Introducing new Cloud Armor features including rate limiting, adaptive protection, and bot defense
Shane Wang
Product Manager, Google Cloud
Navya Dwarakanath
Networking Specialist
As cyberattacks grow in complexity and intensity against cloud customers, they need their cloud providers to play an even more active role in the resiliency of their web applications and APIs. Attacks have evolved from isolated DDoS attempts to far more comprehensive and coordinated techniques, including volumetric flood DDoS attacks, bot attacks, and API abuse.
Google Cloud Armor can help our customers counter these growing security threats to web-applications and services by empowering defenders to deploy a defense-in-depth strategy.
Today, we are proud to announce the General Availability of new capabilities in Cloud Armor that can greatly improve the security, reliability, and availability of deployments, including:
Per-client rate limiting with two new rule actions: “throttle” and “rate_based_ban”;
Bot management with reCAPTCHA Enterprise; and
Machine learning-based Adaptive Protection to help counter advanced Layer 7 attacks
Also today, we are announcing the availability of new Cloud Armor features in Preview, including:
Updated preconfigured WAF rules based on CRS 3.3, and
Network-based threat intelligence to help block known bad traffic
These new capabilities help provide enterprise-ready DDoS protection and web application firewall (WAF) solutions at planet-scale for our customers’ workloads, be they located on-premises, in colocation, or in any public cloud.


