Getting started with Cloud Security Command Center

Kelly Anderson
Product Marketing Manager
Andy Chang
Senior Product Manager
As you deploy Google Cloud Platform (GCP) services in Google Cloud, you need centralized visibility into what resources are running and their security state. You also need to know if there has been anomalous activity and how to take action against it.
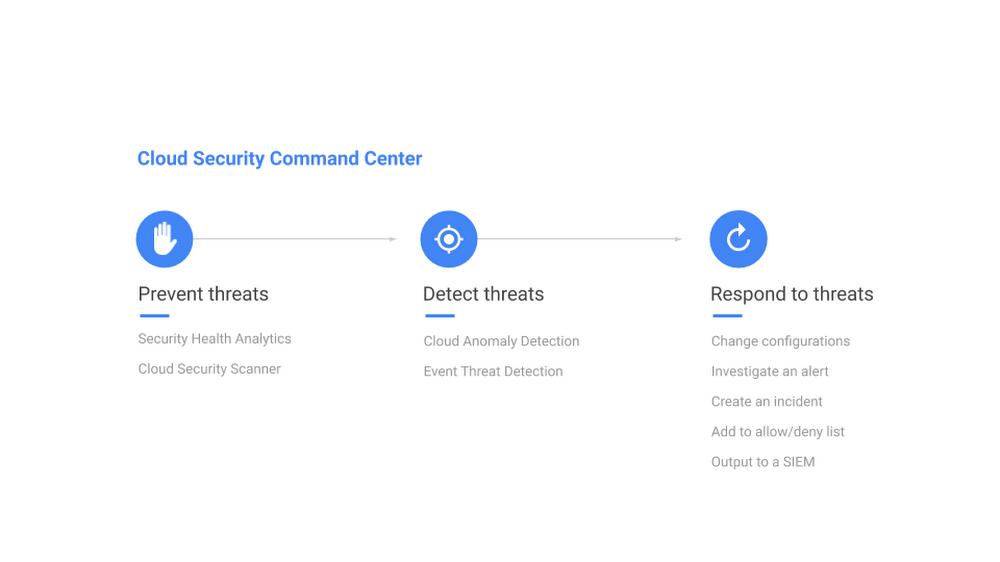
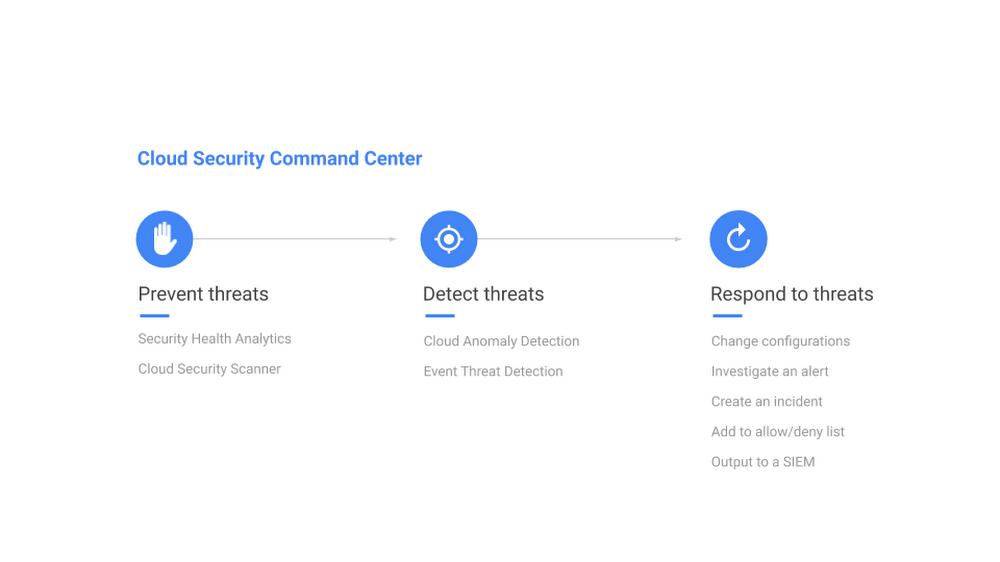
Last week at Google Cloud Next ‘19, we announced the general availability of Cloud Security Command Center (Cloud SCC), a security management and data risk tool for GCP resources that helps you prevent, detect, and respond to threats from a single pane of glass.
