Protect your apps from bots with Cloud Armor and reCAPTCHA Enterprise
Emil Kiner
Senior Product Manager
Badr Salmi
Product Manager Lead, Web Risk, User Protection Services
Try Google Cloud
Start building on Google Cloud with $300 in free credits and 20+ always free products.
Free trialUnwelcome web traffic from bots has proliferated, becoming a significant contributor to business and operational risk. The motivations of bot controllers range from disruption of business through DDoS attacks to fraud such as credential stuffing, denial of inventory, scraping, and fraudulent card use. Google is well positioned to help detect and mitigate these risks by leveraging both our AI/ML strengths for combatting bot traffic as well as the global scale of our network to absorb even the largest threats.
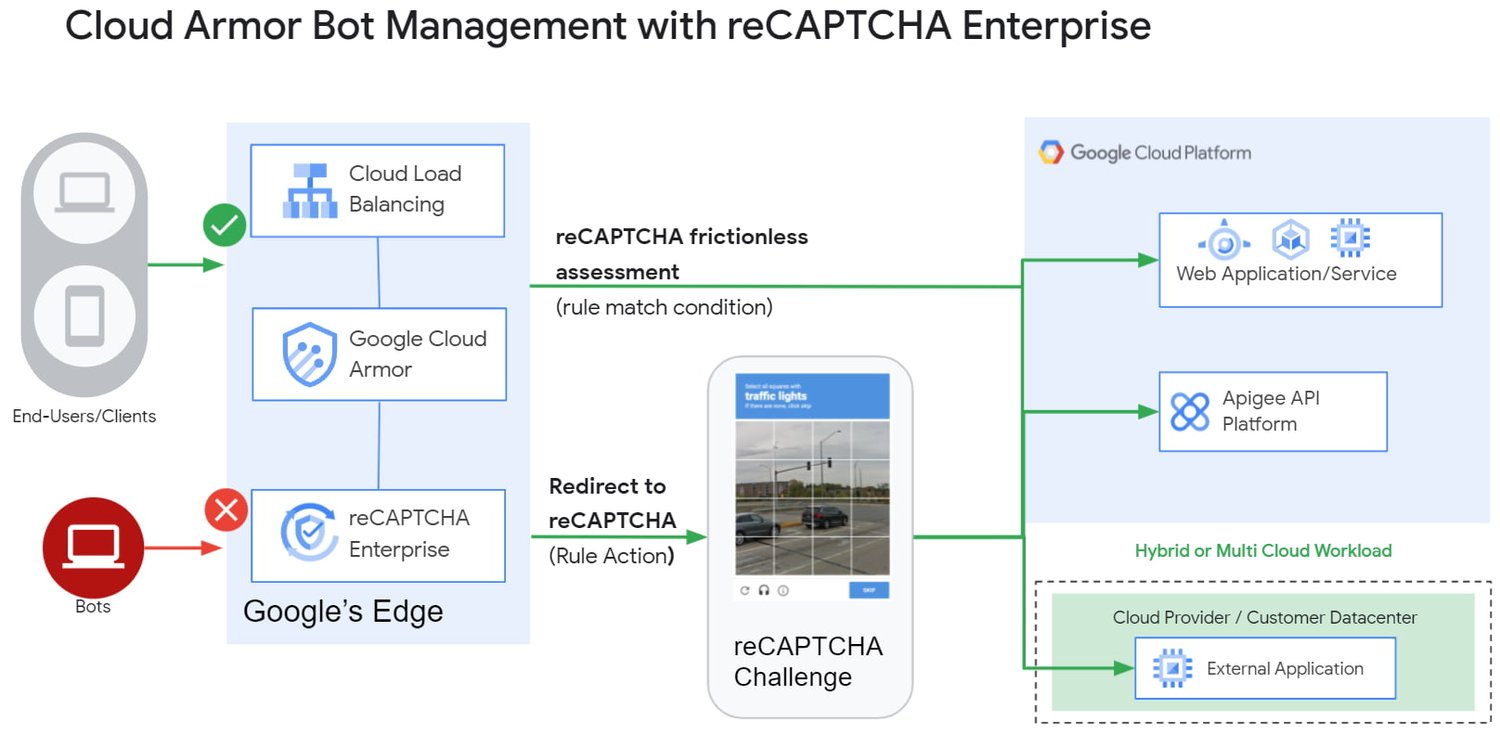
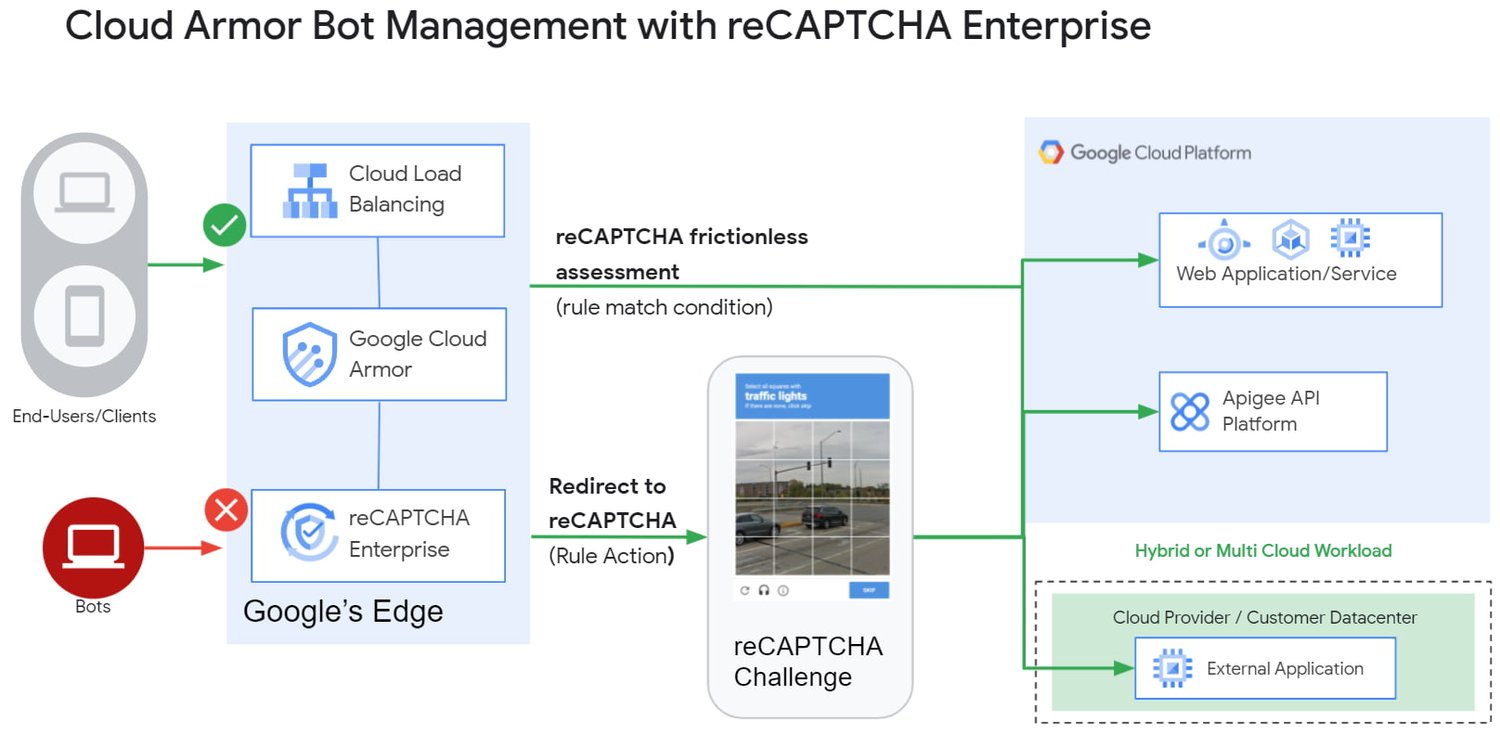
Today we are announcing the public preview of Cloud Armor bot management with reCAPTCHA Enterprise.This new set of capabilities is centered around a new deep integration between reCAPTCHA Enterprise and Cloud Armor as part of our overall Web-App and API Protection (WAAP) solution, which also includes Apigee. You can now leverage the power of reCAPATCHA's intelligence gained from protecting 5+ million sites directly in Cloud Armor to comprehensively manage risk from bots and other application layer threats. You can enable this protection using an easy-to-configure policy in Cloud Armor without any server-side changes to your applications. Because detection and enforcement happens in-line, at the edge of Google’s network, you can mitigate threats before they have a chance to impact your applications, whether they run on GCP, on premise, or in a hybrid or multi-cloud deployment.
