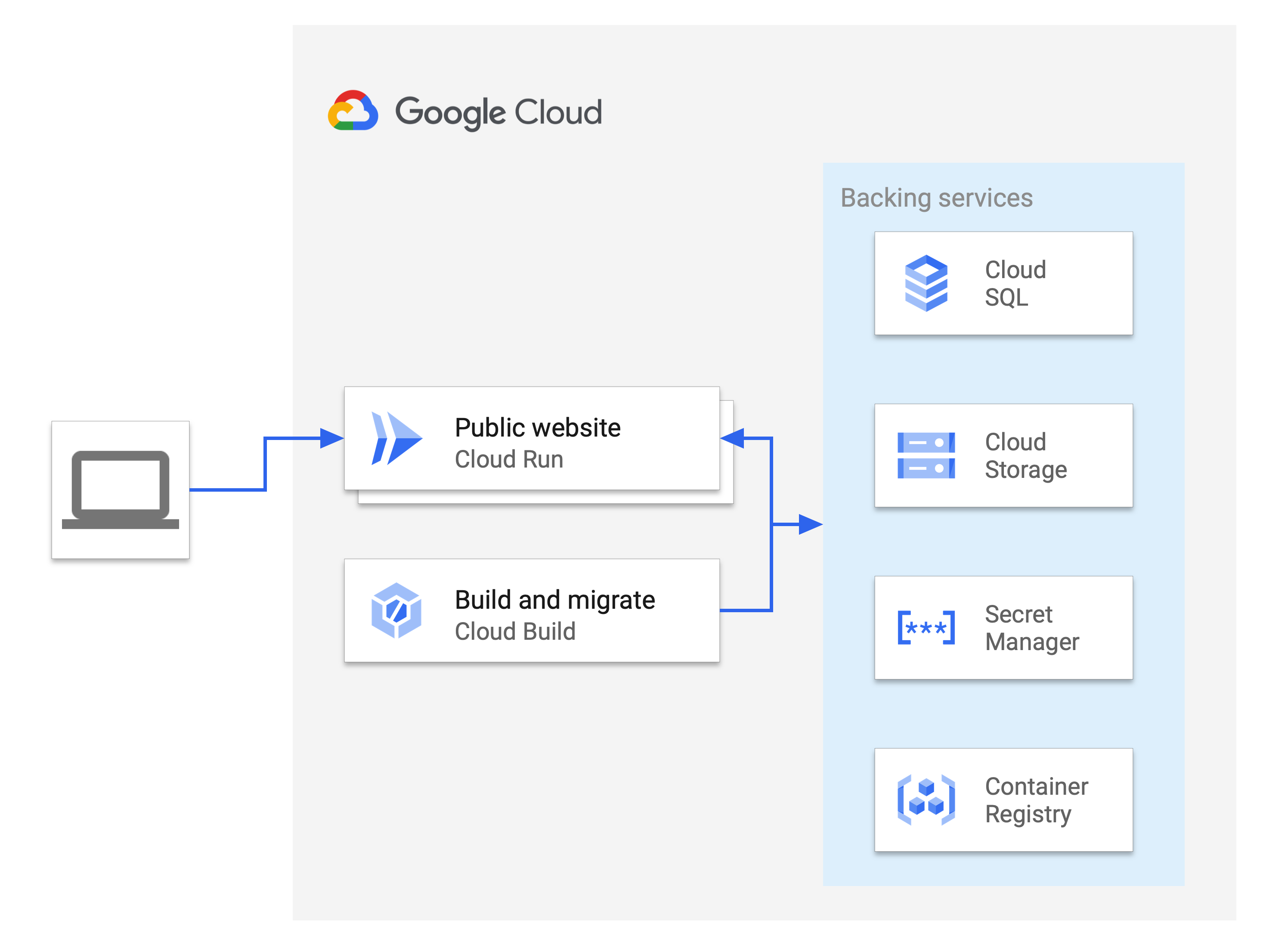
Learn how to deploy a sample Rails application to Cloud Run and how to integrate managed databases, object storage, encrypted secrets, and build pipelines with serverless compute.
Deploying Rails applications involves integrating multiple services together to form a cohesive project. This tutorial assumes that you are familiar with Rails web development.
This tutorial requires Ruby 3.0 or later and Rails 8 or later.
