IsPointer": false, "IsPrimitive": false, "IsCOMObject": false, "HasElementType": false, "IsContextful": false, "IsMarshalByRef": false, "GenericTypeArguments": "", "CustomAttributes": "[System.FlagsAttribute()]" }, "AccessRuleType": { "Module": "System.DirectoryServices.dll", "Assembly": "System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a", "TypeHandle": "System.RuntimeTypeHandle", "DeclaringMethod": null, "BaseType": "System.Security.AccessControl.ObjectAccessRule", "UnderlyingSystemType": "System.DirectoryServices.ActiveDirectoryAccessRule", "FullName": "System.DirectoryServices.ActiveDirectoryAccessRule", "AssemblyQualifiedName": "System.DirectoryServices.ActiveDirectoryAccessRule, System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a", "Namespace": "System.DirectoryServices", "GUID": "0db7ea8c-53d9-3d6d-8b09-bb209cf0d0ae", "IsEnum": false, "GenericParameterAttributes": null, "IsSecurityCritical": false, "IsSecuritySafeCritical": false, "IsSecurityTransparent": true, "IsGenericTypeDefinition": false, "IsGenericParameter": false, "GenericParameterPosition": null, "IsGenericType": false, "IsConstructedGenericType": false, "ContainsGenericParameters": false, "StructLayoutAttribute": "System.Runtime.InteropServices.StructLayoutAttribute", "Name": "ActiveDirectoryAccessRule", "MemberType": 32, "DeclaringType": null, "ReflectedType": null, "MetadataToken": 33554445, "GenericTypeParameters": "", "DeclaredConstructors": "Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, Int32, System.Security.AccessControl.AccessControlType, System.Guid, Boolean, System.Security.AccessControl.InheritanceFlags, System.Security.AccessControl.PropagationFlags, System.Guid)", "DeclaredEvents": "", "DeclaredFields": "", "DeclaredMembers": "System.DirectoryServices.ActiveDirectoryRights get_ActiveDirectoryRights() System.DirectoryServices.ActiveDirectorySecurityInheritance get_InheritanceType() Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AccessControlType, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, Int32, System.Security.AccessControl.AccessControlType, System.Guid, Boolean, System.Security.AccessControl.InheritanceFlags, System.Security.AccessControl.PropagationFlags, System.Guid) System.DirectoryServices.ActiveDirectoryRights ActiveDirectoryRights System.DirectoryServices.ActiveDirectorySecurityInheritance InheritanceType", "DeclaredMethods": "System.DirectoryServices.ActiveDirectoryRights get_ActiveDirectoryRights() System.DirectoryServices.ActiveDirectorySecurityInheritance get_InheritanceType()", "DeclaredNestedTypes": "", "DeclaredProperties": "System.DirectoryServices.ActiveDirectoryRights ActiveDirectoryRights System.DirectoryServices.ActiveDirectorySecurityInheritance InheritanceType", "ImplementedInterfaces": "", "TypeInitializer": null, "IsNested": false, "Attributes": 1048577, "IsVisible": true, "IsNotPublic": false, "IsPublic": true, "IsNestedPublic": false, "IsNestedPrivate": false, "IsNestedFamily": false, "IsNestedAssembly": false, "IsNestedFamANDAssem": false, "IsNestedFamORAssem": false, "IsAutoLayout": true, "IsLayoutSequential": false, "IsExplicitLayout": false, "IsClass": true, "IsInterface": false, "IsValueType": false, "IsAbstract": false, "IsSealed": false, "IsSpecialName": false, "IsImport": false, "IsSerializable": false, "IsAnsiClass": true, "IsUnicodeClass": false, "IsAutoClass": false, "IsArray": false, "IsByRef": false, "IsPointer": false, "IsPrimitive": false, "IsCOMObject": false, "HasElementType": false, "IsContextful": false, "IsMarshalByRef": false, "GenericTypeArguments": "", "CustomAttributes": "" }, "AuditRuleType": { "Module": "System.DirectoryServices.dll", "Assembly": "System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a", "TypeHandle": "System.RuntimeTypeHandle", "DeclaringMethod": null, "BaseType": "System.Security.AccessControl.ObjectAuditRule", "UnderlyingSystemType": "System.DirectoryServices.ActiveDirectoryAuditRule", "FullName": "System.DirectoryServices.ActiveDirectoryAuditRule", "AssemblyQualifiedName": "System.DirectoryServices.ActiveDirectoryAuditRule, System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a", "Namespace": "System.DirectoryServices", "GUID": "4ad0312a-2ed0-3526-97ec-f9c6f310c5e0", "IsEnum": false, "GenericParameterAttributes": null, "IsSecurityCritical": false, "IsSecuritySafeCritical": false, "IsSecurityTransparent": true, "IsGenericTypeDefinition": false, "IsGenericParameter": false, "GenericParameterPosition": null, "IsGenericType": false, "IsConstructedGenericType": false, "ContainsGenericParameters": false, "StructLayoutAttribute": "System.Runtime.InteropServices.StructLayoutAttribute", "Name": "ActiveDirectoryAuditRule", "MemberType": 