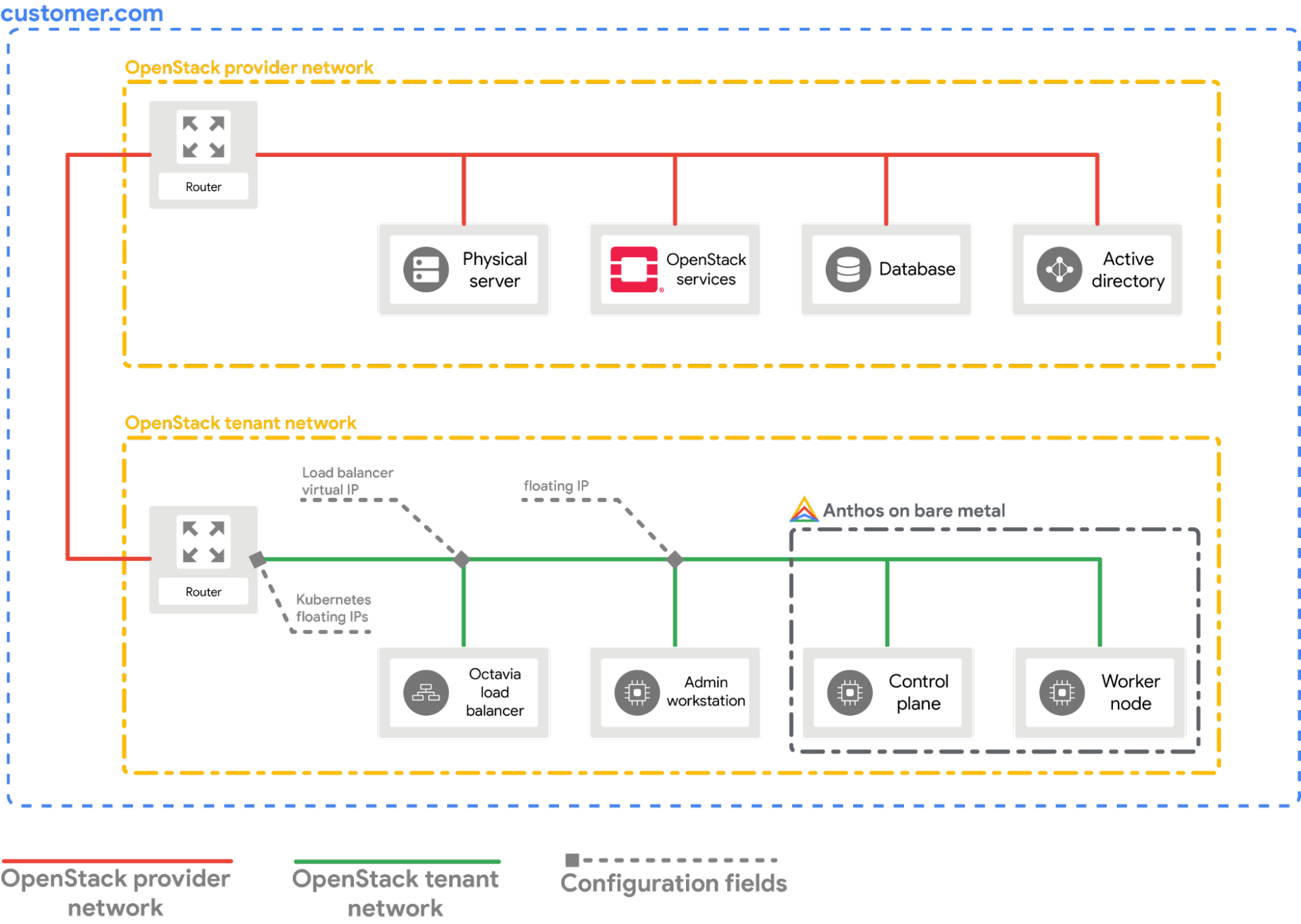
이 가이드에서는 베어메탈 클러스터에서 Kubernetes용 OpenStack 클라우드 제공업체를 구성하는 방법을 설명합니다. OpenStack LBaaS를 사용하여 Kubernetes 서비스를 노출하도록 OpenStack 클라우드 제공업체를 구성해야 합니다.