Cloud SCC helps you identify misconfigured virtual machines, networks, applications, and storage and act on them before they damage your business. Cloud SCC has built-in threat detection services, including Event Threat Detection, that can quickly surface suspicious activity or compromised resources. You can also use it to reduce the amount of time it takes to respond to threats by following actionable recommendations or exporting data to your security information and event management (SIEM) system.
Let’s take a deeper look at how to use Cloud SCC to prevent, detect, and respond to threats.
Prevent threats with visibility and control over your cloud data and services
The cloud makes it easier for anyone in your IT department to create a service. However, if these services are not deployed through your central IT department, you may be unaware of what services are running in GCP and how they are protected. Cloud SCC gives you visibility into what GCP services you are running on Google Cloud, including App Engine, BigQuery, Cloud SQL, Cloud Storage, Compute Engine, Cloud Identity and Access Management (IAM) policies, Google Kubernetes Engine, and more.


With this visibility, you can quickly understand how many projects you have, what resources are deployed, where sensitive data is located, which service accounts have been added or removed, and how firewall rules are configured. It’s also easy to see if users outside of your designated domain, or GCP organization, have access to your resources.
Besides giving you visibility into your GCP assets, Cloud SCC tracks changes to your assets so you can quickly act on unauthorized modifications. You can also view new, deleted, and total assets for within a specific time period or view resources at an organizational or project level. Cloud SCC generates notifications when changes occur and trigger Cloud Functions from a Cloud SCC query.