32, "DeclaringType": null, "ReflectedType": null, "MetadataToken": 33554453, "GenericTypeParameters": "", "DeclaredConstructors": "Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, Int32, System.Security.AccessControl.AuditFlags, System.Guid, Boolean, System.Security.AccessControl.InheritanceFlags, System.Security.AccessControl.PropagationFlags, System.Guid)", "DeclaredEvents": "", "DeclaredFields": "", "DeclaredMembers": "System.DirectoryServices.ActiveDirectoryRights get_ActiveDirectoryRights() System.DirectoryServices.ActiveDirectorySecurityInheritance get_InheritanceType() Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, System.DirectoryServices.ActiveDirectoryRights, System.Security.AccessControl.AuditFlags, System.Guid, System.DirectoryServices.ActiveDirectorySecurityInheritance, System.Guid) Void .ctor(System.Security.Principal.IdentityReference, Int32, System.Security.AccessControl.AuditFlags, System.Guid, Boolean, System.Security.AccessControl.InheritanceFlags, System.Security.AccessControl.PropagationFlags, System.Guid) System.DirectoryServices.ActiveDirectoryRights ActiveDirectoryRights System.DirectoryServices.ActiveDirectorySecurityInheritance InheritanceType", "DeclaredMethods": "System.DirectoryServices.ActiveDirectoryRights get_ActiveDirectoryRights() System.DirectoryServices.ActiveDirectorySecurityInheritance get_InheritanceType()", "DeclaredNestedTypes": "", "DeclaredProperties": "System.DirectoryServices.ActiveDirectoryRights ActiveDirectoryRights System.DirectoryServices.ActiveDirectorySecurityInheritance InheritanceType", "ImplementedInterfaces": "", "TypeInitializer": null, "IsNested": false, "Attributes": 1048577, "IsVisible": true, "IsNotPublic": false, "IsPublic": true, "IsNestedPublic": false, "IsNestedPrivate": false, "IsNestedFamily": false, "IsNestedAssembly": false, "IsNestedFamANDAssem": false, "IsNestedFamORAssem": false, "IsAutoLayout": true, "IsLayoutSequential": false, "IsExplicitLayout": false, "IsClass": true, "IsInterface": false, "IsValueType": false, "IsAbstract": false, "IsSealed": false, "IsSpecialName": false, "IsImport": false, "IsSerializable": false, "IsAnsiClass": true, "IsUnicodeClass": false, "IsAutoClass": false, "IsArray": false, "IsByRef": false, "IsPointer": false, "IsPrimitive": false, "IsCOMObject": false, "HasElementType": false, "IsContextful": false, "IsMarshalByRef": false, "GenericTypeArguments": "", "CustomAttributes": "" }, "AreAccessRulesProtected": false, "AreAuditRulesProtected": false, "AreAccessRulesCanonical": true, "AreAuditRulesCanonical": true }, "ObjectCategory": "CN=Person,CN=Schema,CN=Configuration,DC=testdhcp2,DC=local", "ObjectGUID": "4bde3f8d-8e9e-4ded-9d71-126ba9cd1300", "objectSid": { "BinaryLength": 28, "AccountDomainSid": { "BinaryLength": 24, "AccountDomainSid": "S-1-2-3", "Value": "S-1-2-3" }, "Value": "S-1-2-3-4000m" }, "Office": "db office", "OfficePhone": "91-123456789", "Organization": null, "OtherName": null, "pager": "234567890", "PasswordExpired": false, "PasswordLastSet": "\\/Date(1631174951326)\\/", "PasswordNeverExpires": false, "PasswordNotRequired": false, "physicalDeliveryOfficeName": "db office", "POBox": "dummy", "PostalCode": "380015", "postOfficeBox": [ "dummy" ], "PrimaryGroup": "CN=Domain Users,CN=Users,DC=testdhcp2,DC=local", "primaryGroupID": 513, "PrincipalsAllowedToDelegateToAccount": [], "ProfilePath": null, "ProtectedFromAccidentalDeletion": false, "pwdLastSet": 132756485513268133, "sAMAccountType": 805306368, "ScriptPath": null, "sDRightsEffective": 15, "ServicePrincipalNames": [], "SIDHistory": [], "SmartcardLogonRequired": false, "sn": "itadmin", "st": "Gujarat", "State": "Gujarat", "StreetAddress": "1,user street ,dummy,dummy", "telephoneNumber": "91-123456789", "Title": "it admin", "TrustedForDelegation": false, "TrustedToAuthForDelegation": false, "UseDESKeyOnly": false, "userAccountControl": 1049088, "userCertificate": [], "userParameters": null, "uSNChanged": 57594, "uSNCreated": 32800, "whenChanged": "\\/Date(1631277960000)\\/", "whenCreated": "\\/Date(1628229355000)\\/", "wWWHomePage": "www.test.com" }