기본 요건
이 가이드에서는 OpenStack에 베어메탈 클러스터 배포 가이드에 설명된 것과 비슷한 설정으로 OpenStack 환경에서 Google Distributed Cloud로 만든 클러스터가 실행된다고 가정합니다. 이 단계를 시도하기 전에 먼저 해당 가이드를 참조하세요.
제공업체 구성
다음 섹션에서는 로컬 워크스테이션의 터미널 창에서 시작한다고 가정합니다.
OpenStack 클라이언트 구성(
openrc) 파일을 얻습니다. OpenStack WebUI에서 다운로드할 수 있습니다.source PATH_TO_OPENRC_FILE/openrcOpenStack Kubernetes 클라우드 제공업체를 위한 구성 파일을 만듭니다.
cat > cloud.conf << EOF [Global] auth-url=${OS_AUTH_URL} username=${OS_USERNAME} password=${OS_PASSWORD} region=RegionOne tenant-name=admin domain-id=default # this is for using a self-signed cert if your using a CA then comment this line # and point to the CA certificate using the "ca-file" arg tls-Insecure=true [LoadBalancer] use-octavia=true # this is generally the public network on OpenStack floating-network-id=PUBLIC_NETWORK_ID # this should be private network subnet where vip is allocated for the ABM nodes subnet-id=ABM_NETWORK_SUBNET_ID [BlockStorage] bs-version=v2 EOF다음을 바꿉니다.
OS_AUTH_URL,OS_USERNAME,OS_PASSWORD: 이러한 변수는openrc파일을 가져와서 환경에 이미 설정되어 있어야 합니다. 그러면 변수가 자동으로 선택됩니다.PUBLIC_NETWORK_ID: 유동 IP 주소가 할당된 OpenStack 배포에서 공개적으로 액세스 가능한 네트워크입니다. 이 ID는 Kubernetes 서비스에 대해LoadBalancer IPs가 할당된 이 네트워크에서 가져옵니다. 한 줄 명령어를 사용하여 OpenStack 환경에서 이 IP를 가져올 수 있습니다.ABM_NETWORK_SUBNET_ID: 이것이 Google Distributed Cloud 소프트웨어 전용을 실행하는 VM에 대해 IP가 할당된 OpenStack 배포의 비공개 네트워크에 있는 서브넷입니다. OpenStack에서 공개 네트워크 ID 가져오기와 비슷한 명령어를 사용하여 OpenStack 환경에서 이 IP를 가져올 수 있습니다.
abm-wsVM의 비공개 유동 IP 주소를 가져옵니다.export OPENSTACK_IPS=$(openstack floating ip list --tags=abm_ws_floatingip -f json) export FLOATING_IP=$(jq -c '.[]."Floating IP Address"' <<< $OPENSTACK_IPS | tr -d '"')cloud.conf파일을 OpenStack의abm-wsVM에 복사합니다.scp ./cloud.conf ubuntu@$FLOATING_IP:~SSH를 사용하여
abm-wsVM에 안전하게 연결하고root사용자로 로그인합니다.Terraform 스크립트로 구성된
root사용자는abm입니다.ssh ubuntu@$FLOATING_IP sudo -u abm -icloud.conf파일을root사용자의$HOME디렉터리에 복사합니다.cp /home/ubuntu/cloud.conf $HOME이 구성을 사용해서
Kubernetes Secret을 만듭니다.# make sure the kubectl client is pointing towards your cluster export KUBECONFIG=~/bmctl-workspace/CLUSTER_NAME/CLUSTER_NAME-kubeconfig # store the provider configurations as a Kubernetes secret kubectl create secret -n kube-system generic cloud-config --from-file=cloud.confKubernetes용 OpenStack 클라우드 제공업체를 설치합니다.
