이 문서에서는 Intune 데이터를 사용하여 기기 기반 커스텀 액세스 수준을 만들고 이 액세스 수준을 조직 리소스에 할당하는 방법을 보여줍니다.
시작하기 전에
- Microsoft Intune과의 Chrome Enterprise Premium 통합 설정
- Chrome Enterprise Premium의 유료 구독인 Chrome Enterprise Premium으로 업그레이드합니다. 업그레이드하려면 영업팀에 문의하세요.
- 다음 Identity and Access Management 역할 중 하나가 있는지 확인합니다.
- Access Context Manager 관리자(
roles/accesscontextmanager.policyAdmin) - Access Context Manager 편집자(
roles/accesscontextmanager.policyEditor)
- Access Context Manager 관리자(
- 커스텀 액세스 수준의 Common Expression Language (CEL) 표현식을 빌드하는 데 사용되는 객체 및 속성을 이해합니다. 자세한 내용은 커스텀 액세스 수준 사양을 참조하세요.
커스텀 액세스 수준 만들기
하나 이상의 조건을 사용하여 액세스 수준을 만들 수 있습니다. 사용자의 기기가 여러 조건 (조건의 논리적 AND)을 충족하도록 하려면 모든 필수 조건이 포함된 액세스 수준을 만듭니다.
Intune에서 제공하는 데이터를 사용하여 새 커스텀 액세스 수준을 만들려면 다음 안내를 따르세요.
Google Cloud 콘솔에서 Access Context Manager 페이지로 이동합니다.
Access Context Manager로 이동- 메시지가 표시되면 조직을 선택합니다.
- Access Context Manager 페이지에서 새로 만들기를 클릭합니다.
- 새 액세스 수준 창에서 다음을 입력합니다.
- 액세스 수준 제목 필드에 액세스 수준의 제목을 입력합니다. 제목은 최대 50자여야 하고 문자로 시작해야 하며 숫자, 문자, 밑줄, 공백만 포함할 수 있습니다.
- 조건 만들기 섹션에서 고급 모드를 선택합니다.
- 조건 섹션에서 커스텀 액세스 수준의 표현식을 입력합니다. 조건은 단일 불리언 값으로 평가해야 합니다.
CEL 표현식에 사용할 수 있는 Intune 필드를 찾으려면 기기에 대해 수집된 Intune 데이터를 검토하세요.
예시다음 CEL 표현식은 호환되는 Intune 관리 기기에서만 액세스를 허용하는 규칙을 만듭니다.
device.vendors["Intune"].is_managed_device == true && device.vendors["Intune"].data["complianceState"] == "compliant"
다음 CEL 표현식은 이전 3일 동안 Intune에서 동기화한 기기에서만 액세스를 허용하는 규칙을 만듭니다.
lastSyncDateTime필드는 Intune에서 제공됩니다.request.time - timestamp(device.vendors["Intune"].data["lastSyncDateTime"]) < duration("72h")Common Expression Language(CEL) 지원 및 커스텀 액세스 수준에 대한 예시와 자세한 내용은 커스텀 액세스 수준 사양을 참조하세요.
- 저장을 클릭합니다.
커스텀 액세스 수준 할당
커스텀 액세스 수준을 할당하여 애플리케이션에 대한 액세스를 제어할 수 있습니다. 이러한 애플리케이션에는 Google Workspace 앱과 Google Cloud 의 IAP(Identity-Aware Proxy)로 보호되는 애플리케이션(IAP 보안 리소스라고도 함)이 포함됩니다. 앱에 하나 이상의 액세스 수준을 할당할 수 있습니다. 여러 액세스 수준을 선택한 경우 사용자의 기기는 앱에 대한 액세스 권한이 부여된 액세스 수준 중 하나의 조건만 충족하면 됩니다.
Google Workspace 애플리케이션에 대한 커스텀 액세스 수준 할당
Google Workspace 관리 콘솔에서 Google Workspace 애플리케이션에 대한 액세스 수준을 할당합니다.
관리 콘솔 홈페이지에서 보안 > 컨텍스트 인식 액세스로 이동합니다.
컨텍스트 인식 액세스로 이동액세스 수준 할당을 클릭합니다.
앱 목록이 표시됩니다.
- 조직 단위 섹션에서 조직 단위 또는 그룹을 선택합니다.
액세스 수준을 할당할 앱을 선택하고 할당을 클릭합니다.