Riferimento alla mappatura dei campi: campi dei log del dispositivo ai campi UDM
Questa sezione descrive in che modo il parser mappa i campi dei log originali ai campi del modello di dati unificato.
Riferimento alla mappatura dei campi: WINDOWS_AD
La tabella seguente elenca i campi del log del tipo di log WINDOWS_AD e i relativi campi UDM.
| Log field | UDM mapping | Logic |
|---|---|---|
|
metadata.entity_type |
If the ObjectClass log field value is equal to user or is empty, then the metadata.entity_type UDM field is set to USER. Else, if the ObjectClass log field value is equal to computer, then the metadata.entity_type UDM field is set to ASSET. |
ObjectGuid |
entity.user.product_object_id |
If the ObjectClass log field value is equal to user or is empty, then if the ObjectGuid log field value is not empty, then the ObjectGuid log field is mapped to the entity.user.product_object_id UDM field. Else, if the ObjectClass log field value is equal to computer, then if the ObjectGuid log field value is not empty, then the ObjectGuid log field is mapped to the entity.asset.product_object_id UDM field. |
whenCreated |
metadata.creation_timestamp |
If the ObjectClass log field value is equal to user or is empty, then if the whenCreated log field value is not empty, then when_created is extracted from the whenCreated log field using a Grok pattern, and mapped to the entity.asset.attribute.creation_time UDM field. Else, if the ObjectClass log field value is equal to computer, then if the whenCreated log field value is not empty, then when_created is extracted from the whenCreated log field using a Grok pattern, and mapped to the metadata.creation_timestamp UDM field. Else, timestamp tz_left tz_right is extracted from the whenCreated log field using a Grok pattern, and mapped to the entity.asset.attribute.creation_time UDM field. |
DisplayName |
entity.user.user_display_name |
If the ObjectClass log field value is equal to user or is empty, then if the DisplayName log field value is not empty, then the DisplayName log field is mapped to the entity.user.user_display_name UDM field. |
GivenName |
entity.user.first_name |
If the ObjectClass log field value is equal to user or is empty, then if the GivenName log field value is not empty, then the GivenName log field is mapped to the entity.user.first_name UDM field. |
SamAccountName |
entity.user.userid |
If the ObjectClass log field value is equal to user or is empty, then if the SamAccountName log field value is not empty, then the SamAccountName log field is mapped to the entity.user.userid UDM field. If the ObjectClass log field value is equal to computer, then the SamAccountName log field is mapped to the entity.asset.asset_id UDM field. |
EmployeeID |
entity.user.employee_id |
If the EmployeeID log field value is not empty, then the EmployeeID log field is mapped to the entity.user.employee_id UDM field.Else the employeeID.0 log field is mapped to the entity.user.employee_id UDM field. |
Title |
entity.user.title |
If the Title log field value is not empty, then the Title log field is mapped to the entity.user.title UDM field. |
Surname |
entity.user.last_name |
If the ObjectClass log field value is equal to user or is empty, then if the Surname log field value is not empty, then if the sn log field is mapped to the entity.user.last_name UDM field. Else if Surname log field value is not empty, then the Surname log field is mapped to the entity.user.last_name UDM field. |
Company |
entity.user.company_name |
If the ObjectClass log field value is equal to user or is empty, then if the Company log field value is not empty, then the Company log field is mapped to the entity.user.company_name UDM field. |
City |
entity.user.personal_address.city |
If the ObjectClass log field value is equal to user or is empty, then if the City log field value is not empty, then the City log field is mapped to the entity.user.personal_address.city UDM field. |
Department |
entity.user.department |
If the ObjectClass log field value is equal to user or is empty, then if the Department log field value is not empty, then the Department log field is mapped to the entity.user.department UDM field. |
|
entity.user.email_addresses |