"The risk of a malicious distributed denial of service attack is notoriously hard to mitigate for most organizations,” explained Chris Aitchison, CTO of Australia’s Up, with the highest rated banking app in Australia (4.6 on Google Play). “Google handles a significant amount of the world's internet traffic, and Up is extremely comfortable relying on Google Cloud Armor to give us world-class protection in this space."
Google Cloud Armor
Cloud Armor is the DDoS mitigation service and WAF that leverages Google’s planet-scale infrastructure to help protect your websites and applications from volumetric, protocol-based, and application-level DDoS attacks. Cloud Armor can also filter Layer 7 network traffic to mitigate OWASP Top 10 risks, whether the apps are deployed on Google Cloud, in hybrid environments, or in a multi-cloud architecture.
Rate limiting
Web applications are frequently targeted by high-volume L7 requests like HTTP floods with the intent to make target service unavailable, or by lower volume, abusive user behavior such as credential stuffing. To mitigate such attacks, customers often need to limit the rate of requests that their applications and services receive.
With Cloud Armor’s new rate limiting capability, customers can curtail traffic to backend resources based on request volume, and prevent unwelcome traffic from overconsuming resources or affecting service availability. When Cloud Armor users configure its rules at the edge of their network, it can enable them to protect their applications from unpredictably noisy clients.
In addition to providing the ability to rate limit web traffic, you also have the ability to rate limit at the connection level with Cloud Armor for TCP/SSL Proxy.
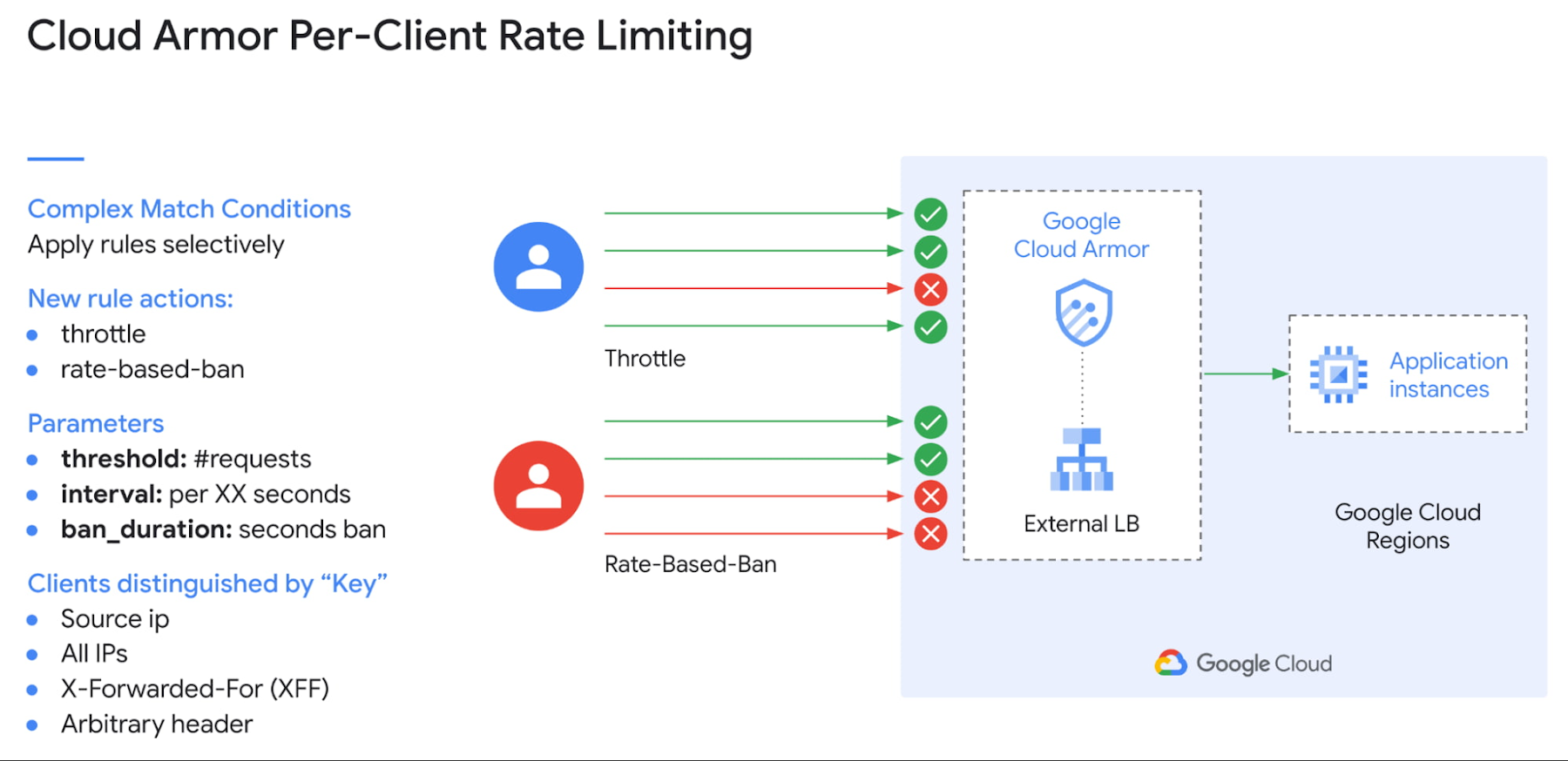
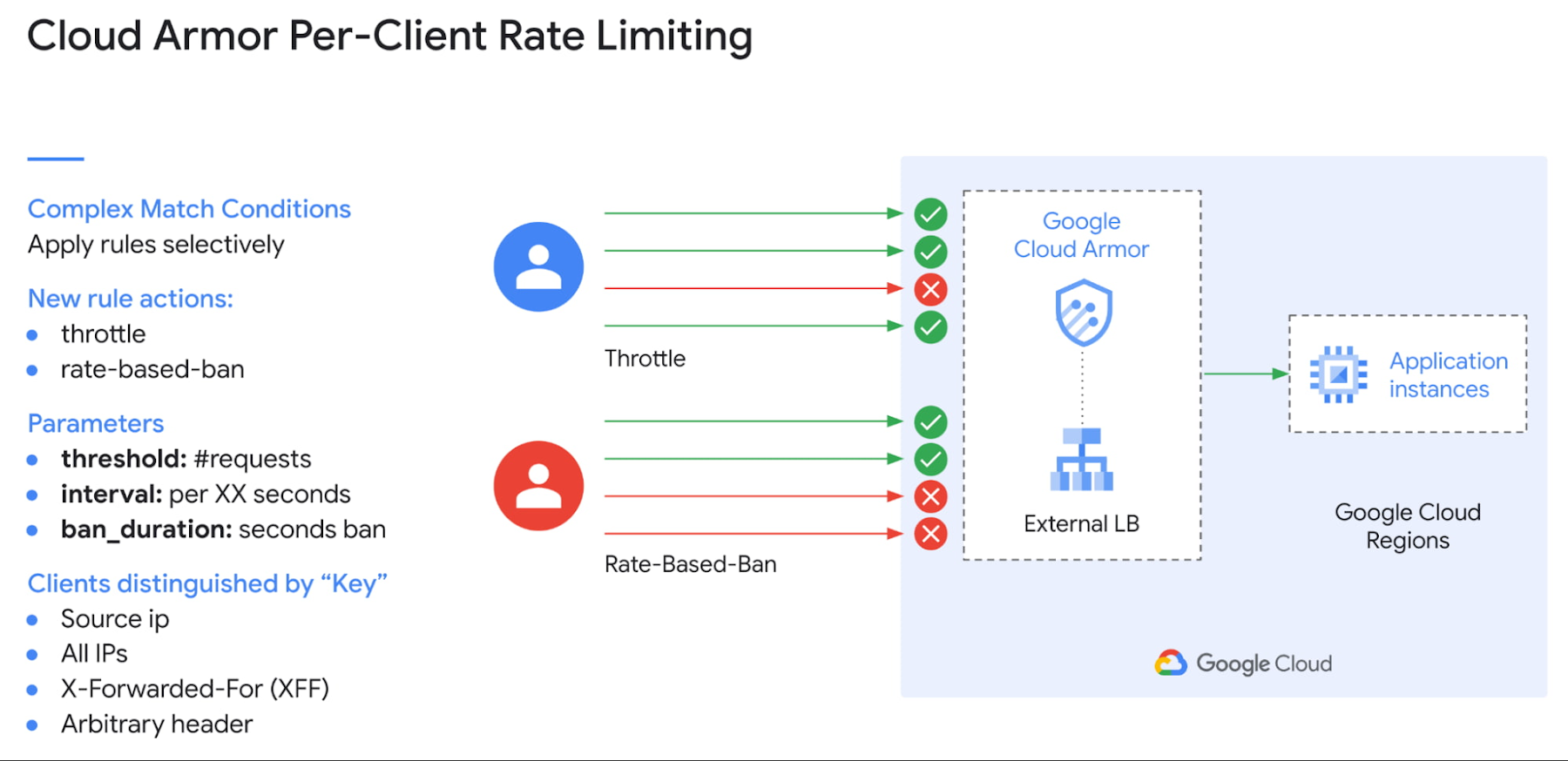
Figure 1. Cloud Armor Per-Client Rate Limiting
Google Cloud Armor has two type of rate-based rules:
Throttle: You can enforce a maximum request limit, or connection limits, per client by throttling individual clients to a user-configured threshold, or enforce a maximum request count across all clients based on a HTTP request property.
Rate-based ban: You can rate-limit requests or connections that match a rule on a per-client basis and then temporarily ban those clients for a configured period of time if they exceed the user-configured threshold.
Customers use Cloud Armor rate limiting to help prevent abusive behavior on a per-client basis such as brute force login attempts against their sites. Similarly, the rate limiting rules can be applied more narrowly using the CEL-based custom rules language to enforce different rate limits to, for example, different countries where they don’t have any (or many) customers, and use rate limiting to throttle those attacks.
Up’s security team created a monitoring and alerting system when they first deployed rate limiting protections, using Cloud Logging and Cloud Monitoring. "We use rate limiting with Cloud Armor in various parts of our platform and we have found it effective in identifying malicious clients and stopping them in their tracks," said Aitchison.
Cloud Armor Bot Management with reCAPTCHA Enterprise
Last fall, we announced the preview of Cloud Armor bot management with reCAPTCHA Enterprise. Now generally available, these new features in Cloud Armor can provide mitigation against bot attacks, credential stuffing, scraping, inventory hoarding attacks and other types of fraudulent transactions for our customers. This capability is powered by reCAPTCHA Enterprise with intelligence derived from more than 5 million websites running reCAPTCHA.