Google Cloud Armor
Cloud Armor is the DDoS mitigation service and web-application firewall (WAF) that brings to bear the global scale of Google’s network - blocking unwelcome traffic upstream from your infrastructure. Cloud Armor helps protect your websites and applications from volumetric and protocol based (Layer 3/4) DDoS attacks, application level DDoS attacks, and mitigates the rest of the OWASP Top 10. With Cloud Armor, you can enforce custom Layer 7 filtering and rate-limiting policies at the edge to ensure availability of your workloads and meet security and compliance requirements.
reCAPTCHA Enterprise
reCAPTCHA Enterprise is Google’s fraud detection service that leverages over a decade of experience defending the internet and data from Google’s network of over 5 million sites. reCAPTCHA Enterprise can be used to prevent fraud and attacks perpetrated by scripts, bot software, or humans. When installed on a web page at the point of action, such as login, purchase, or account creation, reCAPTCHA Enterprise provides a frictionless user experience that allows legitimate users to proceed using a web page while fake users and bots are blocked.
The Cloud Armor and reCAPTCHA Enterprise integration
Users can now configure their Cloud Armor security policies to block requests that reCAPTCHA determines to be coming from a bot. There are several ways to do this:
1) Enforce reCAPTCHA Enterprise frictionless assessment
reCAPTCHA Enterprise assigns risk scores to interactions on your website (e.g., logins, signups, gift card redemption, checking out, etc.) Based on these interactions, it returns a score between 0.0 and 1.0, with 0.0 being a likely fraudulent interaction and 1.0 being a likely legitimate interaction. To reduce fraud, you might choose to take action on returned scores for logins below 0.5, but allow users with higher scores to continue their login with zero friction.
With this new integration, you can also have Cloud Armor take action based on the score, including blocking or redirecting the request based on reCAPTCHA’s assessment from the client-side instrumentation. The client-side instrumentation can be enabled by installing reCAPATCHA's javascript library into browser applications or using the reCAPTCHA SDK with mobile applications. By the time the user’s request leaves the client, it will have a reCAPTCHA assessment and bot score attached to it. This scoring is accomplished in-line, as the user’s request is being evaluated through your Cloud Armor security policy. Crucially, this occurs without incurring the latency of an additional request/response back to the reCAPTCHA service.
2) Serve reCAPTCHA Challenge in Cloud Armor
In this scenario, suspicious users are blocked by Cloud Armor until they solve the reCAPTCHA Enterprise challenge.You can configureCloud Armor to serve a reCAPTCHA challenge for any requests that match on a Cloud Armor security policy rule. To do so, you can configure a rule in through the Google Cloud CLI with an action to redirect to reCAPTCHA Enterprise in order to serve a CAPTCHA:
In the above example, we are choosing to have reCAPTCHA Enterprise deployed to assess every request attempting to access the login page to prevent bots from logging into our service. With Cloud Armor first requiring reCAPTCHA Enterprise to assess the bot risk of reach request, unwelcome traffic from bots would be blocked at the edge.
3) Redemption Flow
While we aim to make the initial reCAPTCHA assessment as accurate as possible, some organizations prefer to give the end-user another chance by solving a challenge in the event that the reCAPTCHA score is lower than their defined threshold. As part of this release, you can combine both the frictionless assessment and manual challenge into what we call the “redemption flow”. To do so, you can configure the match condition of a Cloud Armor rule to detect a low reCAPTCHA token score and configure the action of the same rule to redirect to a reCAPTCHA challenge.
By combining both of these scenarios into the redemption flow, you can give suspicious clients the opportunity to redeem themselves by proving they are not a bot.
These bot detection and mitigation use cases, taken together or separately, allow your bot management strategy to scale up without impacting your protected workloads, as all decisions are made at the edge of Google’s network.
Additional bot management capabilities
In addition to the integration with reCAPTCHA Enterprise, Cloud Armor has added more capabilities to help you implement an effective bot management strategy:
Redirect actions – Cloud Armor rules now support a redirect action to redirect end-clients to a user-configured URL. Requests that match on such rules would respond with an HTTP 302 to the end-client in order to send them to an alternative destination.
Insert Header – With the ability to conditionally insert a custom header and value into an incoming request, users can now tag requests based on the criteria in the match condition of any Cloud Armor rule. This allows you to treat tagged requests differently downstream in your applications. For example, you can choose to route suspicious requests to a honeypot or silently not process their transaction so as not to tip off the bot that it has been detected.
Learn more
Cloud customers can get started right now by configuring a rule to redirect to reCAPTCHA in their Cloud Amor security policies through the command line interface. Learn more in these documentation links:



