Internet-facing application delivery: Networking Architecture
Ammett Williams
Developer Relations Engineer
Exposing your applications to the internet is a common requirement for enterprises. In this article we would be looking at internet facing application delivery. This references information from the document Networking for internet-facing applications: Reference architecture which should be read for more detail.
Internet facing applications
Any application meant to be used by people on the internet needs to be built for high availability, wide consumption and tight security. Services and web-apps need to be built so they can be protected as they scale.
Google Cloud has several services to help you add security controls to your external facing application.
The Edge - Cloud Armor provides WAF and DDoS protection, Load Balancers give you a single IP to expose your services.
In region - Network Virtual Appliances such as Next Generation Firewalls can be used to inspect traffic and Network Firewall policies can be used to control access to your resources.
Other services - Cloud IDS (Cloud Intrusion Detection System) can detect threats in both East West and North South traffic flows.
Networking internet-facing applications
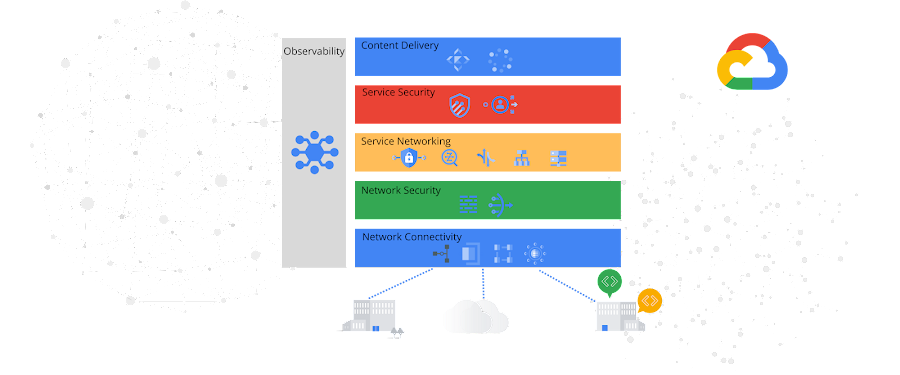
The document Networking for internet-facing applications: Reference architecture explores several patterns grouped as follows:
We will explore two architectures under the hybrid service architecture group.