Objectives
- Create and connect a Cloud SQL database to Active Record
- Create and use Secret Manager to store and access a Rails master key securely
- Host user-uploaded media and files on Cloud Storage from Active Storage
- Use Cloud Build to automate build and database migrations
- Deploy a Rails app to Cloud Run
Costs
Before you begin
- Sign in to your Google Cloud account. If you're new to Google Cloud, create an account to evaluate how our products perform in real-world scenarios. New customers also get $300 in free credits to run, test, and deploy workloads.
-
In the Google Cloud console, on the project selector page, select or create a Google Cloud project.
Roles required to select or create a project
- Select a project: Selecting a project doesn't require a specific IAM role—you can select any project that you've been granted a role on.
-
Create a project: To create a project, you need the Project Creator
(
roles/resourcemanager.projectCreator), which contains theresourcemanager.projects.createpermission. Learn how to grant roles.
-
Verify that billing is enabled for your Google Cloud project.
-
Enable the Cloud Run, Cloud SQL, Cloud Build, Secret Manager, and Compute Engine APIs.
Roles required to enable APIs
To enable APIs, you need the Service Usage Admin IAM role (
roles/serviceusage.serviceUsageAdmin), which contains theserviceusage.services.enablepermission. Learn how to grant roles. -
Install the Google Cloud CLI.
-
If you're using an external identity provider (IdP), you must first sign in to the gcloud CLI with your federated identity.
-
To initialize the gcloud CLI, run the following command:
gcloud init -
In the Google Cloud console, on the project selector page, select or create a Google Cloud project.
Roles required to select or create a project
- Select a project: Selecting a project doesn't require a specific IAM role—you can select any project that you've been granted a role on.
-
Create a project: To create a project, you need the Project Creator
(
roles/resourcemanager.projectCreator), which contains theresourcemanager.projects.createpermission. Learn how to grant roles.
-
Verify that billing is enabled for your Google Cloud project.
-
Enable the Cloud Run, Cloud SQL, Cloud Build, Secret Manager, and Compute Engine APIs.
Roles required to enable APIs
To enable APIs, you need the Service Usage Admin IAM role (
roles/serviceusage.serviceUsageAdmin), which contains theserviceusage.services.enablepermission. Learn how to grant roles. -
Install the Google Cloud CLI.
-
If you're using an external identity provider (IdP), you must first sign in to the gcloud CLI with your federated identity.
-
To initialize the gcloud CLI, run the following command:
gcloud init - Ensure sufficient permissions are available to the account used for this tutorial.
Prepare your environment
This tutorial uses several Google Cloud services to provide the database, media storage, and secret storage that support the deployed Rails application. Prepare your environment by configuring a region to deploy the services in and by cloning the Rails app.
Set the default project and region
Set the default project configuration for the gcloud CLI by running the following command:
gcloud config set project PROJECT_IDReplace
PROJECT_IDwith your Google Cloud project IDConfigure your region:
export REGION=REGIONReplace
REGIONwith an appropriate location. For efficiency between services, all services should be deployed in the same region. For more information about the closest region to you, see Products available by location.
Clone the Rails app
The code for the Rails sample app is in the
GoogleCloudPlatform/ruby-docs-samples
repository on GitHub.
Clone the repository:
git clone https://github.com/GoogleCloudPlatform/ruby-docs-samples.gitGo to the directory that contains the sample code and run the following commands to make sure that the application is properly set up with the required gems and dependencies:
Linux/macOS
cd ruby-docs-samples/run/rails bundle installWindows
cd ruby-docs-samples\run\rails bundle install
Prepare the backing services
This tutorial uses a number of Google Cloud services to provide the database, media storage, and secret storage that support the deployed Rails project. These services are deployed in a specific region. For efficiency between services, it is best that all services are deployed in the same region. For more information about the closest region to you, see Products available by location.
Set up a Cloud SQL for PostgreSQL instance
Rails supports multiple relational databases, including several offered by Cloud SQL. This tutorial uses PostgreSQL, an open source database commonly used by Rails apps.
The following sections describe the creation of a PostgreSQL instance, database, and database user for your Rails app.
Create a PostgreSQL instance
Console
In the Google Cloud console, go to the Cloud SQL Instances page.
Click Create Instance.
Click Choose PostgreSQL.
In the Instance ID field, enter a name for the instance (
INSTANCE_NAME).In the Password field, enter a password for the postgres user.
Use the default values for the other fields.