Oilfield services company Schlumberger uses Google Cloud to help them safely and efficiently manage hydrocarbon exploration and production data. “Adopting Google’s Cloud Security Command Center enables an automated inventory of our numerous assets in GCP,” said Jean-Loup Bevierre, Cyber Security Engineering Manager at Schlumberger. “It provides us with a comprehensive view of their rapidly evolving running status, configuration and external exposure. This is a key enabler for us to proactively secure these resources and engineer solutions for our next-gen SOC."
In addition to giving you visibility into your GCP assets in Google Cloud and when changes are made, Cloud SCC can help you see resources that have been misconfigured or have vulnerabilities—before an attacker can exploit them.
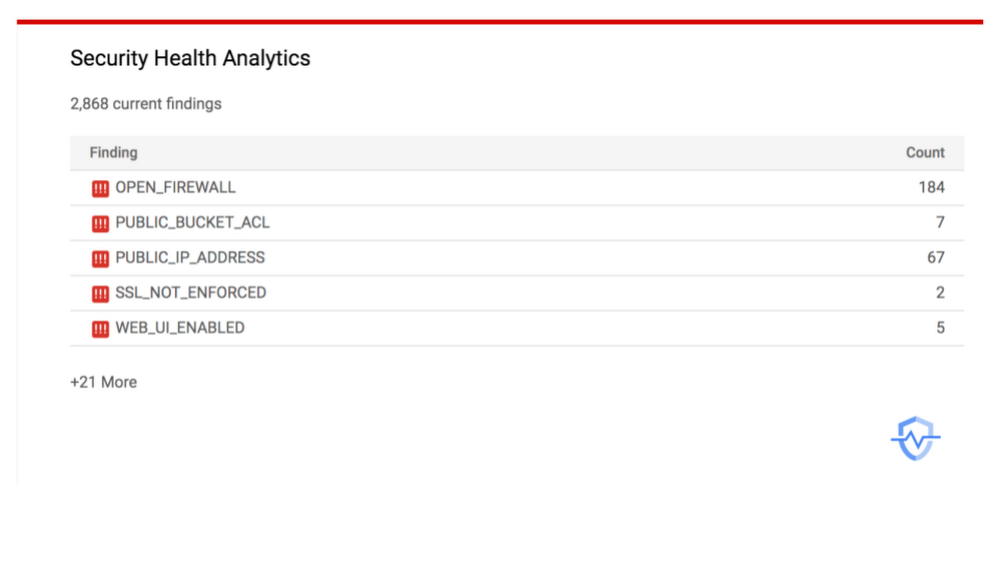
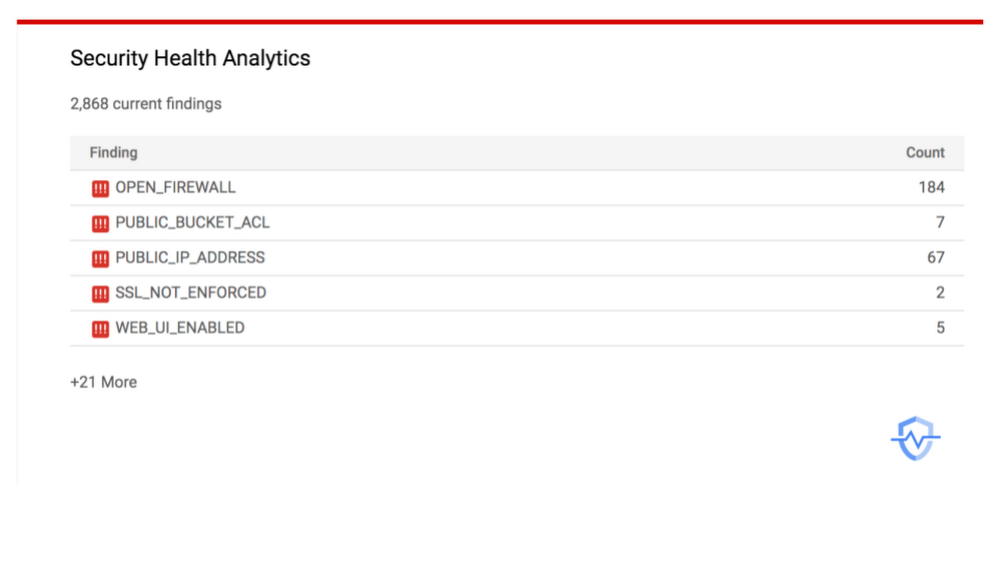
Available today in alpha, Cloud SCC’s Security Health Analytics capability assesses the overall security state and activity of your virtual machines, network, and storage. You can see issues with public storage buckets, open firewall ports, stale encryption keys, or deactivated security logging. To learn more about this capability, visit our documentation. To get started with this new capability, sign up for the alpha program.
Another native capability that helps you prevent threats is Cloud Security Scanner. This scanner can detect vulnerabilities such as cross-site-scripting (XSS), use of clear-text passwords, and outdated libraries in your App Engine apps. It is generally available for App Engine and now available in beta for Google Kubernetes Engine (GKE) and Compute Engine.
Detect threats targeting your GCP assets
It takes an enterprise 197 days, on average, to detect a threat, but it only takes an attacker hours to gain access to your environment, causing an average of $3.86 million dollars worth of damage, according to a Ponemon Institute study.This does not have to be your reality if you use Cloud SCC’s integrated threat detection services.