If the ObjectClass log field value is equal to user or is empty, then if the EmailAddress log field value is not empty, then the EmailAddress log field is mapped to the entity.user.email_addresses UDM field. Else, if the mail log field value is not empty, then the mail log field is mapped to the entity.user.email_addresses UDM field. |
HomePhone |
entity.user.phone_numbers |
If the ObjectClass log field value is equal to user or is empty, then if the HomePhone log field value is not empty, then the HomePhone log field is mapped to the entity.user.phone_numbers UDM field. Else if the telephoneNumber log field value is not empty, then the telephoneNumber log field is mapped to the entity.user.phone_numbers UDM field.
If the ObjectClass log field value is equal to user or is empty, then if the MobilePhone log field value is not empty, then the MobilePhone log field is mapped to the entity.user.phone_numbers UDM field.
If the ObjectClass log field value is equal to user or is empty, then if the otherMobile log field value is not empty, then the otherMobile log field is mapped to the entity.user.phone_numbers UDM field. |
StreetAddress |
entity.user.personal_address.name |
If the ObjectClass log field value is equal to user or is empty, then if the StreetAddress log field value is not empty, then the StreetAddress log field is mapped to the entity.user.personal_address.name UDM field. |
State |
entity.user.personal_address.state |
If the ObjectClass log field value is equal to user or is empty, then if the State log field value is not empty, then the State log field is mapped to the entity.user.personal_address.state UDM field. |
Country |
entity.user.personal_address.country_or_region |
If the ObjectClass log field value is equal to user or is empty, then if the Country log field value is not empty, then the Country log field is mapped to the entity.user.personal_address.country_or_region UDM field. |
Office |
entity.user.office_address.name |
If the ObjectClass log field value is equal to user or is empty, then if the Office log field value is not empty, then the Office log field is mapped to the entity.user.office_address.name UDM field. |
HomeDirectory |
entity.file.full_path |
If the ObjectClass log field value is equal to user or is empty, then if the HomeDirectory log field value is not empty, then the HomeDirectory log field is mapped to the entity.file.full_path UDM field. |
|
entity.user.managers.user_display_name |
If the ObjectClass log field value is equal to user or is empty, then if the Manager log field value is not empty, then manager_name is extracted from the Manager log field using a Grok pattern, and mapped to the entity.user.managers.user_display_name UDM field. |
|
entity.user.windows_sid |
If the SID.Value log field value is not empty, then the SID.Value field is mapped to the entity.user.windows_sid UDM field.Else, if the objectSid log field value is not empty, then the objectSid field is mapped to the entity.user.windows_sid UDM field.If the ObjectClass log field value is equal to user or is empty, then if the Manager log field value is not empty, then if Manager matches the regular expression pattern (S-\d-(\d+-){1,14}\d+), then the Manager log field is mapped to the entity.user.managers.windows_sid UDM field. Else, the Manager log field is mapped to the entity.user.managers.userid UDM field. |
|
relations.relationship |
If the ObjectClass log field value is equal to user or is empty, then if the MemberOf log field value is not empty, then for index in MemberOf, the relations.relationship UDM field is set to MEMBER. Else, if the ObjectClass log field value is equal to computer, then if the ManagedBy log field value is not empty, then the relations.relationship UDM field is set to ADMINISTERS.If the PrimaryGroup log field value is not empty, then group_name is extracted from the PrimaryGroup log field using a Grok pattern, if the group_name extracted field value is not empty, then the relations.relationship UDM field is set to MEMBER. |
|
relations.entity.group.group_display_name |
If the ObjectClass log field value is equal to user or is empty, then if the MemberOf log field value is not empty, then for index in MemberOf, group_name is extracted from the index using a Grok pattern and mapped to the relations.entity.group.group_display_name UDM field. If the PrimaryGroup log field value is not empty, then group_name is extracted from the PrimaryGroup log field using a Grok pattern and mapped to the relations.entity.group.group_display_name UDM field. |