Click Create Instance.
gcloud
Create the PostgreSQL instance:
gcloud sql instances create INSTANCE_NAME \ --database-version POSTGRES_12 \ --tier db-f1-micro \ --region REGIONReplace the following:
INSTANCE_NAME: your new Cloud SQL instance nameREGION: the Google Cloud region
It takes a few minutes to create the instance and for it to be ready for use.
Create a database
Console
In the Google Cloud console, go to the Cloud SQL Instances page.
Select the INSTANCE_NAME instance.
Go to the Databases tab.
Click Create database.
In the Database name dialog, enter
DATABASE_NAME.Click Create.
gcloud
Create the database within the recently created instance:
gcloud sql databases create DATABASE_NAME \ --instance INSTANCE_NAMEReplace
DATABASE_NAMEwith a name for the database inside the instance.
Create a user
Generate a random password for the database user, and write it to a file called dbpassword:
cat /dev/urandom | LC_ALL=C tr -dc '[:alpha:]'| fold -w 50 | head -n1 > dbpassword
Console
In the Google Cloud console, go to the Cloud SQL Instances page.
Select the INSTANCE_NAME instance.
Go to the Users tab.
Click Add User Account.
Under the Built-in Authentication dialog:
- Enter the username
DATABASE_USERNAME. - Enter the content of the
dbpasswordfile as the passwordPASSWORD.
- Enter the username
Click Add.
gcloud
Create the user within the recently created instance and set its password to be the content of dbpassword:
gcloud sql users create DATABASE_USERNAME \ --instance=INSTANCE_NAME --password=$(cat dbpassword)Replace
DATABASE_USERNAMEwith a name for the user inside the instance.
Set up an Artifact Registry repository
Use Artifact Registry to create a repository to store your container image.
Console
In the Google Cloud console, go to the Artifact Registry page.
Click Create Repository.
Enter the following:
- For Name, enter "cloud-run-source-deploy".
- For Format, select "Docker".
- For Region, select REGION.
Keep the default values for the other fields.
Click Create.
gcloud
Create an Artifact Registry repository:
gcloud artifacts repositories create cloud-run-source-deploy \ --repository-format docker \ --location REGION
Set up a Cloud Storage bucket
You can host Rails static assets and user-uploaded media in highly available object storage using Cloud Storage.
Console
- In the Google Cloud console, go to the Cloud Storage Buckets page.
- Click Create.
- On the Create a bucket page, enter your bucket information. To go to the next
step, click Continue.
-
In the Get started section, do the following:
- Enter a globally unique name that meets the bucket naming requirements.
- To add a
bucket label,
expand the Labels section (),
click add_box
Add label, and specify a
keyand avaluefor your label.
- For Location, select the following: us-central1
-
In the Choose how to store your data section, do the following:
- In the Set a default class section, select the following: Standard.
- To enable hierarchical namespace, in the Optimize storage for data-intensive workloads section, select Enable hierarchical namespace on this bucket.
- In the Choose how to control access to objects section, select whether or not your bucket enforces public access prevention, and select an access control method for your bucket's objects.
-
In the Choose how to protect object data section, do the
following:
- Select any of the options under Data protection that you
want to set for your bucket.
- To enable soft delete, click the Soft delete policy (For data recovery) checkbox, and specify the number of days you want to retain objects after deletion.
- To set Object Versioning, click the Object versioning (For version control) checkbox, and specify the maximum number of versions per object and the number of days after which the noncurrent versions expire.
- To enable the retention policy on objects and buckets, click the Retention (For compliance) checkbox, and then do the following:
- To enable Object Retention Lock, click the Enable object retention checkbox.
- To enable Bucket Lock, click the Set bucket retention policy checkbox, and choose a unit of time and a length of time for your retention period.
- To choose how your object data will be encrypted, expand the Data encryption section (), and select a Data encryption method.
- Select any of the options under Data protection that you
want to set for your bucket.
-
In the Get started section, do the following:
- Click Create.
gcloud
Create a Cloud Storage bucket. To create a unique Cloud Storage bucket name, use the PROJECT_ID and a suffix of your choice,
MEDIA_BUCKET_SUFFIX. In Cloud Storage, bucket names must be globally unique.gcloud storage buckets create gs://PROJECT_ID-MEDIA_BUCKET_SUFFIX \ --location=REGION
After creating a bucket, to make the uploaded images public, change the permissions of image objects to be readable by everyone.