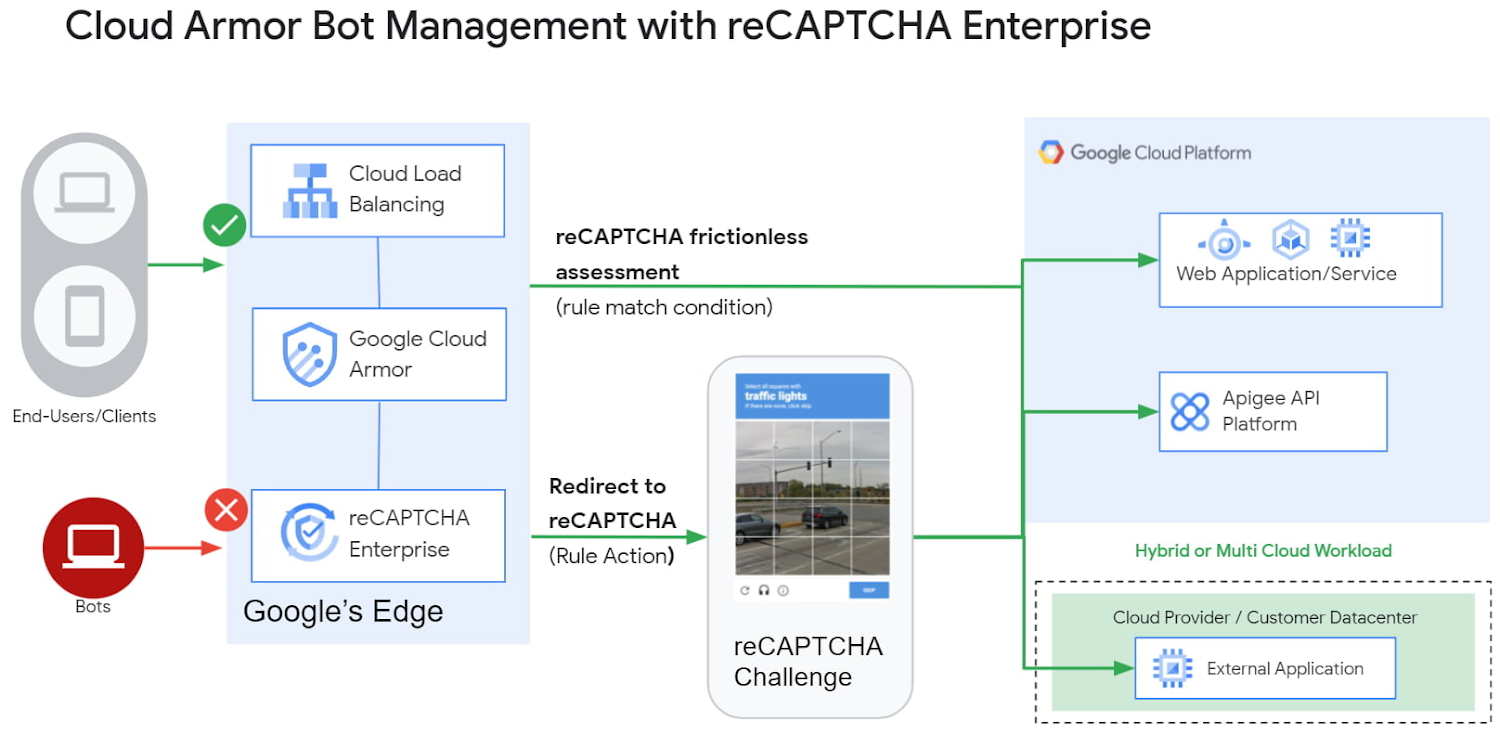
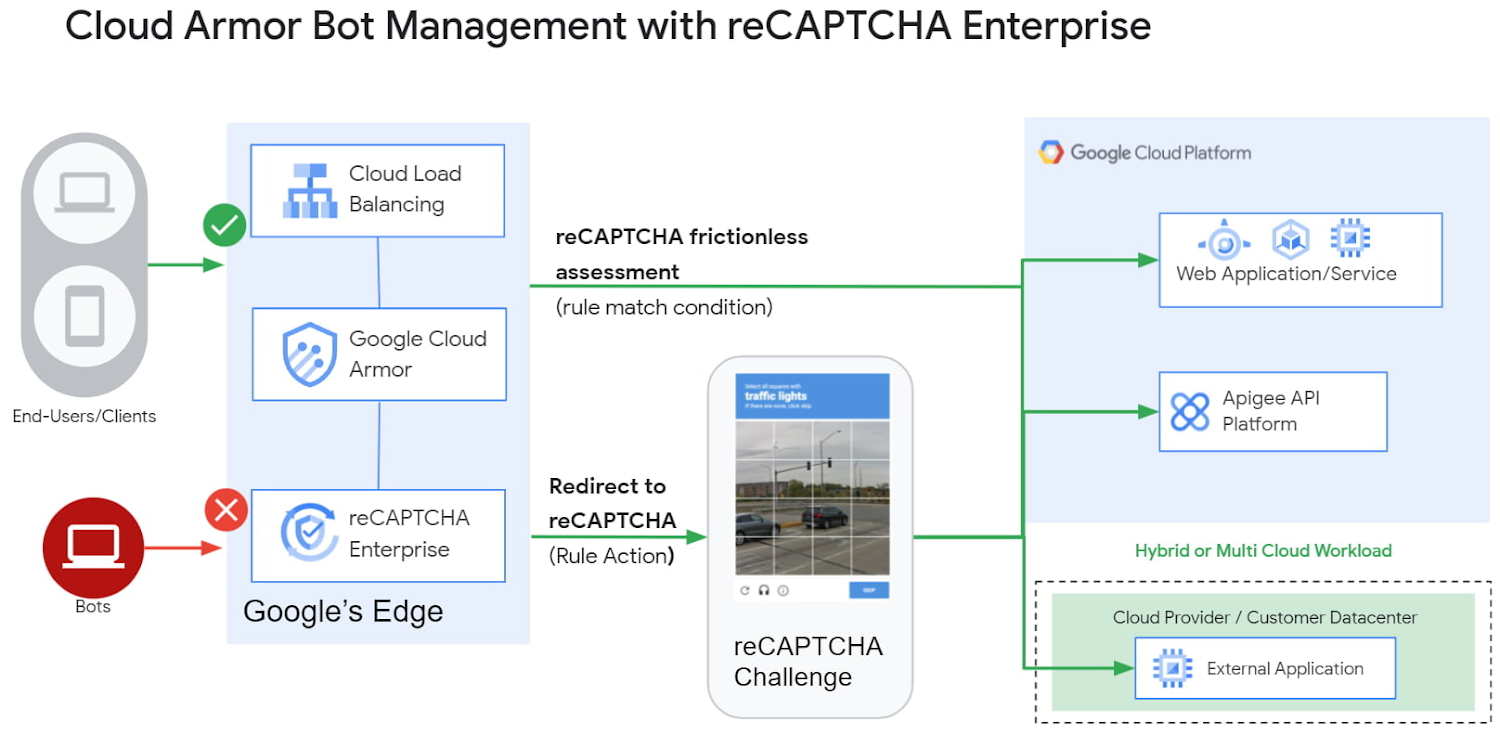
Figure 2. Cloud Armor Advanced Bot Management with reCAPTCHA Enterprise Integration
Our bot management solution integrates Cloud Armor and reCAPTCHA Enterprise to support several use cases. The first allows Cloud Armor to help enforce reCAPTCHA’s more “frictionless” assessment, as it’s referred to, where end users do not have to identify images or decipher text before proceeding on a web page. This assessment automatically deciphers the reCAPTCHA Enterprise token that can indicate if a bot is detected or suspected. Security teams can then create Cloud Armor rules to block access to or redirect suspected bots to alternate content based on the reCAPTCHA’s risk score.
The second use case is a more traditional manual challenge where Cloud Armor can serve a reCAPTCHA challenge to the user when they trigger a WAF rule. In this case, the end user would have to pass the challenge in order for their request to be allowed through to the target application. This method allows for a manual user challenge before their access is blocked, offering flexibility to Cloud Armor users to create their own reCAPTCHA WAF site key and train a security model specific to that key.
Finally, users can also combine both of the above use cases, the frictionless assessment and the manual challenge into the redemption flow. Cloud Armor policies can be configured to serve the manual challenge only to users that receive a high risk score from the reCAPTCHA frictionless assessment. This combination gives end-users the opportunity to redeem themselves by passing a manual challenge and getting through to the target application.
Updated Preconfigured WAF Rules can help mitigate OWASP Top 10
Cloud Armor now offers in preview new preconfigured WAF rules based on OWASP ModSecurity Core Rule Set (CRS) v3.3 in addition to the existing v3.0 rule sets to help our customers to mitigate the OWASP Top 10 vulnerabilities. With this preview release, customers are able to deploy the latest industry standard WAF signatures in Cloud Armor security policies to help selectively filter Layer7 traffic and protect their web apps and services from exploit attempts such as SQL injection (SQLi), cross-site scripting (XSS), or remote code execution (RCE). This predefined set of WAF rules allows customers to set a baseline level of protection for their public-facing endpoints. From there, they can use custom-defined WAF rules more specific to their web applications to further harden access and weed out unwanted connections.
One of Cloud Armor’s large enterprise customers has multiple platform teams, one for each major division. The team using Cloud Armor shared that its WAF defenses catch new threats and attacks before other security teams that aren’t using Cloud Armor, and sometimes even before they read about the indication of compromise in their threat intelligence feeds.
Google Cloud Threat Intelligence for Cloud Armor now in Preview
Another step we are making to empower a defense-in-depth strategy against common web application security threats is to introduce a preview release of Google Cloud Threat Intelligence for Cloud Armor. We heard from many of our customers that managing threat intelligence is becoming increasingly challenging due to the evolving nature of cybersecurity, and that’s why Cloud Armor now provides ready-to-use, continuously updated threat intelligence to help our customers enhance their network security.
With the new Google-curated Threat Intelligence, customers can configure security policies to filter traffic based on the following four categories: Tor exit nodes, malicious IPs, bad bots, and public cloud endpoints, with more categories planned in upcoming releases.
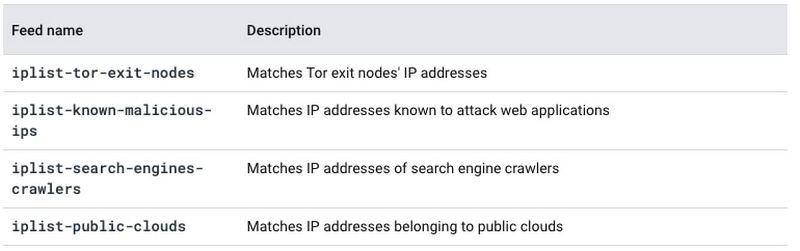
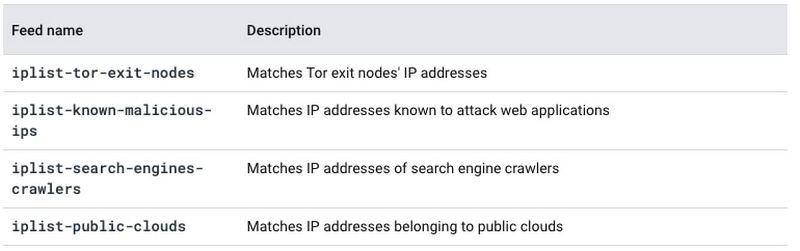
Figure3. Cloud Armor Network Threat Intelligence Categories
Cloud Armor Adaptive Protection
Generally available since December 2021, our machine learning-powered Cloud Armor Adaptive Protection can provide customers additional capability to detect and mitigate suspicious Layer 7 traffic to their applications and services in real-time, using Google’s machine learning technology. You can learn more about it in this blog and this video.


“Adaptive Protection alerts tell us exactly which one(s) of the dozens of attributes about an HTTP connection are out of bounds, and by how much relative to baseline traffic,” explained Fabio Coatti, Engineer at METRO Digital GmbH. "So far, the model has been very accurate, and our confidence in it continues to rise. This is key because mitigation can impact the experiences of legitimate customers. We want to ensure we act only on legitimate threats that might prevent our customers from using our portals.”
Cloud Armor Helps Mitigate a Wide Array of Threats
With all of the newly-added capabilities, Cloud Armor allows you to leverage the scale of Google’s global network while combining industry leading tools and tactics to help mitigate a wide array of threats to your internet-facing web applications and services.


"We're extremely conservative about the traffic that we allow to cross our network boundaries. Cloud Armor allows us to enforce strict restrictions on traffic coming in and out of our platform with a simplicity that we didn't previously realize was possible," said Up’s Aitchison. “When we need to implement international sanctions regarding access to our network, Google Cloud Armor makes this extremely simple for us."
In addition to advancing security capabilities, Cloud Amor recently expanded its workload coverage, further addressing CDN, Storage and additional Load Balancers, as you can read in this blog.
To learn more, explore the following resources:
Get better cost predictability and volume pricing, advanced features, and two additional support services with Cloud Armor Managed Protection Plus