|
relations.entity_type |
If the ObjectClass log field value is equal to user or is empty, then if the MemberOf log field value is not empty, then for index in MemberOf, the relations.entity_type UDM field is set to GROUP. Else, if the ObjectClass log field value is equal to computer, then if the ManagedBy log field value is not empty, then the relations.entity_type UDM field is set to ASSET.If the PrimaryGroup log field value is not empty, then group_name is extracted from the PrimaryGroup log field using a Grok pattern, if the group_name extracted field value is not empty, then the relations.entity_type UDM field is set to GROUP. |
|
relations.direction |
If the ObjectClass log field value is equal to user or is empty, then if the MemberOf log field value is not empty, then for index in MemberOf, the relations.direction UDM field is set to UNIDIRECTIONAL. Else, if the ObjectClass log field value is equal to computer, then if the ManagedBy log field value is not empty, then the relations.direction UDM field is set to UNIDIRECTIONAL.If the PrimaryGroup log field value is not empty, then group_name is extracted from the PrimaryGroup log field using a Grok pattern, if the group_name extracted field value is not empty, then the relations.direction UDM field is set to UNIDIRECTIONAL. |
|
relations.entity.user.user_display_name |
If the ObjectClass log field value is equal to computer, then if the ManagedBy log field value is not empty, then user_name is extracted from the ManagedBy log field using a Grok pattern and mapped to the relations.entity.user.user_display_name UDM field. |
proxyAddresses |
entity.user.group_identifiers |
If the ObjectClass log field value is equal to user or is empty, then for index in proxyAddresses the index is mapped to entity.user.group_identifiers UDM field. |
|
entity.user.attribute.labels[Bad Password Count] |
If the ObjectClass log field value is equal to user or is empty, then if the badPwdCount log field value is not empty, then the entity.user.attribute.labels.key UDM field is set to Bad Password Count and the badPwdCount log field is mapped to the entity.user.attribute.labels.value UDM field. |
LastBadPasswordAttempt |
entity.user.last_bad_password_attempt_time |
If the ObjectClass log field value is equal to user or is empty, then if the LastBadPasswordAttempt log field value is not empty, then last_bad_password_attempt is extracted from the LastBadPasswordAttempt log field using a Grok pattern and mapped to the entity.user.last_bad_password_attempt_time UDM field. Else, if the ObjectClass log field value is equal to computer, then last_bad_password_attempt is extracted from the LastBadPasswordAttempt log field using a Grok pattern and mapped to the entity.user.last_bad_password_attempt_time UDM field. |
AccountExpirationDate |
entity.user.account_expiration_time |
If the ObjectClass log field value is equal to user or is empty, then if the AccountExpirationDate log field value is not empty, then account_expiration_date is extracted from the AccountExpirationDate log field using a Grok pattern and mapped to the entity.user.account_expiration_time UDM field. Else, if the ObjectClass log field value is equal to computer, then if the AccountExpirationDate log field value is not empty, then account_expiration_date is extracted from the AccountExpirationDate log field using a Grok pattern and mapped to the entity.user.account_expiration_time UDM field. |
PasswordLastSet |
entity.user.last_password_change_time |
If the ObjectClass log field value is equal to user or is empty, then if the PasswordLastSet log field value is not empty, then password_last_set is extracted from the PasswordLastSet log field using a Grok pattern and mapped to the entity.user.last_password_change_time UDM field. Else, if the ObjectClass log field value is equal to computer, then if the PasswordLastSet log field value is not empty, then password_last_set is extracted from the PasswordLastSet log field using a Grok pattern and mapped to the entity.user.last_password_change_time UDM field. |
PasswordNotRequired |
entity.user.attribute.labels[Password Not Required] |