# 1 - Hybrid connectivity configuration using external Cloud Load Balancing and network edge services
Securing service access at the edge and distributing traffic to multiple sources can be achieved on Google Cloud. Some components involved in this design are Load balancers, Cloud CDN, Cloud Armor, Identity aware proxy, Google-managed SSL certificates and Network Endpoint Groups.
The design below shows Google Cloud frontend services, Load balancer and multiple backend sources.
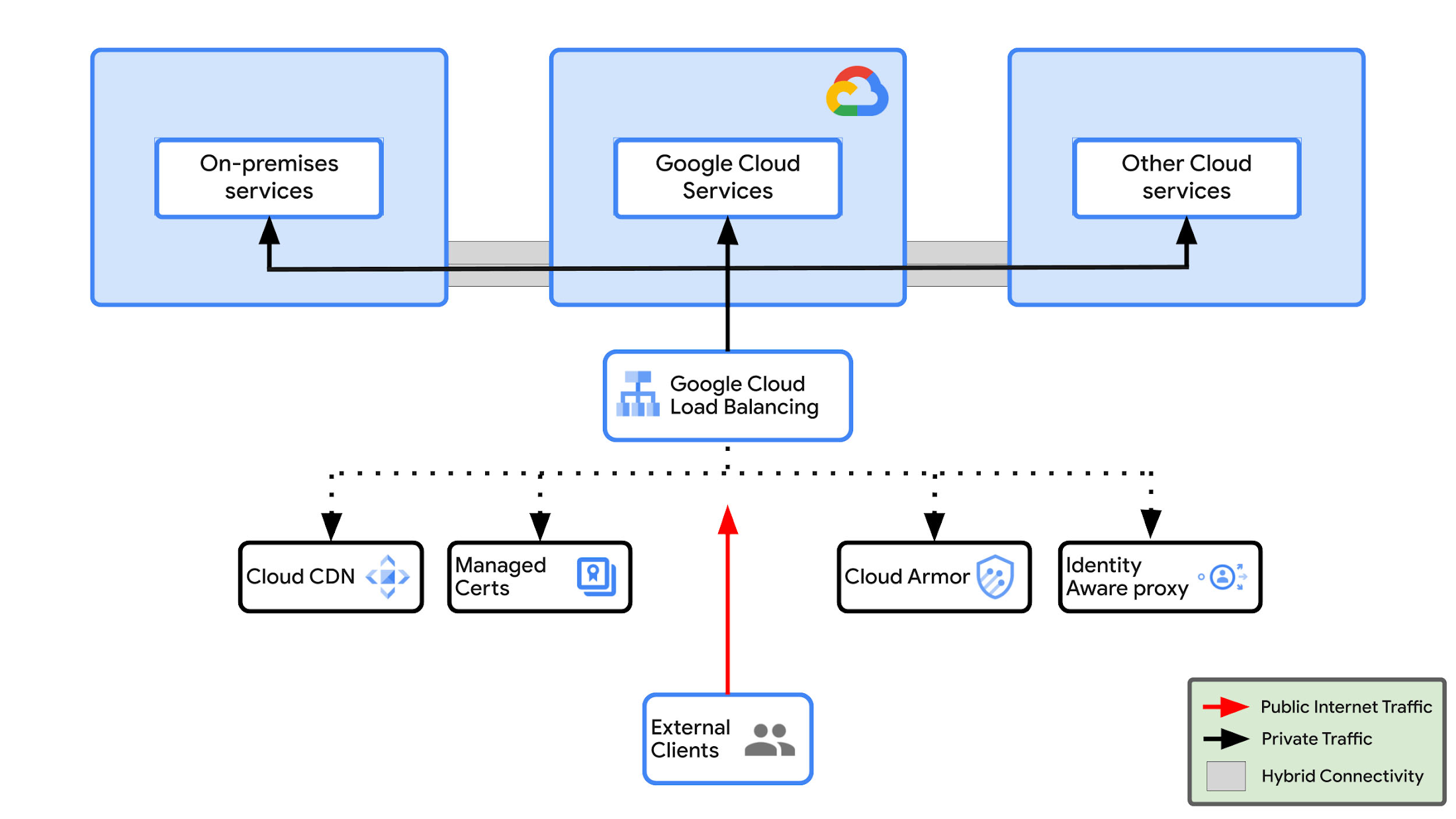
The design elements are as follows.
Edge services
Load balancer - Ingest traffic from external clients.
Cloud CDN - If there is static content and this feature is enabled, Cloud CDN caches content at a location closest to the user and serves it from there thereby reducing latency.
Managed certs - Helps you to manage your domains with Google-managed SSL certificates.
Cloud Armor - Provides protection against DDoS and OWASP top 10 protection.
Identity Aware-proxy - Allows access based on identity.
Backend
The backend resources selected will depend on the URL map configuration. Let's look at some backend types used here.
Managed Instance group - This could be used for Virtual machines resources within Google Cloud.
Hybrid Network endpoint groups (NEG) - These could be set up for on-premise and other cloud connections. Traffic to hybrid NEGs are routed over Cloud VPN, or interconnect connections.
# 2 - IDS traffic inspection
Intrusion Detection Systems (IDS) provide inspection of network traffic and visibility into possible suspicious activity. Cloud IDS is a Google Cloud service which meets this requirement.
The design below shows Cloud IDS providing traffic inspection of internet traffic.