Console
- In the Google Cloud console, go to the Cloud Storage Buckets page.
In the list of buckets, click the name of the bucket that you want to make public.
Select the Permissions tab near the top of the page.
Click the Add members button.
The Add members dialog appears.
In the New members field, enter
allUsers.In the Select a role drop down, select the Cloud Storage sub-menu, and click the Storage Object Viewer option.
Click Save.
Once shared publicly, a link icon appears for each object in the public access column. You can click this icon to get the URL for the object.
To learn how to get detailed error information about failed Ruby operations in the Google Cloud console, see Troubleshooting.
gcloud
Use the
gcloud storage buckets add-iam-policy-bindingcommand to make all objects public. Use the value forMEDIA_BUCKET_SUFFIXthat you used when you created the bucket.gcloud storage buckets add-iam-policy-binding gs://PROJECT_ID-MEDIA_BUCKET_SUFFIX \ --member=allUsers --role=roles/storage.objectViewer
Store secret values in Secret Manager
Now that the backing services are configured, Rails needs secure information, such as passwords, to access these services. Instead of putting these values directly into the Rails source code, this tutorial uses Rails Credentials and Secret Manager to store this information securely.
Create encrypted credentials file and store key as Secret Manager secret
Rails stores secrets in an encrypted file called 'config/credentials.yml.enc'.
The file can be decrypted with the local config/master.key or the environment
variable ENV["RAILS_MASTER_KEY"]. In the credentials file, you can store the
Cloud SQL instance database password and other access keys for external APIs.
You can store this key securely in Secret Manager. Then, you can grant Cloud Run and Cloud Build access to the key by granting access to their respective service accounts. Service accounts are identified by an email address that contains the project number.
Generate the
config/credentials.yml.encfile with the following command:bin/rails credentials:editThe command will create a
config/master.keyif no master key is defined, and create aconfig/credentials.yml.encfile if the file does not exist. This will open a temporary file in your default$EDITORwith the decrypted contents for the secrets to be added.Copy and paste the newly created PostgreSQL instance database password from the
dbpasswordfile into the credentials file:secret_key_base: GENERATED_VALUE gcp: db_password: PASSWORDSecrets can be accessed with
Rails.application.credentials. For example,Rails.application.credentials.secret_key_baseshould return the application's secret key base andRails.application.credentials.gcp[:db_password]should return your database password.The
config/credentials/yml.encis stored encrypted, butconfig/master.keycan be stored in Secret Manager.Console
In the Google Cloud console, go to the Secret Manager page.
Click Create secret
In the Name field, enter a name for the secret
RAILS_SECRET_NAME.In the Secret value dialog, paste the mater.key value into the box.
Click Create secret.
On the Secret details page of your secret, note the project number:
projects/PROJECTNUM/secrets/RAILS_SECRET_NAME
In the Permissions tab, click Add Member
In the New Members field, enter
PROJECTNUM-compute@developer.gserviceaccount.com, and then pressEnter.In the New Members field, enter
PROJECTNUM@cloudbuild.gserviceaccount.com, and then pressEnter.In the Role drop-down menu, select Secret Manager Secret Accessor.
Click Save.
gcloud
Create a new secret with the value of the config/master.key:
gcloud secrets create RAILS_SECRET_NAME --data-file config/master.keyReplace
RAILS_SECRET_NAMEwith a name for the new secret.To confirm the creation of the secret, check it:
gcloud secrets describe RAILS_SECRET_NAME gcloud secrets versions access latest --secret RAILS_SECRET_NAMEGet the value of the project number:
gcloud projects describe PROJECT_ID --format='value(projectNumber)'Grant access to the secret to the Cloud Run service account:
gcloud secrets add-iam-policy-binding RAILS_SECRET_NAME \ --member serviceAccount:PROJECTNUM-compute@developer.gserviceaccount.com \ --role roles/secretmanager.secretAccessorReplace
PROJECTNUMwith the project number value.Grant access to the secret to the Cloud Build service account:
gcloud secrets add-iam-policy-binding RAILS_SECRET_NAME \ --member serviceAccount:PROJECTNUM@cloudbuild.gserviceaccount.com \ --role roles/secretmanager.secretAccessorIn the output, confirm that
bindingslists the two service accounts as members.
Connect Rails app to production database and storage
This tutorial uses a PostgreSQL instance as the production database and
Cloud Storage as the storage backend. For Rails to connect to the
newly created database and storage bucket, you need to specify all the
information needed to access them in the .env file. The .env file contains
the configuration for the application environment variables. The application
will read this file using the dotenv gem. Since the secrets are stored in
credentials.yml.enc and Secret Manager, the .env doesn't
have to be encrypted because it doesn't hold any sensitive credentials.
- To configure the Rails app to connect with the database and storage bucket,
open the
.envfile. Modify the
.envfile configuration to the following. Use the value ofMEDIA_BUCKET_SUFFIXthat you used when you created the bucket.PRODUCTION_DB_NAME: DATABASE_NAME PRODUCTION_DB_USERNAME: DATABASE_USERNAME CLOUD_SQL_CONNECTION_NAME: PROJECT_ID:REGION:INSTANCE_NAME GOOGLE_PROJECT_ID: PROJECT_ID STORAGE_BUCKET_NAME: PROJECT_ID-MEDIA_BUCKET_SUFFIXThe Rails app is now set up to use Cloud SQL and Cloud Storage when deploying to Cloud Run.
Deploy the app to Cloud Run
With the backing services set up, you can now deploy the app as a Cloud Run service.
Using the supplied
cloudbuild.yaml, use Cloud Build to build the image, run the database migrations, and populate the static assets:gcloud builds submit --config cloudbuild.yaml \ --substitutions _SERVICE_NAME=SERVICE_NAME,_INSTANCE_NAME=INSTANCE_NAME,_REGION=REGION,_SECRET_NAME=RAILS_SECRET_NAMEReplace
SERVICE_NAMEwith the name for your service. This first build takes a few minutes to complete. If the build timed out, increase the timeout duration by inserting --timeout=2000s into the build command.When the build is successful, deploy the Cloud Run service for the first time, setting the service region, base image, and connected Cloud SQL instance:
gcloud run deploy SERVICE_NAME \ --region REGION \ --image REGION-docker.pkg.dev/PROJECT_ID/cloud-run-source-deploy/SERVICE_NAME \ --add-cloudsql-instances PROJECT_ID:REGION:INSTANCE_NAME \ --allow-unauthenticatedYou should see output that shows the deployment succeeded, with a service URL.
To see the deployed service, go to the service URL.
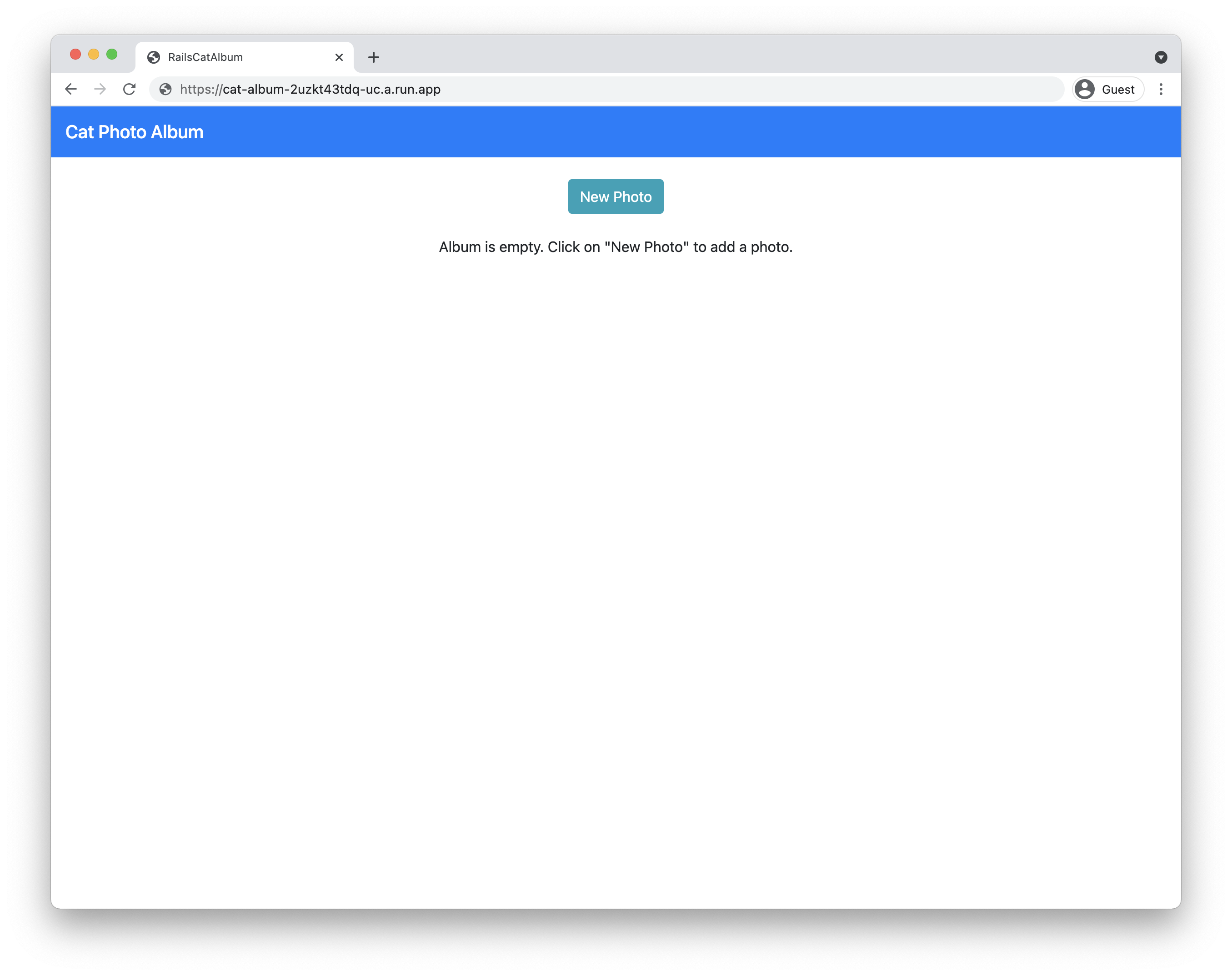
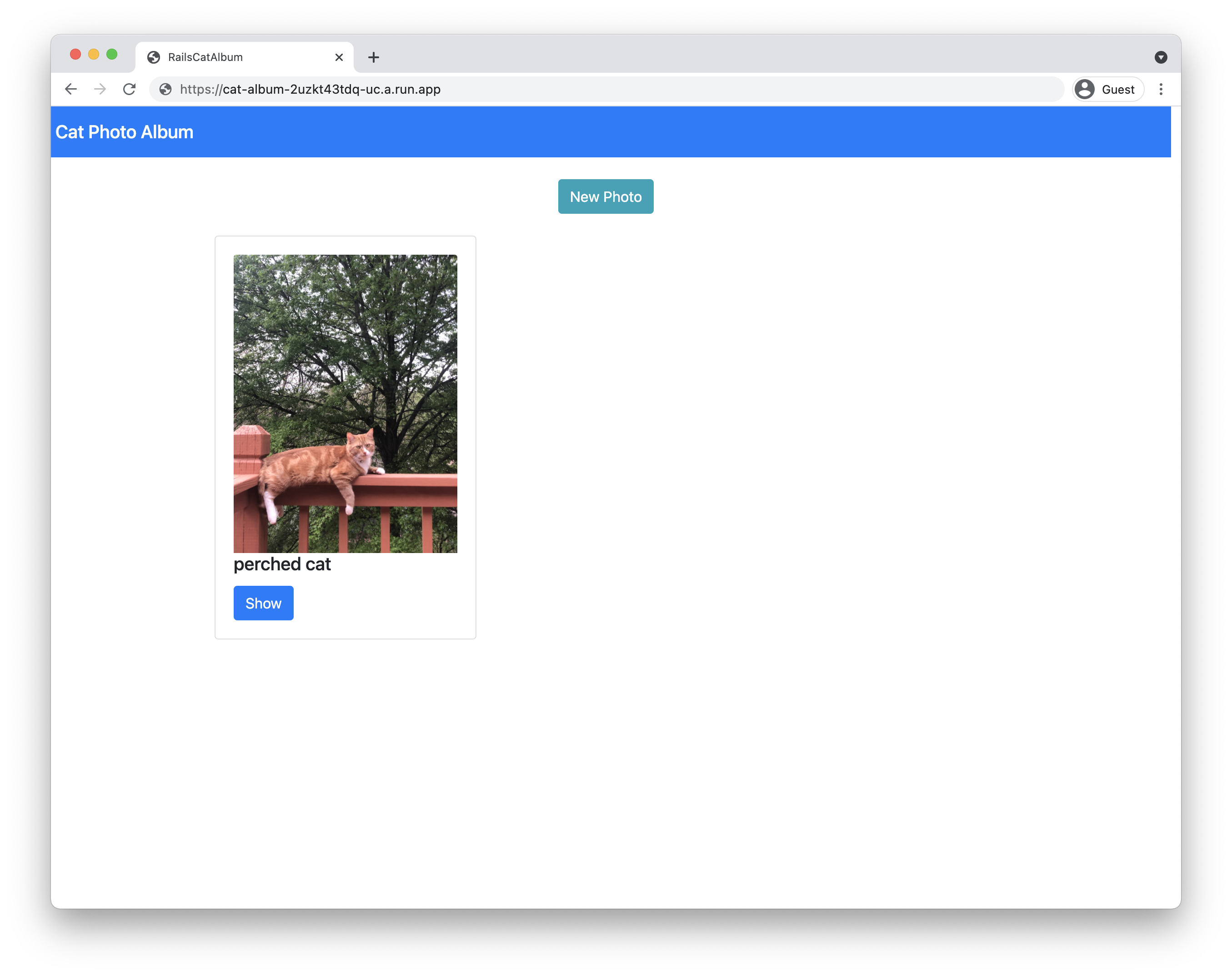
If the service URL shows Cat Photo Album, you're on the homepage of the app. Try to upload a new photo. If the photo successfully uploads, the Rails application has been successfully deployed.
If the service URL shows Cat Photo Album, you're on the homepage of the app.
Update the application
While the initial provisioning and deployment steps were complex, making updates is a simpler process:
Run the Cloud Build build and migration script:
gcloud builds submit --config cloudbuild.yaml \ --substitutions _SERVICE_NAME=SERVICE_NAME,_INSTANCE_NAME=INSTANCE_NAME,_REGION=REGION,_SECRET_NAME=RAILS_SECRET_NAMEDeploy the service, specifying only the region and image:
gcloud run deploy SERVICE_NAME \ --region REGION \ --image REGION-docker.pkg.dev/PROJECT_ID/cloud-run-source-deploy/SERVICE_NAME
Understand the code
The Rails sample app was created using standard Rails commands. The following commands create the cat_album app and use the scaffold command to generate a model, controller, and views for the Photo resource:
rails new cat_album
rails generate scaffold Photo caption:text
Database connection
The config/database.yml file contains the configuration needed to access
your databases in different environments (development, test, production). For
example, the production database is configured to run in Cloud SQL
for PostgreSQL. The database name and username are set through environment
variables in the .env file, while the database password is stored inside the
config/credentials.yml.enc file, which requires the RAILS_MASTER_KEY to
decrypt.