If the ObjectClass log field value is equal to user or is empty, then if the PasswordNotRequired log field value is not empty, then the PasswordNotRequired log field is mapped to the entity.user.attribute.labels.value UDM field. If the ObjectClass log field value is equal to computer, then if the PasswordNotRequired log field value is not empty, then the PasswordNotRequired log field is mapped to the entity.asset.attribute.labels.value UDM field. |
ServicePrincipalNames |
entity.user.attribute.labels[Service Principal Names] |
If the ObjectClass log field value is equal to user or is empty, then if ServicePrincipalNames log field value is not empty, then for index in ServicePrincipalNames the index is mapped to the entity.user.attribute.labels.value UDM field.Else, if the ObjectClass log field value is equal to computer, then if ServicePrincipalNames log field value is not empty, then for index in ServicePrincipalNames, if index is equal to 0, then the index is mapped to the entity.user.attribute.labels.value UDM field. |
AccountLockoutTime |
entity.user.account_lockout_time |
If the ObjectClass log field value is equal to user or is empty, then if the AccountLockoutTime log field value is not empty, then account_lockout_time is extracted from the AccountLockoutTime log field using a Grok pattern and mapped to the entity.user.account_lockout_time UDM field. Else, if the ObjectClass log field value is equal to computer, then if the AccountLockoutTime log field value is not empty, then account_lockout_time is extracted from the AccountLockoutTime log field using a Grok pattern and mapped to the entity.user.account_lockout_time UDM field. |
whenChanged |
entity.asset.attribute.last_update_time |
If the ObjectClass log field value is equal to computer, then when_changed is extracted from the whenChanged log field using a Grok pattern, if whenChanged is not empty, then when_changed is mapped to the entity.asset.attribute.last_update_time UDM field.Else, timestamp and timezone is extracted from whenChanged log field using a Grok pattern and tz_left and tz_right is extracted from the timezone using a Grok pattern and timestamp tz_left tz_right is mapped to entity.asset.attribute.creation_time UDM field. |
DNSHostName |
entity.asset.hostname |
If the ObjectClass log field value is equal to computer, then if the DNSHostName log field value is not empty, then the DNSHostName log field is mapped to the entity.asset.hostname UDM field. |
countryCode |
entity.asset.location.country_or_region |
If the ObjectClass log field value is equal to computer, then if the countryCode log field value is not empty, then the countryCode log field is mapped to the entity.asset.location.country_or_region UDM field. |
|
entity.asset.platform_software.platform |
If the ObjectClass log field value is equal to computer, then if the OperatingSystem log field value is not empty, then if the OperatingSystem log field value matches the regular expression pattern (?i)windows, then the entity.asset.platform_software.platform UDM field is set to WINDOWS.Else, if the OperatingSystem log field value matches the regular expression pattern (?i)mac or the OperatingSystem log field value matches the regular expression pattern (?i)osx, then the entity.asset.platform_software.platform UDM field is set to MAC.Else, if the OperatingSystem log field value matches the regular expression pattern (?i)linux, then the entity.asset.platform_software.platform UDM field is set to LINUX. |
OperatingSystemVersion |
entity.asset.platform_software.platform_version |
If the ObjectClass log field value is equal to computer, then if the OperatingSystem log field value is not empty, then if the OperatingSystemVersion log field value is not empty, then OperatingSystem - OperatingSystemVersion is mapped to the entity.asset.platform_software.platform_version UDM field.Else if the OperatingSystemVersion log field value is not empty, then the OperatingSystemVersion log field is mapped to the entity.asset.platform_software.platform_version UDM field. |
OperatingSystemServicePack |
entity.asset.platform_software.platform_patch_level |
If the ObjectClass log field value is equal to computer, then if the OperatingSystemServicePack log field value is not empty, then the OperatingSystemServicePack log field is mapped to the entity.asset.platform_software.platform_patch_level UDM field. |