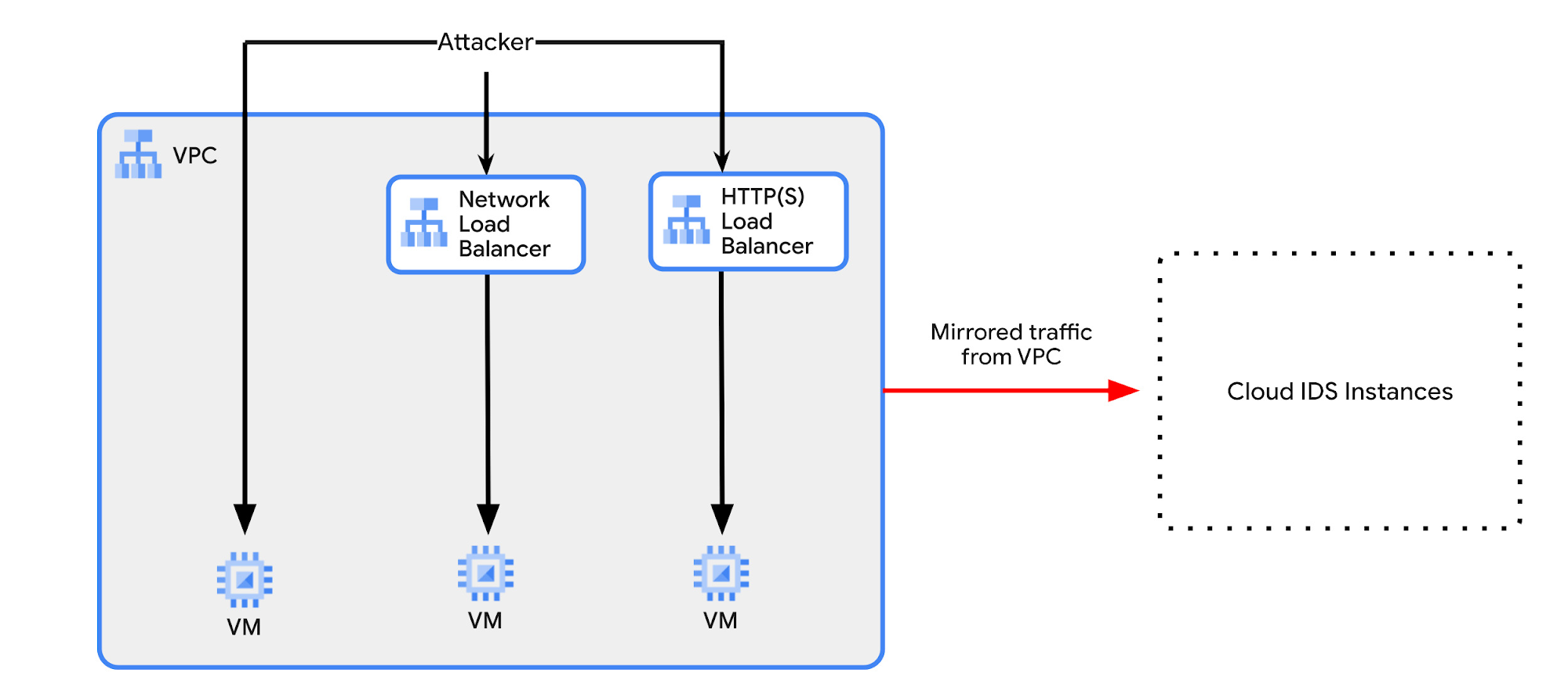
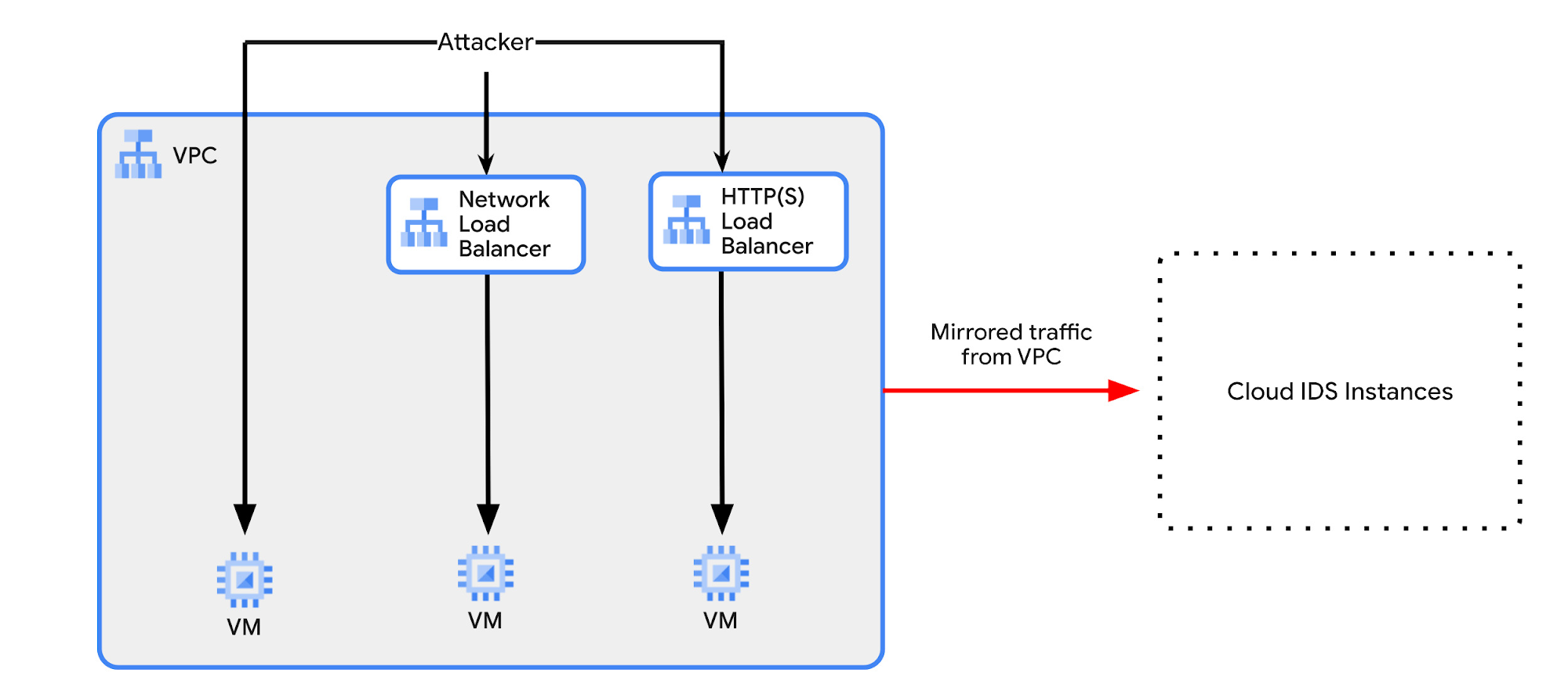
The design elements are as follows.
Front End.
Load Balancers - The design shows the use of both a regional Network load balancer for non HTTP(S) traffic and a global HTTP(S) load balancer. Traffic is directed to the IP’s of the load balancers to be distributed to the relevant backend resources.
External IP - There is also a VMs with an external IP address with firewall rules that allow access.
Cloud IDS.
For Cloud IDS to work the following is setup:
Service Networking, Cloud IDS APIs needs to be enabled.
Reservation of service IPs- A range of private IPs need to be allocated for services.
A private connection to the service producer has to be enabled. This creates a VPC network peering from the network to be monitored to the service network.
A Cloud IDS endpoint has to be set up in the region where traffic is to be monitored. You will add a Cloud IDS service profile and packet mirroring policy to the end point.
Traffic logs will be generated and can be viewed in the Cloud IDS console or in Cloud Logging.
You can get a hands-on introduction lab at the skillsboost site. Cloud IDS: Qwik Start.
Overall this design gives visibility into internet traffic and also internal traffic for (threat intrusion detection, malware, spyware, and command-and-control attacks) and can help meet certain compliance requirements for an organization.
More on architecture
Previous blogs on this topic 6 building blocks for cloud networking and two network patterns for secure intra-area access are very good to explore. Also, I recommend reading the following documents:
Documentation: Networking for secure intra-cloud access: Reference architectures
Documentation: Designing networks for migrating enterprise workloads: Architectural approaches
Documentation: Networking for hybrid and multi-cloud workloads: Reference architectures
Documentation: Hybrid connectivity network endpoint groups overview
Want to ask a question, find out more or share a thought? Please connect with me on Linkedin