# create the necessary roles for the OpenStack provider kubectl apply -f https://raw.githubusercontent.com/kubernetes/cloud-provider-openstack/master/manifests/controller-manager/cloud-controller-manager-roles.yaml # create the required role-bindings for the OpenStack provider kubectl apply -f https://raw.githubusercontent.com/kubernetes/cloud-provider-openstack/master/manifests/controller-manager/cloud-controller-manager-role-bindings.yaml # create the OpenStack controller manager kubectl apply -f https://raw.githubusercontent.com/kubernetes/cloud-provider-openstack/master/manifests/controller-manager/openstack-cloud-controller-manager-ds.yaml
OpenStack 통합 검사
샘플 Point-Of-Sales 애플리케이션을 배포합니다.
kubectl apply -f https://raw.githubusercontent.com/GoogleCloudPlatform/anthos-samples/master/anthos-bm-openstack-terraform/resources/point-of-sales.yaml애플리케이션 포드가 실행 중인지 확인합니다.
kubectl get pods예상 출력:
NAME READY STATUS RESTARTS AGE api-server-7db4777f7f-zflk5 1/1 Running 0 74s inventory-58c6fb5568-dqk2x 1/1 Running 0 74s payments-68d5d65d5c-5mjl6 1/1 Running 0 74sLoadBalancer유형의 서비스를 통해 애플리케이션을 노출했습니다.kubectl apply -f https://raw.githubusercontent.com/GoogleCloudPlatform/anthos-samples/master/anthos-bm-openstack-terraform/resources/point-of-sales-service.yaml브라우저에서 서비스에 액세스해보세요.
# wait for the external IP to be assigned kubectl get service api-server-lb NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE api-server-lb LoadBalancer 10.203.77.215 172.29.249.159 80:32378/TCP 4m12sEXTERNAL-IP를 사용하여 액세스하는 Point-Of-Sales 애플리케이션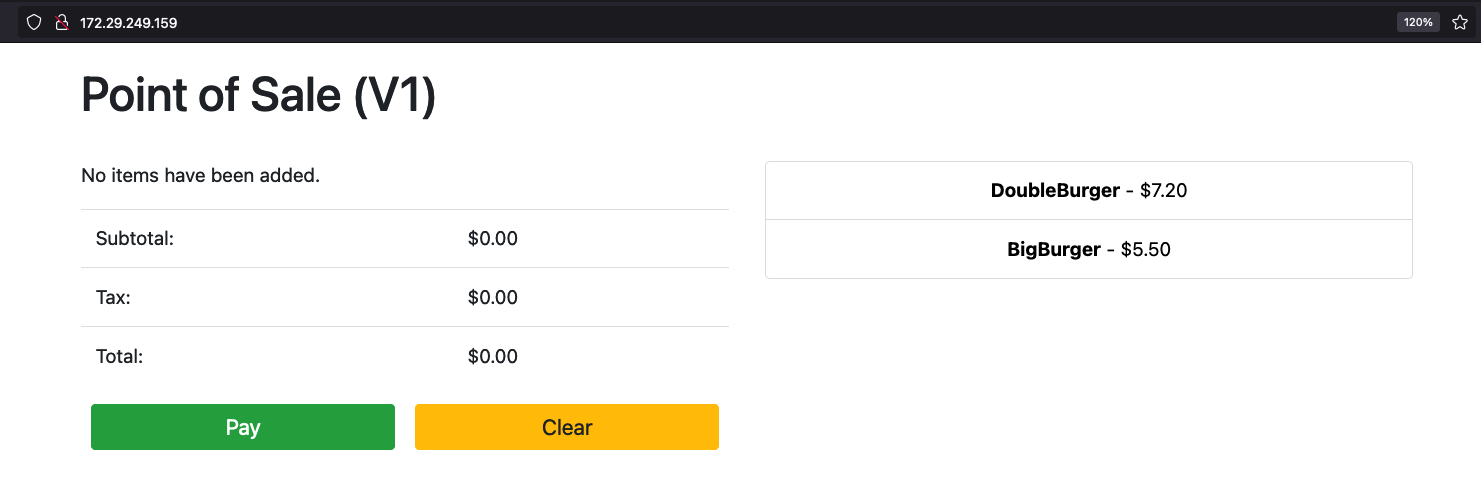
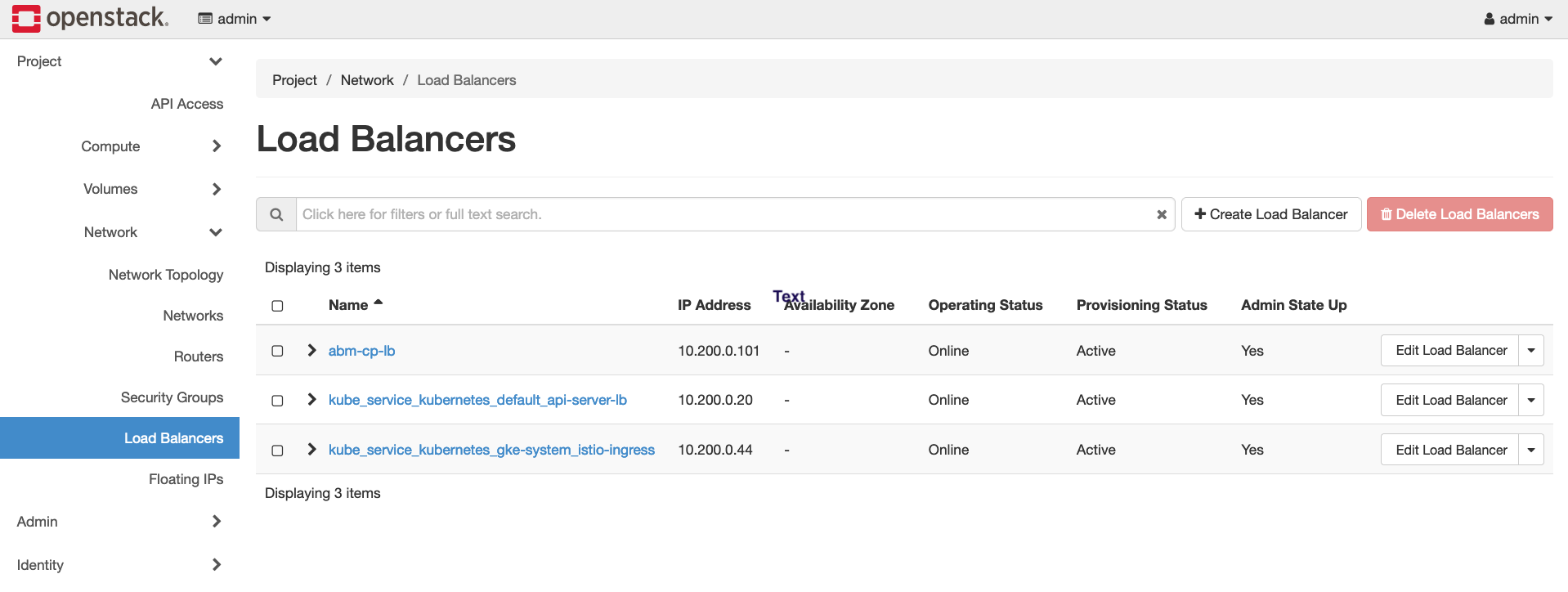
OpenStack WebUI를 방문하면 OpenStack에서 생성 중인 새 OpenStack 부하 분산기를 확인할 수 있습니다.