When the app runs on Cloud Run (fully managed), it connects to the PostgreSQL instance using a socket provided by the Cloud Run environment. When the app runs on your local machine, it connects to the PostgreSQL instance using the Cloud SQL Auth proxy.
Cloud-stored user uploaded media
Rails uses
Active Storage to
upload files to storage providers. The config/storage.yml and
config/environments/production.rb files specify Cloud Storage as the
service provider in the production environment.
Automation with Cloud Build
The cloudbuild.yaml file performs not only the typical image build steps (creating the container image and pushing that to Artifact Registry), but also the Rails database migrations. This migration is performed by using Cloud Run jobs, where a custom command is used so that the container performs the migration, rather than the default web server.
Substitution variables are used in this configuration. Changing the values in the file directly means the --substitutions flag can be dropped at migration time.
In this configuration, only existing migrations in the db/migrate directory
are applied. To create migration files, see
Active Record Migrations.
To build the image and apply migrations, the
Cloud Build configuration
needs access to the RAILS_MASTER_KEY secret from Secret Manager. The availableSecrets field sets the secret version and environment variables to use for the secret. The master key secret is passed in as an argument in the build image step and then gets set to be the RAILS_MASTER_KEY in the Dockerfile when building the image.
To extend the Cloud Build configuration to include the deployment in the one configuration without having to run two commands, see Continuous deployment from git using Cloud Build. This requires IAM changes, as described.
Cleanup
- In the Google Cloud console, go to the Manage resources page.
- In the project list, select the project that you want to delete, and then click Delete.
- In the dialog, type the project ID, and then click Shut down to delete the project.