IPv4Address |
entity.asset.ip |
If the ObjectClass log field value is equal to computer, then if the IPv4Address log field value is not empty, then the IPv4Address log field is mapped to the entity.asset.ip UDM field. |
IPv6Address |
entity.asset.ip |
If the ObjectClass log field value is equal to computer, then if the IPv6Address log field value is not empty, then the IPv6Address log field is mapped to the entity.asset.ip UDM field. |
Location |
entity.asset.location.name |
If the ObjectClass log field value is equal to computer, then if the Location log field value is not empty, then the Location log field is mapped to the entity.asset.location.name UDM field. |
ObjectCategory |
entity.asset.category |
If the ObjectClass log field value is equal to computer, then if the ObjectCategory log field value is not empty, then object_category is extracted from the ObjectCategory log field using a Grok pattern, and mapped to the entity.asset.category UDM field. |
PasswordExpired |
entity.asset.attribute.labels[Password Expired] |
If the ObjectClass log field value is equal to computer, then if the PasswordExpired log field value is not empty, then the PasswordExpired log field is mapped to the entity.asset.attribute.labels.value UDM field.If the ObjectClass log field value is equal to user or is empty, then if the PasswordExpired log field value is not empty, then the PasswordExpired log field is mapped to the entity.user.attribute.labels.value UDM field. |
PasswordNeverExpires |
entity.asset.attribute.labels[Password Never Expires] |
If the ObjectClass log field value is equal to computer, then if the PasswordNeverExpires log field value is not empty, then the PasswordNeverExpires log field is mapped to the entity.asset.attribute.labels.value UDM field.If the ObjectClass log field value is equal to user or is empty, then if the PasswordNeverExpires log field value is not empty, then the PasswordNeverExpires log field is mapped to the entity.user.attribute.labels.value UDM field. |
|
entity.user.attribute.labels[Last Logon] |
If the ObjectClass log field value is equal to user or is empty, then if the lastLogon log field value is not equal to 0, then the entity.user.attribute.labels.key UDM field is set to Last Logon and the lastLogon log field is mapped to the entity.user.attribute.labels.value UDM field. If the ObjectClass log field value is equal to computer, then if the lastLogon log field value is not equal to 0, then the entity.asset.attribute.labels.key UDM field is set to Last Logon and the lastLogon log field is mapped to the entity.asset.attribute.labels.value UDM field. |
lastLogoff |
entity.asset.attribute.labels[Last Logoff] |
If the ObjectClass log field value is equal to computer, then if the lastLogoff log field value does not contain one of the following values, then the lastLogoff log field is mapped to the entity.asset.attribute.labels.value UDM field.
|
LastLogonDate |
entity.user.last_login_time |
If the ObjectClass log field value is equal to user or is empty, then if the LastLogonDate log field value is not empty, then last_logon_date is extracted from the LastLogonDate log field using a Grok pattern, and mapped to the entity.user.last_login_time UDM field.Else if the ObjectClass log field value is equal to computer,then if the LastLogonDate log field value is not empty, then last_logon_date is extracted from the LastLogonDate log field using a Grok pattern, and mapped to the entity.user.last_login_time UDM field. |
HomePage |
entity.url |
If the HomePage log field value is not empty, then the HomePage log field is mapped to the entity.url UDM field. |
|
entity.administrative_domain |
If the CanonicalName log field value is not empty, then domain_name is extracted from the CanonicalName log field using a Grok pattern, and mapped to the entity.administrative_domain UDM field. |
|
metadata.vendor_name |
The metadata.vendor_name UDM field is set to Microsoft. |
|
metadata.product_name |
The metadata.product_name UDM field is set to Windows Active Directory. |
Description |
metadata.description |
The Description log field is mapped to the metadata.description UDM field. |
Hai bisogno di ulteriore assistenza? Ricevi risposte dai membri della community e dai professionisti di Google SecOps.