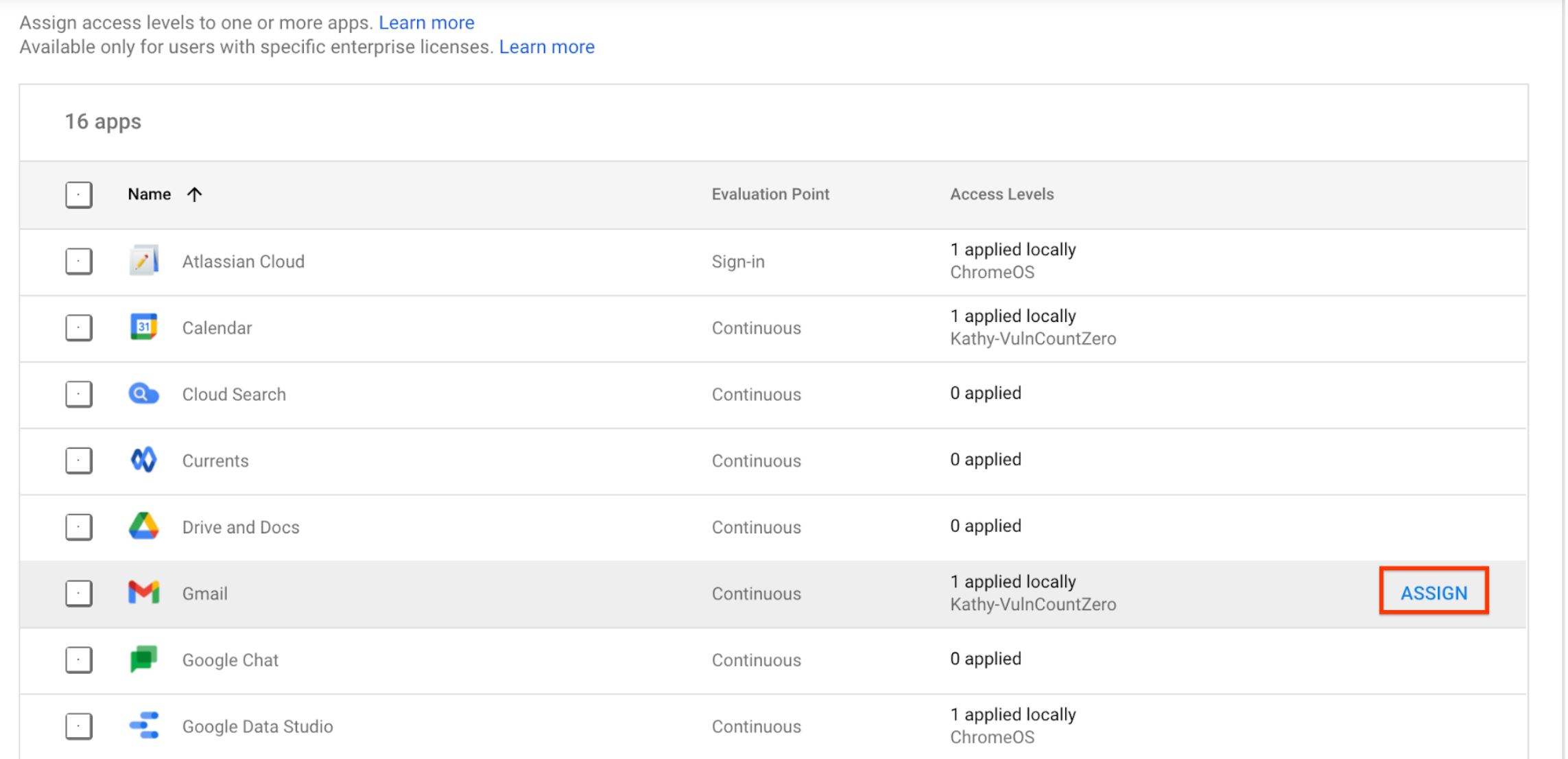
모든 액세스 수준 목록이 표시됩니다. 액세스 수준은 Google Workspace, Cloud ID, Google Cloud 간에 공유되는 리소스이므로 내가 만들지 않은 액세스 수준도 목록에 표시될 수 있습니다.
- 앱에 대한 액세스 수준을 하나 이상 선택합니다.
- 데스크톱 및 모바일 앱 (및 브라우저)의 사용자에게 액세스 수준을 적용하려면 Google 데스크톱 및 모바일 앱에 적용을 선택합니다. 이 체크박스는 기본 제공 앱에만 적용됩니다.
- 저장을 클릭합니다. 액세스 수준 이름은 앱 옆에 있는 할당된 액세스 수준 목록에 표시됩니다.
IAP 보안 리소스에 대한 커스텀 액세스 수준 할당
Google Cloud 콘솔에서 IAP 보안 리소스에 대해 액세스 수준을 할당하려면 IAP 보안 리소스에 액세스 수준 적용의 안내를 따르세요.