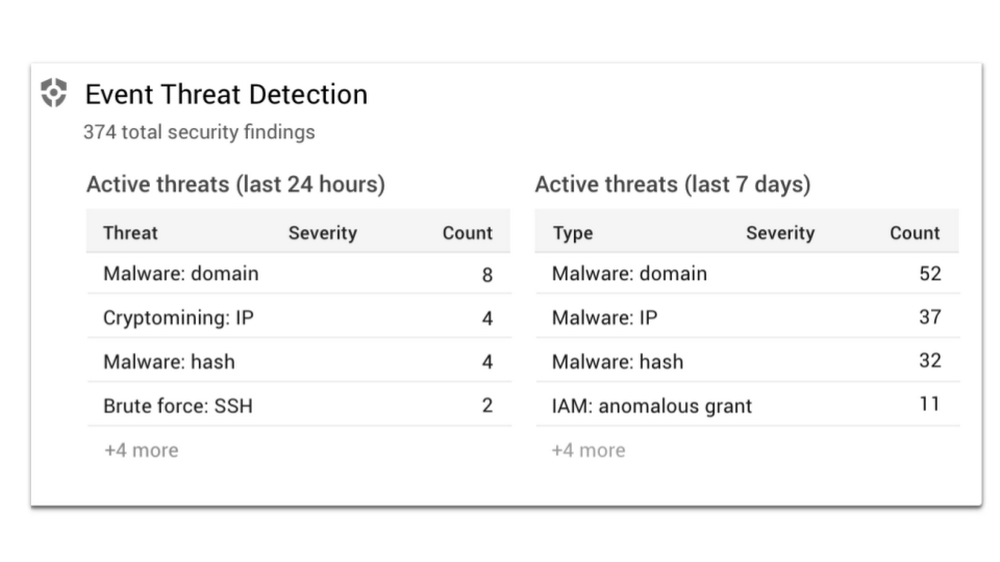
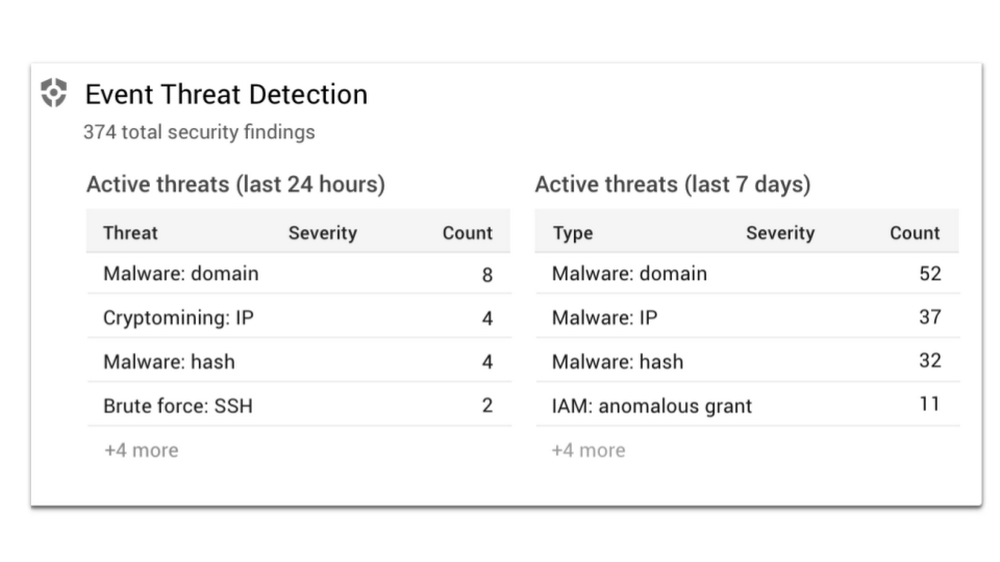
Available today in beta, Event Threat Detection scans your Stackdriver security logs for high-profile indicators that your environment has been compromised. Event Threat Detection uses industry-leading threat intelligence, including Google Safe Browsing, to detect malware, cryptomining, unauthorized access to GCP resources, outgoing DDoS attacks, port scanning, and brute-force SSH. Event Threat Detection sorts through large quantities of logs to help you identify high-risk incidents and focus on remediation. For further analysis, you can send findings to a third-party solution, such as a SIEM, using Cloud Pub/Sub and Cloud Functions. Sign up for the beta program today.
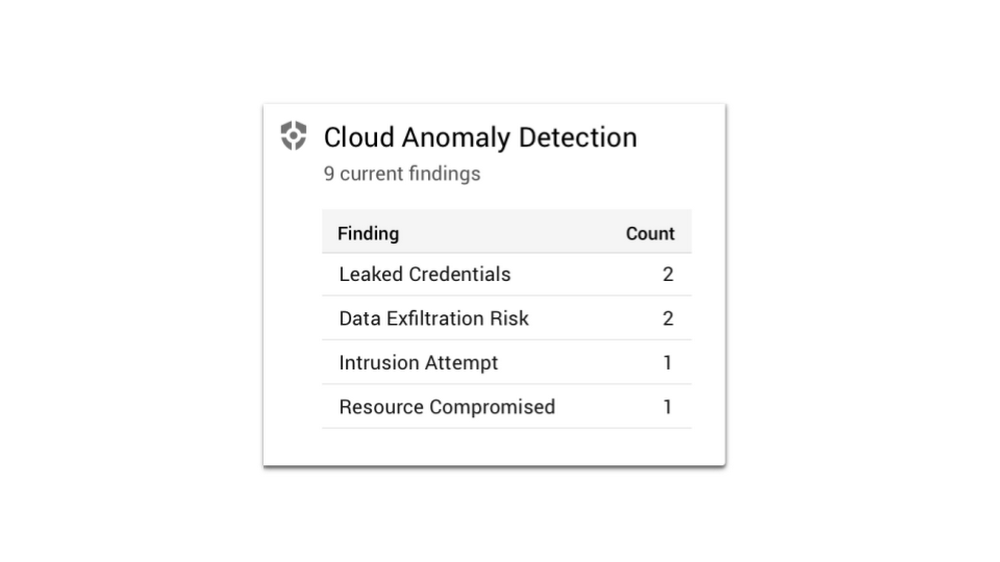
Cloud Anomaly Detection, another built-in Cloud SCC service, can detect leaked credentials, cryptomining, unusual activity, hijacked accounts, compromised machines used for botnets or DDoS attacks, and anomalous data activity. In just a few clicks, you can find out more information about the attack and follow actionable recommendations.
Respond to threats targeting your GCP assets
When a threat is detected, we know that every second counts. Cloud SCC gives you several ways to respond to threats, including updating a configuration setting on a VM, changing your firewall rules, tracking an incident in Stackdriver Incident Response Management or pushing security logs to a SIEM for further analysis.
Meet your security needs with a flexible platform
We understand that you have investments in security solutions for both on-premises and other cloud environments. Cloud SCC is a flexible platform that integrates with partner security solutions and Google security tools.
Partner solutions surface vulnerabilities or threats directly into Cloud SCC. Now you can see findings from Google security tools and partner tools in one location and quickly take action. You can also move from the Cloud SCC dashboard into third-party consoles to remediate issues.
We’re excited to share today that Acalvio, Capsule8, Cavirin, Chef, Check Point CloudGuard Dome 9, Cloudflare, CloudQuest, McAfee, Qualys, Reblaze, Redlock by Palo Alto Networks, StackRox, Tenable.io, and Twistlock are running their security services on Google Cloud and integrate into Cloud SCC. Find out more about how Capsule8, Cavirin, CloudQuest, McAfee, Reblaze, and Cloud SCC work together.


Cloud SCC also integrates with GCP security tools, including Access Transparency, Binary Authorization, Cloud Data Loss Prevention (DLP), Enterprise Phishing Protection, and the open-source security toolkit Forseti, letting you view and take action on the information provided by these tools.
Access Transparency gives you near real-time logs when GCP administrators access your content. Gain visibility into accessor location, access justification, or the action taken on a specific resource from Cloud SCC.
Binary Authorization ensures only trusted container images are deployed on GKE. With Cloud SCC, it’s easy to see if you are running containers with trusted or untrusted images and take action.
Cloud DLP shows storage buckets that contain sensitive and regulated data. Cloud DLP can help prevent you from unintentionally exposing sensitive data and ensure access is conditional.
Forseti integrates with Cloud SCC to help you keep track of your environment, monitor and understand your policies, and provide correction.
Enterprise Phishing Protection reports URLs directly to Google Safe Browsing and publishes phishing results in the Cloud SCC dashboard, making it your one-stop shop to see and respond to abnormal activity in your environment and respond.
Cloud SCC pricing
There is no separate charge for Cloud SCC. However, you will be charged if you upload more than 1 GB per day of external findings into Cloud SCC. In addition, some detectors that are integrated into Cloud SCC, such as Cloud DLP, charge by usage. Learn more on the DLP pricing page.
Get started today
There are lots of ways to start taking advantage of Cloud SCC.
- Enable it from the GCP Marketplace and start using for free.
- Learn more about Cloud SCC by reading the documentation.
Watch Cloud SCC in action in this session from Next ‘19.